1.安装cfssl工具
master节点部署即可
$wget https://pkg.cfssl.org/R1.2/cfssl_linux-amd64
$wget https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64
$wget https://pkg.cfssl.org/R1.2/cfssl-certinfo_linux-amd64
$ chmod +x cfssl*
$mv cfssl_linux-amd64 cfssl
$mv cfssljson_linux-amd64 cfssljson
$mv cfssl-certinfo_linux-amd64 cfssl-certinfo
$mv cfssl* /usr/bin/
$ll /usr/bin/cfssl*
2.创建CA配置文件
$mkdir /root/ssl
$cd ssl/
$cfssl print-defaults config > config.json
$cfssl print-defaults csr > csr.json
3.创建ca-config.json文件
$cat > ca-config.json <<EOF
{
"signing": {
"default": {
"expiry": "87600h"
},
"profiles": {
"kubernetes": {
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
],
"expiry": "87600h"
}
}
}
}
EOF
4.创建CA证书签名请求
$cat > ca-csr.json <<EOF
{
"CN": "kubernetes",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "BeiJing",
"L": "BeiJing",
"O": "k8s",
"OU": "System"
}
]
}
EOF
5.生成 CA 证书和私钥
$cfssl gencert -initca ca-csr.json | cfssljson -bare ca
$ ls ca*
ca-config.json ca.csr ca-csr.json ca-key.pem ca.pem
6.创建 kubernetes 证书
注:红色内容写入k8s集群环境中所有节点的IP地址。
$cat > kubernetes-csr.json <<EOF
{
"CN": "kubernetes",
"hosts": [
"127.0.0.1",
"192.168.7.191",
"192.168.7.192",
"192.168.7.193",
"10.254.0.1",
"kubernetes",
"kubernetes.default",
"kubernetes.default.svc",
"kubernetes.default.svc.cluster",
"kubernetes.default.svc.cluster.local"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "BeiJing",
"L": "BeiJing",
"O": "k8s",
"OU": "System"
}
]
}
EOF
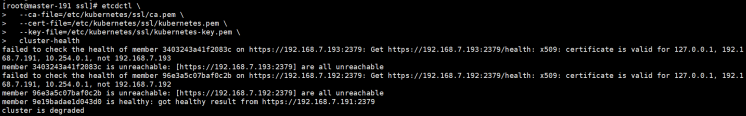
注:下图是我验证文档可用性时,重新搭建的环境,上文红色中地址仅写了master的地址,后面查看etcd集群健康状态时失败,原因是没有其它两个从节点的认证。所以这里建议写k8s集群中所有节点地址。
7.生成 kubernetes 证书和私钥
$cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes kubernetes-csr.json | cfssljson -bare kubernetes
$ls kubernetes*
kubernetes.csr kubernetes-csr.json kubernetes-key.pem kubernetes.pem
8.创建 admin 证书
$cat > admin-csr.json <<EOF
{
"CN": "admin",
"hosts": [],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "BeiJing",
"L": "BeiJing",
"O": "system:masters",
"OU": "System"
}
]
}
EOF
9.生成 admin 证书和私钥
$cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes admin-csr.json | cfssljson -bare admin
$ls admin*
admin.csr admin-csr.json admin-key.pem admin.pem
10.创建 kube-proxy 证书
$cat > kube-proxy-csr.json <<EOF
{
"CN": "system:kube-proxy",
"hosts": [],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "BeiJing",
"L": "BeiJing",
"O": "k8s",
"OU": "System"
}
]
}
EOF
11.生成 kube-proxy 客户端证书和私钥
$cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes kube-proxy-csr.json | cfssljson -bare kube-proxy
$ls kube-proxy*
kube-proxy.csr kube-proxy-csr.json kube-proxy-key.pem kube-proxy.pem
12.校验证书
$ openssl x509 -noout -text -in kubernetes.pem
13.分发证书
$mkdir -p /etc/kubernetes/ssl #所有节点创建该目录
$cp *.pem /etc/kubernetes/ssl
$scp *.pem root@192.168.7.132:/etc/kubernetes/ssl
$scp *.pem root@192.168.7.133:/etc/kubernetes/ssl