起因:
居然有ddos脚本,怎么可以没防御ddos的脚本!
开始:
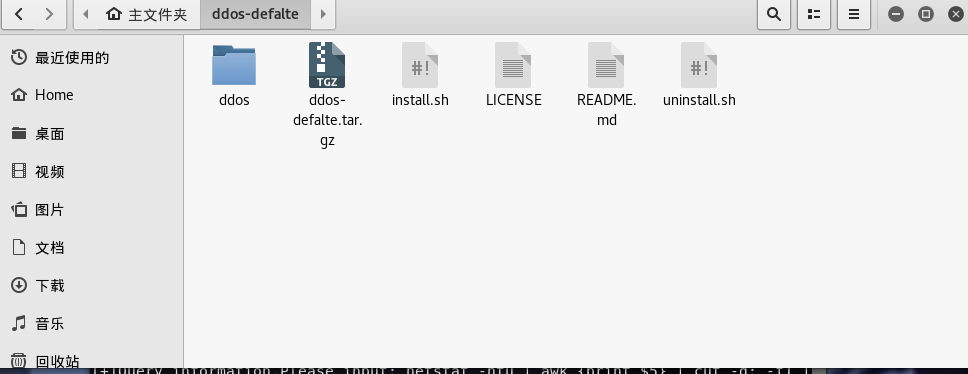
1.请执行 install.py安装好DDos-defalte,会在root目录下多出这个文件夹
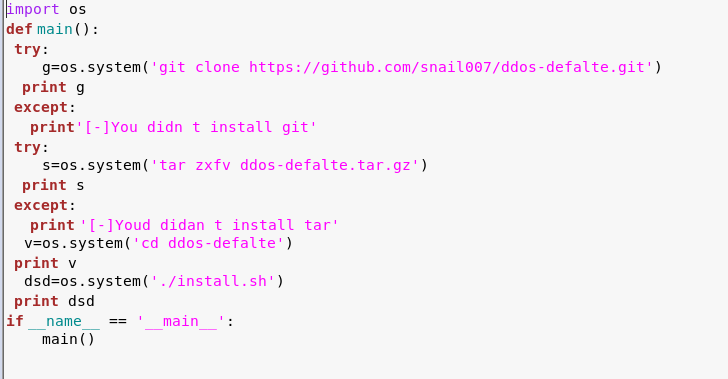
代码:
2.然后执行fyddos.py
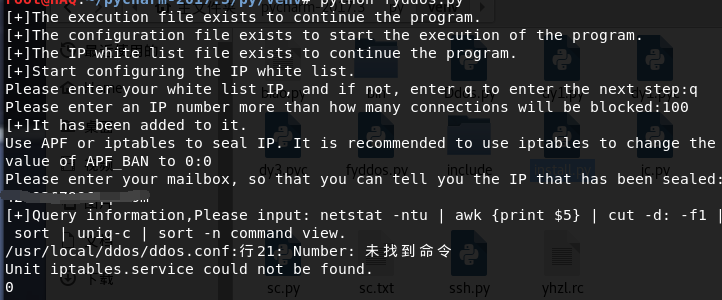
第一个让你设置IP白名单
第二个让你设置一个ip超过100个连接数,自动封掉
第三个封ip,自动发送邮件,设置好你的邮件
默认封600秒
4.然后输入这条命令
netstat -ntu | awk '{print $5}' | cut -d: -f1 | sort | uniq -c | sort -n
就可以查询谁DDos你了
DDos-defalte DDOS defalte是一款免费的用来防御和减轻DDoS攻击。它通过netstat监测跟踪创建大量网络连接的IP地址,在检测到某个结点超过预设的限制时,该程序会通过APF或iptables禁止或阻挡这些IP. #该版对原版进行了错误修复,而且进行了本地化不需要安装的时候下载文件。 #安装步骤 下载 ddos-defalte.tar.gz tar zxfv ddos-defalte.tar.gz cd ddos-defalte ./install.sh 安装完毕。 配置文件位于 /usr/local/ddos/ddos.conf ip白名单文件位于 /usr/local/ddos/ignore.ip.list ,格式:一行一个ip 配置完毕之后执行命令 ddos 可以看到一行行的输出,每行:第一个是连接数 第二个是对应ip /usr/local/sbin/ddos命令是脚本/usr/local/ddos/ddos.sh的一个软链接 安装完毕。 然后只需要计划任务周执 ddos 命令即可。ddos每执行一次都会检测配置里面的设置监测系统网络连接情况封ip。 比如root帐号下,执crontab -e 可以这样执行计划任务 */1 * * * * /usr/local/ddos/ddos.sh >/dev/null 2>&1 命令ddos有一些带参数的用法,可以通过ddos -h 了解用法。 配置文件/usr/local/ddos/ddos.conf的一些简要说明: PROGDIR="/usr/local/ddos" PROG="/usr/local/ddos/ddos.sh" IGNORE_IP_LIST="/usr/local/ddos/ignore.ip.list" #ip的白名单 APF="/etc/apf/apf" IPT="/sbin/iptables" ##### How many connections define a bad IP? Indicate that below. NO_OF_CONNECTIONS=100 #一个ip超过100个连接数,自动封掉 ##### APF_BAN=1 (Make sure your APF version is atleast 0.96) ##### APF_BAN=0 (Uses iptables for banning ips instead of APF) APF_BAN=0 #这里我使用iptables封ip ##### KILL=0 (Bad IPs are'nt banned, good for interactive execution of script) ##### KILL=1 (Recommended setting) KILL=1 ##### An email is sent to the following address when an IP is banned. ##### Blank would suppress sending of mails ,设置为 root 则不发邮件 EMAIL_TO="root" #封ip,自动发送邮件 ##### Number of seconds the banned ip should remain in blacklist. BAN_PERIOD=600
所有代码:
import os
import time
def fyddos():
IGNORE_IP_LIST = "/usr/local/ddos/ignore.ip.list"
PGOPDIR="/usr/local/ddos/ddos.conf"
PROG = "/usr/local/ddos/ddos.sh"
if os.path.exists(PROG):
print '[+]The execution file exists to continue the program.'
else:
print '[-]The execution file does not exist, the closing procedure.'
exit()
if os.path.exists(PGOPDIR):
print '[+]The configuration file exists to start the execution of the program.'
else:
print '[-]There is no exit procedure for the configuration file.'
exit()
if os.path.exists(IGNORE_IP_LIST):
