Firewalld防火墙
Centos7 中集成了防火墙管理工具, Firewall系统动态防火墙管理器是作为默认的防火墙工具.
它支持规则动态更新,并加入zone区域概念.
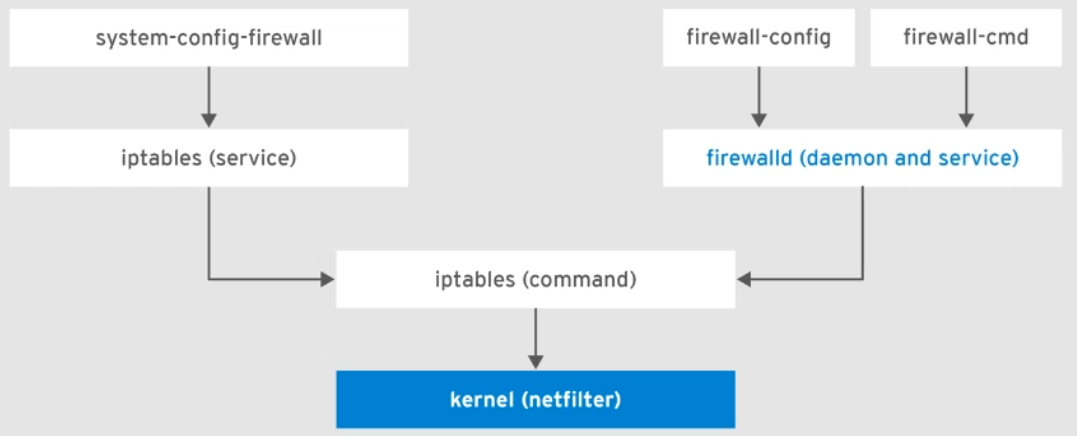
Firewalld防火墙是在iptables基础上新型的防火墙服务,它调用的是iptables
firewalld防火墙默认规则
在Firewalld防火墙规则设置中,从外部访问服务器内部,如果没有添加规则,默认是拒绝的
而从服务器内部访问服务器外部则是默认放行的.
防火墙基本命令
#启动停止命令:
systemctl start firewalld
systemctl stop firewalld
systemctl status firewalld
systemctl enable firewalld
#禁用旧版防火墙
systemctl mask iptables.service
systemctl mask ip6tables.service
#zone区域命令
firewall-cmd --get-default-zone #查看默认区域
firewall-cmd --get-active-zones #查看活跃的区域
#活跃区域规则查看:
[root@master ~]# firewall-cmd --list-all
public
target: default
icmp-block-inversion: no
interfaces:
sources:
services: ssh dhcpv6-client
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
[root@xuexi-001 ~]# firewall-cmd --list-all --zone=drop
drop
target: DROP #默认拒绝
icmp-block-inversion: no
interfaces: eth0 #网卡接口
sources: #源
services: #服务
ports: #端口
protocols: #端口转换
masquerade: no #IP伪装
forward-ports: #端口伪装
source-ports: #源端口
icmp-blocks: #源ip
rich rules: #规则
## 检查服务端口是否开放:
firewall-cmd --set-default-zone=public
[root@xuexi-001 ~]# firewall-cmd --zone=public --query-service=ssh
yes
firewall-cmd --add-masquerade #开启IP伪装
firewalld恢复默认规则:
恢复默认规则有两种方式:
1. 命令行操作
[root@xuexi-001 ~]# firewall-cmd --set-default-zone=public
Warning: ZONE_ALREADY_SET: public
success
[root@xuexi-001 ~]# firewall-cmd --reload
success
2. 配置文件操作
[root@xuexi-001 ~]# vim /etc/firewalld/firewalld.conf
[root@xuexi-001 ~]# firewall-cmd --reload
success
无论那种方法修改都需要对防火墙执行重启操作: firewall-cmd --reload
如果有规则存在,需要清空规则 如:
方法1:
[root@xuexi-001 ~]# firewall-cmd --remove-source=10.0.0.0/24 --zone=public --permanent
Warning: NOT_ENABLED: 10.0.0.0/24
success
方法2: 修改配置文件 vim /etc/firewalld/zones/public.xml
<?xml version="1.0" encoding="utf-8"?>
<zone>
<short>Public</short>
<description>For use in public areas. You do not trust the other computers on networks to not harm your computer. Only selected incoming connections are accepted.</description>
<service name="ssh"/> #--- 对应规则
<service name="dhcpv6-client"/> #--- 对应规则
</zone>
删除对应规则然后 firewall-cmd --reload 即可
firewalld实验: 设置默认区域和白名单
使用默认区域 drop可以拒绝所有连接,在使用白名单配合后可以配置仅限于某个IP能够连接到服务器
清理默认区域
1. 设置默认区域drop:
firewall-cmd --set-default-zone=drop
firewall-cmd --permanent --change-interface=eth0 --zone=drop
2. 检查设置
[root@master ~]# firewall-cmd --get-default-zone
drop
3. 添加白名单:
[root@master ~]# firewall-cmd --add-source=10.0.0.0/24
success
[root@master ~]# firewall-cmd --add-source=192.168.0.0/24
success
#两个网段一个是本机网段一个是虚拟机网段.
