攻防世界-web-新手训练12题
(以下解题基于firefox浏览器)
题目一网址:
https://adworld.xctf.org.cn/task/answer?type=web&number=3&grade=0&id=5061&page=1
解题过程:
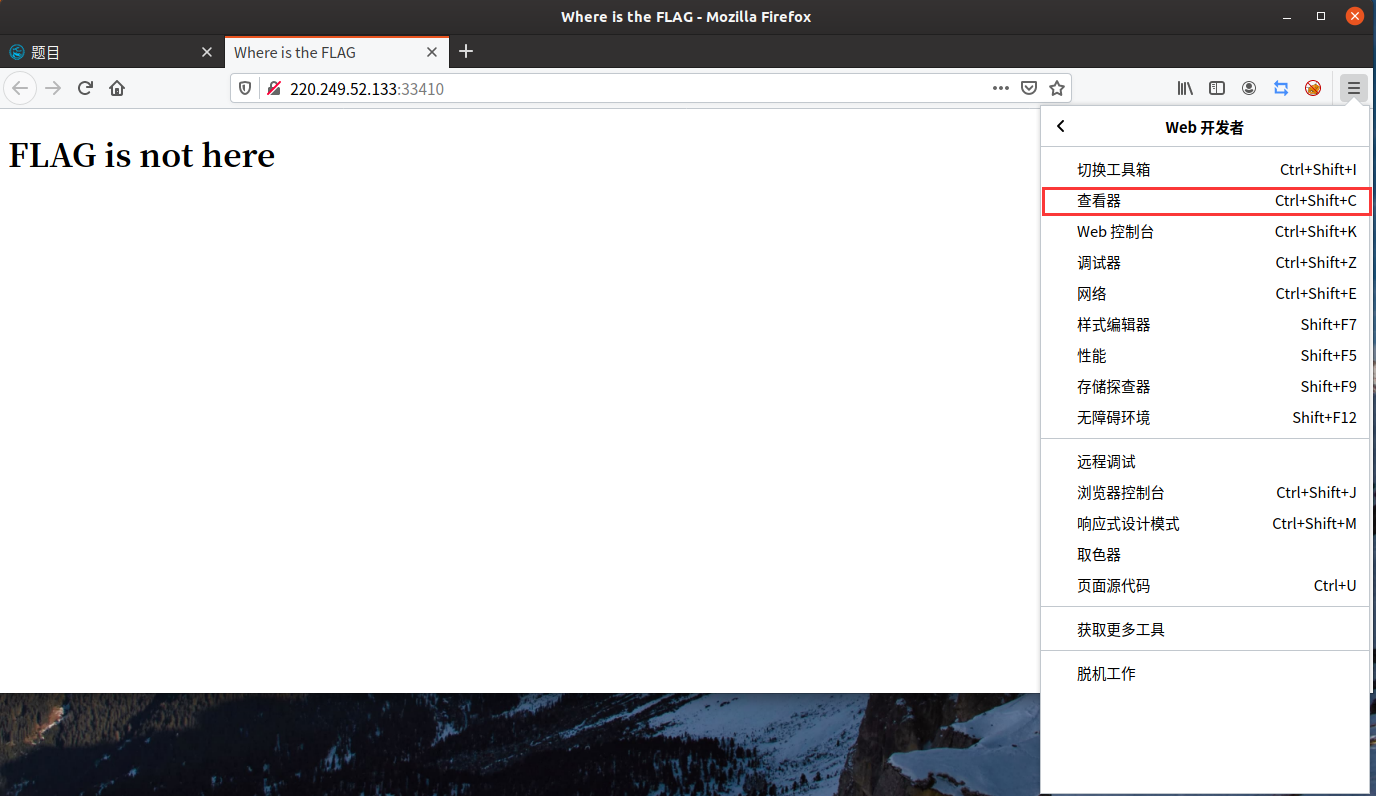
题目要求查看网页源代码,但提示右键不可用,这时选择用菜单打开查看器
具体操作:打开菜单-->Web开发者-->查看器(或者快捷键ctrl+shift+c)
注释中找到flag:cyberpeace{7aa273be6b275511e1611780a2d4c09c}
图片提示:

---------------------------------------------------------------------------------------------------

---------------------------------------------------------------------------------------------------
---------------------------------------------------------------------------------------------------
---------------------------------------------------------------------------------------------------
题目二网址:
https://adworld.xctf.org.cn/task/answer?type=web&number=3&grade=0&id=5062&page=1
