域外windows
一句话域内搜集
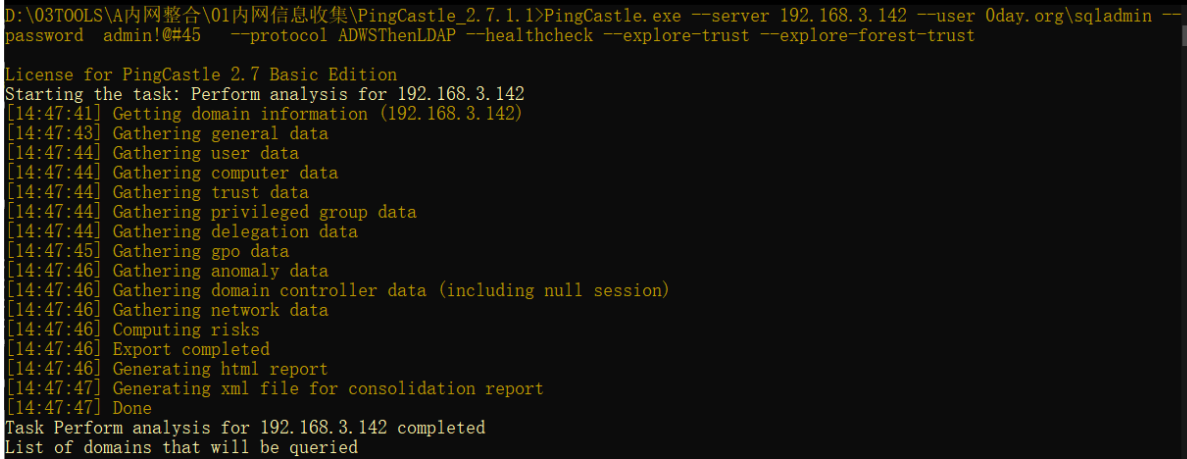
PingCastle.exe --server 192.168.3.142 --user 0day.orgjack --password admin!@#45 --protocol ADWSThenLDAP --healthcheck --explore-trust --explore-forest-trust
