一、实验目的
1.能够运用 wireshark 对 OpenFlow 协议数据交互过程进行抓包;
2.够借助包解析工具,分析与解释 OpenFlow协议的数据包交互过程与机制。
二、实验环境
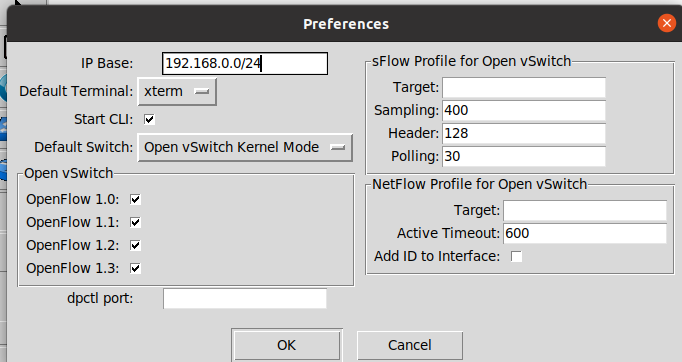
1.下载虚拟机软件Oracle VisualBox;
2.在虚拟机中安装Ubuntu 20.04 Desktop amd64,并完整安装Mininet;
三、实验要求
(一)基本要求
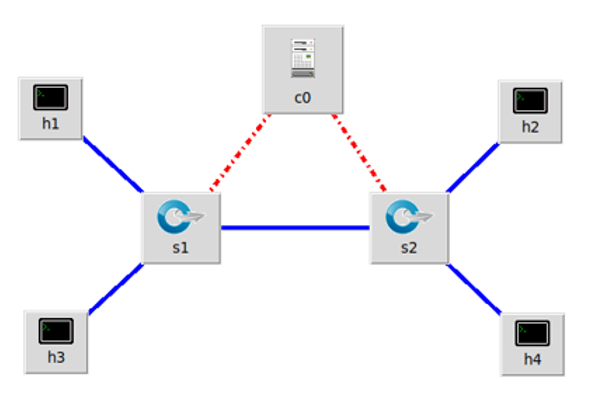
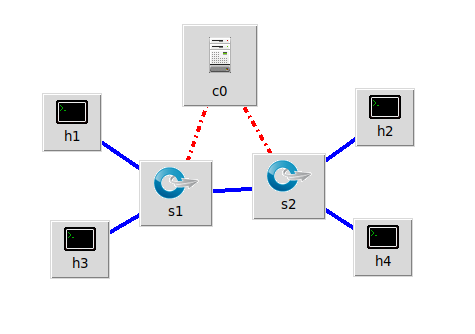
1.搭建下图所示拓扑,完成相关 IP 配置,并实现主机与主机之间的 IP 通信。用抓包软件获取控制器与交换机之间的通信数据包。
| 主机 | IP地址 |
|---|---|
| h1 | 192.168.0.101/24 |
| h2 | 192.168.0.102/24 |
| h3 | 192.168.0.103/24 |
| h4 | 192.168.0.104/24 |
| 2.保存拓扑文件 | |
 |
|
 |
|
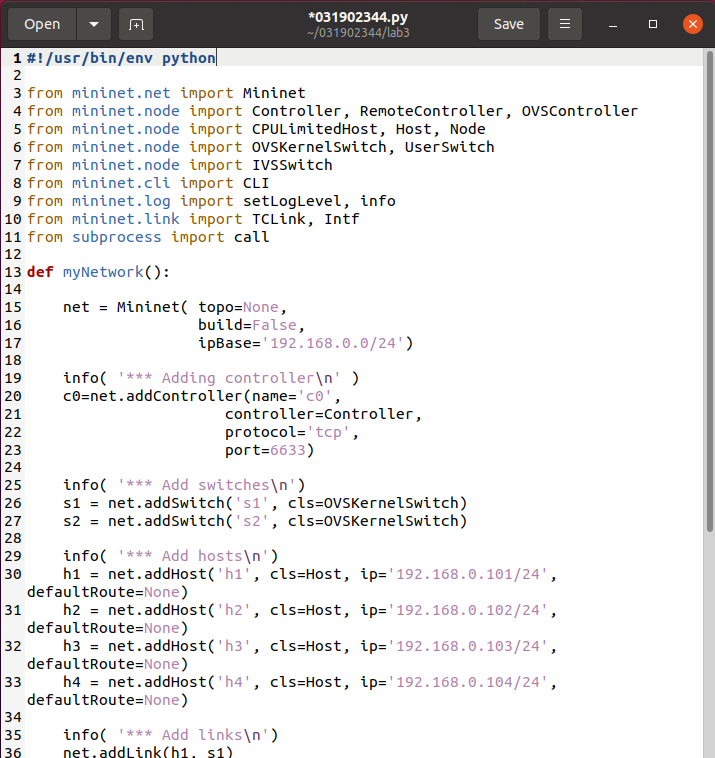 |
3.运行wireshark,选择any模式进行抓包,开启另一个终端,命令行运行031902344.py文件,运行pingall

