SSCTF2020 RE2
有时间做了一下SSCTF 2020的re2
附件地址:
链接:https://pan.baidu.com/s/1k5SuiJIHJzgYZVbc9hX8ZA
提取码:lyco
基本方法:动调
int sub_8310A0()
{
HANDLE v0; // esi
HMODULE v1; // eax
FARPROC v2; // eax
unsigned int v3; // ebx
__int64 v4; // rdi
signed int v5; // kr08_4
unsigned int v6; // ecx
unsigned int v7; // edx
unsigned int v8; // eax
unsigned int v9; // ecx
int v10; // eax
int v11; // edx
unsigned int v12; // ecx
char v13; // al
bool v14; // cf
unsigned int v15; // ecx
const char *v16; // eax
int v17; // eax
int v18; // edx
char v19; // cl
int v20; // edx
char v21; // ch
int v22; // eax
char v23; // cl
int v24; // eax
int v25; // edx
char v26; // ch
char v27; // cl
int v28; // kr28_4
signed int v29; // ecx
unsigned int v30; // ebx
unsigned int v31; // edi
unsigned int v32; // ecx
unsigned int v33; // eax
char v35; // [esp+13h] [ebp-125h]
char v36; // [esp+13h] [ebp-125h]
unsigned int v37; // [esp+14h] [ebp-124h]
int v38; // [esp+14h] [ebp-124h]
int v39; // [esp+18h] [ebp-120h]
char *v40; // [esp+1Ch] [ebp-11Ch]
unsigned int v41; // [esp+20h] [ebp-118h]
signed int v42; // [esp+2Ch] [ebp-10Ch]
int v43; // [esp+30h] [ebp-108h]
int v44; // [esp+34h] [ebp-104h]
int v45; // [esp+38h] [ebp-100h]
int v46; // [esp+3Ch] [ebp-FCh]
int v47; // [esp+40h] [ebp-F8h]
int v48; // [esp+44h] [ebp-F4h]
__int64 v49; // [esp+48h] [ebp-F0h]
int v50; // [esp+50h] [ebp-E8h]
int v51; // [esp+54h] [ebp-E4h]
char *v52; // [esp+58h] [ebp-E0h]
int v53; // [esp+64h] [ebp-D4h]
char v54; // [esp+68h] [ebp-D0h]
char v55; // [esp+69h] [ebp-CFh]
char v56[202]; // [esp+6Ah] [ebp-CEh]
sub_832260((__m128i *)&v54, 0, 0xC8u);
v43 = 0x3B082235;
v44 = 0xFCF20A00;
v45 = 0xE2EED037;
v46 = 0xF3FEFAD6;
v47 = 0xC2101FF5;
v48 = 0xD703FBEC;
v49 = 0xE029FC16FCC9E2FCi64;