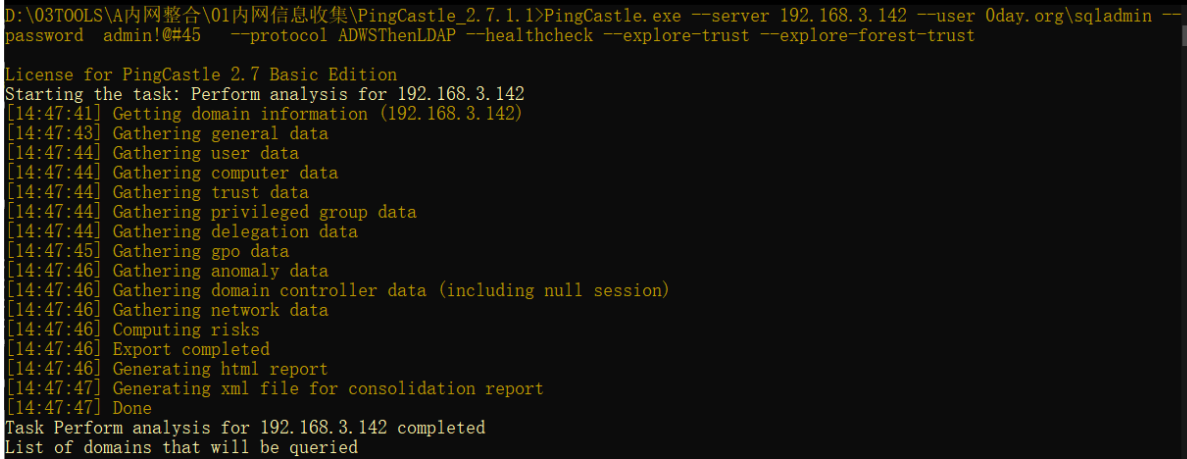
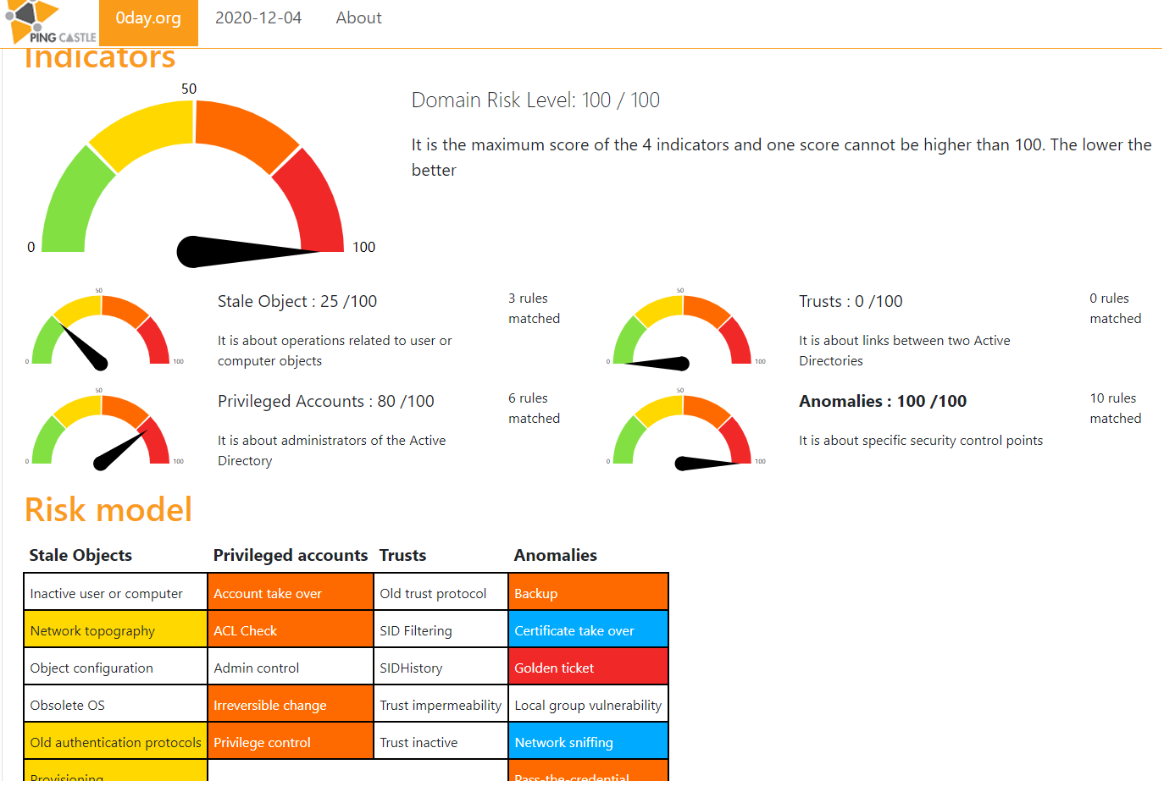
目录内输出信息如下
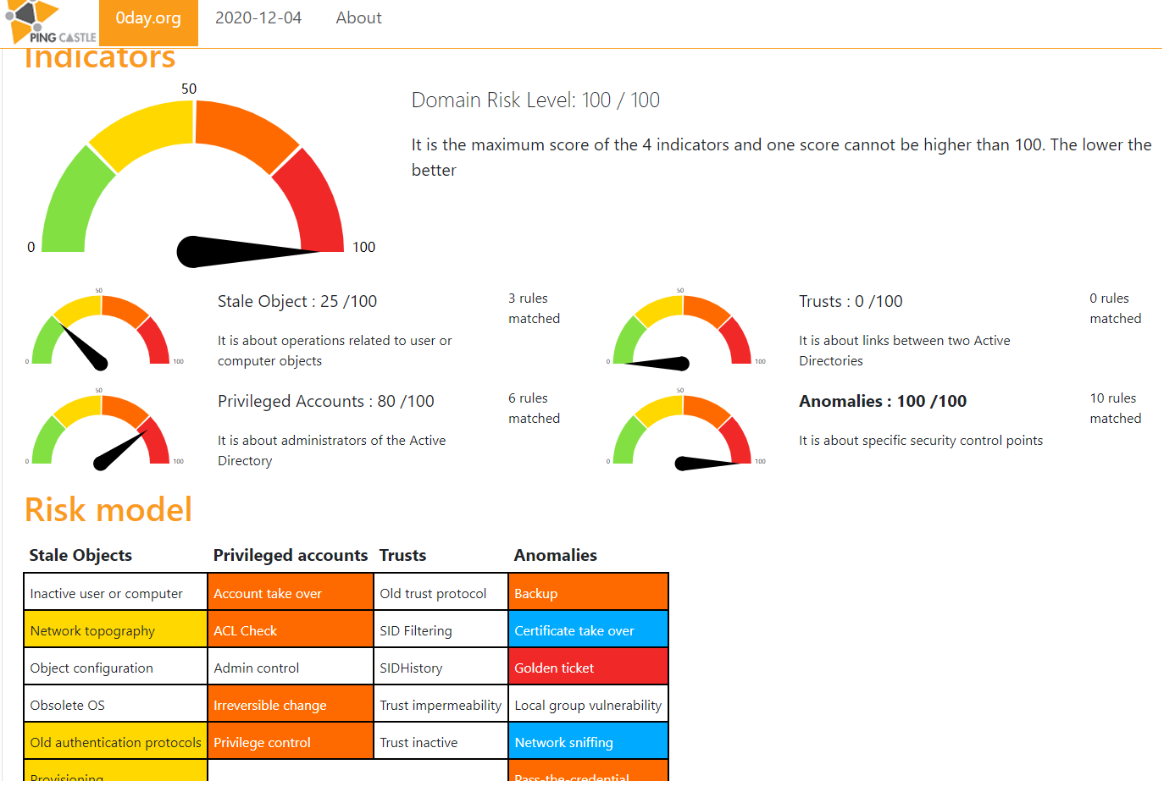
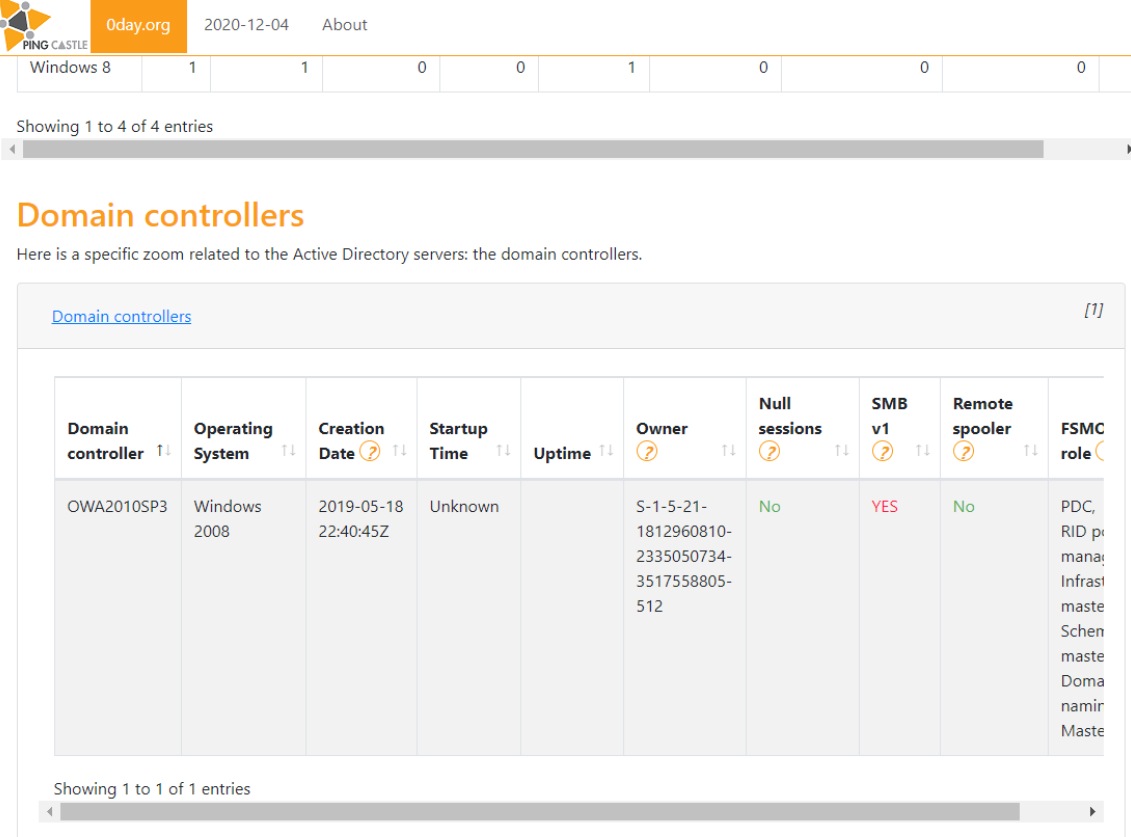
