1- 环境说明
| role | os | ip | cpu | ram | disk |
|---|---|---|---|---|---|
| master | Centos7.7 mini | 192.168.123.212(nat) | 2 cores | 8G | 80G |
| node-1 | Centos7.7 mini | 192.168.123.211 | 2 cores | 8G | 80G |
2- 准备环境【所有节点】
2.1- 初始化
#关闭防火墙和selinux
systemctl stop firewalld
systemctl disable firewalld
setenforce 0
sed -i.bak 's/SELINUX=enforcing/SELINUX=disabled/' /etc/selinux/config
## 关闭swap分区
swapoff -a
sed -i.bak '/ swap / s/^(.*)$/#1/g' /etc/fstab
#配置清华源
rm -rf /etc/yum.repos.d/*
curl -o /etc/yum.repos.d/CentOS-Base.repo https://files-cdn.cnblogs.com/files/lemanlai/CentOS-7.repo.sh
curl -o /etc/pki/rpm-gpg/RPM-GPG-KEY-7 https://mirror.tuna.tsinghua.edu.cn/centos/7/os/x86_64/RPM-GPG-KEY-CentOS-7
yum install epel-release -y
curl -o /etc/yum.repos.d/docker-ce.repo https://files-cdn.cnblogs.com/files/lemanlai/docker-ce.repo.sh
yum clean all
yum makecache fast
2.2- docker-ce 安装
yum remove docker docker-common docker-selinux docker-engine -y #如果你之前安装过 docker,请先删掉
yum install -y yum-utils device-mapper-persistent-data lvm2 #安装一些依赖
yum -y install docker-ce
systemctl enable docker
mkdir -p /etc/docker/
#写入加速地址和使用systemd driver
cat << EOF > /etc/docker/daemon.json
{"registry-mirrors": ["http://f1361db2.m.daocloud.io"],"exec-opts": ["native.cgroupdriver=systemd"]}
EOF
systemctl daemon-reload
systemctl restart docker #重启服务
2.3- 内核优化
##将桥接的IPv4流量传递到iptables的链
cat > /etc/sysctl.d/k8s.conf << EOF
net.bridge.bridge-nf-call-ip6tables = 1
net.bridge.bridge-nf-call-iptables = 1
net.ipv4.ip_forward = 1
EOF
sysctl --system
2.4- 安装kubeadm工具
cat << EOF >/etc/yum.repos.d/kubernetes.repo
[Kubernetes]
name=Kubernetes
baseurl=https://mirrors.aliyun.com/kubernetes/yum/repos/kubernetes-el7-x86_64
enabled=1
gpgcheck=1
repo_gpgcheck=1
gpgkey=https://mirrors.aliyun.com/kubernetes/yum/doc/yum-key.gpg https://mirrors.aliyun.com/kubernetes/yum/doc/rpm-package-key.gpg
EOF
yum clean all
yum makecache fast -y
## 查询kubeadm版本
yum list|egrep 'kubeadm|kubectl|kubelet'
[root@localhost ~]# yum list|egrep 'kubeadm|kubectl|kubelet'
kubeadm.x86_64 1.18.4-1 Kubernetes
kubectl.x86_64 1.18.4-1 Kubernetes
kubelet.x86_64 1.18.4-1 Kubernetes
##安装
yum install -y kubeadm-1.18.4 kubelet-1.18.4 kubectl-1.18.4
## 设置开机启动kubelet
systemctl enable kubelet
3- 开始安装
3.1- 集群初始化【master节点】
hostnamectl set-hostname master ##设置主机名
#初始化和部署master节点
kubeadm init
--apiserver-advertise-address=192.168.123.212
--image-repository registry.aliyuncs.com/k8s_containers_google
--kubernetes-version v1.18.1
--service-cidr=10.10.0.0/16
--pod-network-cidr=10.20.0.0/16
- 说明:
--apiserver-advertise-address=192.168.123.212 #master组件监听的api地址,必须能被其他节点所访问到
--image-repository registry.aliyuncs.com/k8s_containers_google #使用阿里云镜像
--kubernetes-version v1.18.1 #kubernetes的版本,阿里云上还没有1.18.4版本的镜像,此次使用1.18.1版本
--service-cidr=10.10.0.0/16 #services的网络范围
--pod-network-cidr=10.20.0.0/16 #pod的网络
- 部署过程:
[root@master ~]# kubeadm init
> --apiserver-advertise-address=192.168.123.212
> --image-repository registry.aliyuncs.com/k8s_containers_google