解题过程:
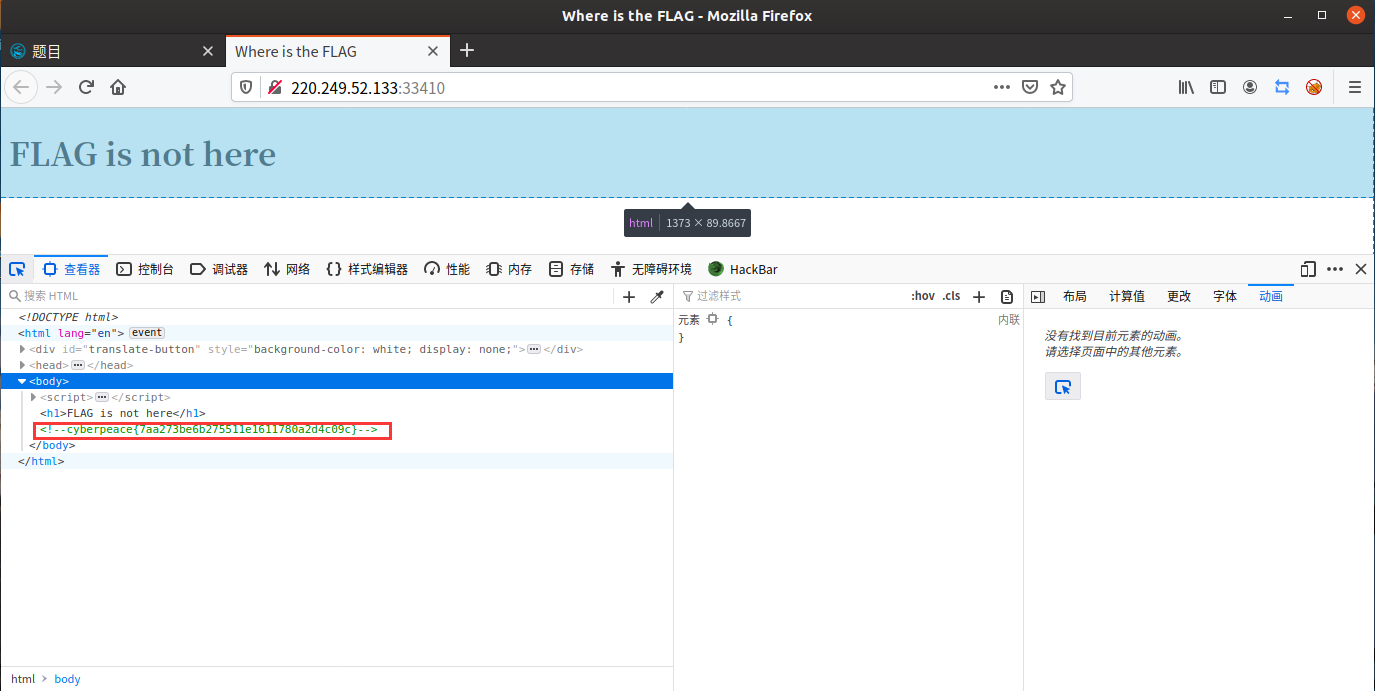
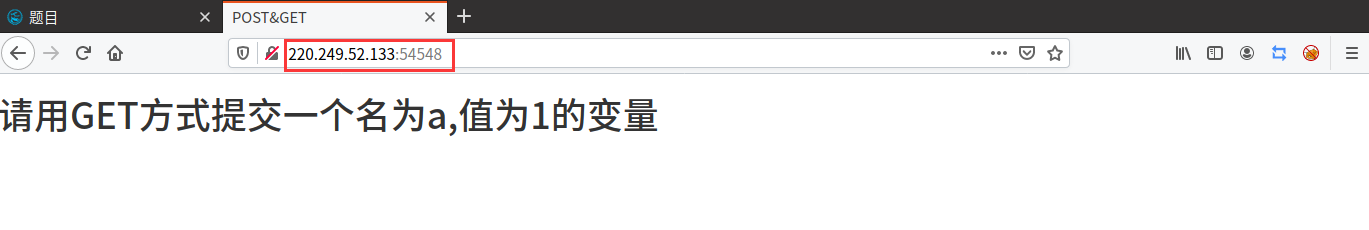
题目问HTTP通常使用的两种请求方法,是GET和POST
第一步:
用GET方式提交一个名为a,值为1的变量
GET:在ip网址后加 /?a=1 或者 /index.php?a=1
(index.php是首页的意思)
第二步:
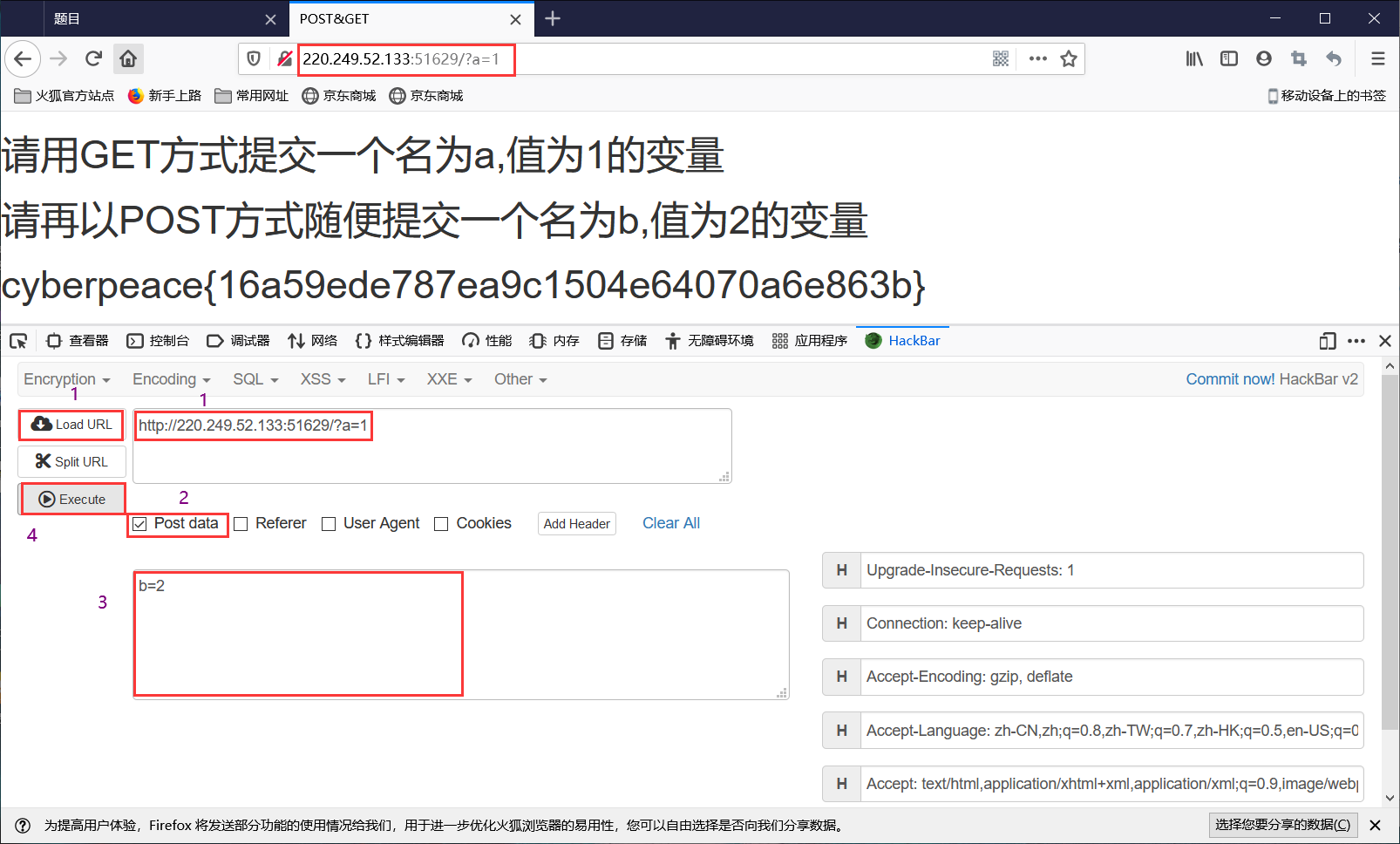
先下载一个HackBar V2(免费),https://addons.mozilla.org/zh-CN/firefox/addon/hackbar-free/?src=search
火狐:菜单-->附加组件-->扩展-->搜索HackBar V2-->选择并添加-->确认
请再以POST方式随便提交一个名为b,值为2的变量
打开查看器,HackBar V2在最右面,点击,选择Load URL,选Post data,输入b=2,点击Execute
得到cyberpeace{16a59ede787ea9c1504e64070a6e863b}
图片提示:
--------------------------------------------------------------------------------------------

--------------------------------------------------------------------------------------------
--------------------------------------------------------------------------------------------