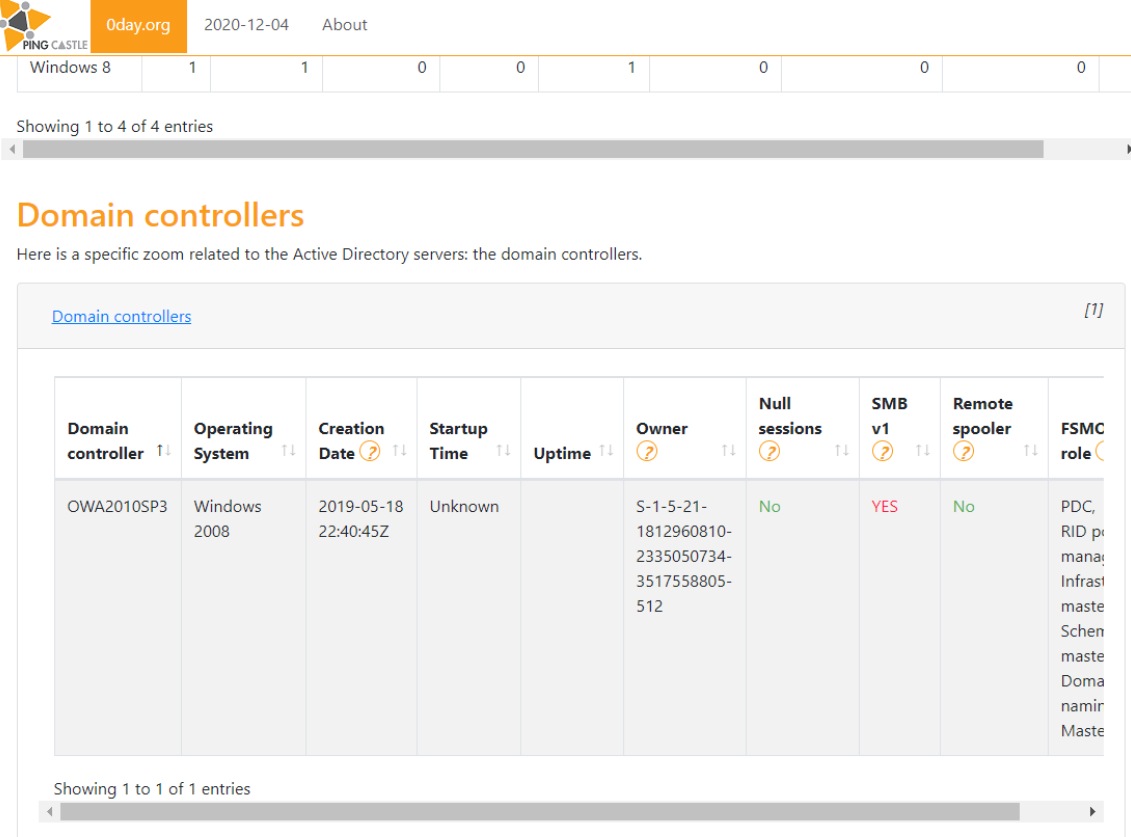
域控信息
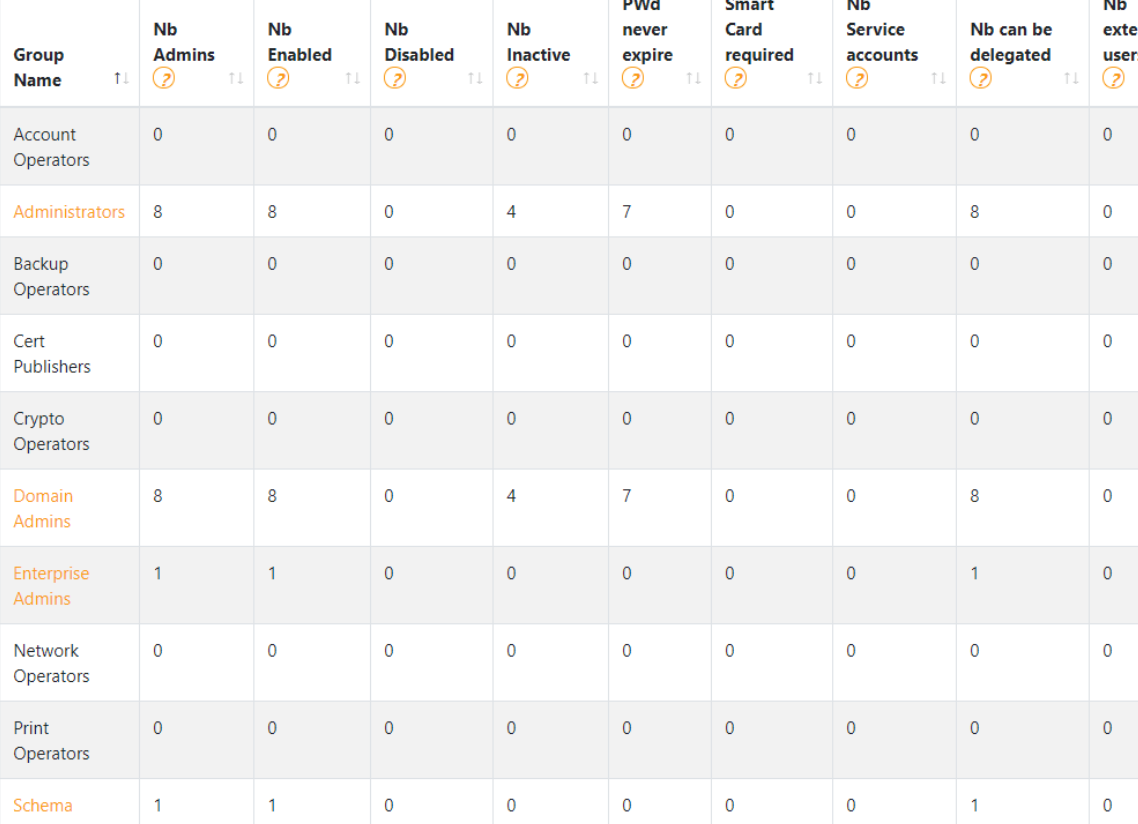
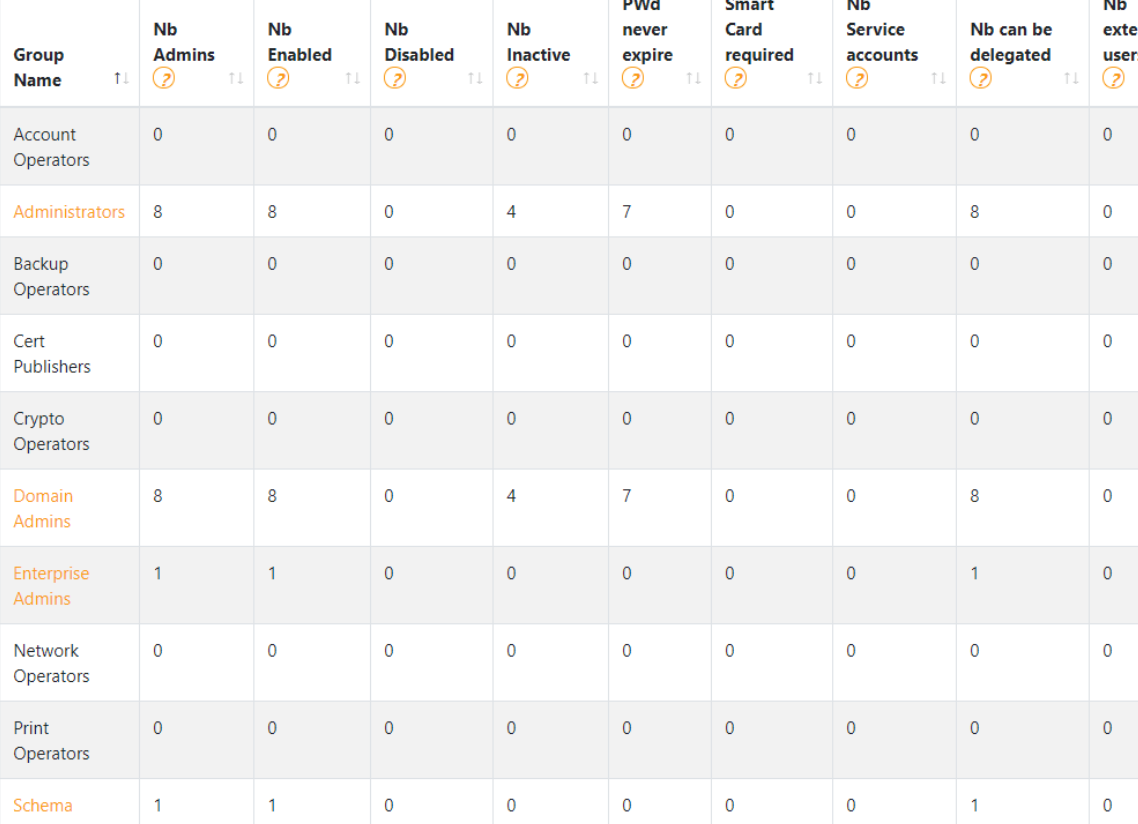
组信息
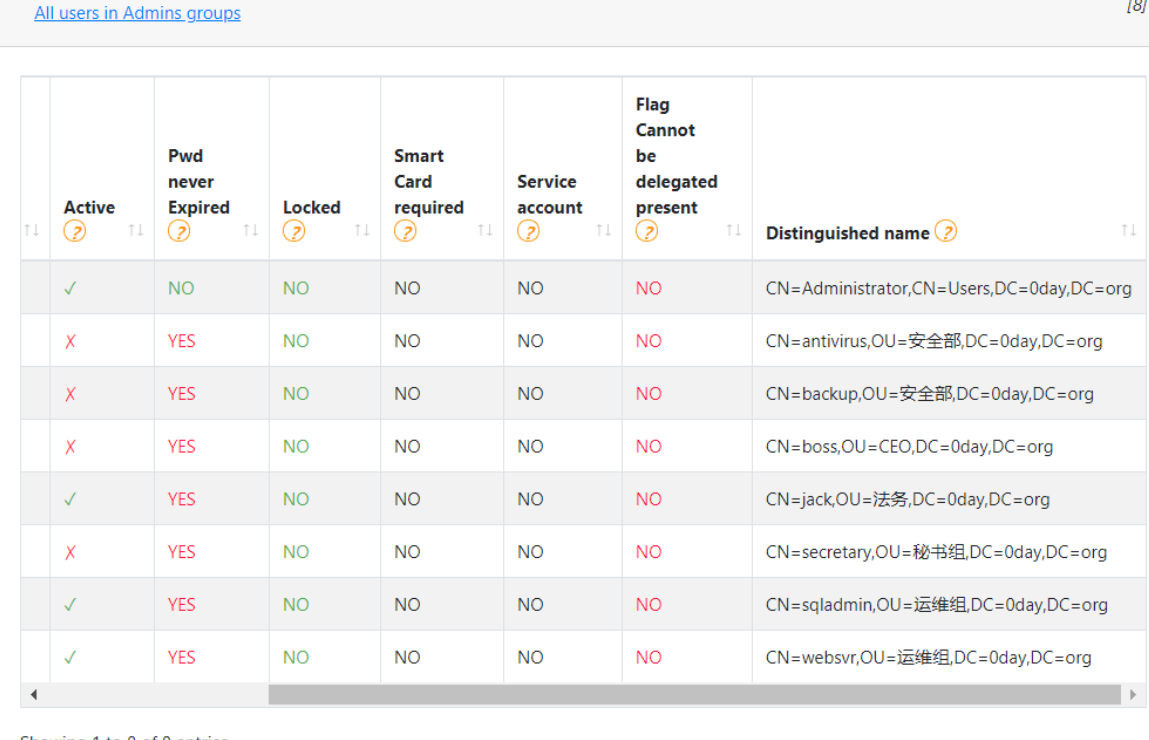
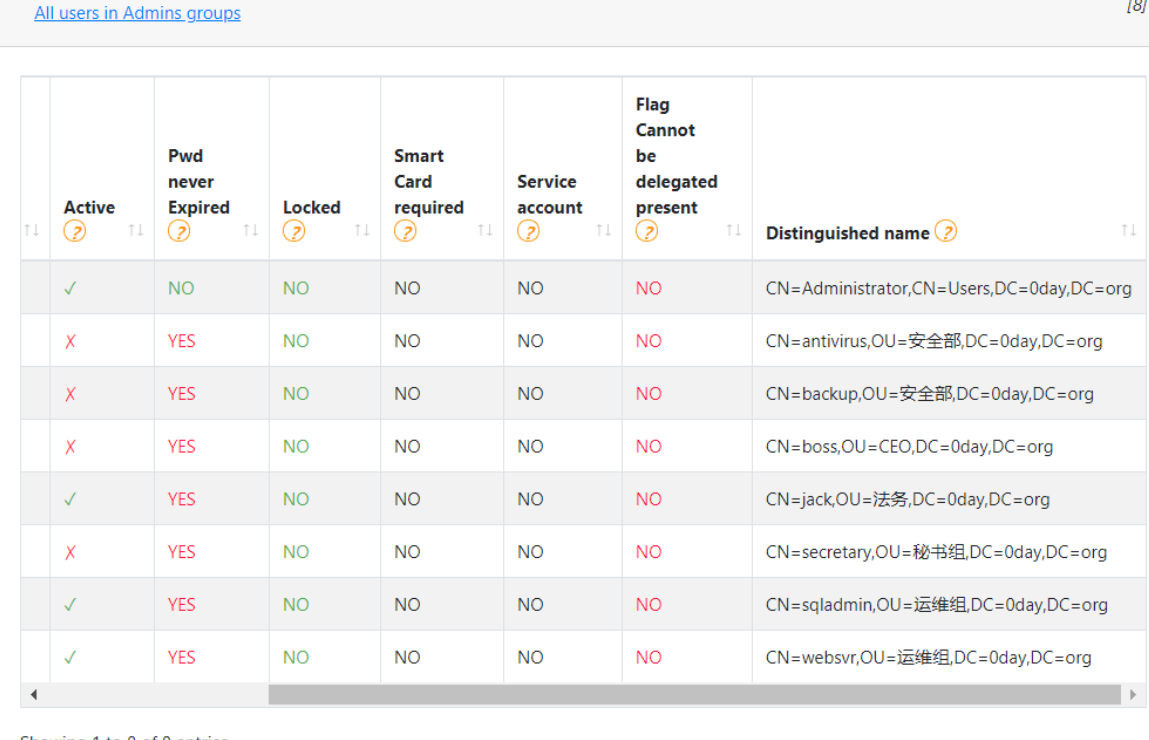