> --kubernetes-version v1.18.1
> --service-cidr=10.10.0.0/16
> --pod-network-cidr=10.20.0.0/16
W0627 18:49:03.368901 19261 configset.go:202] WARNING: kubeadm cannot validate component configs for API groups [kubelet.config.k8s.io kubeproxy.config.k8s.io]
[init] Using Kubernetes version: v1.18.1
[preflight] Running pre-flight checks
[preflight] Pulling images required for setting up a Kubernetes cluster
[preflight] This might take a minute or two, depending on the speed of your internet connection
[preflight] You can also perform this action in beforehand using 'kubeadm config images pull'
[kubelet-start] Writing kubelet environment file with flags to file "/var/lib/kubelet/kubeadm-flags.env"
[kubelet-start] Writing kubelet configuration to file "/var/lib/kubelet/config.yaml"
[kubelet-start] Starting the kubelet
[certs] Using certificateDir folder "/etc/kubernetes/pki"
[certs] Generating "ca" certificate and key
[certs] Generating "apiserver" certificate and key
[certs] apiserver serving cert is signed for DNS names [master kubernetes kubernetes.default kubernetes.default.svc kubernetes.default.svc.cluster.local] and IPs [10.10.0.1 192.168.123.212]
[certs] Generating "apiserver-kubelet-client" certificate and key
[certs] Generating "front-proxy-ca" certificate and key
[certs] Generating "front-proxy-client" certificate and key
[certs] Generating "etcd/ca" certificate and key
[certs] Generating "etcd/server" certificate and key
[certs] etcd/server serving cert is signed for DNS names [master localhost] and IPs [192.168.123.212 127.0.0.1 ::1]
[certs] Generating "etcd/peer" certificate and key
[certs] etcd/peer serving cert is signed for DNS names [master localhost] and IPs [192.168.123.212 127.0.0.1 ::1]
[certs] Generating "etcd/healthcheck-client" certificate and key
[certs] Generating "apiserver-etcd-client" certificate and key
[certs] Generating "sa" key and public key
[kubeconfig] Using kubeconfig folder "/etc/kubernetes"
[kubeconfig] Writing "admin.conf" kubeconfig file
[kubeconfig] Writing "kubelet.conf" kubeconfig file
[kubeconfig] Writing "controller-manager.conf" kubeconfig file
[kubeconfig] Writing "scheduler.conf" kubeconfig file
[control-plane] Using manifest folder "/etc/kubernetes/manifests"
[control-plane] Creating static Pod manifest for "kube-apiserver"
[control-plane] Creating static Pod manifest for "kube-controller-manager"
W0627 18:51:46.378499 19261 manifests.go:225] the default kube-apiserver authorization-mode is "Node,RBAC"; using "Node,RBAC"
[control-plane] Creating static Pod manifest for "kube-scheduler"
W0627 18:51:46.380355 19261 manifests.go:225] the default kube-apiserver authorization-mode is "Node,RBAC"; using "Node,RBAC"
[etcd] Creating static Pod manifest for local etcd in "/etc/kubernetes/manifests"
[wait-control-plane] Waiting for the kubelet to boot up the control plane as static Pods from directory "/etc/kubernetes/manifests". This can take up to 4m0s
[kubelet-check] Initial timeout of 40s passed.