题目三网址:
https://adworld.xctf.org.cn/task/answer?type=web&number=3&grade=0&id=5063&page=1
解题过程:
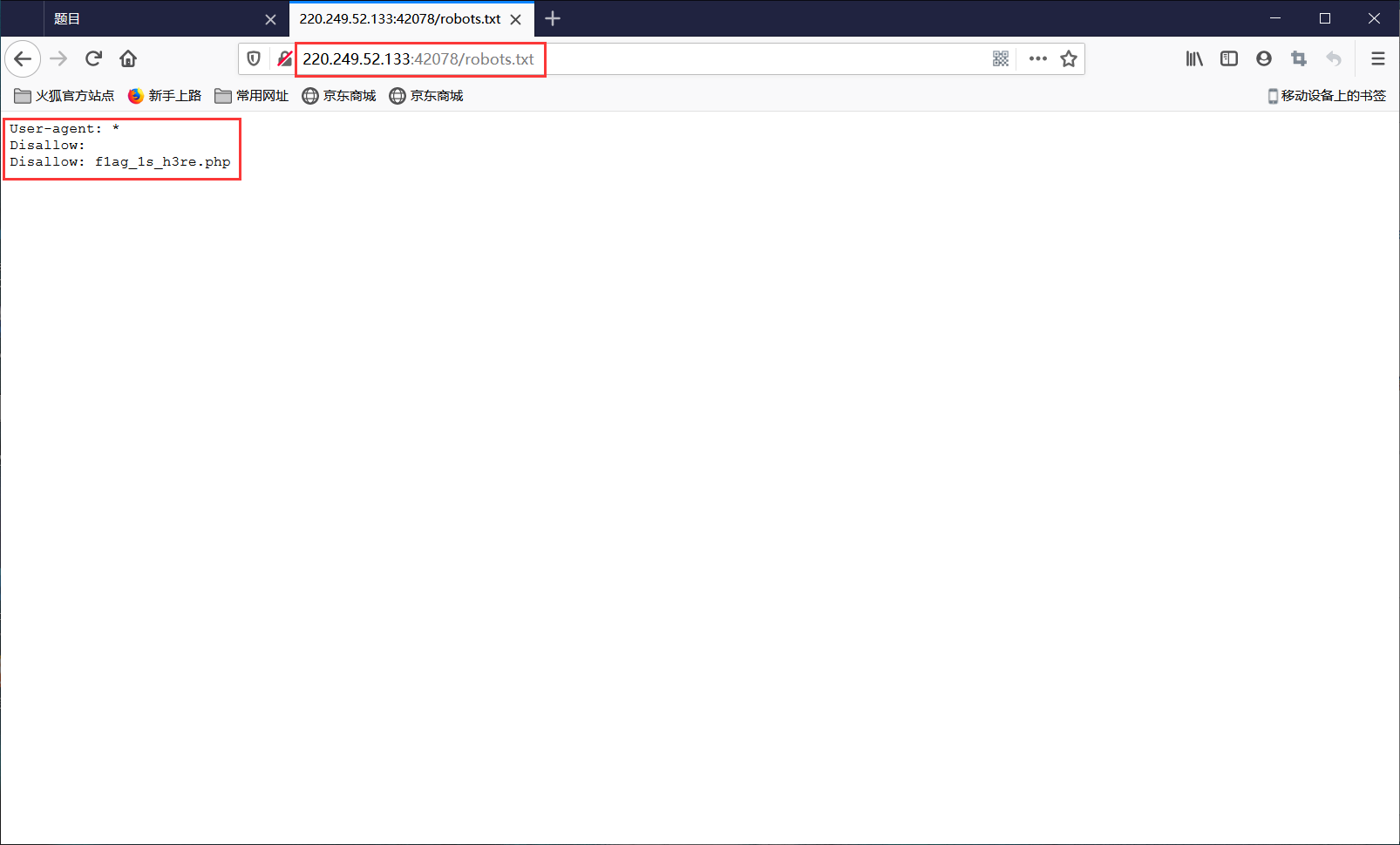
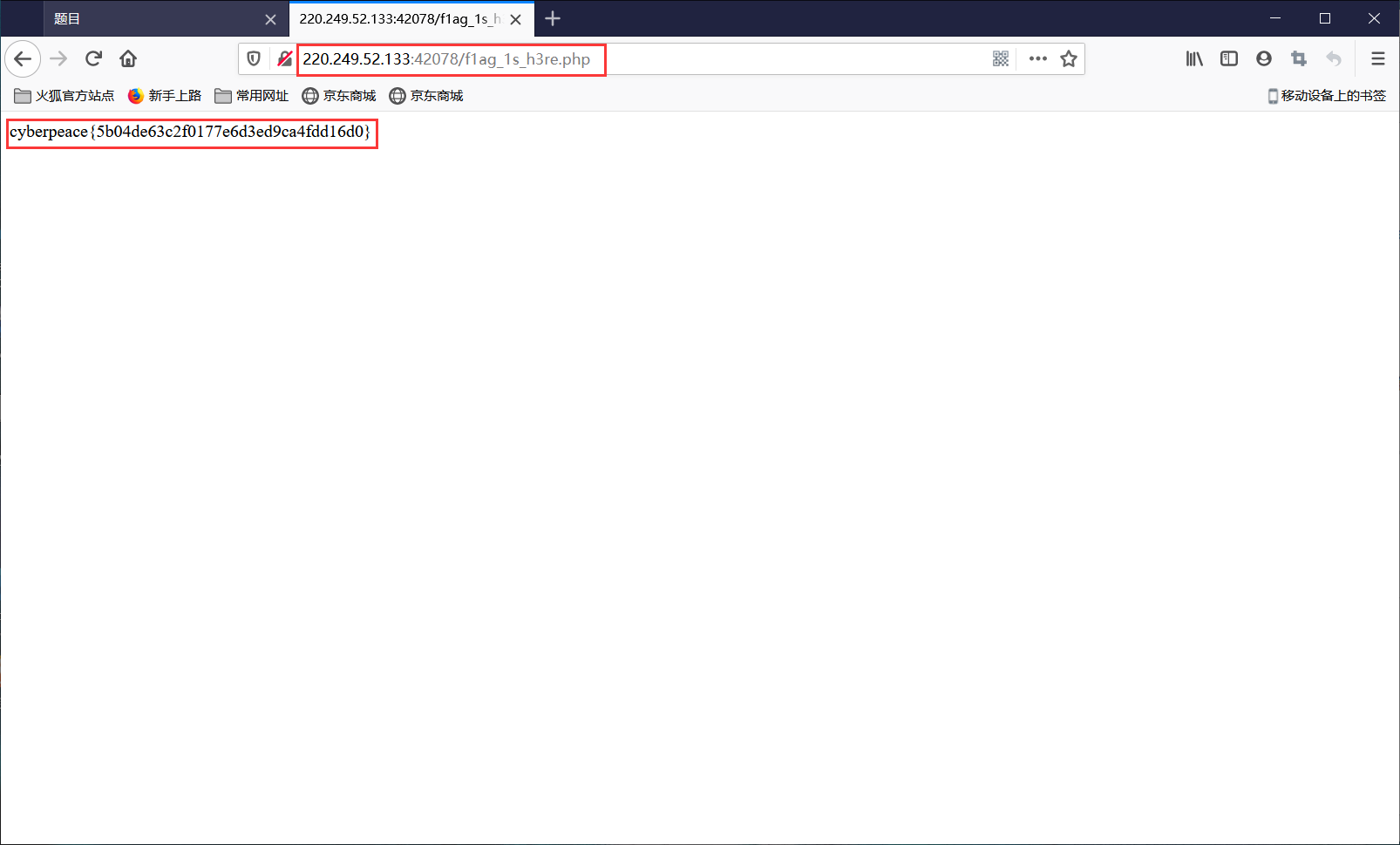
题目提到Robots协议,百度百科:
https://baike.baidu.com/item/robots%E5%8D%8F%E8%AE%AE/2483797?fr=aladdin#8_2
在网址后面加 /robots.txt进入后发现只有 f1ag_1s_h3re.php 文件,在原来的网址后加 /f1ag_1s_h3re.php,进入看到 cyberpeace{5b04de63c2f0177e6d3ed9ca4fdd16d0}
图片提示:
--------------------------------------------------------------------------------------------
--------------------------------------------------------------------------------------------
题目四网址:
https://adworld.xctf.org.cn/task/answer?type=web&number=3&grade=0&id=5064&page=1
解题过程:
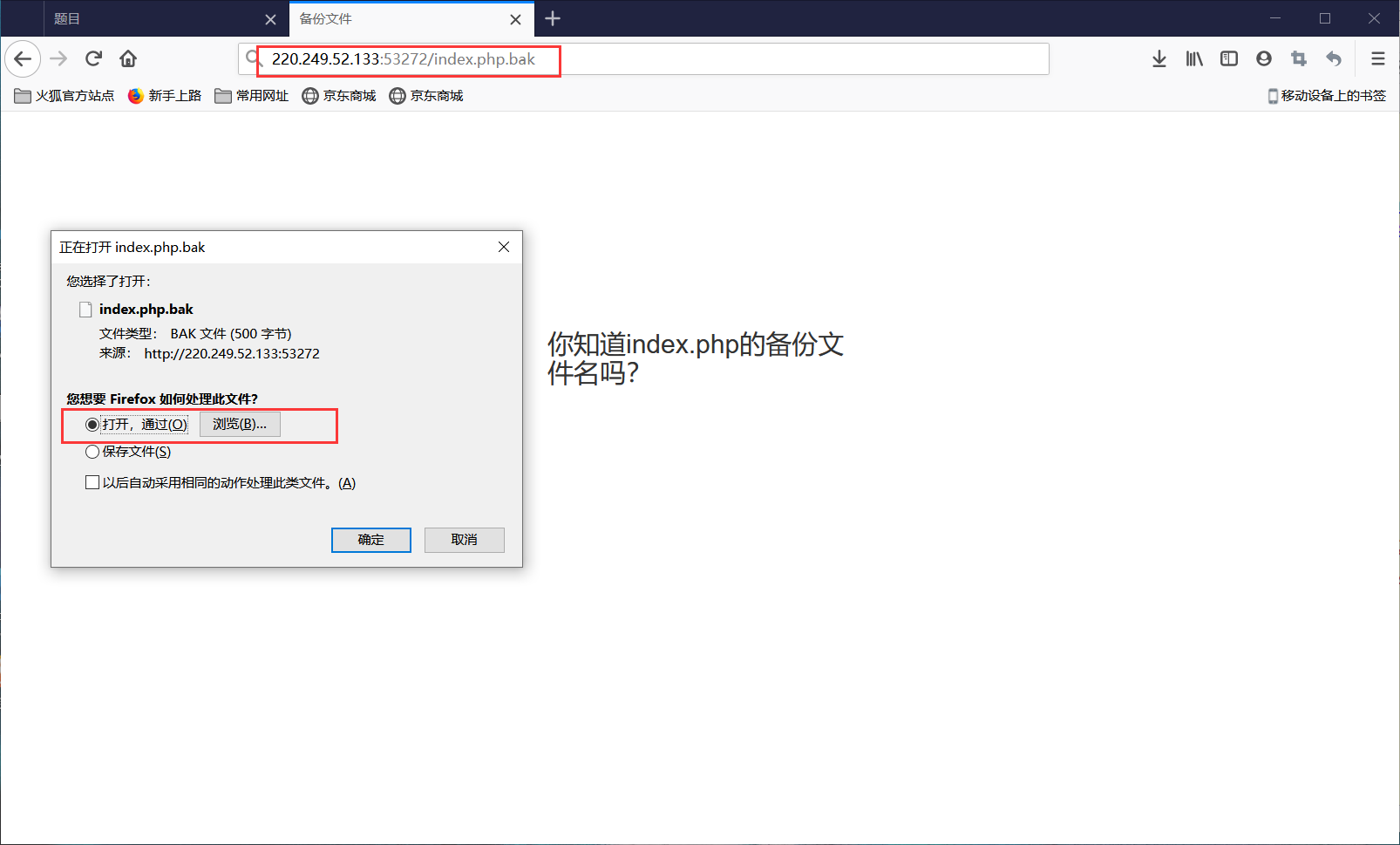
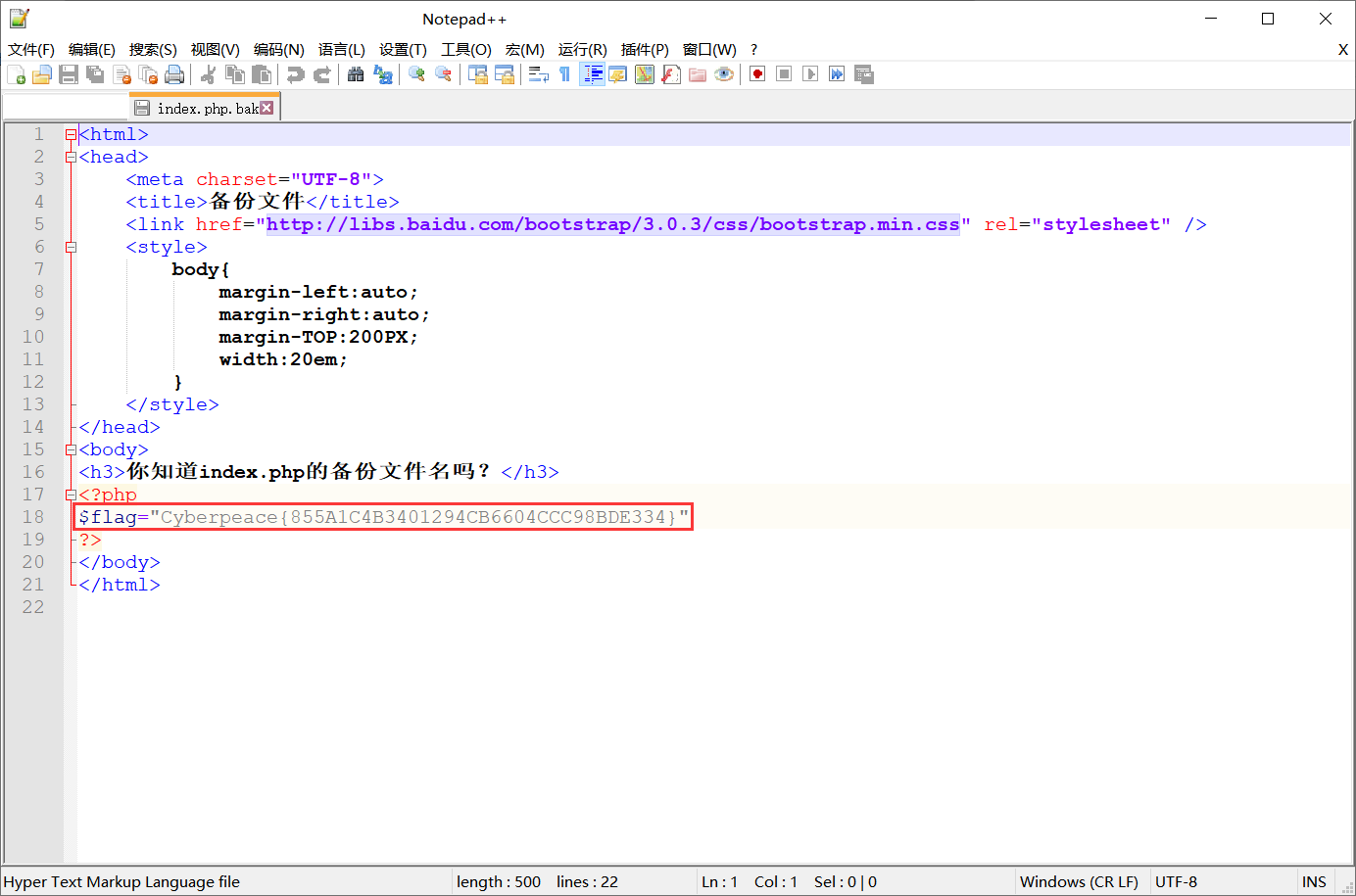