v50 = 0xFE1134F0;
LOWORD(v51) = 0x2761;
BYTE2(v51) = 39;
v0 = GetCurrentThread();
v1 = LoadLibraryA("ntdll.dll");
v2 = GetProcAddress(v1, "ZwSetInformationThread");// 反调试,直接修改EIP绕过
((void (__stdcall *)(HANDLE, signed int, _DWORD, _DWORD))v2)(v0, 17, 0, 0);
sub_831020((int)"Pls Input Your Flag:");
sub_831060("%s", &v54, 39);
v3 = (signed int)&v54 >> 31;
HIDWORD(v4) = &v54;
LODWORD(v4) = &v54;
v52 = &v54;
v40 = &v54;
v5 = strlen(&v54);
v53 = v5;
if ( v5 > 0 )
{
v6 = 0;
v37 = 0;
v41 = 0;
do
{
do
{
v7 = v37;
v8 = v41 - 7 * (v6 / 7);
v9 = v41;
*(&v54 + v41) = (*(&v54 + v41) ^ aDdxtqkl[v8]) + 65;// 进行第一次加密,即将输入与对应字符串进行取余异或加65
v10 = v41++;
v37 = (__PAIR__(v37, v9) + 1) >> 32;
v6 = v9 + 1;
}
while ( v5 - 1 != v10 );
}
while ( v7 );
v38 = 0;
HIDWORD(v4) = (signed int)&v54 >> 31;
do
{
v35 = *(_BYTE *)(v4 + 3);
v11 = (unsigned __int64)(v4 + 3) >> 32;
v12 = v4 + 3;
LODWORD(v4) = v4 + 3;
do
{
v13 = *(_BYTE *)(v4 - 1);
v14 = v12-- != 0; // 第二次加密,即分组,每组四位 将每组第四位放在第一位,前三个顺延,即1->2,2->3,3->4
LODWORD(v4) = v12;
v11 = v14 + v11 - 1;
*(_BYTE *)(v12 + 1) = v13;
}
while ( __PAIR__(HIDWORD(v4), v12) != __PAIR__(v11, (unsigned int)v40) );
LODWORD(v4) = v40;
v38 += 4;
*v40 = v35;
v40 += 4;
v4 += 4i64;
}
while ( v53 > v38 );
HIDWORD(v4) = v52;
v3 = (signed int)&v54 >> 31;
}
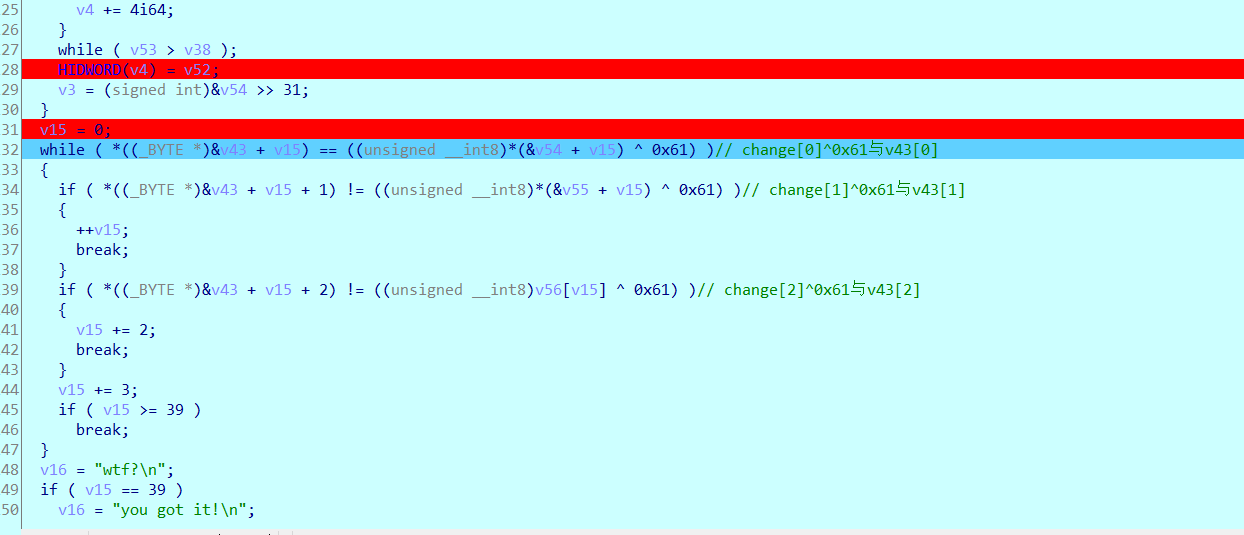
v15 = 0;
while ( *((_BYTE *)&v43 + v15) == ((unsigned __int8)*(&v54 + v15) ^ 0x61) )// change[0]^0x61与v43[0]
{
if ( *((_BYTE *)&v43 + v15 + 1) != ((unsigned __int8)*(&v55 + v15) ^ 0x61) )// change[1]^0x61与v43[1]
{
++v15;
break;
}
if ( *((_BYTE *)&v43 + v15 + 2) != ((unsigned __int8)v56[v15] ^ 0x61) )// change[2]^0x61与v43[2]
{
v15 += 2;
break;
}
v15 += 3;
if ( v15 >= 39 )
break;
}
v16 = "wtf?
";
if ( v15 == 39 )
v16 = "you got it!