[apiclient] All control plane components are healthy after 80.503096 seconds
[upload-config] Storing the configuration used in ConfigMap "kubeadm-config" in the "kube-system" Namespace
[kubelet] Creating a ConfigMap "kubelet-config-1.18" in namespace kube-system with the configuration for the kubelets in the cluster
[upload-certs] Skipping phase. Please see --upload-certs
[mark-control-plane] Marking the node master as control-plane by adding the label "node-role.kubernetes.io/master=''"
[mark-control-plane] Marking the node master as control-plane by adding the taints [node-role.kubernetes.io/master:NoSchedule]
[bootstrap-token] Using token: cnl2v7.9ss2f6m1ekv2dncw
[bootstrap-token] Configuring bootstrap tokens, cluster-info ConfigMap, RBAC Roles
[bootstrap-token] configured RBAC rules to allow Node Bootstrap tokens to get nodes
[bootstrap-token] configured RBAC rules to allow Node Bootstrap tokens to post CSRs in order for nodes to get long term certificate credentials
[bootstrap-token] configured RBAC rules to allow the csrapprover controller automatically approve CSRs from a Node Bootstrap Token
[bootstrap-token] configured RBAC rules to allow certificate rotation for all node client certificates in the cluster
[bootstrap-token] Creating the "cluster-info" ConfigMap in the "kube-public" namespace
[kubelet-finalize] Updating "/etc/kubernetes/kubelet.conf" to point to a rotatable kubelet client certificate and key
[addons] Applied essential addon: CoreDNS
[addons] Applied essential addon: kube-proxy
Your Kubernetes control-plane has initialized successfully!
To start using your cluster, you need to run the following as a regular user:
mkdir -p $HOME/.kube
sudo cp -i /etc/kubernetes/admin.conf $HOME/.kube/config
sudo chown $(id -u):$(id -g) $HOME/.kube/config
You should now deploy a pod network to the cluster.
Run "kubectl apply -f [podnetwork].yaml" with one of the options listed at:
https://kubernetes.io/docs/concepts/cluster-administration/addons/
Then you can join any number of worker nodes by running the following on each as root:
kubeadm join 192.168.123.212:6443 --token cnl2v7.9ss2f6m1ekv2dncw
--discovery-token-ca-cert-hash sha256:17baabf25b24968032bbe33538f6517ced7c970bcc28494a36b923eb86bdcfa0
- 创建连接集群配置文件
mkdir -p $HOME/.kube
cp -i /etc/kubernetes/admin.conf $HOME/.kube/config
chown $(id -u):$(id -g) $HOME/.kube/config
- 后续worker节点加入集群就只需要执行命令
kubeadm join 192.168.123.212:6443 --token cnl2v7.9ss2f6m1ekv2dncw
--discovery-token-ca-cert-hash sha256:17baabf25b24968032bbe33538f6517ced7c970bcc28494a36b923eb86bdcfa0
- 查看集群节点
[root@master ~]# kubectl get nodes -o wide
NAME STATUS ROLES AGE VERSION INTERNAL-IP EXTERNAL-IP OS-IMAGE KERNEL-VERSION CONTAINER-RUNTIME
master NotReady master 4m47s v1.18.4 192.168.123.212 <none> CentOS Linux 7 (Core) 3.10.0-1062.el7.x86_64 docker://19.3.12
3.2- 部署flannel
wget https://raw.githubusercontent.com/coreos/flannel/master/Documentation/kube-flannel.yml
sed -i 'squay.ioquay-mirror.qiniu.comg' kube-flannel.yml #改成国内源,加速镜像下载
kubectl apply -f kube-flannel.yml
部署过程:
[root@master ~]# kubectl apply -f kube-flannel.yml
podsecuritypolicy.policy/psp.flannel.unprivileged created
clusterrole.rbac.authorization.k8s.io/flannel created
clusterrolebinding.rbac.authorization.k8s.io/flannel created
serviceaccount/flannel created
configmap/kube-flannel-cfg created
daemonset.apps/kube-flannel-ds-amd64 created
daemonset.apps/kube-flannel-ds-arm64 created
daemonset.apps/kube-flannel-ds-arm created
daemonset.apps/kube-flannel-ds-ppc64le created
daemonset.apps/kube-flannel-ds-s390x created
[root@master ~]# kubectl get nodes -o wide
NAME STATUS ROLES AGE VERSION INTERNAL-IP EXTERNAL-IP OS-IMAGE KERNEL-VERSION CONTAINER-RUNTIME
master Ready master 16m v1.18.4 192.168.123.212 <none> CentOS Linux 7 (Core) 3.10.0-1062.el7.x86_64 docker://19.3.12
3.2- 加入集群【node节点】
hostnamectl set-hostname node-1
##加入集群
kubeadm join 192.168.123.212:6443 --token cnl2v7.9ss2f6m1ekv2dncw
--discovery-token-ca-cert-hash sha256:17baabf25b24968032bbe33538f6517ced7c970bcc28494a36b923eb86bdcfa0
##加入过程
[root@localhost ~]# kubeadm join 192.168.123.212:6443 --token cnl2v7.9ss2f6m1ekv2dncw --discovery-token-ca-cert-hash sha256:17baabf25b24968032bbe33538f6517ced7c970bcc28494a36b923eb86bdcfa0
W0627 20:49:40.750611 2328 join.go:346] [preflight] WARNING: JoinControlPane.controlPlane settings will be ignored when control-plane flag is not set.