题目提示忘记删除备份文件,找到备份文件
提示index.php的备份文件,通常备份文件以 .bak 结尾,在网址后加 /index.php.bak ,跳出弹窗打开文件,选择“打开,通过-文本编辑器”,在注释中看到 flag="Cyberpeace{855A1C4B3401294CB6604CCC98BDE334}"
图片提示:

--------------------------------------------------------------------------------------------
--------------------------------------------------------------------------------------------
--------------------------------------------------------------------------------------------
题目五网址:
https://adworld.xctf.org.cn/task/answer?type=web&number=3&grade=0&id=5065&page=1
解题过程:
题目里出现cookie,百度百科:
https://baike.baidu.com/item/cookie/1119?fr=aladdin;
好好了解一下Cookie(强烈推荐):https://blog.csdn.net/zhangquan_zone/article/details/77627899
服务器端向客户端发送Cookie是通过HTTP响应报文实现的,在Set-Cookie中设置需要向客户端发送的cookie,这个在开发者选项的网络查看
具体操作:打开菜单-->Web开发者-->网络(或者快捷键ctrl+shift+e)
打开之后选择重新载入,选择第一个状态为200的,在消息头的响应头中找到 Set-Cookie:look-here=cookie.php ,在网址后加 /cookie.php 进入看到 “See the http response” ,在网络消息头的响应头中找到 flag:cyberpeace{fd8e6890540c0680f316ac2bdb5c97c6}
图片提示:

----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------
题目六网址:
https://adworld.xctf.org.cn/task/answer?type=web&number=3&grade=0&id=5066&page=1
解题过程:
题目提示前端知识,进入后看到“一个不能按的按钮flag”,打开网页查看器,看到 disabled="" ,双击disabled,改成abled,回车,这时flag可以按了,点击flag得到 cyberpeace{7cca50f9aeeb7ad671d21d3d71ea9ac8}
图片提示:

----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------
题目七网址:
https://adworld.xctf.org.cn/task/answer?type=web&number=3&grade=0&id=5069&page=1
解题过程:
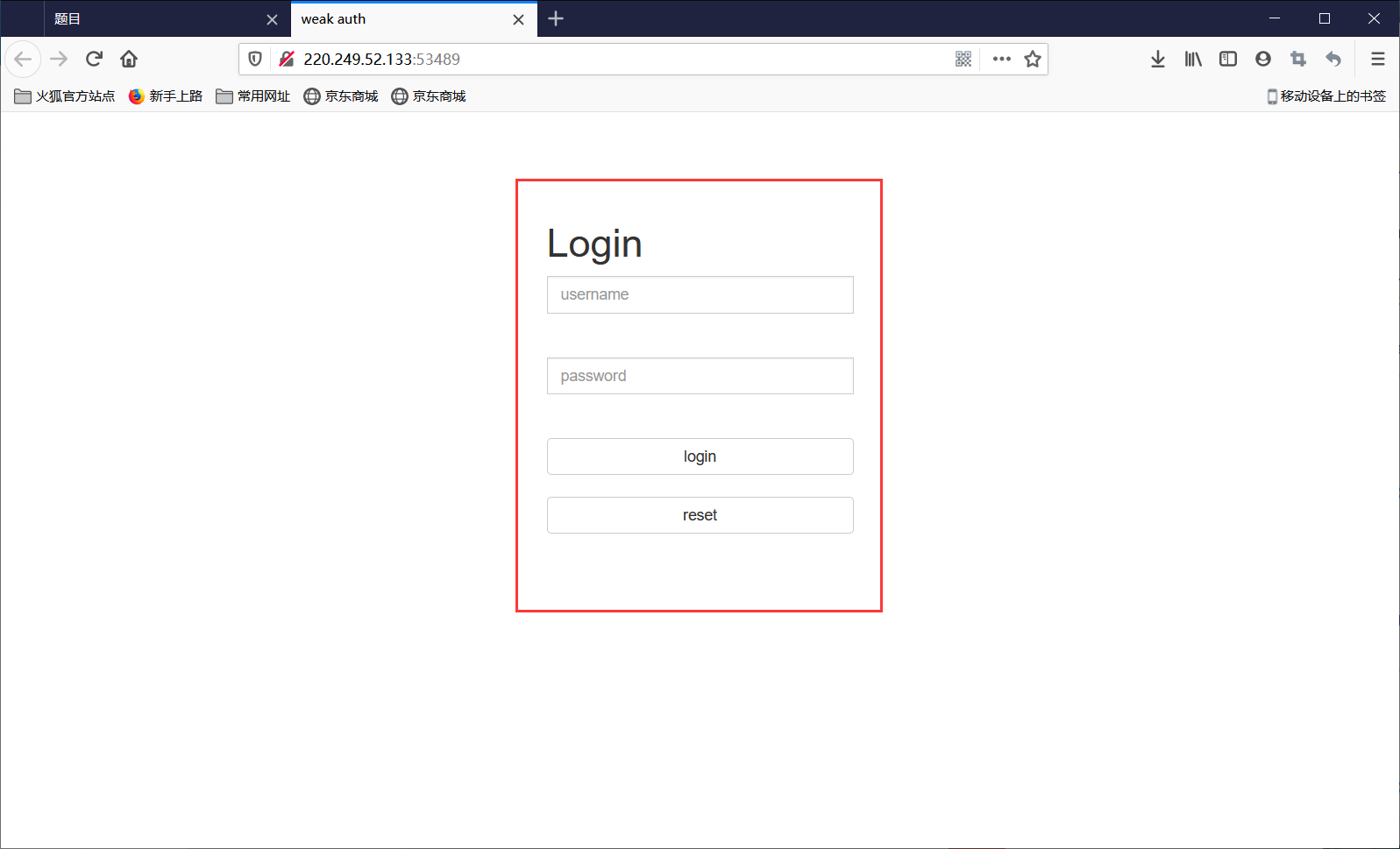
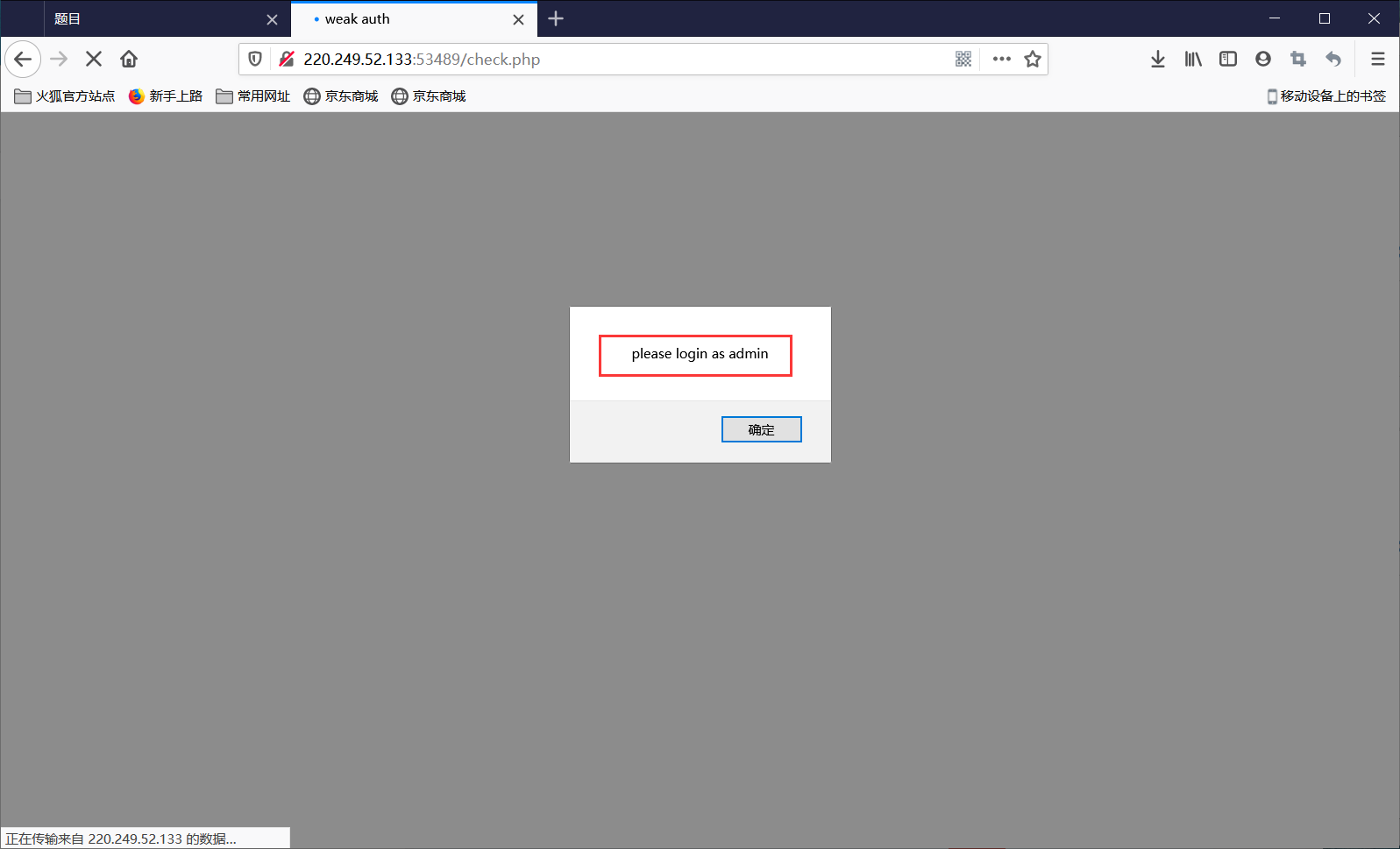