域内用户信息收集
不是特别的全
PingCastle.exe --server 192.168.3.142 --user 0day.orgjack --password admin!@#45 --protocol ADWSThenLDAP --scanner export_user
zerologon漏洞探测
PingCastle.exe --server 192.168.3.142 --scanner zerologon --scmode-dc
假如,目标系统无.net 3.5 环境,可尝试直接在 cmd 命令行下在线安装
DISM /Online /Enable-Feature /FeatureName:NetFx3 /All
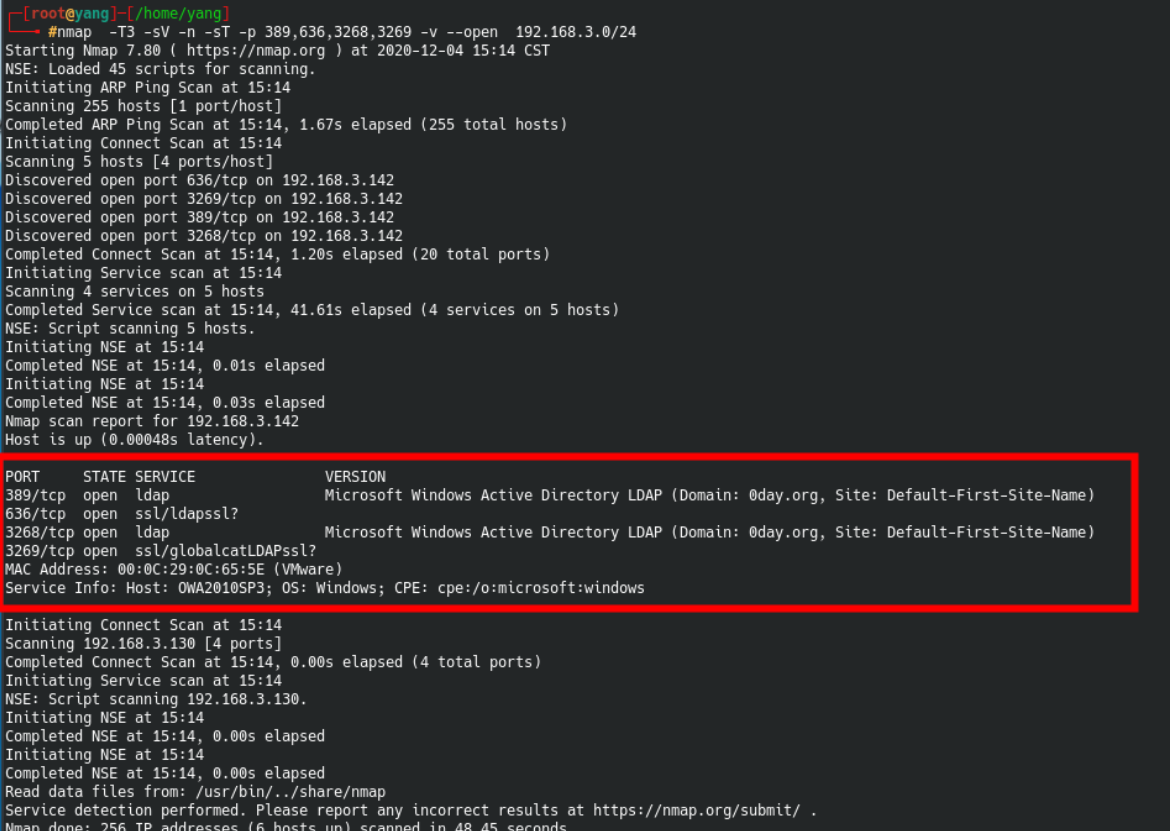
域外linux
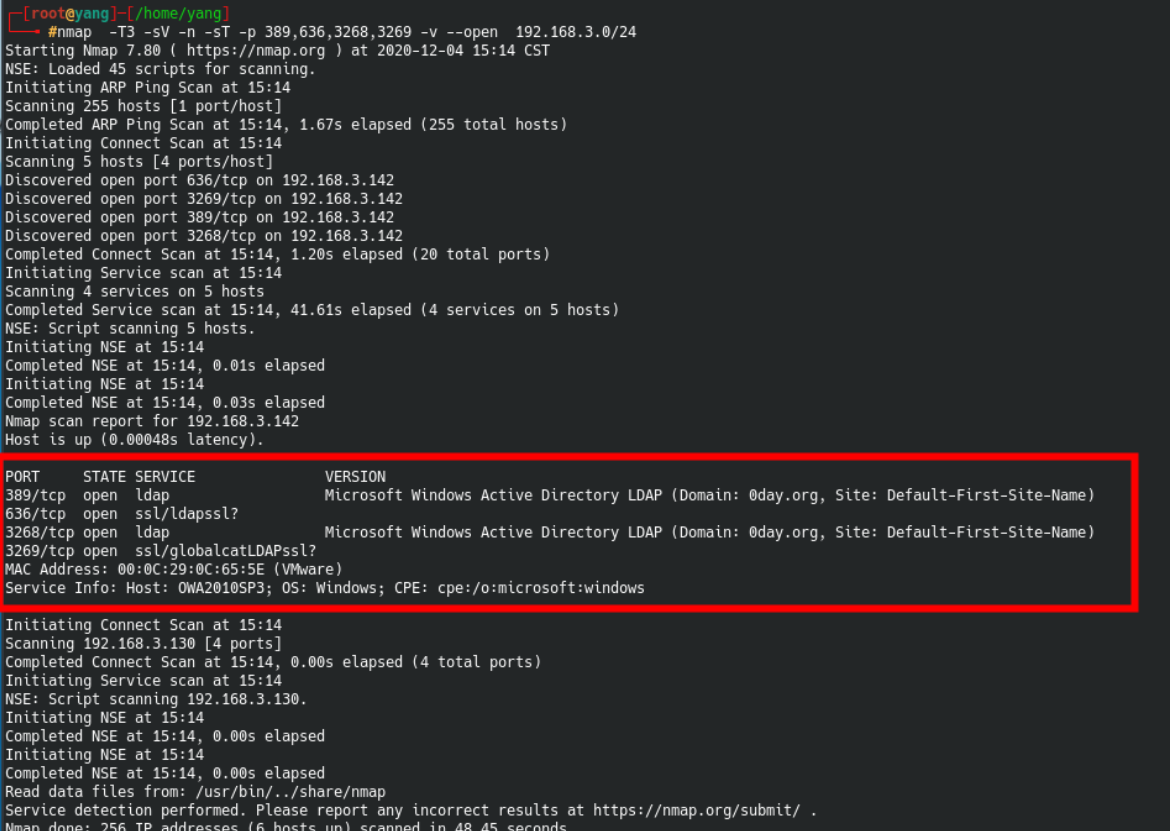