[preflight] Running pre-flight checks
[WARNING IsDockerSystemdCheck]: detected "cgroupfs" as the Docker cgroup driver. The recommended driver is "systemd". Please follow the guide at https://kubernetes.io/docs/setup/cri/
[preflight] Reading configuration from the cluster...
[preflight] FYI: You can look at this config file with 'kubectl -n kube-system get cm kubeadm-config -oyaml'
[kubelet-start] Downloading configuration for the kubelet from the "kubelet-config-1.18" ConfigMap in the kube-system namespace
[kubelet-start] Writing kubelet configuration to file "/var/lib/kubelet/config.yaml"
[kubelet-start] Writing kubelet environment file with flags to file "/var/lib/kubelet/kubeadm-flags.env"
[kubelet-start] Starting the kubelet
[kubelet-start] Waiting for the kubelet to perform the TLS Bootstrap...bash
This node has joined the cluster:
* Certificate signing request was sent to apiserver and a response was received.
* The Kubelet was informed of the new secure connection details.
Run 'kubectl get nodes' on the control-plane to see this node join the cluster.
##在master执行
[root@master ~]# kubectl get nodes
NAME STATUS ROLES AGE VERSION
master Ready master 129m v1.18.4
node-1 Ready <none> 39m v1.18.4
[root@master ~]#
##node-1添加集群配置文件,允许node节点访问集群
[root@node-1 ~]# mkdir -p $HOME/.kube ##node节点运行
#master节点
[root@master ~]# scp /etc/kubernetes/admin.conf root@192.168.123.211:/root/.kube/config
root@192.168.123.211's password:
admin.conf 100% 5451 3.9MB/s 00:00
##node节点
[root@node-1 ~]# chown $(id -u):$(id -g) $HOME/.kube/config
[root@node-1 ~]# kubectl get nodes
NAME STATUS ROLES AGE VERSION
master Ready master 136m v1.18.4
node-1 Ready <none> 46m v1.18.4
##以上看到node-1的roles没有标签
##添加node-1的role标签为node
[root@node-1 ~]# kubectl label node node-1 node-role.kubernetes.io/node=
node/node-1 labeled
[root@node-1 ~]# kubectl get nodes
NAME STATUS ROLES AGE VERSION
master Ready master 139m v1.18.4
node-1 Ready node 49m v1.18.4