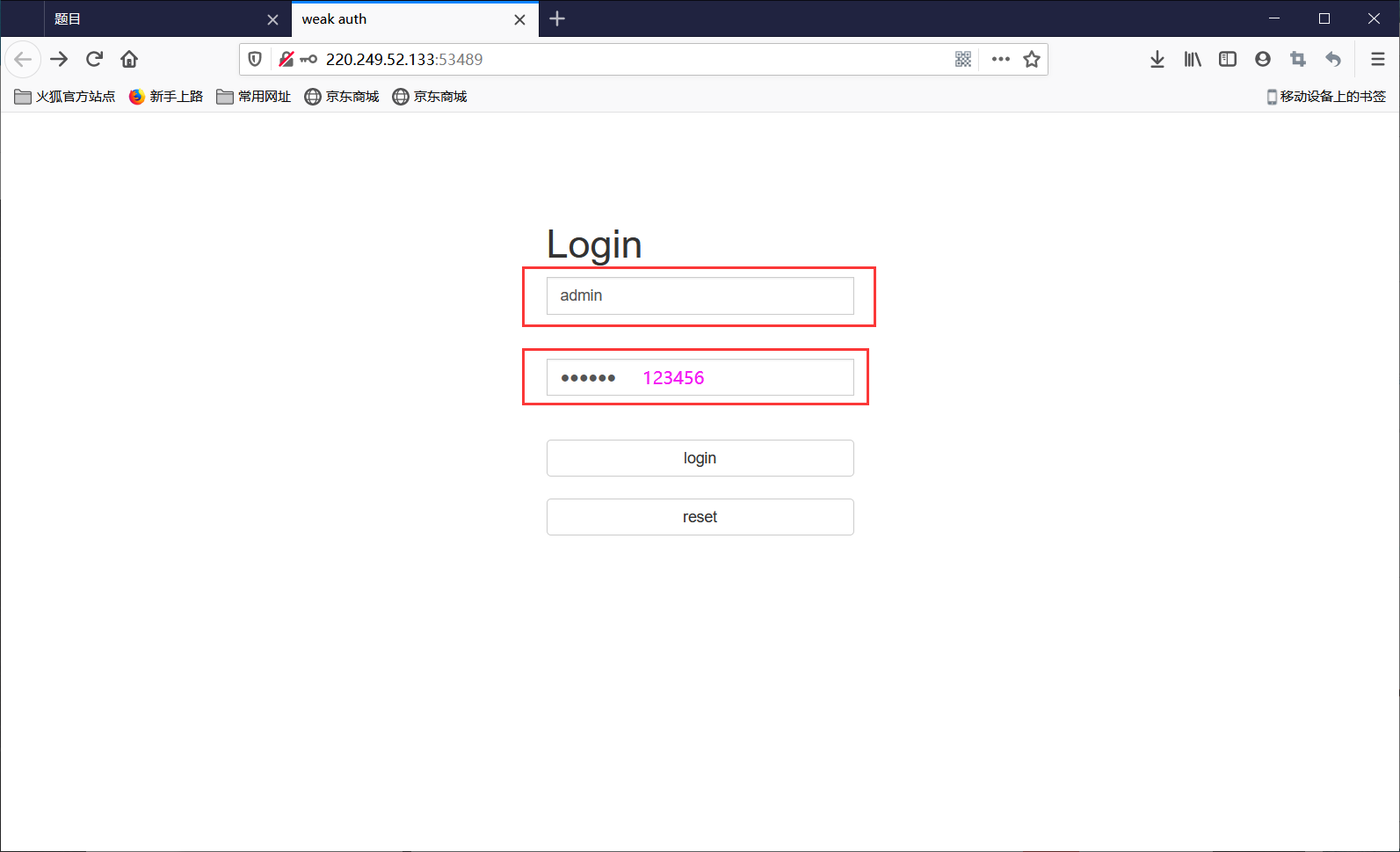
题目提示登陆验证页面,随手设了一个密码。题目是weak auth(弱口令)。
在页面随便输入名字和密码:user和12345,得到提示:please login as admin。退回到输入页面,名字输:admin,密码选择简单的连续数字,多试几次,最后123456成功。登录得到 cyberpeace{10ef9544431a68e2f2c77560e6ab42f1}
图片提示:
----------------------------------------------------------------------------------------------------------
----------------------------------------------------------------------------------------------------------
----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------
题目八网址:
https://adworld.xctf.org.cn/task/answer?type=web&number=3&grade=0&id=5071&page=1
解题过程:
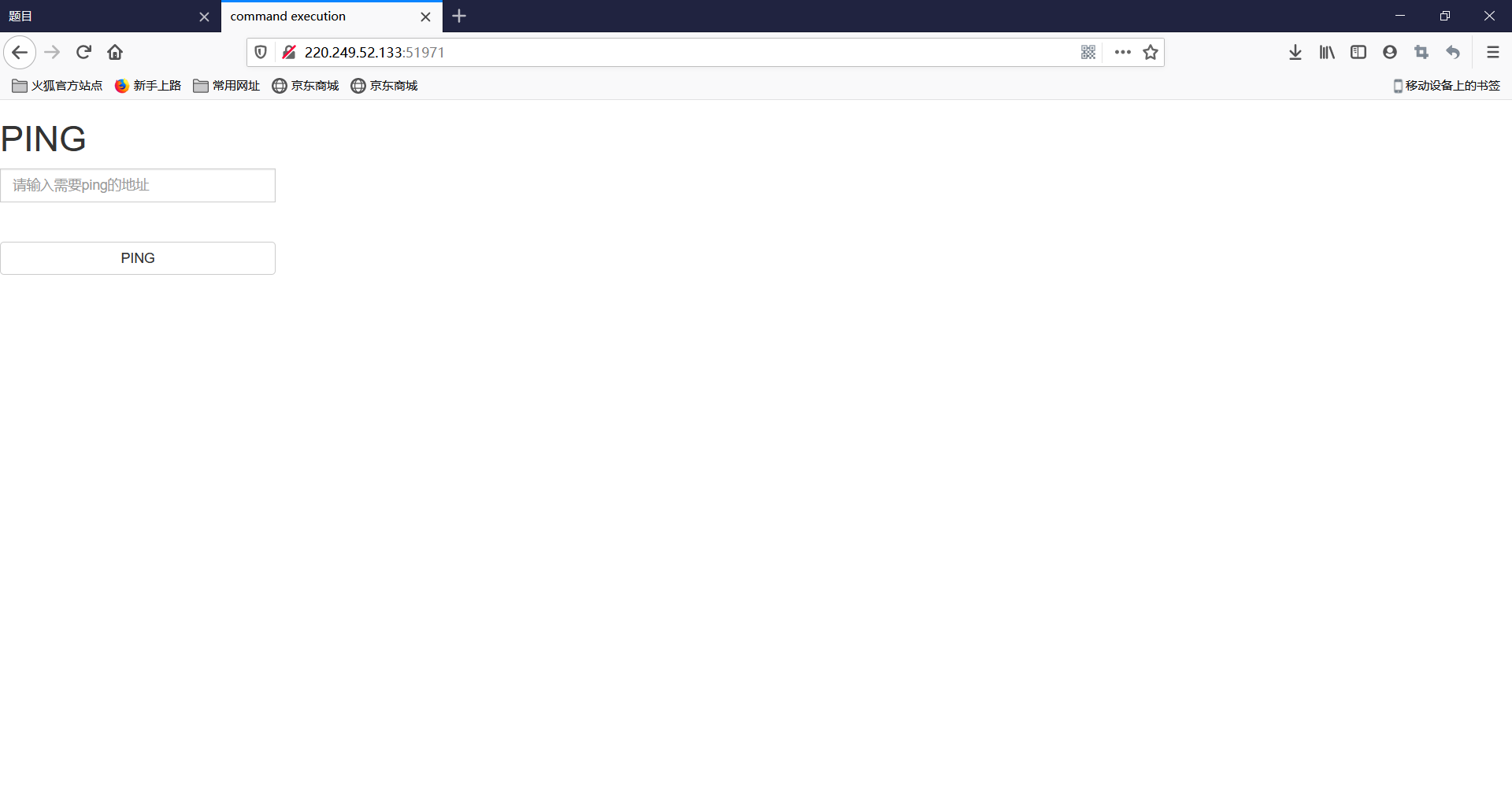
小宁写了个ping功能,但没有写waf,X老师告诉她这是非常危险的
攻防世界 web command_execution:
https://blog.csdn.net/weixin_43092232/article/details/104595830
Linux命令行:find的26个用法示例!