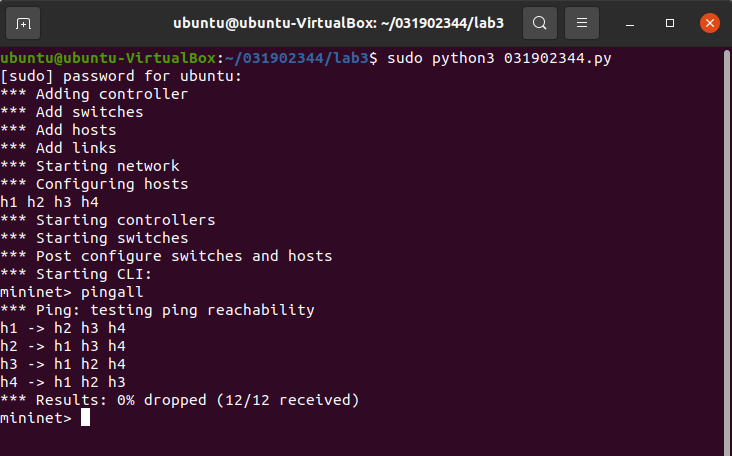
4.查看抓包结果,分析OpenFlow协议中交换机与控制器的消息交互过程
4.1.OFPT_HELLO控制器6633端口 ---> 交换机36052端口,从控制器到交换机

4.2.OFPT_HELLO 源端口36052-> 目的端口6633,从交换机到控制器,此处协议为openflow1.5

控制器与交换机建立连接,并使用OpenFlow 1.0
4.3.OFPT_FEATURES_REQUEST 源端口6633 -> 目的端口36052,从控制器到交换机
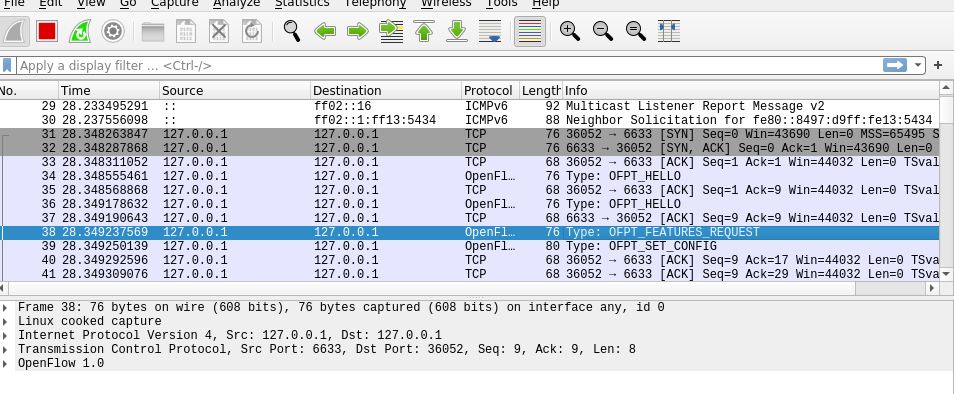
控制器请求交换器的特征信息
4.4.OFPT_SET_CONFIG 源端口6633 -> 目的端口36052,从控制器到交换机