4- 部署应用
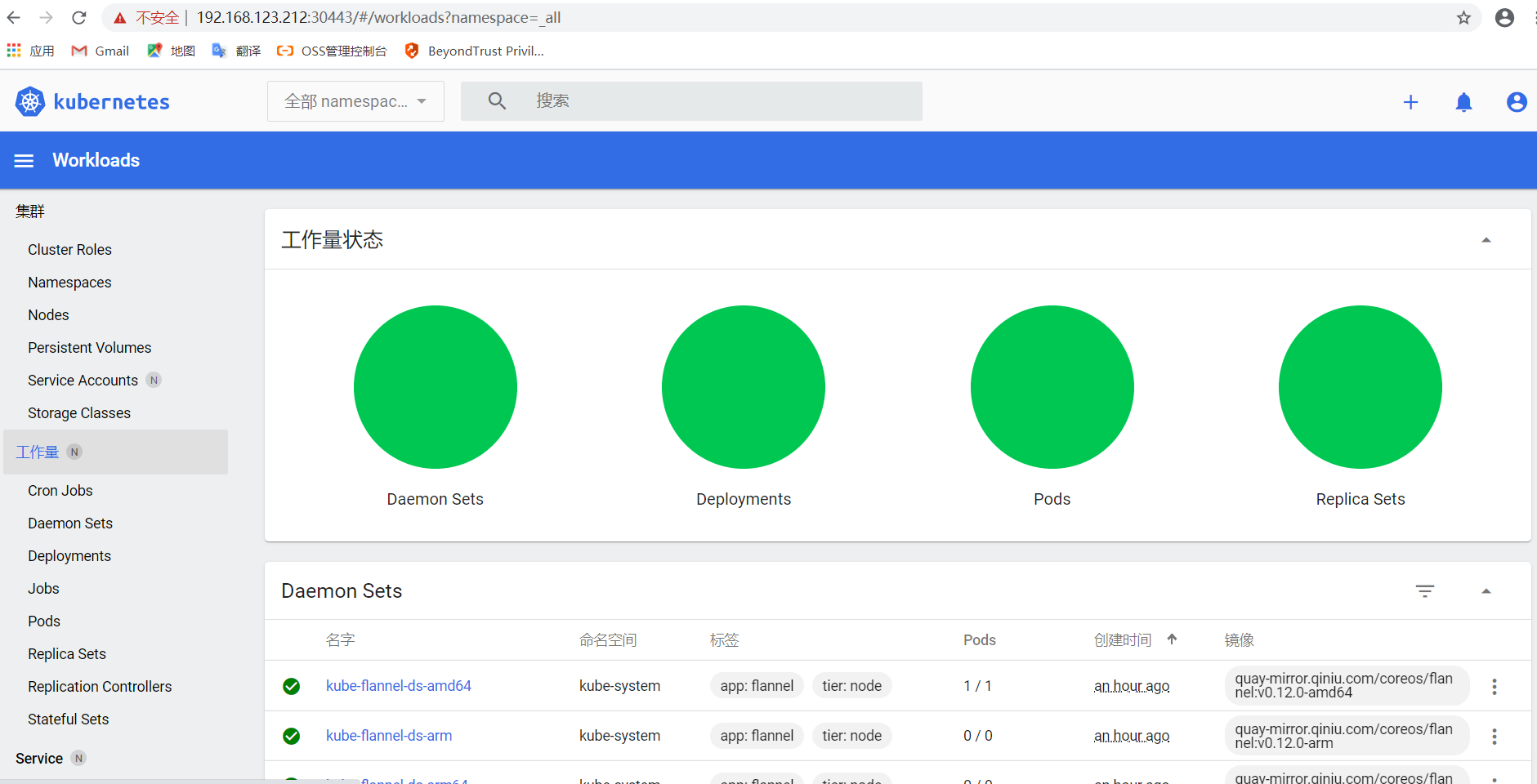
4.1- 部署 Dashboard
wget https://raw.githubusercontent.com/kubernetes/dashboard/v2.0.3/aio/deploy/recommended.yaml -O kubernetes-dashboard.yaml ##注意,
sed -i s'kubernetesui/dashboard
egistry.cn-hangzhou.aliyuncs.com/liuzheng_k8s/kubernetesui-dashboardg' kube-dashboard.yaml ##修改镜像为阿里源
sed -i s'kubernetesui/metrics-scraper
egistry.cn-hangzhou.aliyuncs.com/google_containers/metrics-scraperg' kube-dashboard.yaml
##添加services端口类型NodePort。
[root@master ~]# cat kube-dashboard.yaml -n |egrep '^39|4[0-3]'
40 type: NodePort
41 ports:
42 - port: 443
43 targetPort: 8443
44 nodePort: 30443
[root@master ~]# cat kube-dashboard.yaml |grep image image: registry.cn-hangzhou.aliyuncs.com/liuzheng_k8s/kubernetesui-dashboard:v2.0.3
imagePullPolicy: Always
image: registry.cn-hangzhou.aliyuncs.com/google_containers/metrics-scraper:v1.0.4
##注意:高版本的集群不能使用低版本的镜像,否则会web会提示404错误
##创建应用
[root@master ~]# kubectl apply -f kubernetes-dashboard.yaml
secret/kubernetes-dashboard-certs created
serviceaccount/kubernetes-dashboard created
role.rbac.authorization.k8s.io/kubernetes-dashboard-minimal created
rolebinding.rbac.authorization.k8s.io/kubernetes-dashboard-minimal created
deployment.apps/kubernetes-dashboard created
service/kubernetes-dashboard created
#查看创建情况
[root@master ~]# kubectl get pods,svc -n kubernetes-dashboard
NAME READY STATUS RESTARTS AGE
pod/coredns-554f8d5588-rxtjx 1/1 Running 0 59m
pod/coredns-554f8d5588-vpfsp 1/1 Running 0 59m
pod/etcd-master 1/1 Running 0 59m
pod/kube-apiserver-master 1/1 Running 0 59m
pod/kube-controller-manager-master 1/1 Running 0 59m
pod/kube-flannel-ds-amd64-r8td7 1/1 Running 0 45m
pod/kube-proxy-vg2tl 1/1 Running 0 59m
pod/kube-scheduler-master 1/1 Running 0 59m
pod/kubernetes-dashboard-f66795b7-xfvx6 1/1 Running 0 65s
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
service/kube-dns ClusterIP 10.10.0.10 <none> 53/UDP,53/TCP,9153/TCP 59m