https://blog.csdn.net/FULqzD8d82PcCC/article/details/78956533
进入后先ping一下127.0.0.1:ping 127.0.0.1,可以成功。使用find命令查找flag文件,ping 127.0.0.1 | find / -name "flag.*",成功找到 /home/flag.txt,然后输入:ping 127.0.0.1 | cat /home/flag.txt,获取flag.txt内容:cyberpeace{ef556294fce99b4f1c45739b0fe3410c}
图片提示:
----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------
题目九网址:
https://adworld.xctf.org.cn/task/answer?type=web&number=3&grade=0&id=5072&page=1
解题过程:
php中的== 和 ===的用法及区别:
https://blog.csdn.net/caoyouming0609/article/details/77822919
提示php简单语法,进入之后看到php代码,flag由两部分组成,
$a==0 and $a :要求a等于0,并且a是TRUE,php是弱语言,在执行关系运算“==”时要求运算符两边的数据类型必须一致,如果等号右边是字符串abc,会被强制转换为了整型0,但字符串是TRUE。
is_numeric($b) :is_numeric() 函数用于检测变量是否为数字或数字字符串。如果指定的变量是数字和数字字符串则返回TRUE,否则返回FALSE。
$b>1234 :b要大于1234,上面要求不能是数字和数字字符串,所以数字后面加字母就行:1345a。
$a=@$_GET['a'];$b=@$_GET['b']; :GET方式输入a和b,/?a=abc&b=1345a
页面显示:Cyberpeace{647E37C7627CC3E4019EC69324F66C7C}
图片提示:

----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------
题目十网址:
[https://adworld.xctf.org.cn/task/answer?type=web&number=3&grade=0&id=5072&page=1](https://adworld.xctf.org.cn/task/answer?type=web&number=3&grade=0&id=5068&page=1)
解题过程:
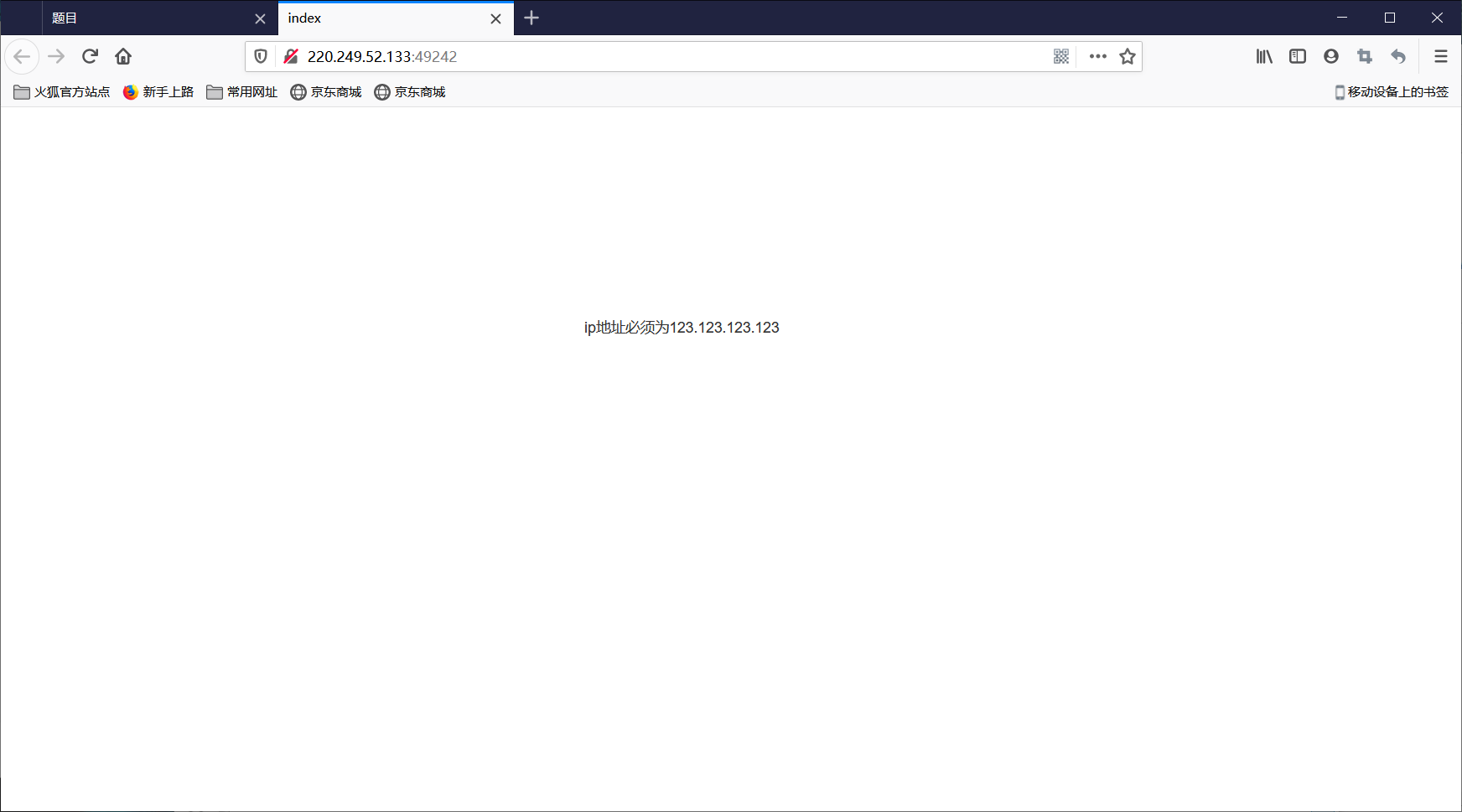
提示:xff和referer是可以伪造的
WEB安全-伪造X-Forwarded-For绕过服务器IP地址过滤:
https://www.jianshu.com/p/98c08956183d
HTTP_REFERER的用法及伪造
https://blog.csdn.net/u011250882/article/details/49679535
提示ip地址必须为123.123.123.123,在开发者选项中选HackBar,Load URL->找 X-Forwarded-For:,后面改成 123.123.123.123->Execute,出现 必须来自https://www.google.com;选Referer->R->后面改成 https://www.google.com->Execute;出现cyberpeace{5eaec471c77190975462ba5e4f6b23b0}。
