标签:SHA1碰撞
源代码:
<?php
error_reporting(0);
include 'flag.php';
if(empty($_GET))
highlight_file(__FILE__);
if($_GET['a'] === $_GET['b'])
die("nooooo1");
if($_GET['a'] != $_GET['b'])
die("nooooo2");
if (md5($_GET['a']) === md5($_GET['b'])){
$c =base64_decode($_GET['c']);
$d =base64_decode($_GET['d']);
if($c===$d)
die("nooooo4");
if(sha1($c)===sha1($d))
echo $flag;
else
die("nooooo5");
}else{
die('nooooo3');
}
预期解
第一部分:
要求a!==b && a==b && md5(a) === md5(b);
绕过方式:a[]=0e1&b[]=0e2(科学计数法a==b,数组md5 = null)
第二部分:
如果不存在base64_decode时,可使用数组绕过。
这里使用碰撞:
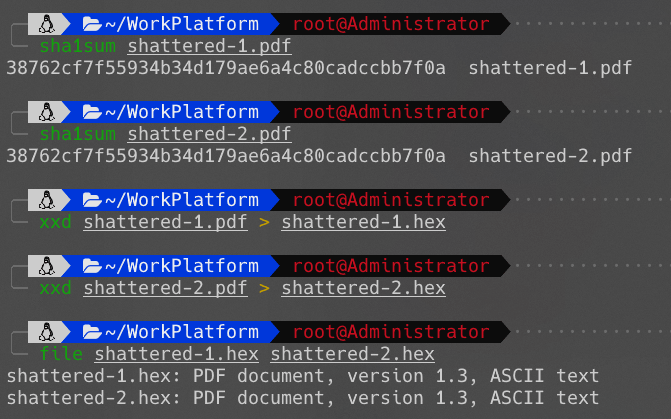
生成Payload脚本:
<?php
// 不需要base64时,可直接使用以下payload
$a = "%25PDF-1.3%0A%25%E2%E3%CF%D3%0A%0A%0A1%200%20obj%0A%3C%3C/Width%202%200%20R/Height%203%200%20R/Type%204%200%20R/Subtype%205%200%20R/Filter%206%200%20R/ColorSpace%207%200%20R/Length%208%200%20R/BitsPerComponent%208%3E%3E%0Astream%0A%FF%D8%FF%FE%00%24SHA-1%20is%20dead%21%21%21%21%21%85/%EC%09%239u%9C9%B1%A1%C6%3CL%97%E1%FF%FE%01sF%DC%91f%B6%7E%11%8F%02%9A%B6%21%B2V%0F%F9%CAg%CC%A8%C7%F8%5B%A8Ly%03%0C%2B%3D%E2%18%F8m%B3%A9%09%01%D5%DFE%C1O%26%FE%DF%B3%DC8%E9j%C2/%E7%BDr%8F%0EE%BC%E0F%D2%3CW%0F%EB%14%13%98%BBU.%F5%A0%A8%2B%E31%FE%A4%807%B8%B5%D7%1F%0E3.%DF%93%AC5%00%EBM%DC%0D%EC%C1%A8dy%0Cx%2Cv%21V%60%DD0%97%91%D0k%D0%AF%3F%98%CD%A4%BCF%29%B1";
$b = "%25PDF-1.3%0A%25%E2%E3%CF%D3%0A%0A%0A1%200%20obj%0A%3C%3C/Width%202%200%20R/Height%203%200%20R/Type%204%200%20R/Subtype%205%200%20R/Filter%206%200%20R/ColorSpace%207%200%20R/Length%208%200%20R/BitsPerComponent%208%3E%3E%0Astream%0A%FF%D8%FF%FE%00%24SHA-1%20is%20dead%21%21%21%21%21%85/%EC%09%239u%9C9%B1%A1%C6%3CL%97%E1%FF%FE%01%7FF%DC%93%A6%B6%7E%01%3B%02%9A%AA%1D%B2V%0BE%CAg%D6%88%C7%F8K%8CLy%1F%E0%2B%3D%F6%14%F8m%B1i%09%01%C5kE%C1S%0A%FE%DF%B7%608%E9rr/%E7%ADr%8F%0EI%04%E0F%C20W%0F%E9%D4%13%98%AB%E1.%F5%BC%94%2B%E35B%A4%80-%98%B5%D7%0F%2A3.%C3%7F%AC5%14%E7M%DC%0F%2C%C1%A8t%CD%0Cx0Z%21Vda0%97%89%60k%D0%BF%3F%98%CD%A8%04F%29%A1";
print_r(urlencode(base64_encode(urldecode($a))));
echo "
";
print_r(urlencode(base64_encode(urldecode($b))));
?>
Payload:
http://[IP]/temp.php?
a[]=0e2
&b[]=0e1
&c=JVBERi0xLjMKJeLjz9MKCgoxIDAgb2JqCjw8L1dpZHRoIDIgMCBSL0hlaWdodCAzIDAgUi9UeXBlIDQgMCBSL1N1YnR5cGUgNSAwIFIvRmlsdGVyIDYgMCBSL0NvbG9yU3BhY2UgNyAwIFIvTGVuZ3RoIDggMCBSL0JpdHNQZXJDb21wb25lbnQgOD4%2BCnN0cmVhbQr%2F2P%2F%2BACRTSEEtMSBpcyBkZWFkISEhISGFL%2BwJIzl1nDmxocY8TJfh%2F%2F4Bc0bckWa2fhGPApq2IbJWD%2FnKZ8yox%2FhbqEx5AwwrPeIY%2BG2zqQkB1d9FwU8m%2Ft%2Bz3DjpasIv571yjw5FvOBG0jxXD%2BsUE5i7VS71oKgr4zH%2BpIA3uLXXHw4zLt%2BTrDUA603cDezBqGR5DHgsdiFWYN0wl5HQa9CvP5jNpLxGKbE%3D
&d=JVBERi0xLjMKJeLjz9MKCgoxIDAgb2JqCjw8L1dpZHRoIDIgMCBSL0hlaWdodCAzIDAgUi9UeXBlIDQgMCBSL1N1YnR5cGUgNSAwIFIvRmlsdGVyIDYgMCBSL0NvbG9yU3BhY2UgNyAwIFIvTGVuZ3RoIDggMCBSL0JpdHNQZXJDb21wb25lbnQgOD4%2BCnN0cmVhbQr%2F2P%2F%2BACRTSEEtMSBpcyBkZWFkISEhISGFL%2BwJIzl1nDmxocY8TJfh%2F%2F4Bf0bck6a2fgE7ApqqHbJWC0XKZ9aIx%2FhLjEx5H%2BArPfYU%2BG2xaQkBxWtFwVMK%2Ft%2B3YDjpcnIv561yjw5JBOBGwjBXD%2BnUE5ir4S71vJQr4zVCpIAtmLXXDyozLsN%2FrDUU503cDyzBqHTNDHgwWiFWZGEwl4lga9C%2FP5jNqARGKaE%3D
非预期
http://[IP]/temp.php?a[]=0e2&b[]=0e1&c[]=1&d[]=&c