print '[+]The IP white list file exists to continue the program.'
else:
print '[-]IP white list file does not exist, end the program.'
exit()
time.sleep(1)
print '[+]Start configuring the IP white list.'
IPlist=raw_input('Please enter your white list IP, and if not, enter q to enter the next step:')
if IPlist=='q':
try:
import dy1
except Exception , g:
print '[-]Catch the error cause:',g
print '[+]It has been added to it.'
time.sleep(3)
try:
import dy2
except Exception , r:
print '[-]Catch the error cause:',r
time.sleep(3)
try:
import dy3
except Exception , p:
print '[-]Catch the error cause:',p
print '[+]Query information,Please input: netstat -ntu | awk ''{print $5}'' | cut -d: -f1 | sort | uniq-c | sort -n command view.'
isd=os.system('ddos')
sda=os.system('service iptables status')
print isd
print sda
else:
list=open('/usr/local/ddos/ignore.ip.list','w')
list.write(IPlist+"
")
print '[+]It has been added to it:',IPlist
time.sleep(3)
try:
import dy1
except Exception , w:
print('[-]Catch the error cause:',w)
time.sleep(3)
try:
import dy2
except Exception , d:
print '[-]Catch the error cause:',d
time.sleep(3)
try:
import dy3
except Exception ,z:
print '[-]Catch the error cause:',z
print '[+]Query information,Please input: netstat -ntu | awk ''{print $5}'' | cut -d: -f1 | sort | uniq-c | sort -n command view.'
isds = os.system('ddos')
sdas= os.system('service iptables status')
print isds
print sdas
fyddos()
conf=input('Please enter an IP number more than how many connections will be blocked:')
data = ''
with open('/usr/local/ddos/ddos.conf', 'r+') as f:
for line in f.readlines():
if (line.find('NO_OF_CONNECTIONS') == 0):
line = 'NO_OF_CONNECTIONS={}'.format(conf) + '
'
data += line
with open('/usr/local/ddos/ddos.conf', 'r+') as f:
f.writelines(data)
lv=raw_input('Use APF or iptables to seal IP. It is recommended to use iptables to change the value of APF_BAN to 0:')
data=''
with open('/usr/local/ddos/ddos.conf','r+') as f:
for line in f.readlines():
if(line.find('APF_BAN')==0):
line='APF_BAN={}'.format(lv)+'
'
data+=line
with open('/usr/local/ddos/ddos.conf','r+') as f:
f.writelines(data)
原理:通过DDos-defalte的设置来帮助我们防御DDos(如果愿意请自行加设置代码)
一篇有关DDos-defalte的文章:http://blog.csdn.net/fly2749/article/details/51354696
ddos-defalte的Github下载地址:https://github.com/snail007/ddos-defalte
我的Github:https://github.com/422926799/python