图片提示:
----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------
题目十一网址:
https://adworld.xctf.org.cn/task/answer?type=web&number=3&grade=0&id=5070&page=1
解题过程:
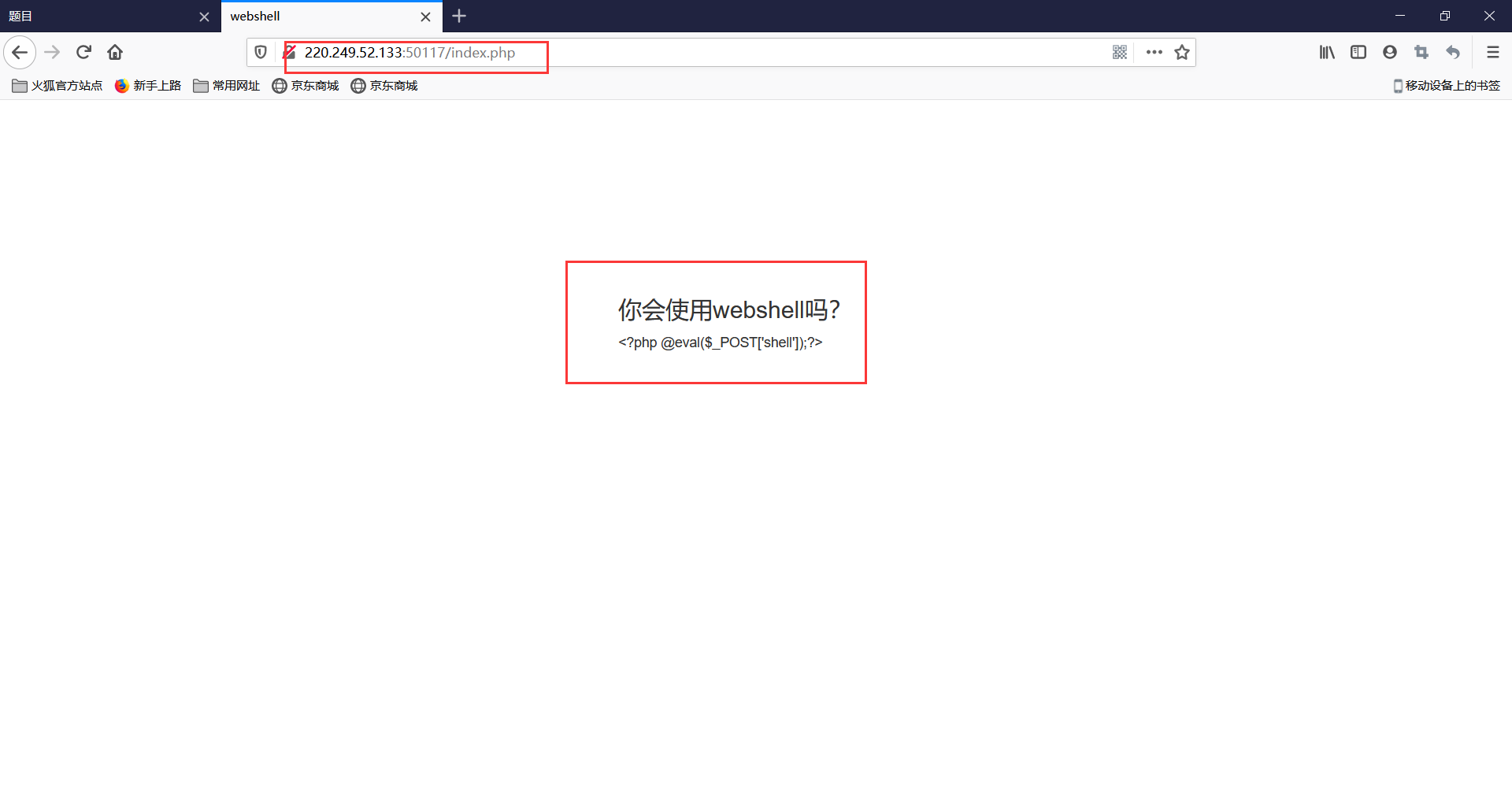
提示:php一句话,觉着很有意思,并且把它放在index.php里
PHP之一句话木马:
打开进入网页,/index.php进入新网页,看到 <?php eval(@$_POST['shell']); ?>,这个一句话木马可以通过POST,向网站提交查看文件的请求,打开HackBar->Load URL->选择post data->输入 shell=system(ls);,看到网页出现flag.txt,在原网址后加 /flag.txt,看到cyberpeace{9bc0eb08d1eb24f1aeaac411ce29fac7}
图片提示:

----------------------------------------------------------------------------------------------------------
----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------
题目十二网址:
https://adworld.xctf.org.cn/task/answer?type=web&number=3&grade=0&id=5067&page=1
解题过程:
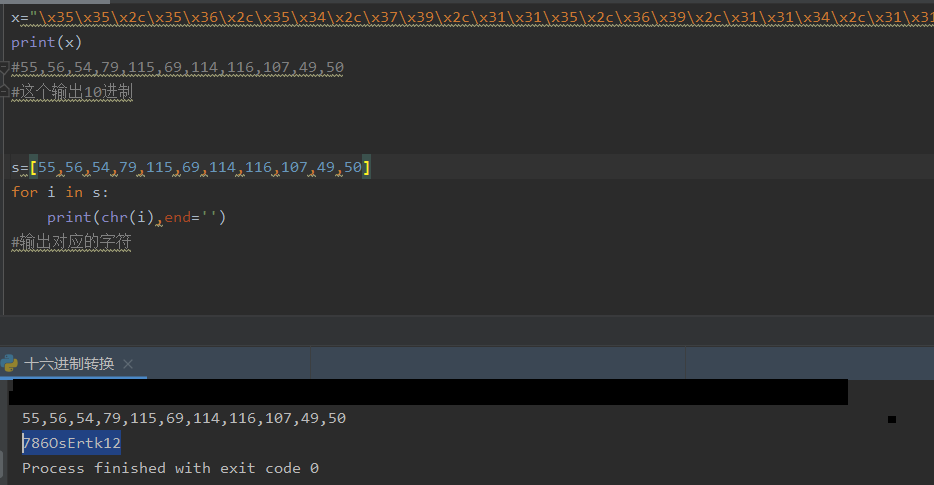
提示一直输不对密码。(Flag格式为 Cyberpeace{xxxxxxxxx} )
随便输入一串密码,显示 FAUX PASSWORD HAHA,web开发者->页面源代码,分析之后看出function dechiffre()函数没有用,alert(dechiffre(h))输出弹窗和 FAUX PASSWORD HAHA,真flag是 "x35x35x2cx35x36x2cx35x34x2cx37x39x2cx31x31x35x2cx36x39x2cx31x31x34x2cx31x31x36x2cx31x30x37x2cx34x39x2cx35x30",这是十六进制编码,用ASCII表查看,得到字符串 "55,56,54,79,115,69,114,116,107,49,50",再用这个十进制数字串,得到ASCII字符串:786OsErtk12,加上壳就是flag:Cyberpeace{786OsErtk12}
图片提示:

----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------

----------------------------------------------------------------------------------------------------------
----------------------------------------------------------------------------------------------------------