通过ldap发现域控所在
nmap -T3 -sV -n -sT -p 389,636,3268,3269 -v --open 192.168.3.0/24
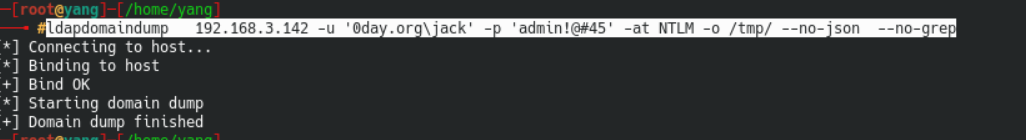
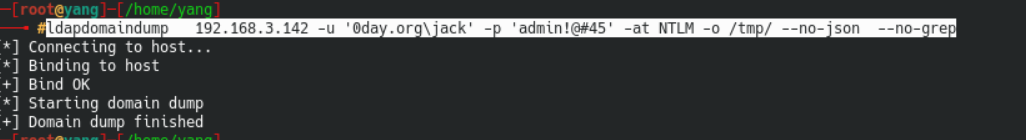
只需普通用户即可远程dump,此处在socks下也可使用
pip2.7 install ldapdomaindump
ldapdomaindump 192.168.3.142 -u '0day.orgjack' -p 'admin!@#45' -at NTLM -o /tmp/ --no-json --no-grep
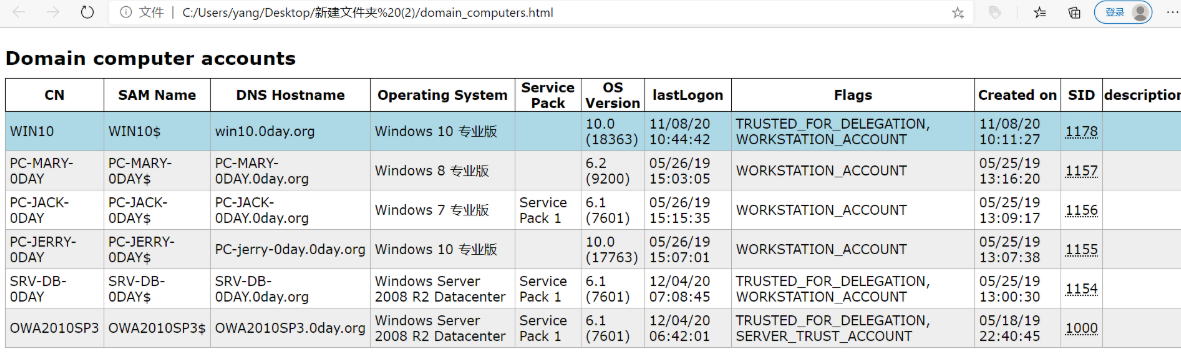
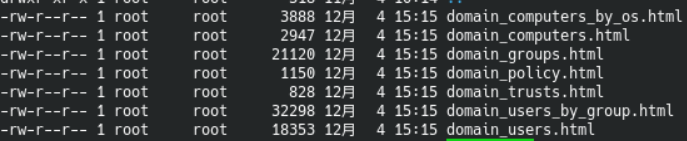