";
sub_831020((int)v16);
sub_8395C1("pause");
v42 = 10;
do
{
v36 = *(_BYTE *)(HIDWORD(v4) + 3);
LODWORD(v4) = HIDWORD(v4) + 3;
v17 = __CFADD__(HIDWORD(v4), 3) + v3;
v18 = HIDWORD(v4) + 3;
do
{
v19 = *(_BYTE *)(v18 - 1);
v14 = (_DWORD)v4 != 0;
LODWORD(v4) = v4 - 1;
v18 = v4;
v17 = v14 + v17 - 1;
*(_BYTE *)(v4 + 1) = v19;
}
while ( __PAIR__(HIDWORD(v4), v3) != __PAIR__(v4, v17) );
LODWORD(v4) = HIDWORD(v4) + 3;
v20 = HIDWORD(v4) + 3;
*(_BYTE *)HIDWORD(v4) = v36;
v21 = *(_BYTE *)(HIDWORD(v4) + 3);
v22 = __CFADD__(HIDWORD(v4), 3) + v3;
do
{
v23 = *(_BYTE *)(v20 - 1);
v14 = (_DWORD)v4 != 0;
LODWORD(v4) = v4 - 1;
v20 = v4;
v22 = v14 + v22 - 1;
*(_BYTE *)(v4 + 1) = v23;
}
while ( __PAIR__(HIDWORD(v4), v3) != __PAIR__(v4, v22) );
v24 = HIDWORD(v4) + 3;
v25 = __CFADD__(HIDWORD(v4), 3) + v3;
LODWORD(v4) = HIDWORD(v4) + 3;
*(_BYTE *)HIDWORD(v4) = v21;
v26 = *(_BYTE *)(HIDWORD(v4) + 3);
do
{
do
{
v27 = *(_BYTE *)(v4 - 1);
v14 = v24-- != 0;
LODWORD(v4) = v24;
v25 = v14 + v25 - 1;
*(_BYTE *)(v24 + 1) = v27;
}
while ( HIDWORD(v4) != v24 );
}
while ( v3 != v25 );
*(_BYTE *)HIDWORD(v4) = v26;
v28 = HIDWORD(v4) + 4;
v3 = (__PAIR__(v3, HIDWORD(v4)) + 4) >> 32;
HIDWORD(v4) += 4;
--v42;
}
while ( v42 );
v29 = strlen((const char *)(v28 - 40));
if ( v29 > 0 )
{
*(_QWORD *)&v52 = 0i64;
v30 = 0;
v31 = 0;
v39 = v29 - 1;
do
{
do
{
v32 = v30;
*(_BYTE
*)(v31 + v28 - 40) = aDdxtqkl[v31 % 7] ^ (*(_BYTE *)(v31 + v28 - 40) - 65);
v33 = v31;
v30 = (__PAIR__(v30, v31++) + 1) >> 32;
}
while ( v39 != v33 );
}
while ( v32 );
}
return 0;
}
最底下的迷惑语句不需要管,找到出口就行
#include <stdio.h>
#include <string.h>
int main()
{
char s[]="dDxtQkl";
unsigned char ida_chars[] =
{
0x35, 0x22, 0x08, 0x3B, 0x00, 0x0A, 0xF2, 0xFC, 0x37, 0xD0,
0xEE, 0xE2, 0xD6, 0xFA, 0xFE, 0xF3, 0xF5, 0x1F, 0x10, 0xC2,
0xEC, 0xFB, 0x03, 0xD7, 0xFC, 0xE2, 0xC9, 0xFC, 0x16, 0xFC,
0x29, 0xE0, 0xF0, 0x34, 0x11, 0xFE,0x61,0x27,0x27
};
int i=0;
int j=0,tmp;
for(i=0;i<39;i++){
ida_chars[i]^=0x61;
}
for(i=0;i<39;i=i+4){
tmp=ida_chars[i];
ida_chars[i]=ida_chars[i+1];
ida_chars[i+1]=ida_chars[i+2];
ida_chars[i+2]=ida_chars[i+3];
ida_chars[i+3]=tmp;
}
for(i=0;i<39;i++){
printf("%c",(ida_chars[i]-65)^s[i%7]);
}
return 0;
}