[root@master ~]# firewall-cmd --add-source=192.168.0.0/24 --permanent --zone=trusted
success
4. 检查:
[root@master ~]# firewall-cmd --list-all
drop (active)
target: DROP
icmp-block-inversion: no
interfaces:
sources: 10.0.0.0/24 192.168.0.0/24
services:
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
[root@master ~]# firewall-cmd --list-all-zones
trusted (active)
target: ACCEPT
icmp-block-inversion: no
interfaces:
sources: 192.168.0.0/24
services:
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
[root@master ~]# firewall-cmd --list-all --zone=trusted
trusted (active)
target: ACCEPT
icmp-block-inversion: no
interfaces:
sources: 10.0.0.0/24 192.168.0.0/24
services:
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
5. 重载生效:
[root@master ~]# firewall-cmd --reload
success
策略配置
1. 安装一个nginx,并启动
yum install -y nginx
2. 测试从外部访问nginx
发现无法访问
3. 防火墙策略配置:
[root@xuexi-001 firewalld]# firewall-cmd --add-port=80/tcp
success
如果需要移除可以使用命令: firewall-cmd --remove-port=80/tcp 即可
添加80端口访问后检查防火墙如下:
[root@xuexi-001 firewalld]# firewall-cmd --list-all
public
target: default
icmp-block-inversion: no
interfaces:
sources:
services: ssh
ports: 80/tcp #------- 允许80
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
移除80端口后检查防火墙如下:
[root@xuexi-001 firewalld]# firewall-cmd --list-all
public
target: default
icmp-block-inversion: no
interfaces:
sources:
services: ssh
ports: #--------- 没有允许80
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
## 多端口添加:
[root@xuexi-001 firewalld]# firewall-cmd --permanent --add-port=8080/tcp --add-port=8080/udp
success
注意: --permanent 参数为永久生效的意思
## 删除添加的端口[临时删除]:
[root@xuexi-001 firewalld]# firewall-cmd --remove-port=8080/udp
success
[root@xuexi-001 firewalld]# firewall-cmd --remove-port=8080/tcp
success
## 注意如果是永久有效的规则,还需要继续配置永久失效[永久删除]:
firewall-cmd --remove-port=8080/tcp --permanent
firewall-cmd --remove-port=8080/udp --permanent
#服务名方式添加和移除端口
案例: 添加nginx端口
[root@xuexi-001 firewalld]# firewall-cmd --add-service=http --add-service=https
success
检查:
[root@xuexi-001 firewalld]# firewall-cmd --list-all
public
target: default
icmp-block-inversion: no
interfaces:
sources:
services: ssh http https
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
添加陌生服务端口
思考: 这些服务名我们知道哪些端口,但是是否也有一些陌生服务端口我们不知道的,这里面也没有的呢? 如何自定义添加陌生服务端口?如:zabbix nfs php-fpm
检查这些端口有没有:
[root@xuexi-001 firewalld]# firewall-cmd --add-service=php-fpm
Error: INVALID_SERVICE: php-fpm
这些端口都是没有被提供的,现在需要我们自定义添加端口.
