准备cfssl环境
wget https://pkg.cfssl.org/R1.2/cfssl_linux-amd64 -O /usr/local/bin/cfssl
wget https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64 -O /usr/local/bin/cfssljson
wget https://pkg.cfssl.org/R1.2/cfssl-certinfo_linux-amd64 -O /usr/local/bin/cfssl-certinfo
chmod +x /usr/local/bin/cfssl*
生成ca证书
cd;mkdir keys;cd keys
cat > ca-config.json <<EOF
{
"signing": {
"default": {
"expiry": "8760h"
},
"profiles": {
"app": {
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
],
"expiry": "8760h"
}
}
}
}
EOF
cat > ca-csr.json <<EOF
{
"CN": "k8s",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "BeiJing",
"L": "BeiJing",
"O": "k8s",
"OU": "System"
}
]
}
EOF
cfssl gencert -initca ca-csr.json | cfssljson -bare ca
生成server证书
cd /root/keys
cat > app-csr.json <<EOF
{
"CN": "app",
"hosts": [
"127.0.0.1",
"192.168.1.11",
"app",
"app.ma.com"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "BeiJing",
"L": "BeiJing",
"O": "k8s",
"OU": "System"
}
]
}
EOF
cfssl gencert -ca=/root/keys/ca.pem
-ca-key=/root/keys/ca-key.pem
-config=/root/keys/ca-config.json
-profile=app app-csr.json | cfssljson -bare app
openssl x509 -noout -text -in app.pem
构建https webserver模拟测试
cd /root/
cat > http-server.js <<EOF
var https = require('https');
var fs = require('fs');
var options = {
key: fs.readFileSync('./keys/app-key.pem'),
cert: fs.readFileSync('./keys/app.pem')
};
https.createServer(options, function (req, res) {
res.writeHead(200);
res.end('hello world');
}).listen(8000);
EOF
yum install nodejs -y
npm install https -g
node http-server.js
访问服务端https://192.168.1.x:8000端口(域已添加本地hosts)
发现

opera浏览器

处理浏览器安全问题
1.导出ca.pem到win7,改名为ca.crt.
2.运行 certmgr.msc 打开证书管理器

3.浏览器访问8000端口(ctrl+shift+del清缓存)
opera浏览器

4.使用apps.ma.com访问,也报错

无SAN(Subject Alternative Name)-CN: app.ma.com-即使地址栏的域名和CN一样也报错
cd /root/keys
rm -rf app*
cat > app-csr.json <<EOF
{
"CN": "app.ma.com", #将hosts字段去掉(SAN干掉)
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "BeiJing",
"L": "BeiJing",
"O": "k8s",
"OU": "System"
}
]
}
EOF
cfssl gencert -ca=/root/keys/ca.pem
-ca-key=/root/keys/ca-key.pem
-config=/root/keys/ca-config.json
-profile=app app-csr.json | cfssljson -bare app
openssl x509 -noout -text -in app.pem
无SAN(Subject Alternative Name)-CN: *.ma.com-即使地址栏的域名和CN一样也报错
cd /root/keys
rm -rf app*
cat > app-csr.json <<EOF
{
"CN": "*.ma.com",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "BeiJing",
"L": "BeiJing",
"O": "k8s",
"OU": "System"
}
]
}
EOF
cfssl gencert -ca=/root/keys/ca.pem
-ca-key=/root/keys/ca-key.pem
-config=/root/keys/ca-config.json
-profile=app app-csr.json | cfssljson -bare app
openssl x509 -noout -text -in app.pem

SAN含app.ma.com(Subject Alternative Name)-CN: *.ma.com-仅app.ma.com域名可访问
cd /root/keys
rm -rf app*
cat > app-csr.json <<EOF
{
"CN": "*.ma.com",
"hosts": [
"app.ma.com"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "BeiJing",
"L": "BeiJing",
"O": "k8s",
"OU": "System"
}
]
}
EOF
cfssl gencert -ca=/root/keys/ca.pem
-ca-key=/root/keys/ca-key.pem
-config=/root/keys/ca-config.json
-profile=app app-csr.json | cfssljson -bare app
openssl x509 -noout -text -in app.pem
cd ..;node http-server.js


SAN含*.ma.com(Subject Alternative Name)-CN: .ma.com-可用任意.ma.com来访问
cd /root/keys
rm -rf app*
cat > app-csr.json <<EOF
{
"CN": "*.ma.com",
"hosts": [
"*.ma.com"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "BeiJing",
"L": "BeiJing",
"O": "k8s",
"OU": "System"
}
]
}
EOF
cfssl gencert -ca=/root/keys/ca.pem
-ca-key=/root/keys/ca-key.pem
-config=/root/keys/ca-config.json
-profile=app app-csr.json | cfssljson -bare app
openssl x509 -noout -text -in app.pem
cd ..;node http-server.js