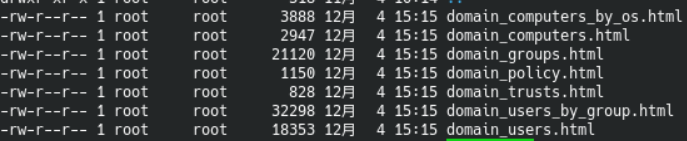
获得信息如下
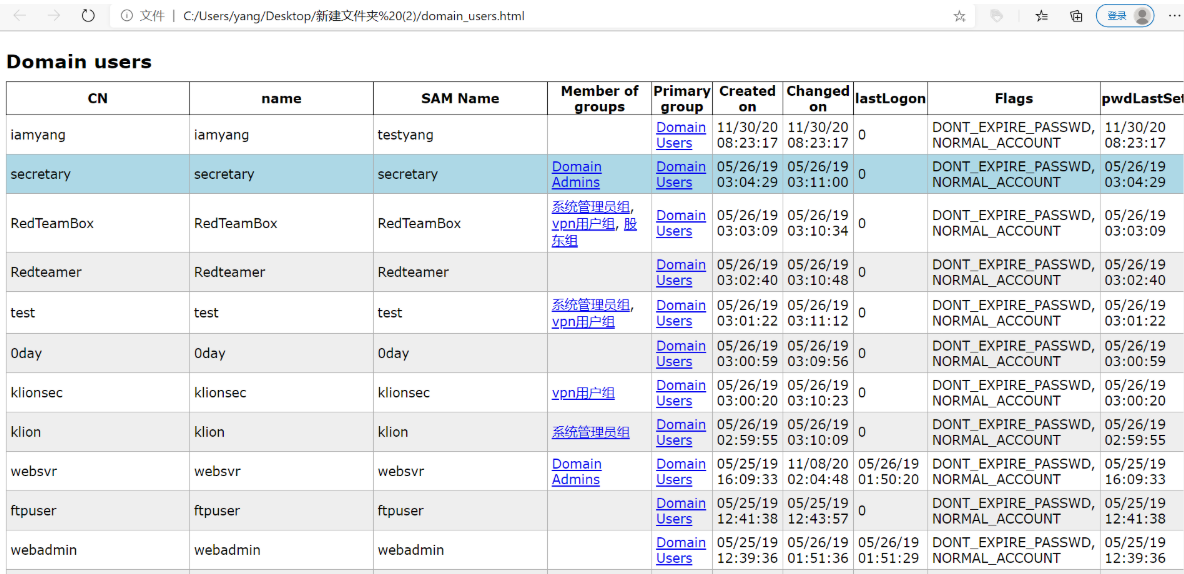
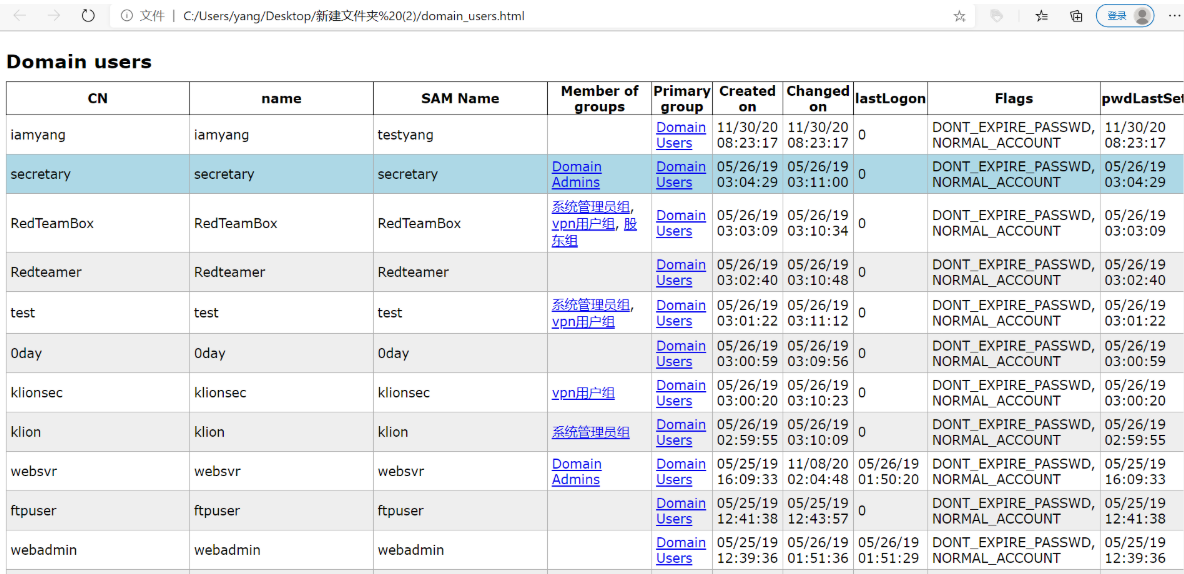
域用户信息如下
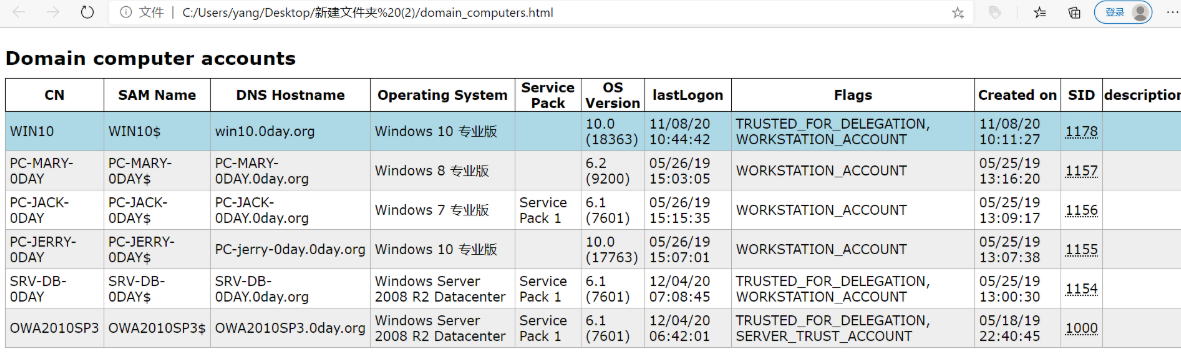
域成员终端信息如下