所有服务端口其实都是定义了一个配置文件,它位于: /usr/lib/firewalld/services/ 目录中,我们可以照葫芦画瓢,拷贝一份用于新服务配置
#配置php-fpm端口
[root@xuexi-001 firewalld]# cd /usr/lib/firewalld/services/
[root@xuexi-001 services]# cp http.xml php-fpm.xml
[root@xuexi-001 services]# vim php-fpm.xml
<?xml version="1.0" encoding="utf-8"?>
<service>
<short>WWW (HTTP)</short>
<description>HTTP is the protocol used to serve Web pages. If you plan to make your Web server publicly available, enable this option. This option is not required for viewing pages locally or developing Web pages.</description>
<port protocol="tcp" port="80"/>
</service>
改为:
<?xml version="1.0" encoding="utf-8"?>
<service>
<short>WWW (HTTP)</short>
<description>HTTP is the protocol used to serve Web pages. If you plan to make your Web server publicly available, enable this option. This option is not required for viewing pages locally or developing Web pages.</description>
<port protocol="tcp" port="8000"/>
</service>
修改完成后,添加服务允许试试:
[root@xuexi-001 services]# firewall-cmd --reload #添加完了服务配置文件需要重载firewall
success
[root@xuexi-001 services]# firewall-cmd --add-service=zabbix # 这样就可以自定义添加服务了.
success
#还是重启服务有用,直接firewall-cmd --reload 有时候不生效.
[root@xuexi-001 services]# systemctl restart firewalld.service
添加完成后,通过命令就可以看到我们服务名 zabbix 已经添加成功.
[root@xuexi-001 services]# firewall-cmd --list-all
public
target: default
icmp-block-inversion: no
interfaces:
sources:
services: ssh zabbix
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
firewall端口转发案例:
#语法:
firewall-cmd --permanent --zone=[区域,默认:public] --add-forward-port=port=[源端口]:proto=[协议名,如:tcp]:toport=[目标端口]:toaddr=<目标IP地址>
--permanent是永久生效.
#将80端口转为8888端口
[root@xuexi-001 services]# firewall-cmd --add-forward-port=port=8888:proto=tcp:toport=80
success
#注意如果需要永久生效,记得尾部在添加 --permanent
[root@xuexi-001 services]# firewall-cmd --list-all
public
target: default
icmp-block-inversion: no
interfaces:
sources:
services: ssh http zabbix
ports:
protocols:
masquerade: no
forward-ports: port=8888:proto=tcp:toport=80:toaddr= #这里是添加后的规则
source-ports:
icmp-blocks:
rich rules:
例子:
将本地端口10.0.0.63:888端口转发到后端10.0.0.64:22端口
命令:
[root@xuexi-001 ~]# firewall-cmd --add-forward-port=port=888:proto=tcp:toport=22:toaddr=10.0.0.64
success
[root@xuexi-001 ~]# firewall-cmd --add-masquerade #开启IP伪装
[root@xuexi-001 ~]# firewall-cmd --list-all
public
target: default
icmp-block-inversion: no
interfaces:
sources:
services: ssh
ports:
protocols:
masquerade: no
forward-ports: port=888:proto=tcp:toport=22:toaddr=10.0.0.64
source-ports:
icmp-blocks:
rich rules:

可以看到我们连接的IP是10.0.0.63的888端口,而我们进入服务器得到的IP是真实服务器: 10.0.0.64
案例1: 允许10.0.0.0/24网段中的 10.0.0.10主机访问http服务,其他网段主机都不可以访问,当前和永久生效
firewall-cmd --add-rich-rule='rule family=ipv4 source address=10.0.0.1/32 server name=http accept'
案例2: 拒绝10.0.0.0/24网段中的10.0.0.10主机发起的SSH请求,但是允许访问http,当前和永久生效
firewall-cmd --permanent --zone=public --add-rich-rule='rule family=ipv4 source address=10.0.0.10/32 service name=ssh drop'
案例3: 将远程10.0.0.10的主机请求 firewalld的5000端口转发到后端10.0.0.20的22端口?
firewall-cmd --add-rich-rule='rule family=ipv4 source address=10.0.0.10/32 forward-port port="5551" protocol="top" to-port="22"'
firewalld共享上网
1. 开启内核转发
echo "net.ipv4.ip_forward = 1" >>/etc/sysctl.conf
2. 防火墙规则
firewall-cmd --add-masquerade --permanent
firewall-cmd --reload