service/kubernetes-dashboard NodePort 10.10.155.240 <none> 443:30443/TCP 65s
##映射的NodePort是32092
- 创建管理员账户和token
[root@master ~]# kubectl create serviceaccount dashboard-admin -n kube-system
serviceaccount/dashboard-admin created
[root@master ~]#
[root@master ~]# kubectl create clusterrolebinding dashboard-admin --clusterrole=cluster-admin --serviceaccount=kube-system:dashboard-admin
clusterrolebinding.rbac.authorization.k8s.io/dashboard-admin created
[root@master ~]#
- 查看token
[root@master ~]# kubectl get secret -n kube-system|grep dashboard
dashboard-admin-token-9dmjq kubernetes.io/service-account-token 3 3m15s
[root@master ~]# kubectl describe secret dashboard-admin-token-9dmjq -n kube-system
Name: dashboard-admin-token-9dmjq
Namespace: kube-system
Labels: <none>
Annotations: kubernetes.io/service-account.name: dashboard-admin
kubernetes.io/service-account.uid: 8573c2f7-4609-4da3-9b42-3c4d61cd3d78
Type: kubernetes.io/service-account-token
Data
====
ca.crt: 1025 bytes
namespace: 11 bytes
token: eyJhbGciOiJSUzI1NiIsImtpZCI6IlRVUlR2cmZWc016WERVazJNOWFvZkVodzZ1WnNXSlVubXVaYWpTTGt0M1kifQ.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJrdWJlLXN5c3RlbSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VjcmV0Lm5hbWUiOiJkYXNoYm9hcmQtYWRtaW4tdG9rZW4tcmJwczIiLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC5uYW1lIjoiZGFzaGJvYXJkLWFkbWluIiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZXJ2aWNlLWFjY291bnQudWlkIjoiODU3M2MyZjctNDYwOS00ZGEzLTliNDItM2M0ZDYxY2QzZDc4Iiwic3ViIjoic3lzdGVtOnNlcnZpY2VhY2NvdW50Omt1YmUtc3lzdGVtOmRhc2hib2FyZC1hZG1pbiJ9.TSszwxkh4Uryf2iL3uEla1GuI1Hpb5gbgQc3oZAMHF8HrAXGAKzZXNMCOev2Odc5k1sjjW3DCbr7vfeYi1dDJG-b2eXLoPIgoGNIu1_rdNp0mk1yKMIGMPhFW2kSY1FHABLaal6-xnUfjSjWGOep8Qn49NzGXWdmjzAFLtd3CBD_DsurVzCaSe9ey_NzZSJFnvfXXgH4sgPEGIJcDWoiwCRktgWVsOpU1aHGiyCne3JcY2KKPig8KojlHuUIT8AnbIf7xDomr-1kgU36-z3cokmemZvoYIQBcdYFi_X7V78ivakgFPIkZrlxl_aMpiNz72xEHiFjea0ihrydpxyjpQ
- 浏览器打开ip地址 https://192.168.123.212:30443