查看互联网上一些证书
-
汽车之家的通用型(*)证书(而且一个证书对应了多个域名)

-
谷歌的 www证书


wildcard和san两种证书的区别
wildcard: 可变部分sub-domain:
*.maotai.com
www.maotai.com
bbs.maotai.com
san: 可变部分: subdomain和domain
subdomain
*.ma.com
*.ma.net
*.xx.net
注:一般通用型证书比www证书价格贵一半左右.
浏览器如何验证证书
参考: http://www.cnblogs.com/iiiiher/p/8085698.html
当浏览器使用HTTPS连接到您的服务器时,他们会检查以确保您的SSL证书与地址栏中的主机名称匹配。
浏览器有三种找到匹配的方法:
-
1.主机名(在地址栏中)与证书主题(Subject)中的通用名称(Common Name)完全匹配。
-
2.主机名称与通配符通用名称相匹配。例如,www.example.com匹配通用名称* .example.com。
-
3.主机名 在主题备用名称(SAN: Subject Alternative Name)字段中列出
-
1.The host name (in the address bar) exactly matches the Common Name in the certificate's Subject.
-
2.The host name matches a Wildcard Common Name. For example, www.example.com matches the common name *.example.com.
-
3.The host name is listed in the Subject Alternative Name field.
客户端使用服务端返回的信息验证服务器的合法性,包括:
证书是否过期
发型服务器证书的CA是否可靠
返回的公钥是否能正确解开返回证书中的数字签名
服务器证书上的域名是否和服务器的实际域名相匹配 -- 要核对CN或SAN,见上
验证通过后,将继续进行通信,否则,终止通信
在哪里可以查看到san
参考: https://www.digicert.com/subject-alternative-name.htm
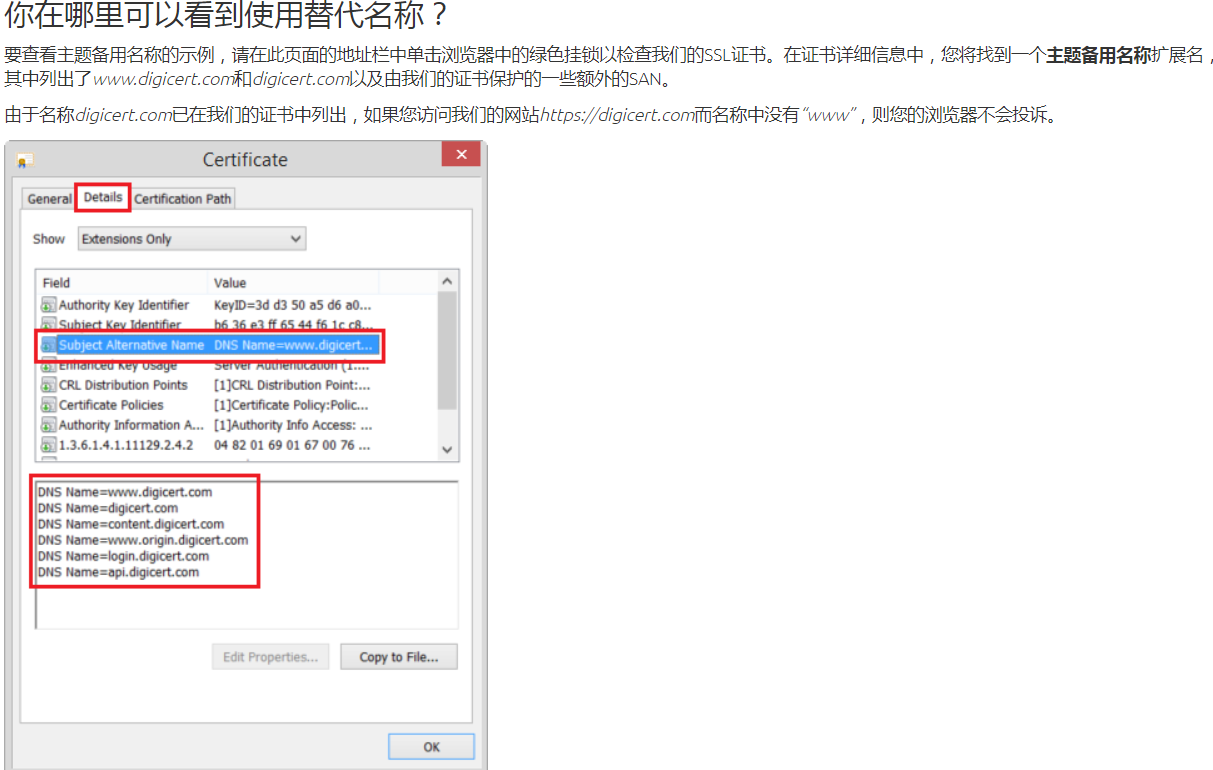
小结: 正因为访问的域名在san列表,所以访问才能被通过校验.