控制器要求交换机按照所给出的信息进行配置
4.5.OFPT_PORT_STATUS 源端口36052-> 目的端口6633,从交换机到控制器

当交换机端口发生变化时,交换机告知控制器相应的端口状态
4.6.OFPT_FEATURES_REPLY 源端口36052-> 目的端口6633,从交换机到控制器

交换机告知控制器它的特征信息
4.7.OFPT_PACKET_IN 源端口36052-> 目的端口6633,从交换机到控制器
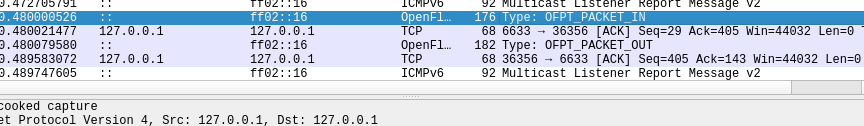
交换机告知控制器有数据包进来,请求控制器指示
4.8.OFPT_PACKET_OUT 源端口6633 -> 目的端口36052,从控制器到交换机
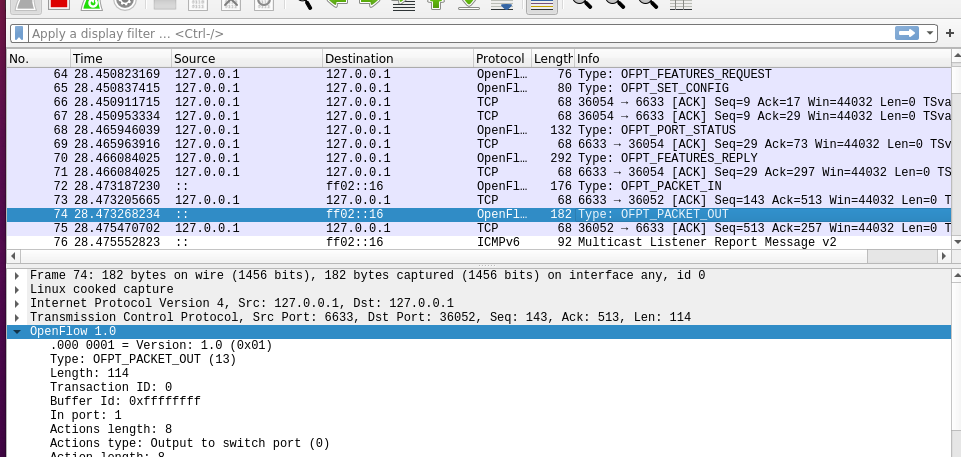
控制器要求交换机按照所给出的action进行处理
4.9.OFPT_FLOW_MOD 源端口6633 -> 目的端口36052,从控制器到交换机

控制器对交换机进行流表的添加、删除、变更等操作

5.交换机与控制器建立通信时是使用TCP协议还是UDP协议?
如图所示为TCP协议

(二)进阶要求
将抓包结果对照OpenFlow源码,了解OpenFlow主要消息类型对应的数据结构定义。
1.HELLO

struct ofp_header {
uint8_t version; /* OFP_VERSION. */
uint8_t type; /* One of the OFPT_ constants. */
uint16_t length; /* Length including this ofp_header. */
uint32_t xid; /* Transaction id associated with this packet.
Replies use the same id as was in the request
to facilitate pairing. */
};
2.FEATURES_REQUEST
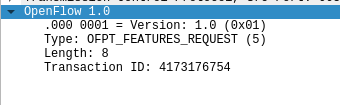
代码同上
3.SET_CONFIG
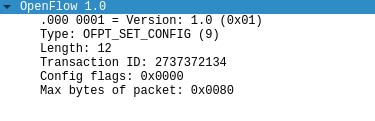
/* Switch configuration. */
struct ofp_switch_config {
struct ofp_header header;
uint16_t flags; /* OFPC_* flags. */
uint16_t miss_send_len; /* Max bytes of new flow that datapath should
send to the controller. */
};
4.PORT_STATUS
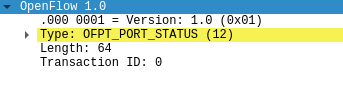
struct ofp_port_status {
struct ofp_header header;
uint8_t reason; /* One of OFPPR_*. */
uint8_t pad[7]; /* Align to 64-bits. */
struct ofp_phy_port desc;
};
5.FEATURES_REPLY

/* Description of a physical port */
struct ofp_phy_port {
uint16_t port_no;
uint8_t hw_addr[OFP_ETH_ALEN];
char name[OFP_MAX_PORT_NAME_LEN]; /* Null-terminated */
uint32_t config; /* Bitmap of OFPPC_* flags. */
uint32_t state; /* Bitmap of OFPPS_* flags. */
/* Bitmaps of OFPPF_* that describe features. All bits zeroed if
* unsupported or unavailable. */
uint32_t curr; /* Current features. */
uint32_t advertised; /* Features being advertised by the port. */
uint32_t supported; /* Features supported by the port. */
uint32_t peer; /* Features advertised by peer. */
};
/* Switch features. */
struct ofp_switch_features {
struct ofp_header header;
uint64_t datapath_id; /* Datapath unique ID. The lower 48-bits are for
a MAC address, while the upper 16-bits are
implementer-defined. */
uint32_t n_buffers; /* Max packets buffered at once. */
uint8_t n_tables; /* Number of tables supported by datapath. */
uint8_t pad[3]; /* Align to 64-bits. */
/* Features. */
uint32_t capabilities; /* Bitmap of support "ofp_capabilities". */
uint32_t actions; /* Bitmap of supported "ofp_action_type"s. */
/* Port info.*/
struct ofp_phy_port ports[0]; /* Port definitions. The number of ports
is inferred from the length field in
the header. */
};
6.PACKET_IN

struct ofp_packet_in {
struct ofp_header header;
uint32_t buffer_id; /* ID assigned by datapath. */
uint16_t total_len; /* Full length of frame. */
uint16_t in_port; /* Port on which frame was received. */
uint8_t reason; /* Reason packet is being sent (one of OFPR_*) */
uint8_t pad;
uint8_t data[0]; /* Ethernet frame, halfway through 32-bit word,
so the IP header is 32-bit aligned. The
amount of data is inferred from the length
field in the header. Because of padding,
offsetof(struct ofp_packet_in, data) ==
sizeof(struct ofp_packet_in) - 2. */
};
7.PACKET_OUT
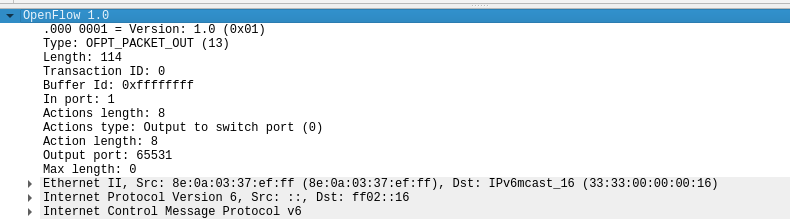
struct ofp_packet_out {
struct ofp_header header;
uint32_t buffer_id; /* ID assigned by datapath (-1 if none). */
uint16_t in_port; /* Packet's input port (OFPP_NONE if none). */
uint16_t actions_len; /* Size of action array in bytes. */
struct ofp_action_header actions[0]; /* Actions. */
/* uint8_t data[0]; */ /* Packet data. The length is inferred
from the length field in the header.
(Only meaningful if buffer_id == -1.) */
};
8.FLOW_MOD
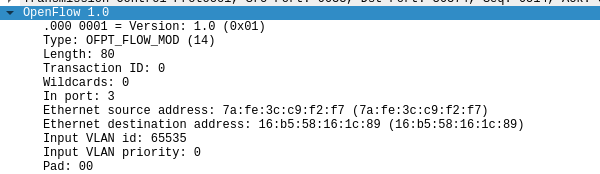
/* Flow setup and teardown (controller -> datapath). */
struct ofp_flow_mod {
struct ofp_header header;
struct ofp_match match; /* Fields to match */
uint64_t cookie; /* Opaque controller-issued identifier. */
/* Flow actions. */
uint16_t command; /* One of OFPFC_*. */
uint16_t idle_timeout; /* Idle time before discarding (seconds). */
uint16_t hard_timeout; /* Max time before discarding (seconds). */
uint16_t priority; /* Priority level of flow entry. */
uint32_t buffer_id; /* Buffered packet to apply to (or -1).
Not meaningful for OFPFC_DELETE*. */
uint16_t out_port; /* For OFPFC_DELETE* commands, require
matching entries to include this as an
output port. A value of OFPP_NONE
indicates no restriction. */
uint16_t flags; /* One of OFPFF_*. */
struct ofp_action_header actions[0]; /* The action length is inferred
from the length field in the
header. */
};
实验总结
1.本次实验遇到的问题:
本次实验难度适中,总体实验过程流畅,没有很大的问题。
2.实验心得:
通过本次实验,我们学会了运用 wireshark 对 OpenFlow 协议数据交互过程进行抓包,了解如何借助包解析工具,分析与解释 OpenFlow协议的数据包交互过程与机制,对wireshark的使用更加熟练。在本次实验中,我第一次抓包之后有几个数据没有记录,然后进行了第二次抓包,发现端口号有变化。为了让实验结果更加具有可读性,只能把数据再次全部截图。这提醒我记录数据要完整有连贯性,少记录一个数据可能整组数据就没有用了。本次实践进一次锻炼了我们的能力,相信这对我们未来的学习将会有很大的帮助。